AWS Security Blog
Tag: DevSecOps
Beyond IAM access keys: Modern authentication approaches for AWS
When it comes to AWS authentication, relying on long-term credentials, such as AWS Identity and Access Management (IAM) access keys, introduces unnecessary risks; including potential credential exposure, unauthorized sharing, or theft. In this post, I present five common use cases where AWS customers traditionally use IAM access keys and present more secure alternatives that you […]
Strengthen the DevOps pipeline and protect data with AWS Secrets Manager, AWS KMS, and AWS Certificate Manager
In this blog post, we delve into using Amazon Web Services (AWS) data protection services such as AWS Secrets Manager, AWS Key Management Service (AWS KMS), and AWS Certificate Manager (ACM) to help fortify both the security of the pipeline and security in the pipeline. We explore how these services contribute to the overall security […]
Automate Cedar policy validation with AWS developer tools
Cedar is an open-source language that you can use to write policies and make authorization decisions based on those policies. AWS security services including AWS Verified Access and Amazon Verified Permissions use Cedar to define policies. Cedar supports schema declaration for the structure of entity types in those policies and policy validation with that schema. […]
Introducing IAM Access Analyzer custom policy checks
July 12, 2024: AWS has extended custom policy checks to include a new check called Check No Public Access. This new check determines whether a resource policy grants public access to a specified resource type. In addition to this new check, there has been an update to the existing Check Access Not Granted check. The […]
Validate IAM policies by using IAM Policy Validator for AWS CloudFormation and GitHub Actions
April 15, 2024: AWS has launched two new GitHub Actions that can be used to simplify some of the steps covered in this blog post. Click here to learn more abbot the new GitHub actions for AWS CloudFormation and HashiCorp’s Terraform. In this blog post, I’ll show you how to automate the validation of AWS […]
Use Amazon Inspector to manage your build and deploy pipelines for containerized applications
Amazon Inspector is an automated vulnerability management service that continually scans Amazon Web Services (AWS) workloads for software vulnerabilities and unintended network exposure. Amazon Inspector currently supports vulnerability reporting for Amazon Elastic Compute Cloud (Amazon EC2) instances and container images stored in Amazon Elastic Container Registry (Amazon ECR). With the emergence of Docker in 2013, […]
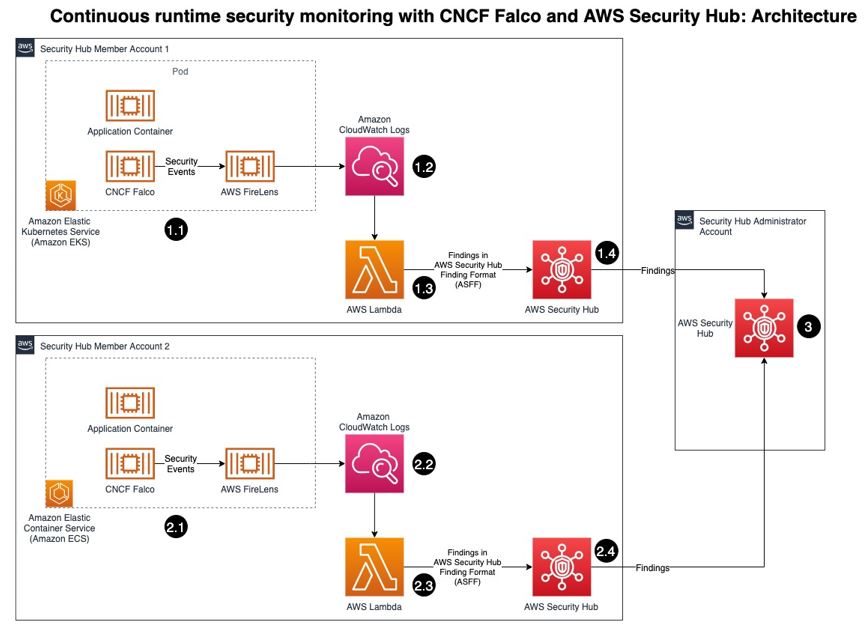
Continuous runtime security monitoring with AWS Security Hub and Falco
Customers want a single and comprehensive view of the security posture of their workloads. Runtime security event monitoring is important to building secure, operationally excellent, and reliable workloads, especially in environments that run containers and container orchestration platforms. In this blog post, we show you how to use services such as AWS Security Hub and […]
Forensic investigation environment strategies in the AWS Cloud
When a deviation from your secure baseline occurs, it’s crucial to respond and resolve the issue quickly and follow up with a forensic investigation and root cause analysis. Having a preconfigured infrastructure and a practiced plan for using it when there’s a deviation from your baseline will help you to extract and analyze the information […]
7 ways to improve security of your machine learning workflows
In this post, you will learn how to use familiar security controls to build more secure machine learning (ML) workflows. The ideal audience for this post includes data scientists who want to learn basic ways to improve security of their ML workflows, as well as security engineers who want to address threats specific to an […]
Use Macie to discover sensitive data as part of automated data pipelines
Data is a crucial part of every business and is used for strategic decision making at all levels of an organization. To extract value from their data more quickly, Amazon Web Services (AWS) customers are building automated data pipelines—from data ingestion to transformation and analytics. As part of this process, my customers often ask how […]