AWS Storage Blog
AWS Partners use AWS PrivateLink to connect privately to Amazon S3
Many customers use applications from the AWS Partner ecosystem for a range of use cases, including data lakes, data analytics, data warehousing, backup and restore, archive, and more. Certain security-conscious applications running in on-premises data centers need private access to Amazon S3 without going over the internet or using public IPs. Traditionally, to achieve this private connectivity to Amazon S3 from on-premises applications, customers deployed proxy servers with private IP addresses in their Amazon Virtual Private Cloud (VPC)s. Requests are then sent to these proxy servers, which in-turn route the traffic to Amazon S3 via gateway VPC endpoints. While this approach works, it is complex to manage, adds additional points of failure, and is difficult to scale.
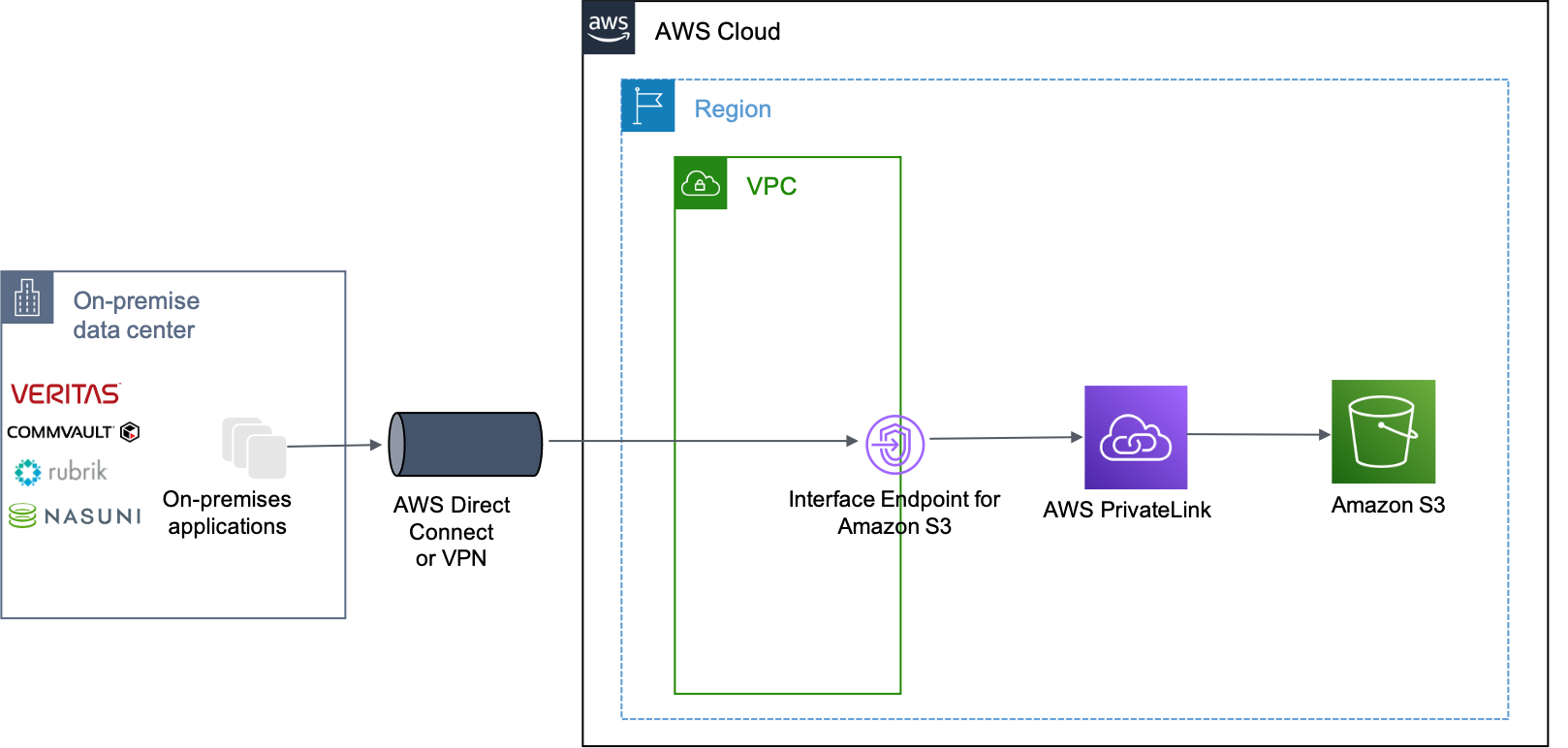
To address these challenges, we recently introduced Amazon S3 support for AWS PrivateLink, which provides a simple way to connect privately to Amazon S3 via interface VPC endpoints. These interface endpoints are accessible from on-premises networks via AWS Direct Connect or AWS Virtual Private Network (AWS VPN), and provide private connectivity to Amazon S3 over private IP addresses. Similar to gateway endpoints, they are also accessible to applications running inside the VPC. This can simplify a customer’s network architecture by eliminating the need to deploy an internet gateway, configure firewall rules, or set up proxy servers in the VPC.
In this blog post, I highlight use cases and testimonials from a few of our AWS Partners that use Amazon S3 support for AWS PrivateLink to facilitate private connections to S3.
AWS Partner solutions using Amazon S3 support for AWS PrivateLink
Many of our AWS Partners, especially those providing storage, data analytics, and DevOps solutions, have shown tremendous support for Amazon S3 support for AWS PrivateLink. Veritas, Commvault, Rubrik, Nasuni, Snowflake, Elastic, and HashiCorp were early adopters of this feature. Based on this, they were capable of supporting AWS PrivateLink immediately upon its general availability.
AWS Storage Partners
Veritas, Commvault and Rubrik provide backup and recovery capabilities for workloads running on-premises and in the cloud, and support Amazon S3 as one of the targets for storing backup data. Without Amazon S3 support for AWS PrivateLink, backup applications running in on-premises data centers must use proxy servers set up in the VPC for private connectivity to Amazon S3. This configuration becomes simpler with Amazon S3 support for AWS PrivateLink, as customers can upload and download backup data over the private connection to Amazon S3.
Nasuni provides a primary storage solution that uses Amazon S3 on the backend to store file system data. Nasuni’s edge appliances, that run on-premises, use Amazon S3 support for AWS PrivateLink to securely store and recover file system data to Amazon S3.
Storage partners highlight the benefit of Amazon S3 support for AWS PrivateLink in their own words:
![]()
“Veritas is pleased to leverage Amazon S3 support for AWS PrivateLink for customers who now have a safe and reliable transport mechanism to move backup data from the customer data center to the cloud using Veritas NetBackup. Veritas and AWS engaged with several financial Veritas NetBackup customers who are interested in performing backup and recovery operations using AWS PrivateLink for Amazon S3.”
Karthik Ramamurthy, VP Product Management, Veritas
![]() “Amazon S3 support for AWS PrivateLink is a game changer for our customers. Our customers trust us to back up, recover, and move their data securely from on-premises to AWS. PrivateLink for S3 will now ensure that customer encrypted data additionally has secure private connection between the on-premises environment and their S3 resources in the cloud. This should provide our customers with greater flexibility in terms of backing up and migrating their workloads to S3 using Commvault.”
“Amazon S3 support for AWS PrivateLink is a game changer for our customers. Our customers trust us to back up, recover, and move their data securely from on-premises to AWS. PrivateLink for S3 will now ensure that customer encrypted data additionally has secure private connection between the on-premises environment and their S3 resources in the cloud. This should provide our customers with greater flexibility in terms of backing up and migrating their workloads to S3 using Commvault.”
Rahul Pawar, Global Field CTO and Strategy, Commvault

“Amazon S3 support for AWS PrivateLink allows Rubrik’s customers to secure network traffic from on-premises workloads to Amazon S3, greatly minimizing threat exposures experienced over the public internet. Utilizing AWS Direct Connect or VPN, customers can use private IP connectivity to connect to S3 via the Amazon private network, all while simplifying network management. This frictionless architecture allows our mutual customers to rapidly exploit a best of breed data management solution backed by Rubrik and AWS.”
Jerome Noll, Director of Alliances, Rubrik

“With Nasuni’s support for AWS PrivateLink for Amazon s3, customer’s can deploy Nasuni’s file storage on AWS faster than before, especially in hybrid cloud environments where critical infrastructure is restricted to the company’s domain namespaces. For these deployments, the on-premises Nasuni’s Edge appliances are truly integrated with S3 under one customer-controlled domain that can avoid the public internet, a preferred security model for many of our customers.”
Russ Kennedy, Chief Product Officer, Nasuni
AWS Data and Analytics Partners
AWS Partners that provide data analytics and data warehousing solutions have seen similar benefits with Amazon S3 support for AWS PrivateLink.
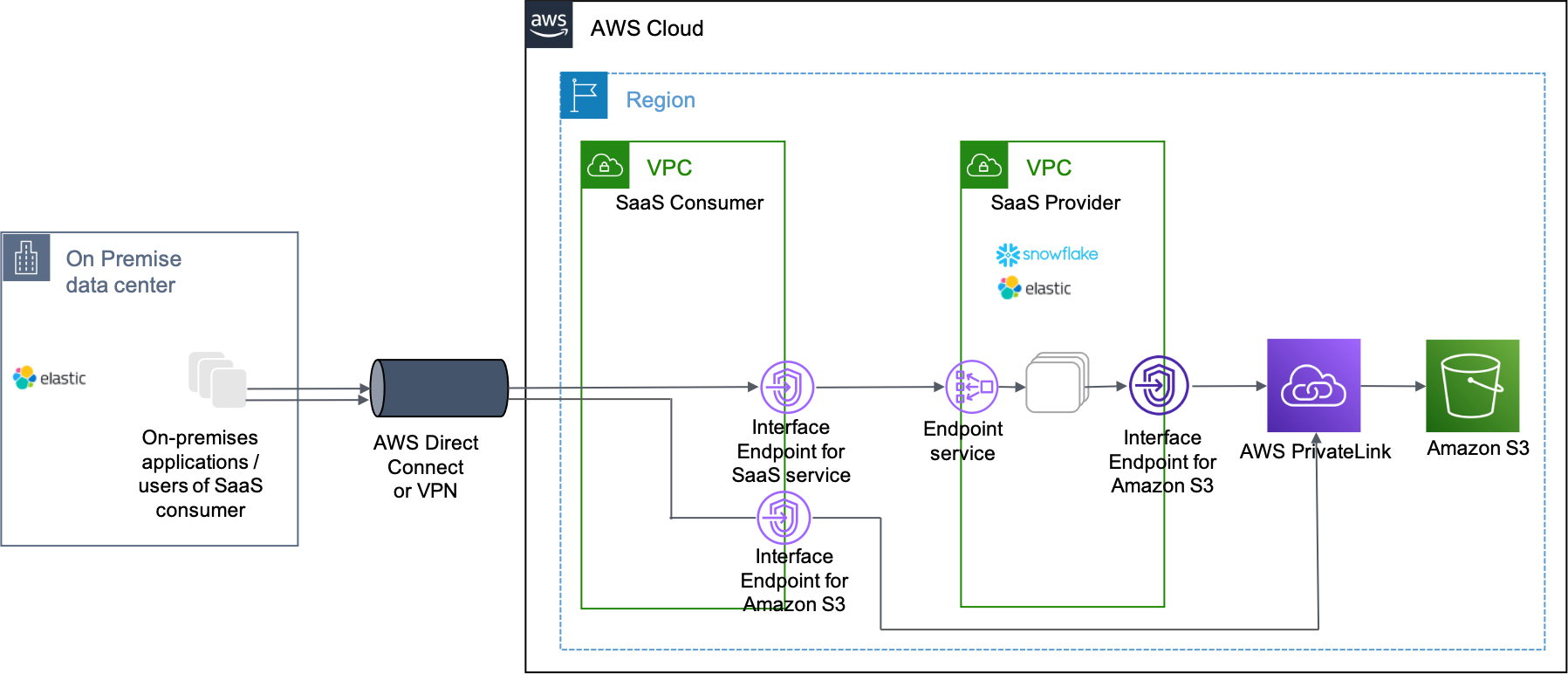
Secure VPC connectivity from clients is critical for customers of Snowflake and Elastic. As shown in the preceding architecture diagram, clients running on-premises or inside the VPC can now access Amazon S3 privately via AWS PrivateLink.
Partners highlight the benefits in their own words:

“Many of today’s organizations still struggle to mobilize all of their data in service of their enterprise. Data Cloud helps our customers connect to massive amount of data, creating a powerful global data network effect for mobilizing data. Amazon S3 support for AWS PrivateLink greatly simplifies and enhances security for our customers in this data network effect by providing private connectivity to Snowflake environments.”
Vikas Jain, Product Manager, Snowflake

“Elastic Cloud customers expect the highest level of security from our products. One of the common asks from Elastic customers is secure connectivity from their VPCs to Elastic Cloud on AWS. Integration with AWS PrivateLink helps us serve these customers while meeting their highest bar for security and ease of use. With Amazon S3 being a prevalent service in a lot of Elastic Cloud on AWS architectures for our users, we are extremely excited that our users can now double down on security across the architecture by leveraging Amazon S3 support for AWS PrivateLink”
Shubha Anjur Tupil, Senior Product Manager, Elastic
AWS DevOps Partners
Hashicorp provides infrastructure automation tools and their Terraform product that enables customers to deploy infrastructure as code, supports configuring Amazon S3 support for AWS PrivateLink.
Hashicorp highlights this support in the following quote:

“HashiCorp Terraform is an infrastructure as code automation tool providing a consistent workflow to provision and manage AWS infrastructure with support for over 600 AWS resources. We are excited to have Terraform provide a declarative option for configuring Amazon S3 interface endpoints via AWS PrivateLink, allowing you to configure, read from, and write to your S3 buckets over a private connection from on-premises or inside a VPC.”
Burzin Patel, VP Global Alliances, Hashicorp
Conclusion
Amazon S3 support for AWS PrivateLink helps customers simplify their network architecture for privately connecting to Amazon S3 from applications running on premises or inside a VPC. AWS PrivateLink is available at a low per-GB charge for data processed and a low hourly charge for interface VPC endpoints. For pricing details, please visit AWS PrivateLink pricing.
Thanks to the AWS Partners in this post for lending their voices. We look forward to working together with our partners to help customer workloads on Amazon S3.
For implementation details on using Amazon S3 support for AWS PrivateLink with a solution provided by an AWS Partner, refer to the respective AWS Partner documentations regarding the solution. If you have any comments or questions, don’t hesitate to leave them in the comments section.