AWS Partner Network (APN) Blog
How to Automate and Secure Branch Office Connectivity to AWS with Cisco SD-WAN
By Gayathri Chandrasekaran, Software Development Manager at Cisco
By Nikolai Pitaev, Sr. Technical Marketing Engineer at Cisco
By Muffadal Quettawala, Partner Solutions Architect at AWS
 |
 |
 |
Combining SD-WAN with cloud-native applications on Amazon Web Services (AWS) has presented a need to connect your SD-WAN network to applications running in the cloud. As a result, traditional WAN architectures with expensive MPLS circuits have evolved into SD-WAN architectures utilizing cloud-native networks and services.
In this post, we will explore how customers can leverage native integrations from Cisco Systems, an AWS Advanced Technology Partner, that work with AWS network services to interconnect branches over the AWS network backbone.
In an earlier blog post, we described steps and shared custom automation scripts for deploying multiple SD-WAN architectures with Cisco SD-WAN and AWS Transit Gateway.
We’ll go a step further here and demonstrate how the Cisco vManage 20.3 software release natively integrates with AWS Transit Gateway and AWS Transit Gateway Network Manager to interconnect branches over the AWS network backbone. This further simplifies connectivity, segmentation, monitoring, and security of your SD-WAN network.
Using the Cisco Cloud OnRamp for Multi-Cloud feature in Cisco vManage 20.3 software release, customers can seamlessly:
- Use Cisco SD-WAN vManage to connect their SD-WAN networks with AWS Transit Gateway.
- Simplify network segmentation using Cisco vManage to program AWS Transit Gateway route tables.
- Utilize the AWS global backbone to connect SD-WAN networks globally using AWS Transit Gateway inter-region peering.
- Monitor branch and AWS SD-WAN network resources with AWS Transit Gateway Network Manager and Cisco vManage.
- Inspect internet-bound traffic in their SD-WAN networks with integration between Cisco SD-WAN and Cisco Umbrella cloud-delivered firewall.
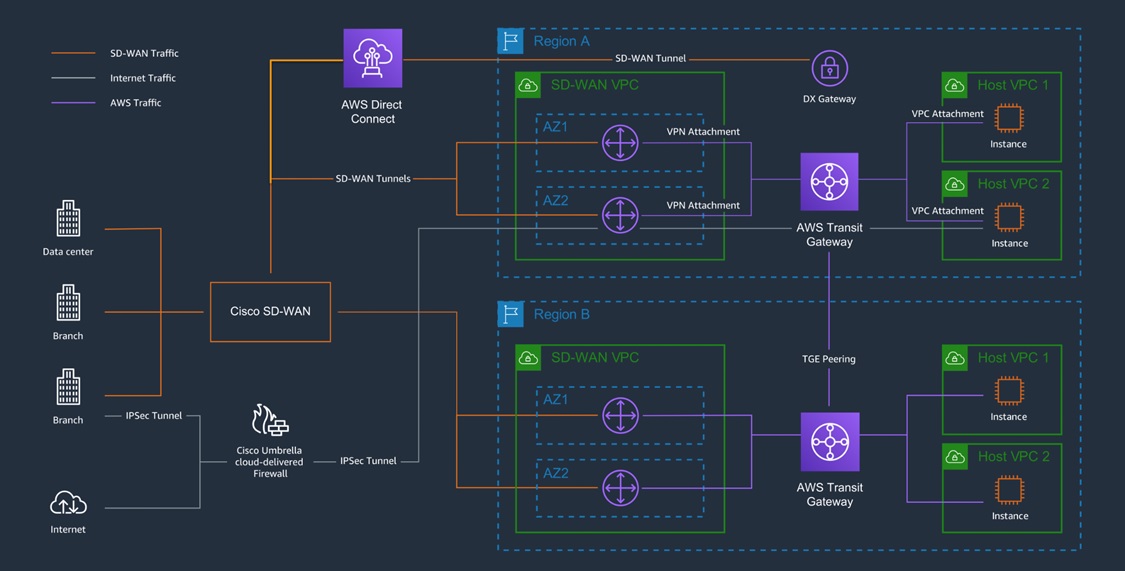
The diagram below depicts a reference architecture of Cisco SD-WAN on AWS:
- SD-WAN branches connect with cloud-hosted applications in a hub and spoke topology, with the SD-WAN overlay traffic terminating on shared SD-WAN virtual private clouds (VPCs) that host redundant Cisco SD-WAN cloud routers.
- The SD-WAN VPCs connect with AWS Transit Gateways used for routing and segmenting AWS traffic from branches to the applications.
- Branch and/or application traffic between regions traverse the AWS backbone via peering connections between AWS Transit Gateways.
- Internet egress traffic from the branches or applications can be routed to Cisco Umbrella Cloud-delivered firewall for inspection. The integration between Cisco Umbrella with Cisco SD-WAN seamlessly builds IPSec tunnels to route internet traffic via the SaaS-delivered Umbrella firewall.
Figure 1 – Cisco SD-WAN reference architecture on AWS.
Connect Your SD-WAN Network to AWS
Using Cisco Cloud OnRamp for Multi-Cloud, connecting the SD-WAN network to AWS is a simple four-step process.
Step 1: Setup
Provide Cisco vManage access permissions into your AWS account(s). As a best practice, use AWS Identity and Access Management (IAM) roles with scoped down permissions.
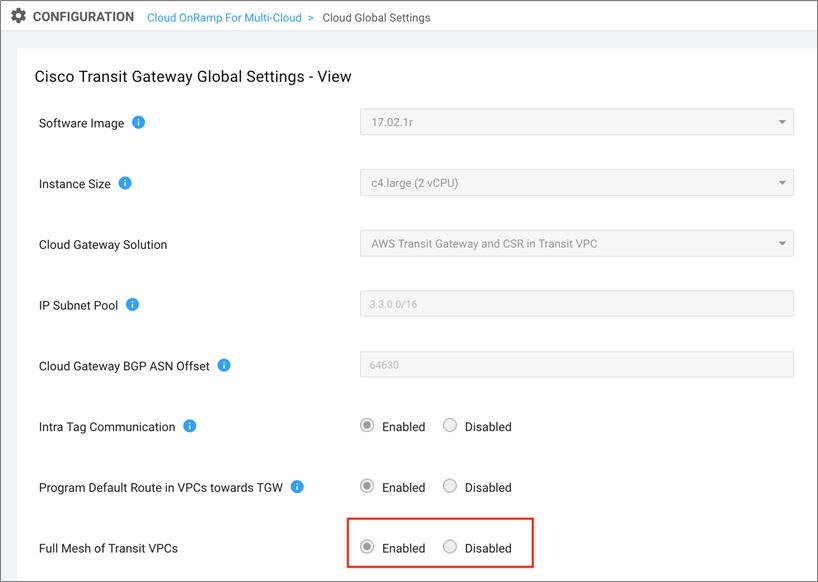
Next, specify the configuration settings for the CSR 1000V SD-WAN router:
- The software image version for the CSR 1000V routers in the Transit VPC.
- Instance size.
- Subnet pool used for the transit VPC creation.
- Border Gateway Protocol (BGP) Autonomous System Number (ASN) for AWS Transit Gateway.
- Enable VPC tags for communication between VPCs.
- Enable default route addition in the main route table of the application VPC pointing to TGW as the next hop.
Step 2: Discover
Discover application VPCs across AWS regions:
- Select application VPCs to connect to your cloud SD-WAN network.
- Add tags to application VPCs for management purposes.
Note that tags can map to multiple VPCs in the same or different regions. Using tags is recommended as Cisco vManage uses tags to manage branch to VPC and/or VPC to VPC communication.
Step 3: Manage
Configure vManage to deploy an SD-WAN VPC with a pair of CSR 1000V SD-WAN routers. Note that Cisco vManage orchestration of SD-WAN tunnels from colocation facilities over AWS Direct Connect into AWS Transit Gateway is not supported in release 20.3/17.3.1.
- Configure Cisco vManage to deploy a new AWS Transit Gateway.
- Connect the SD-WAN VPC with the AWS Transit Gateway via a virtual private network (VPN) attachment.
Note that service-side (branch VPN) routes from the SD-WAN network are propagated into the AWS Transit Gateway route table via BGP.
Also, traffic between CSR 1000V SD-WAN router and AWS Transit Gateway can be scaled by Equal Cost Multi Path (ECMP) load balancing traffic across multiple IPSec VPN tunnels or VPN attachments between the CSR 1000V SD-WAN router and AWS Transit Gateway.
Figure 2 – Configuring SD-WAN cloud gateway through vManage.
Step 4: Intent Management
In this step, you configure Cisco vManage to:
- Segment traffic between service-side (SD-WAN branches, data centers) and application VPCs.
- Segment traffic between application VPCs.
Figure 3 – Configuring traffic segmentation through vManage.
Connect Your SD-WAN Shared VPC to an Existing AWS Transit Gateway
Customers can connect to an existing AWS Transit Gateway using the following manual steps:
- Use Cisco vManage Cloud OnRamp for Multi-Cloud to deploy an SD-WAN VPC in your AWS account.
- Update CSR 1000V SD-WAN router IPSec and BGP feature template in Cisco vManage with the Site-to-Site (S2S) VPN attachment configuration details of the existing AWS Transit Gateway.
- Use Cisco vManage to apply the CSR 1000V SD-WAN router configuration template.
- In your AWS Account SD-WAN VPC, configure route in SD-WAN VPC to point to the existing AWS Transit Gateway.
- From your AWS account, update the existing AWS Transit Gateway route table associations and propagations.
Native support on Cisco vManage for network connectivity orchestration to existing AWS Transit Gateway will be supported in the 20.4 release.
Simplify Network Segmentation
Cisco vManage 20.3 provides the simplicity to segment network traffic from branch to cloud via an easy-to-use user interface. Cisco vManage automatically programs the branch VPNs routes, SD-WAN VPC routes, and AWS Transit Gateway route table associations and propagations based on your user interface (UI) selections.
The examples below demonstrate how to configure network segmentation scenarios via vManage Cloud-On-Ramp for Multi-Cloud > Intent Management > Connectivity UI.
The nomenclature used is described below:
- Cisco_SDWAN: SD-WAN Shared VPC with CSR 1000V SD-WAN routers
- ENG-VPC, Finance-VPC, and HR-VPC: Applications residing in AWS
- VPN1 and VPN2: Service-side (Branch to AWS SD-WAN) VPNs
Full Connectivity Between HR-VPC, ENG-VPC, and Branch VPNs
Figure 4 defines a connectivity model where all branches can communicate with all applications and all applications can communicate with each other.
The rows represent the source while the columns represent the destination. To configure this using Cisco vManage, define an intent selection between branch VPNs, and application VPCs as shown in green:
- In this case, branch VPN1 and branch VPN2 can both communicate with ENG-VPC and HR-VPC.
- Additionally, HR-VPC and ENG-VPC can communicate with each other.
Figure 4 – Configuring full north-south and east-west connectivity.
The AWS Transit Gateway associations, propagations, and route table are transparent to the user. Cisco vManage automates the orchestration using AWS APIs, thereby shielding the complexity from the user.
Figure 5 – AWS Transit Gateway routes for full connectivity.
Segmented Connectivity Between SD-WAN Branches and Applications
Figure 6 defines a connectivity model where you would like to segment the traffic from branched to cloud-hosted applications. Additionally, you don’t want applications to be able to communicate with each other. The rows represent the source and the columns represent the destination.
To configure this using Cisco vManage, define an intent selection between branch VPNs, and application VPCs:
- In this case, branch VPN1 can only communicate with ENG-VPC and branch VPN2 can only communicate with HR-VPC.
- HR-VPC and ENG-VPC cannot communicate with each other.
Segmentation policies are enforced through advertisement of filtered routes in respective AWS Transit Gateway route domains.
Figure 6 – Configuring segmentation between branches and applications.
The AWS Transit Gateway associations, propagations, and route table are transparent to the user. Cisco vManage automates the orchestration using AWS APIs, thereby shielding the complexity from the user.
Figure 7 – AWS Transit Gateway routes for segmented connectivity.
Using the AWS Global Backbone Between Regions
Customers want to build and optimize private networks on the AWS global backbone for inter-region branch-to-branch SD-WAN traffic. Utilizing the AWS global backbone enables global reach within minutes, and provides consistent and redundant network links for your SD-WAN traffic.
Cisco vManage leverages the inter-region AWS Transit Gateway peering feature to:
- Route inter-region branch-to-branch traffic over the AWS global backbone.
- Route inter-region VPC-to-VPC traffic over the AWS global backbone.
Figure 8 provides a preview into how customers can enable this feature with a few clicks. When enabled, the AWS backbone is represented as a Transport Location (TLOC) interface with a unique color in the SD-WAN overlay network.
Customers can choose to traverse branch-to-branch or application (VPC-to-VPC) traffic using SD-WAN centralized policies.
When using this feature, Cisco vManage will orchestrate the following in your AWS account:
- Deploy and connect AWS Transit Gateways in your regions of choice.
- Configure routes to transparent route application VPC traffic across regions via the AWS Transit Gateways.
- Route branch traffic to the AWS Transit Gateway in the closest region.
- Configure static routes on each AWS Transit Gateway to point to the peered AWS Transit Gateway as the next hop for inter-region branch to branch traffic.
Figure 8 – Configure AWS Transit Gateway inter-region peering through vManage.
Support for this feature is targeted in Cisco vManage release 20.4 end of 2020.
Simplify Network Management
Large enterprise SD-WAN deployments have independent, and sometimes siloed, administrative business units with dedicated roles and responsibilities.
For example, network administrators are responsible for managing network infrastructure and configuring access controls, whilst application developers are focused on writing code utilizing the infrastructure provisioned for them.
This division of responsibility presents a network management and monitoring challenge. In some cases, the SD-WAN service may be outsourced to a third-party service provider with limited visibility to the AWS operator.
Cisco vManage 20.3 integrates with AWS Network Manager to populate elements of your global SD-WAN network, such as branch devices, links, VPN and VPC attachments, and AWS Transit Gateways into AWS Network Manager.
Figure 9 – Link to AWS Transit Gateway Network Manager from vManage.
This unified view of branch and cloud sites enables a single visualization of both the physical and virtual worlds.
Optionally, events and metrics from these network elements can be integrated, providing end-to-end monitoring of your global network. This significantly accelerates network troubleshooting and operations.
Figure 10 – Visualize your global network in AWS Transit Gateway Network Manager.
Inspecting Internet Traffic of Your SD-WAN Network
Cisco SD-WAN natively integrates with Cisco Umbrella Secure Internet Gateway (SIG) for direct internet traffic (DIA) inspection from the SD-WAN edge (branch/DC, home, etc.) egress to the internet. Cisco SD-WAN edge routers automatically establish IPsec tunnels to Umbrella SIG and send DIA traffic through the SIG.
Internet egress traffic inspection from AWS applications will also be supported. Cisco vManage will orchestrate internet egress traffic inspection to Umbrella SIG from the AWS application VPCs via the SD-WAN Shared VPC.
Support for this feature is targeted in Cisco vManage release 20.4 end of 2020.
Customer Success: ENGIE
ENGIE, a global reference in low-carbon energy, is headquartered in France and employs more than 170,000 employees worldwide across 50 countries.
Their networking team needed to provide connectivity for domestic networks around the world, while adhering to different regulatory and compliance standards. ENGIE also has different firewall policies for subsidiaries and each partner. Traffic segmentation needs to be strictly maintained and inspected between the different constituents.
ENGIE deployed the Cisco SD-WAN and AWS Transit Gateway solution, which enabled them to create end-to-end connectivity between users and cloud-hosted apps and apply consistent network segmentation and data security policies to traffic flows across all regions.
In doing so, ENGIE was able to increase their overall network visibility and control and accelerate new site onboarding to under 15 days.
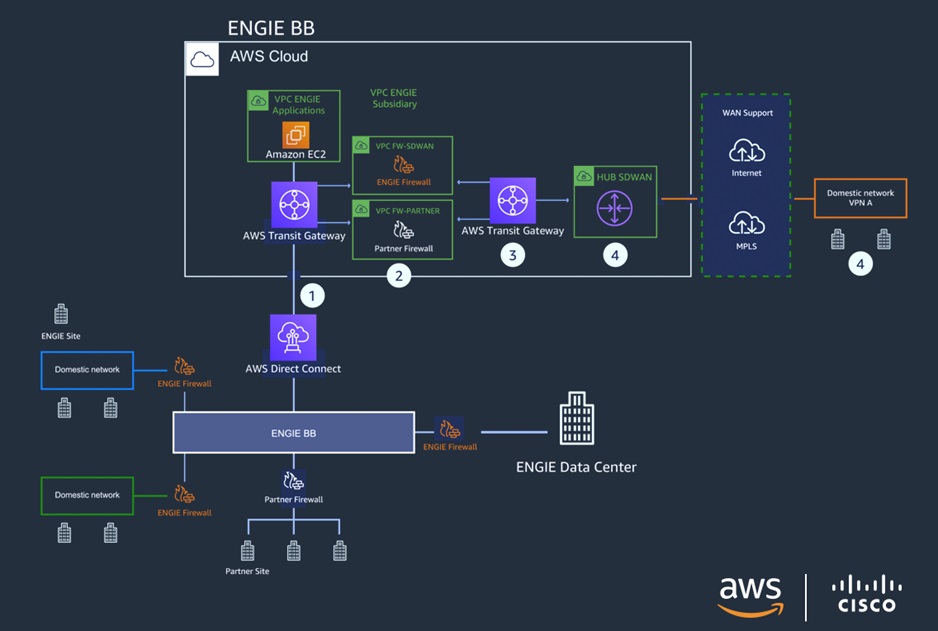
Engie’s global network architecture is detailed in the architecture below:
- ENGIE backbone is extended to AWS via AWS Direct Connect and AWS Transit Gateway.
- ENGIE and partner firewalls inspect traffic between two AWS Transit Gateways.
- The second AWS Transit Gateway acts as an underlay for the VPN tunnels established between the Cisco SD-WAN routers and the firewall.
- Sites are connected to the ENGIE network via the shared SD-WAN VPC with Cisco SD-WAN routers.
Figure 11 – ENGIE’s global network deployment.
To learn more about ENGIE’s experience, check out our AWS Partner webinar.
Conclusion
The Cisco vManage 20.3 release is an exciting step forward in helping customers simplify and automate their global networks on AWS.
Within minutes, customers can securely deploy their SD-WAN networks by seamlessly utilizing AWS as the global backbone for their underlay network for their branch-to-cloud and branch-to-branch traffic. Additionally, you can consistently visualize and monitor global networks with both Cisco vManage and AWS Network Manager.
Cisco and AWS make it easy to automate and view end-to-end SD-WAN connectivity through a single, unified, automated interface. This combined solution offers ease of management, and increased security through network segmentation to customers across the board.
For the latest enhancements, refer to cisco.com/go/aws.
.
 .
.
Cisco Systems – AWS Partner Spotlight
Cisco is an AWS Advanced Technology Partner providing a range of products for transporting data, voice, and video within buildings, across campuses, and around the world.
Contact Cisco | Solution Overview | AWS Marketplace
*Already worked with Cisco? Rate the Partner
*To review an APN Partner, you must be an AWS customer that has worked with them directly on a project.