AWS Partner Network (APN) Blog
How to Integrate AWS Single Sign-On with MongoDB Atlas
By Igor Alekseev, Sr. Partner Solutions Architect at AWS
By Manish Agarwal, Sr ISV Solutions Architect at AWS
 |
 |
 |
AWS Single Sign-On (SSO) makes it easy to centrally manage SSO access to multiple Amazon Web Services (AWS) accounts and business applications.
With AWS SSO, users sign in to a central portal to access all of their AWS accounts and applications.
If you’re an IT administrator of a growing workforce, your users will require access to a growing number of business applications and AWS accounts. You can use AWS SSO to create and manage users centrally and grant access to AWS accounts and business applications.
In this post, we will show you how to configure MongoDB Atlas to authenticate using AWS SSO.
Instead of having to sign in separately to MongoDB Atlas Control Plane, with this configuration enabled users can access the MongoDB Atlas user interface (UI) with their corporate credentials using AWS SSO. This delivers a better user experience without the need for managing separate sets of credentials.
MongoDB is an AWS Advanced Technology Partner with the AWS Data & Analytics Competency. MongoDB Atlas is the global cloud database service for modern applications. It provides best-in-class automation and proven practices for availability, scalability, and compliance with the most demanding data security and privacy standards.
Architecture Diagram
The diagram below depicts the configuration we will implement in this post, and how AWS SSO and MongoDB Atlas interact.
Additionally, on-premises Active Directory (AD) can be connected to AWS SSO, which further simplifies SSO configuration.
Security Assertion Markup Language (SAML) works by passing information about users, logins, and attributes between the identity provider and service providers. Each user logs in once to Single Sign-On with the identify provider, which can pass SAML attributes to the service provider when the user attempts to access those services.
The service provider then requests the authorization and authentication from the identify provider. Since both of those systems speak the same language (SAML), the user only needs to log in once.
Figure 1 – AWS SSO and MongoDB Atlas architecture diagram.
Each identity provider and service provider need to agree upon the configuration for SAML. Both ends need to have the exact configuration for the SAML authentication to work.
AWS SSO supports SAML 2.0, meaning you can extend SSO access to MongoDB Atlas by using the AWS SSO application configuration wizard. This is possible because both MongoDB Atlas and AWS SSO support SAML 2.0.
Through the AWS Management Console, administrators can configure and manage permissions for SSO-enabled applications like MongoDB Atlas.
In our configuration, MongoDB Atlas acts as an SAML-enabled application while AWS SSO acts as an identity provider.
Integrating MongoDB Atlas with AWS SSO
Here are the steps to configure MongoDB Atlas SSO to integrate with your AWS SSO.
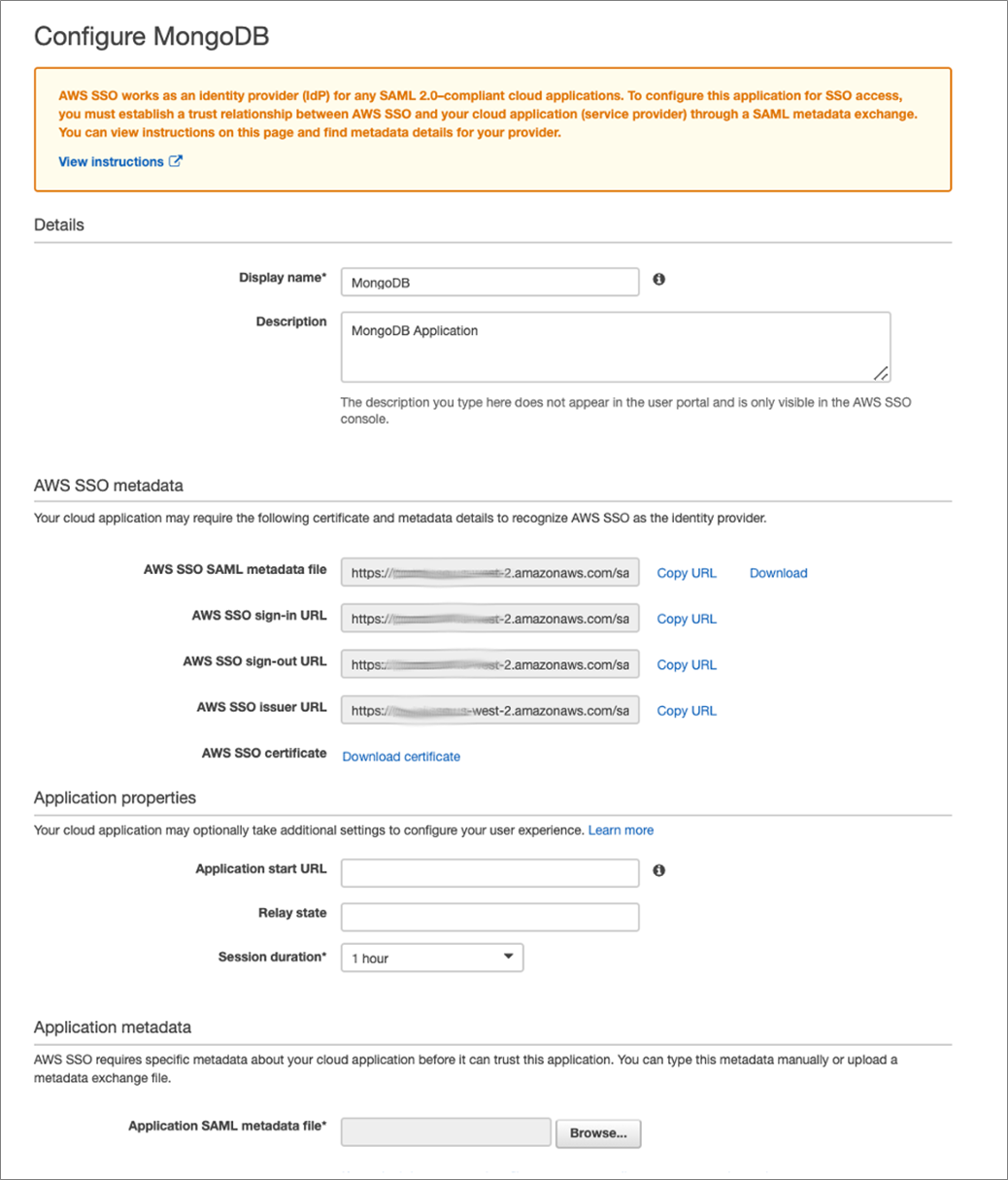
- First, we’ll create the SAML Identity Provider, which is AWS SSO. To do that, log in to AWS console and navigate to AWS SSO.
. - Select the Welcome to AWS Single Sign-On page and Applications from the left pane.
. - Next, select Add a New Application and search for “MongoDB” in the Application Catalog. Choose the MongoDB application icon and click Add Application.
- These values should be set up in MongoDB Atlas while creating the identity provider: AWS SSO Issuer URL and AWS SSO Sign-In URL.
. - Next, log in into the MongoDB Atlas UI and navigate to your organization form the Access Manager drop-down.
- Select Settings and click on Manage Federation Settings.
. - Next, select the identity providers, and click on Add Identity Provider.
. - Provide the Issuer URI and Single Sign-On URL.
- Now, download the metadata file and copy the Assertion Consumer Service URL and Audience AUI. These need to be updated in SAML Identity provider “AWS SSO.”
- Click on Add Domains to add an associated domain. Select domain and click on Submit.
- Click on Activate to activate the identity provider.
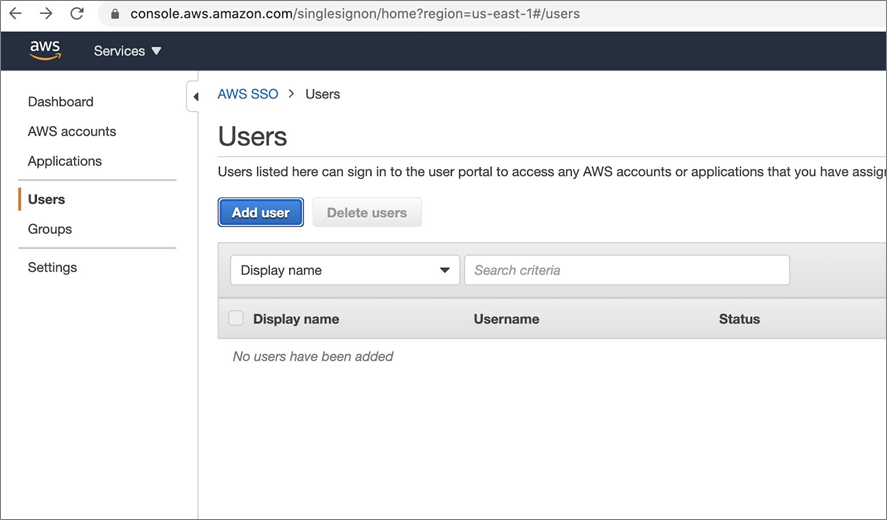
. - Now, in the AWS SSO Console, click on Users in left menu and click on Add user.
- Enter your details and click on the Next:Groups button.
. - Associate it to a group and click on Add user to finish.
. - Finally, the user is created. Note the User Portal URL, as we’ll use it later to login into MongoDB Atlas.
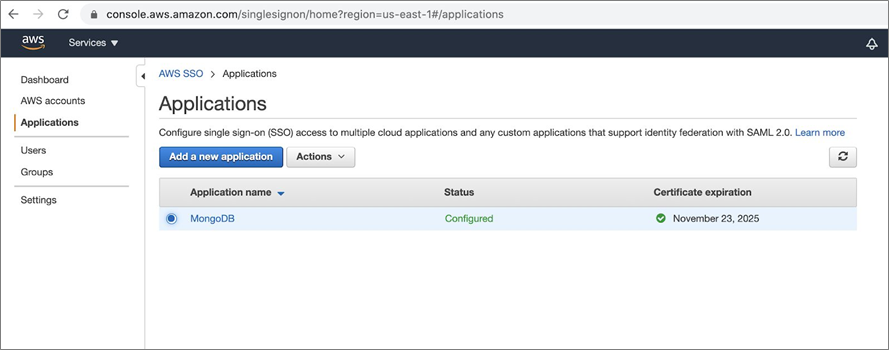
- Click on Services > AWS SSO > Applications, and then select the application.
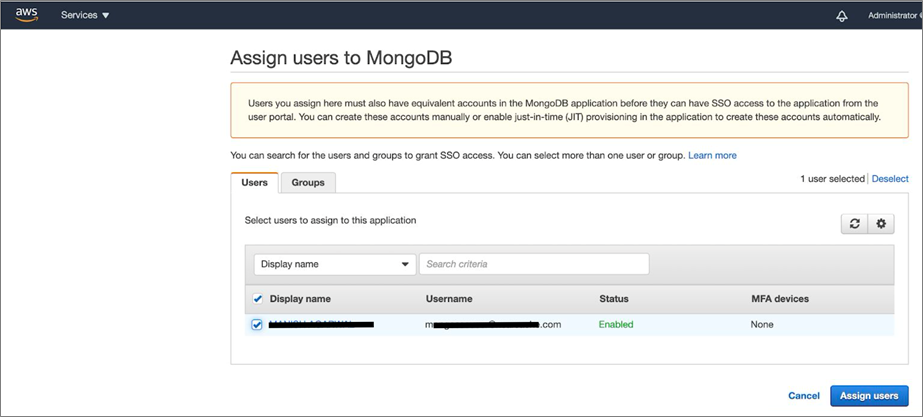
- Now, click on the Assigned users tab and then the Assign users button.
. - Select the user you created and click on the Assign users button.
- Now, sign in by opening the user Portal URL in an incognito window. It will redirect to the AWS SSO endpoint for authentication unless already signed in.
- Enter login credentials for the AWS SSO user.
. - Finally, the user is redirected back to MongoDB Atlas and is now able to log in to MongoDB atlas using AWS SSO credentials. If you were signed in already, you’ll be redirected to the MongoDB Atlas home page without being prompted for a password.
Conclusion
In this post, we explained how to configure MongoDB Atlas with AWS Single Sign-On. AWS SSO provides a user portal so your users can find and access all of their assigned accounts and applications from one place, using their existing corporate credentials.
AWS SSO is integrated with AWS Organizations to enable you to manage access to AWS accounts in your organization. Try out MongoDB Atlas with AWS SSO using the links below:
- To start using AWS SSO, navigate to the AWS SSO console.
- Sign up for MongoDB Atlas to deploy a free cluster and connect securely with your AWS applications and services.
- Learn more about AWS Single Sign-On.
.
.
MongoDB – AWS Partner Spotlight
MongoDB is an AWS Competency Partner. Their modern, general purpose database platform is designed to unleash the power of software and data for developers and the applications they build.
Contact MongoDB | Partner Overview | AWS Marketplace
*Already worked with MongoDB? Rate the Partner
*To review an AWS Partner, you must be an AWS customer that has worked with them directly on a project.