AWS Partner Network (APN) Blog
Protect, Detect, and Respond to Ransomware with Presidio’s Ransomware Mitigation Kit
By Tom Hanley, Sr. Solutions Architect, Public Sector – AWS
By Adam Book, Principal Architect, Cloud Adoption – Presidio
By Dan Lewandowski, National Solutions Architect – CrowdStrike
By Joe Shawfield, Principal Cloud Architect and Consultant – Atayo Group
 |
| Presidio |
 |
Organizations are under heightened threat from ransomware incidents as “ransomware as a service” has increased in prevalence, duration, and cost.
Frequent attacks occur within the public sector, targeting critical functions such as elections, public services like wastewater or recycling services, criminal justice information services (CJIS), and health and human services (HHS). These incidents can sometimes have deadly consequences, especially when they impact hospitals and other critical services.
Security teams are looking to further mitigate the ransomware threat beyond mere ransomware insurance, which only addresses a portion of the impact and has become increasingly expensive and difficult to acquire.
Teams typically employ some manner of antivirus and backup to prevent, detect, and recover from an event, but these are pinpoint solutions that generally operate independently and require manual coordination.
Complicating matters is the reliance of traditional antivirus on signatures, which contributes to delayed recognition of threats and lack protection from zero-day attacks.
Organizations need an integrated approach that addresses the NIST CSF pillars. They need a means to close the speed advantage between the attackers and defenders. Firms are looking for a synchronous way to detect and protect their institutions from the impact of breaches and return their operations to an online state as quickly as possible.
Furthermore, they need trusted partners equipped to work through the business and technical requirements creating a solution that is tailored to their specific needs. Presidio, Atayo, and CrowdStrike are such partners, having decades of combined experience building security solutions and working with Amazon Web Services (AWS).
This post walks you through the components of an offering that was first announced at re:Invent 2021. It combines together the forces of:
- CrowdStrike Falcon Pro which combines next-generation antivirus (NGAV) and endpoint, detection, and response (EDR) in both managed and unmanaged variants.
- AWS Elastic Disaster Recovery Service (AWS DRS) which enables pilot light disaster recovery (DR).
- Presidio DRS Orchestration Layer (DOL) which orchestrates response activities between CrowdStrike Falcon Pro and AWS DRS.
These elements come together to allow an organization to quickly identify a ransomware bad actor, determine the point-in-time the incident occurred, and then support dialing-back/restoring the affected endpoints to a point-in-time just before the incident.
In doing so, business operations can be rapidly restored rather than taking days or weeks, greatly reducing the organizational impact and cost of the incident.
Solution Overview
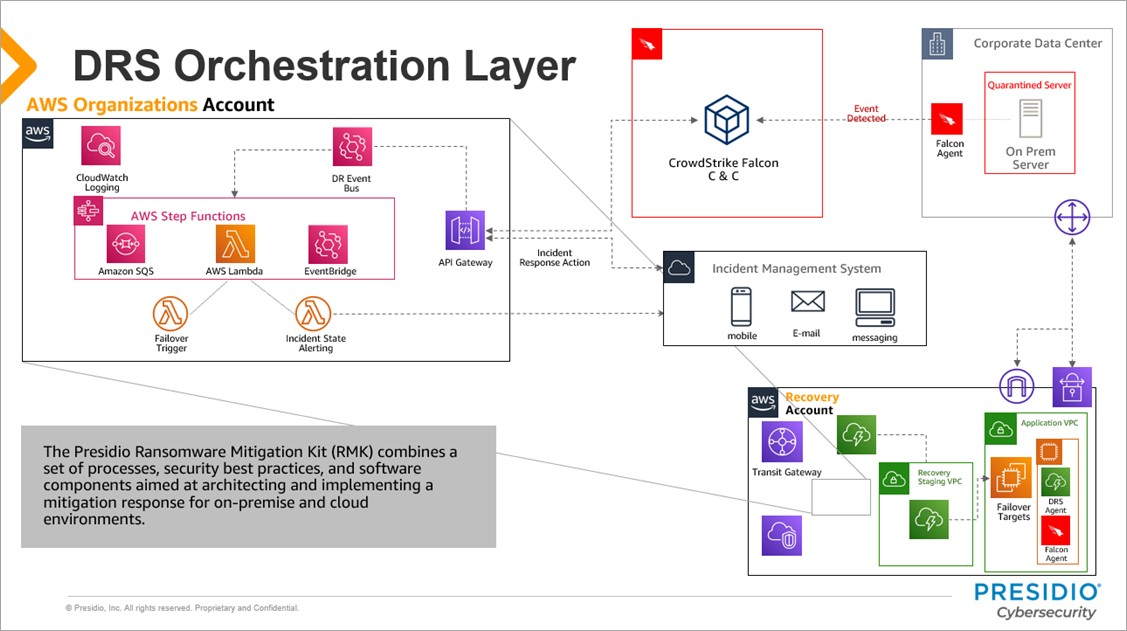
At the heart of this solution is a series of AWS services and Presidio code named the DRS Orchestration Layer (DOL). This middleware provides the “glue” that manages, logs, and coordinates the ransomware response.
Figure 1 – DRS Orchestration Layer overview.
As seen in the diagram above:
- An intrusion is detected by CrowdStrike Falcon Pro. Notifications are sent to the Falcon console for the impacted servers.
- CrowdStrike kicks off a workflow automation that will send an incident detection event to the Presidio’s DOL.
- Incident payload is ingested into AWS via Amazon API Gateway. Authentication is handled by Amazon Cognito.
- AWS Step Functions associate the impacted servers to the underlying business workloads and orchestrate the parsing of the incident payload. Options for AWS DRS failover execution are determined.
- Incident alerting is generated and sent to the incident management system (IMS). The incident response (IR) team is notified and prompted to choose the business workloads to mitigate along with the points-in-time to failback to.
- A response is returned via API Gateway. The original servers associated with the workloads are quarantined in CrowdStrike, taking those workloads offline to prevent proliferation of the attack. A snapshot restore point is identified and sent with the response.
- Presidio’s DOL triggers a failover of the workloads into AWS based on user input from Step 5.
- AWS DRS launches a recovery job for the affected servers and instances are hydrated into the target region.
- Connectivity is established and users are repointed to the failover server location, restoring business operations for the impacted workloads.
Laying the Right Foundation
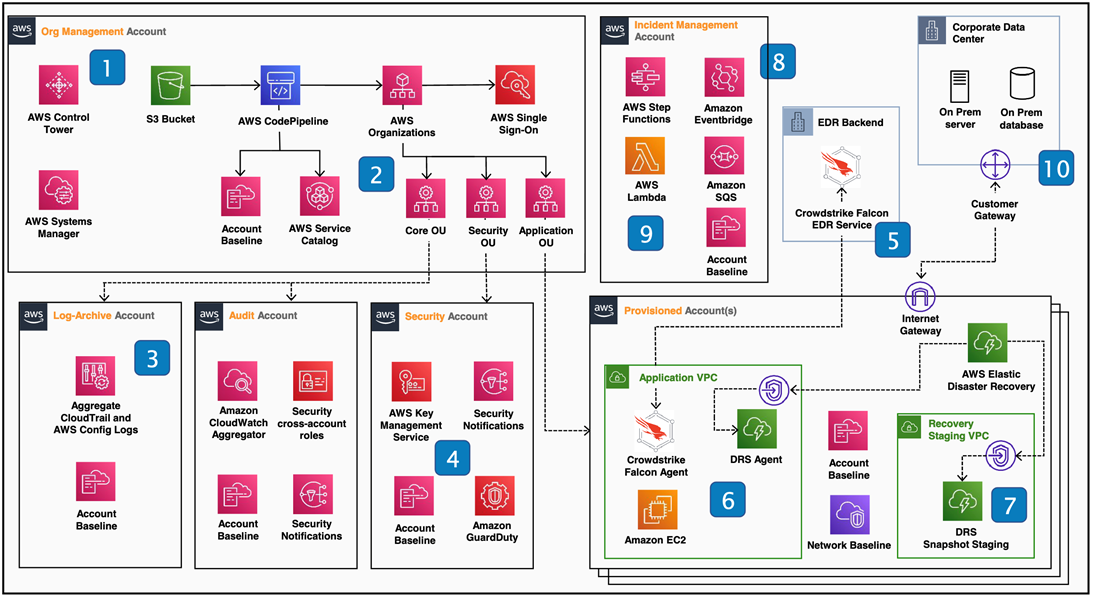
A solution built to respond to a security event should itself be secure. Presidio’s Ransomware Mitigation Kit (RMK) is architected from the ground up with security in mind, leveraging AWS Control Tower to have a well-architected landing zone.
Figure 2 – High-level solution overview.
To support best practices, the solution starts with a landing zone (see left side of Figure 2) following the use of AWS Control Tower. The design of this landing zone will be custom tailored based on an organization’s particular needs. This is achieved by Presidio kicking off an engagement via an NIST-based CSF (Cloud Security Framework) gap assessment.
The results will determine not only the necessary technical architecture, but a RACI chart and workflows, as well illustrate who receives notifications and who can make decisions regarding any ransomware incident. The gap assessment also provides a baseline of how an organization measures against NIST’s bar, and a roadmap for further improvement.
Intelligent Protection to Prevent an Attack
The difference between traditional antivirus compared to an NGAV/EDR combined solution, such as CrowdStrike Falcon Pro, is the manner of identifying an attack and, consequently, the speed and reliability of such identification.
Traditional antivirus relies upon periodic scanning looking for signatures (aka identifiable hashes) of malware. The compilation of such signatures comes at a price (the first to see a new attack loses), often times requiring some percentage of the protected clients to become infected.
Organizations then have to hope the reporting, identification, and dissemination of the rogue signatures happens quickly enough to prevent their clients from getting infected.
Compare and contrast that with a combined NGAV/EDR solution. This approach is centered around observation, in real-time, of kernel activity that is indicative of ransomware.
For example, the agent can flag any process it doesn’t recognize that:
- Try to list out the contents of the file system.
- Delete local shadow backups.
- And call an encryption routine or library.
If one of these indicators of compromise (IOCs) are present, it is likely ransomware with its goal to encrypt and damage the environment. This protection can be done locally and intercepted quicker.
CrowdStrike collects over one trillion data points each day from sensors on a wide range of endpoints, and these suspect processes can be correlated and threat intelligence can be disseminated.
Recovering to Before the Incident
The power of this solution is in the orchestrated and controlled manner of response facilitated by Presidio’s DRS Orchestration Layer (DOL). This response is predicated on the idea of the EDR and disaster recovery working together to restore resources in a clean environment at a point-in-time prior to the infection.
Note that most attacks are expected to be thwarted by the NGAV/EDR agent at the outset. If and when an attack penetrates, the EDR component reports the point-in-time it first detected the suspect activity and reports that to the DOL.
The responsible party inside the organization, typically operations security (OpSec), would investigate the message delivered via the IMS and determine not only what action to take in response but also the point-in-time to rollback to should failover be warranted.
AWS DRS takes a pilot light approach to DR, keeping costs low while allowing for granular snapshots with intervals as low as 10 minutes that provide more recovery options for the incident. With EDR and DR agents on the endpoints throughout the course of the snapshots, the failed over workloads will spin up, minus the infection, in a clean and secure environment with continual protection.
Interested parties are encouraged to reach out to RansomwareMitigationKit@presidio.com and/or visit the AWS Marketplace listing.
Presidio – AWS Partner Spotlight
Presidio is an AWS Partner and leading IT services and solutions provider that helps customers accelerate time-to-outcome via agile digital platforms, with technology expertise across cloud, security, modern IT infrastructure, and networking.
Contact Presidio | Partner Overview | AWS Marketplace
*Already worked with Presidio? Rate the Partner
*To review an AWS Partner, you must be a customer that has worked with them directly on a project.