AWS Partner Network (APN) Blog
Streamlining Secrets Management for Enhanced Security Using CyberArk Secrets Hub and AWS
By Chris Smith, Director DevSecOps – CyberArk
By Raj Kulkarni, Sr. Partner Solutions Architect – AWS
 |
| CyberArk |
 |
Speed is the name of the game when it comes to software development, and developers are being asked to work faster than ever before to meet business demands.
At the same time, unauthorized users are increasingly creative and aggressive, seeking out and attacking potential vulnerabilities. Too often, this pushes corporate security teams to be more vigilant, more cautious, and even slowing deployment of new services.
As a best practice, security administrators want all secrets across the organization to be governed by the same processes and automation, regardless of where the secrets will be consumed. However, as organizations evolve with hybrid architectures and build on Amazon Web Services (AWS), their developers want to rely on the native AWS Secrets Manager to simplify development and operations.
In this post, we’ll discuss a jointly developed solution between CyberArk and AWS that was designed to centralize control of secrets, automate rotation, and eliminate vault sprawl for security teams while making no changes to developer workflows.
CyberArk is an AWS Security Competency Partner and AWS Marketplace Seller that is a global leader in identity security. The CyberArk identity solution is CyberArk’s SaaS-delivered identity and access management.
Overview and Background
CyberArk has worked closely with AWS to create a solution that enables security teams to manage secrets and credentials using the CyberArk solutions they already have, while also giving developers using AWS Secrets Manager the same experience they have today.
The result is CyberArk Secrets Hub, which enables identity security teams to centrally manage secrets across all projects, teams, and applications using the security tools they’re already familiar with.
Development teams are often focused on security measures that are specific to their project or app, not the overall enterprise’s security posture. Of course, security teams know what’s needed to protect the enterprise–centralized management of credentials, policy-based rotation, and applying least privilege.
CyberArk Secrets Hub pairs with AWS Secrets Manager to help CISOs and enterprise security teams work towards their goal of securing the entire organization. Security teams can centrally manage secure and rotate application credentials across the enterprise’s entire compute environment from legacy mainframe apps, .NET apps, and Java to AWS Lambda functions and AWS workloads.
CyberArk and AWS Secrets Manager: Better Together
AWS Secrets Manager provides a way for organizations to enable any application running on AWS to securely store and retrieve the credentials they need to access resources, using a set of APIs. First, the application must be authenticated, which is achieved by assigning the application an AWS Identity and Access Management (IAM) role. These roles are defined by an empowered individual and assigned to resources within AWS.
This makes it easy for the application to securely store and retrieve secrets and gives developers what they need. For security teams in large enterprises, though, it gets more complicated with hybrid environments with each potentially managing their own set of secrets when there are multiple AWS accounts and multiple instances of AWS Secrets Manager. Additionally, security teams want automated credential rotation and a centralized view of all credentials used across the enterprise.
CyberArk Secrets Hub, part of the CyberArk Identity Security Platform, acts as a bridge between CyberArk Privileged Access Manager and AWS Secrets Manager to provide a read-only copy of credentials, synced regularly. Now, multiple subsets of credentials can be synchronized to multiple AWS Secrets Manager instances, allowing for segregation and policy management across all AWS accounts.
When AWS Secrets Manager is already used, minimal to no changes are required to workflows and the existing code bases because CyberArk Secrets Hub only acts as a backend agent to synchronize Secrets Manager.
CyberArk Secrets Hub is designed to provide security teams with:
- Visibility into AWS Secrets Manager instances to easily find and manage existing secrets.
- Ability to centrally manage secrets across multiple AWS Secret Manager instances (across multiple AWS accounts) and other vaults, easily and quickly.
- Automated policy-based rotation.
- Support for centralized audit using security information and event management (SIEM).
- Automated capabilities for managing the secrets lifecycle, including the ability to optimize the secrets retirement process.
How it Works
Here’s a breakdown of how CyberArk and AWS solutions work together:
- AWS Secrets Manager: Authenticates application access using IAM roles and retrieves/delivers the appropriate secrets.
- CyberArk Secrets Hub: Serves as an intermediary between AWS Secrets Manager and CyberArk Privileged Access Manager, with the IAM role configured to work with CyberArk Secrets Hub.
- CyberArk Privileged Access Manager: Manages and rotates the credentials, updating them directly in the AWS Secrets Manager instance as well as in the target system.
Automated credential rotation is an important function for managing secrets, and CyberArk automatically uses various plugins, integrations, and approaches to simplify rotation and ensure the credentials used by the target system (for example, the external data provider) are the same as the credentials provided by AWS Secrets Manager to the cloud workload or Lambda function.
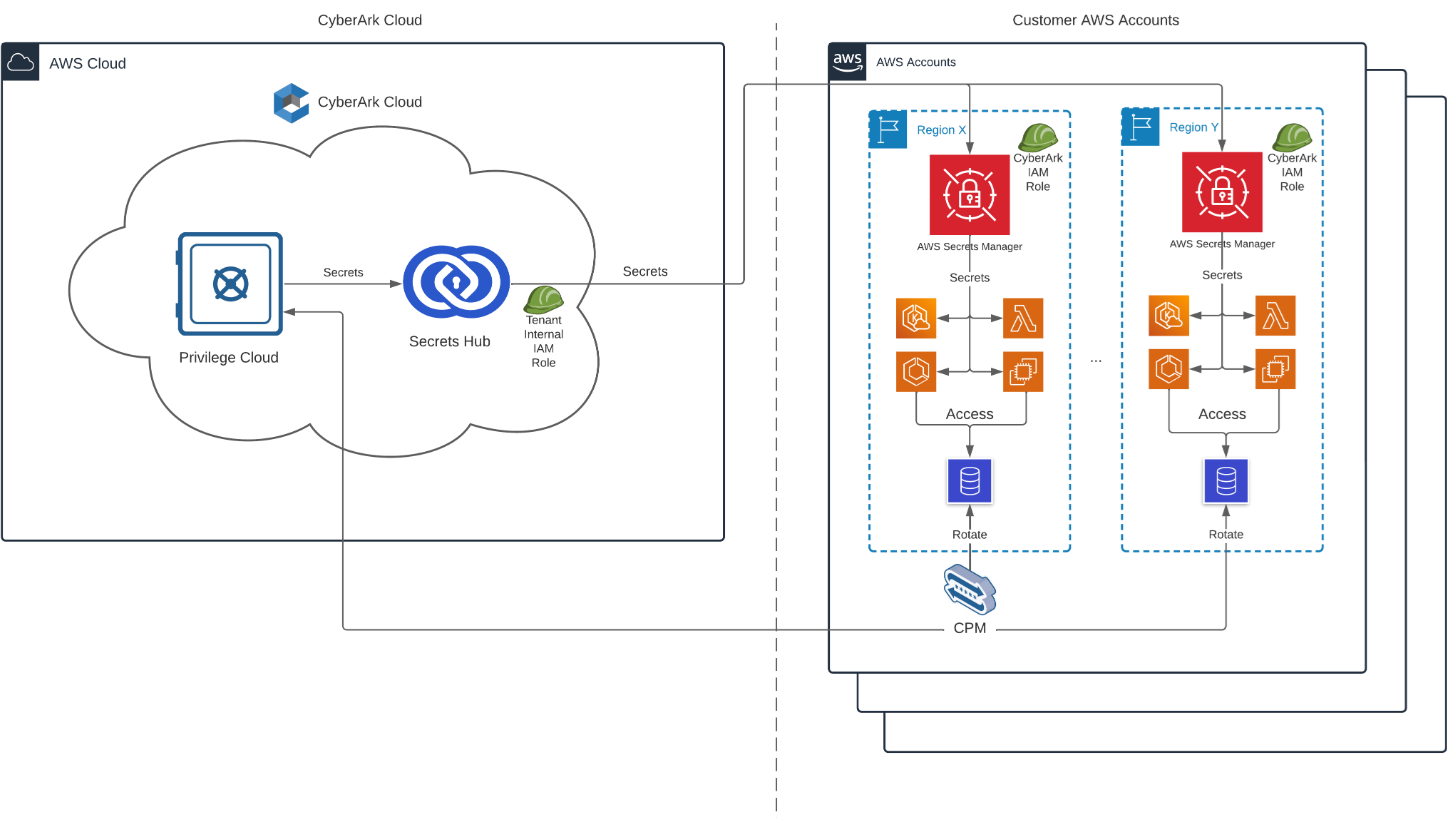
Figure 1 – CyberArk Secrets Hub schematic.
The diagram above describes how secrets are synchronized between CyberArk Privilege Cloud (the SaaS version of CyberArk Privileged Access Manager) and AWS Secrets Manager using CyberArk Secrets Hub.
- Secrets are stored and managed in CyberArk Privilege Cloud.
- Secrets are consumed by developers and workloads from AWS Secrets Manager.
- CyberArk Secrets Hub serves as an intermediary and synchronizes the secrets between CyberArk Privilege Cloud and AWS:
- In the solution, sync targets and sync policies are created to define which secrets need to be synchronized.
- A trust is created between the solution and the relevant AWS Secrets Manager targets using a user created IAM role that provides CyberArk Secrets Hub with the required permissions to write secrets into AWS Secrets Manager.
- CyberArk Secrets Hub synchronizes the secrets at regular intervals, while the CyberArk Privilege Cloud Central Policy Manager (CPM) ensures the rotation of the secrets as defined in their password policy.
For additional information, refer to the documentation for CyberArk Secrets Hub architecture.
Centralized Secrets Management Across Hybrid Environments
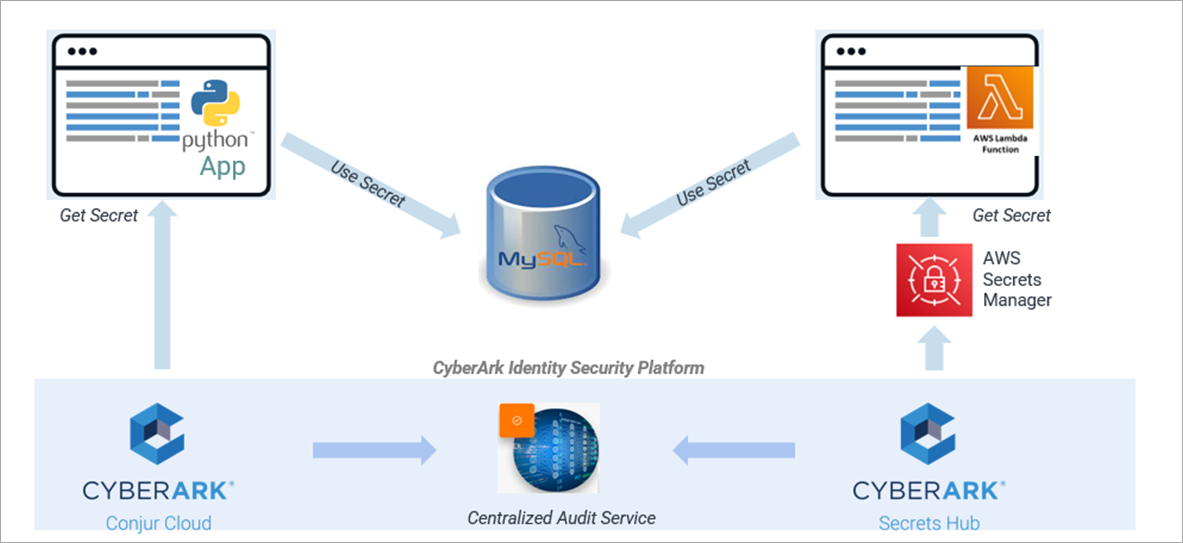
In this hybrid example, the same database needs to be accessed by AWS Lambda functions as well as code running in a data center and other environments outside of AWS.
Given the sensitivity of the data, the goal is to centrally manage which applications have access, rotate credentials based on corporate policy, and maintain a centralized audit of which applications and functions are accessing the resources.
By using CyberArk Secrets Hub, there is minimal change for the AWS developers and codebase. For example, the Lambda function can continue using AWS Secrets Manager to access the credentials needed to connect to the database, while CyberArk Secrets Hub enables the CyberArk security team to meet corporate policy.
Figure 2 – Centrally manage access across hybrid deployment environments.
Getting Started with CyberArk Secrets Hub
If you’re already a CyberArk customer with CyberArk Privilege Cloud or the CyberArk Identity Security Platform, there are just three steps for the security team to follow in order to centrally manage secrets stored in AWS Secrets Manager.
For more details, see a video demo or review the CyberArk Secrets Hub documentation.
Step 1: In CyberArk Secrets Hub, Add the AWS Secrets Manager Sync Target
First, use the CyberArk Secrets Hub user interface (UI) or API to add a sync target which specifies the secrets CyberArk will manage. In this example, we’ll use the UI to specify the AWS account ID, AWS account alias, region, and the CyberArk Secrets Hub IAM role.
Figure 3 – Add sync target from CyberArk Secrets Hub UI.
If you are using the solution for the first time with the AWS account, you’ll need to create an IAM role in the AWS account that CyberArk Secrets Hub can connect to. This is made easy by providing a code snippet that uses an AWS CloudFormation template to set up the IAM role for you. In the CloudFormation console, simply create a stack with the CyberArk template.
Note that while CloudFormation only needs to be run once for each AWS account, running the template requires a high level of privilege, including requiring “role creation” permissions. It would typically be performed by the AWS account admin. For additional information on the CFN and its usage, refer to the CyberArk Secrets Hub documentation.
Step 2: Give CyberArk Secrets Hub Access to the Safe with the Secrets
You also need to put the secrets that you want AWS Secrets Manager to provide access to in a CyberArk safe. A safe is a secure location or vault that holds the secrets that CyberArk manages access and applies policies to.
To give the CyberArk Secrets Hub user access to the safe, use the CyberArk Privilege Cloud console to select the safe and add the user as a member of the safe.
Figure 4 – Assign a CyberArk safe to the ASM instance.
Initially, assign the user with the minimum level of permissions. Note that if there are multiple instances of AWS Secrets Manager, you’ll potentially have multiple safes or multiple users accessing secrets in the same safe.
Permissions include safe management tasks such as the ability to view safe members and audit logs.
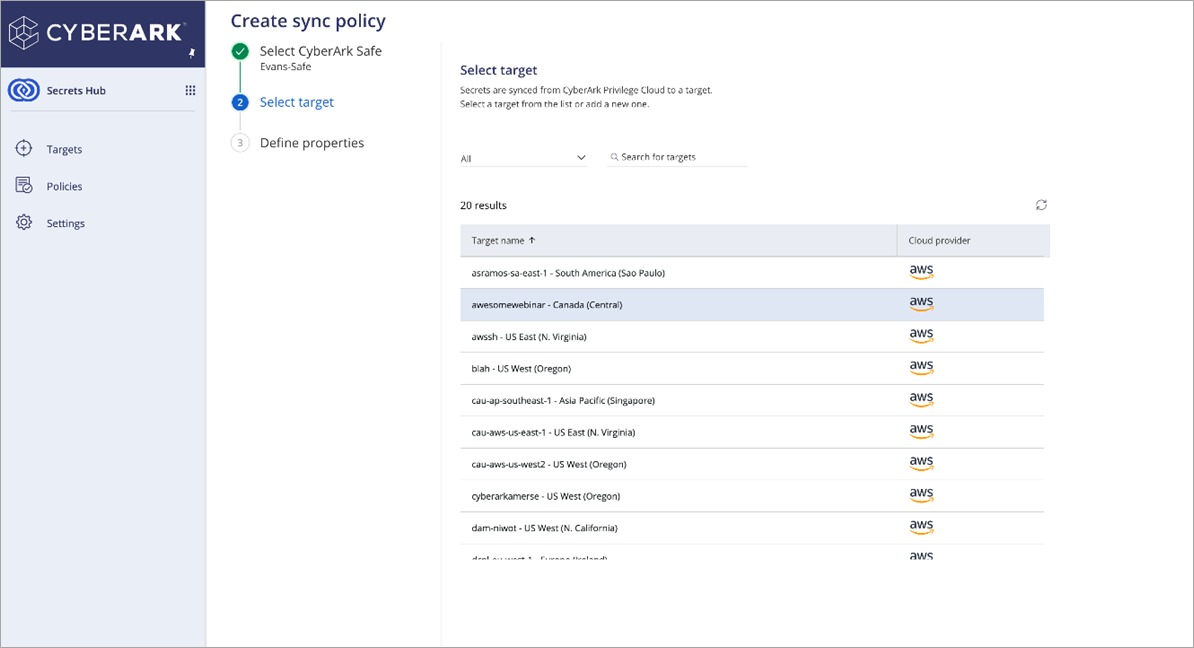
Step 3: Configure the Sync Policy Between CyberArk and AWS Secrets Manager
Finally, use the CyberArk Secrets Hub UI to create a sync policy between the safe and the AWS Secrets Manager target.
Select the sync target name that was set up in AWS previously.
Figure 5 – Create the sync policy for the ASM instance.
Now, CyberArk Secrets Hub will ensure the read-only copy of the secrets is continually maintained and synced in the AWS Secrets Manager target.
That’s it! The secrets provided by AWS Secrets Manager are managed and rotated centrally by CyberArk in the safe you set up earlier with the appropriate rotation policy and permissions.
Summary
CyberArk Secrets Hub works with AWS Secrets Manager to help simplify how development teams meet corporate security policies. With centralized secrets management, CyberArk Secrets Hub helps organizations consolidate managing secrets across multiple instances of AWS Secrets Manager and hybrid environments, reducing vault sprawl and improving security and efficiency.
Intended to scale to support large secrets management environments, the solution is designed to be highly resilient to ensure that, in the event of an outage, there is no impact on production applications using AWS Secrets Manager.
As part of the CyberArk Identity Security Platform, CyberArk Secrets Manager (which includes CyberArk Secrets Hub) helps secure secrets across a broad range of application types and compute environments, supporting both legacy and AWS cloud-native environments.
CyberArk Secrets Hub and AWS work together to ensure developers can keep using the tools they’re currently working in, while the security team gains full visibility of secrets across the enterprise from a single pane of glass.
Get started using CyberArk Secrets Hub to centrally manage and rotate secrets managed by AWS Secrets Manager. You can also learn more about CyberArk in AWS Marketplace.
CyberArk – AWS Partner Spotlight
CyberArk is an AWS Partner and global leader in identity security with a rich portfolio of SaaS products for which customers can buy and use a subscription-based license.