AWS Database Blog
How DevOcean built a vulnerability remediation management platform for cloud-native applications using Amazon Neptune
In this post, we discuss how DevOcean uses Amazon Neptune to power its cloud application vulnerability remediation platform. The DevOcean platform provides a unified dashboard to manage security events across all the layers of a customer’s cloud applications. With DevOcean, users can prioritize risk, reduce alert fatigue, and manage remediation faster with appropriate owners within the organization.
DevOcean is a leading software as a service (SaaS) development company that provides cloud-native application vulnerability remediation management and automation solutions to enterprise organizations worldwide. Its unified platform solution bridges the gap between development, infrastructure security, and application security teams by providing them with a single source of truth for visibility and control over cloud assets and their connected risk.
DevOcean builds a virtual blueprint of its customers’ cloud applications that provides them with a live visualization of how assets and risks are connected, and how architectural drift affects them.
With DevOcean, security teams are able to get the context they need to prioritize risk, reduce noise, and manage remediation with the appropriate teams within the organization.
DevOcean is listed as an AWS partner. Organizations may request a free trial of the software at www.devocean.security.
DevOcean vulnerability remediation platform overview
The following diagram illustrates the data architecture within the platform.

The DevOcean platform is built using an AWS serverless microservices architecture. Data is collected by connecting to the customer cloud accounts and collecting all the cloud assets and their configuration and metadata.
In parallel, the platform connects to the security tools that the customer has connected (such as CSPM, CWPP, CNAPP, code vulnerability scanners, least privilege, and other OSS tools) and extracts the security events.
A pipeline then pushes the data to Neptune, where smart clustering logic connects the data and adds context to findings. With this context, DevOcean makes risk prioritization recommendations. For example, a security tool might give a particular security event a high rating, but DevOcean deems it low risk because the event is connected to an asset in a test environment.
DevOcean’s smart clustering also allows for the deduplication of connected events reported by different tools along with identifying the root cause event, greatly reducing the amount of noise, and reducing the number of tickets needed to solve a single issue.
By creating a unified security picture from hundreds of thousands of disparate security events, tools, and cloud assets, DevOcean provides the context needed to manage and automate risk remediation in cloud-native applications.
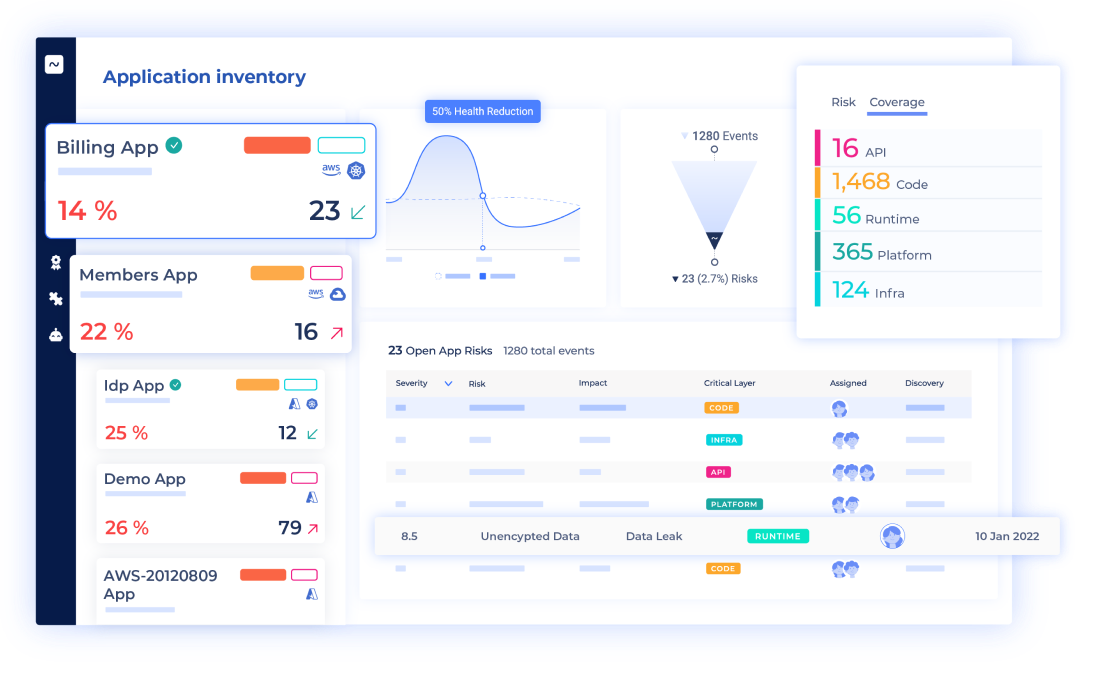
The following screenshot illustrates the DevOcean user interface.
Solution overview
DevOcean is an agent-free deployment that can be deployed to your cloud in a matter of minutes. In the initial onboarding phase, it connects to all your cloud accounts and begins the data collection process from all your assets. After that, data collection is constant in order to maintain an always up-to-date blueprint of the cloud environment.
This generates a tremendous amount of data that needs to be stored in a way that it can be clustered into applications and microservices, allowing DevOcean to highlight relationships and usage, and to generate meaningful insight driven by context.
During the development of the system, the DevOcean team examined the required access patterns to the data. They would need a high-performance database that would be secure and easily scalable, and would easily integrate into DevOcean’s serverless architecture. A high level of support, of course, would also be critical.
It became clear that a graph database would answer those requirements most efficiently, and after evaluating its options, DevOcean chose Neptune as the graph database from which to run its SecOps platform.
Why Neptune?
The DevOcean platform is a serverless application deployed by the AWS Cloud Development Kit (AWS CDK). DevOcean uses infrastructure as code (IaC) to deploy its backend services. Deploying Neptune with the AWS CDK reduces backend deployment effort.
As a managed service, Neptune integrates with other managed services that construct DevOcean’s backend, which makes internal service communication easier. Additionally, managing all databases in one platform (AWS) makes support, debugging, and monitoring processes much easier.
Building the application blueprint: Clustering data into an application
During the collection process, the raw data is saved to an Amazon Simple Storage Service (Amazon S3) bucket and gets loaded to a Neptune cluster using the Neptune bulk loader. After inserting the resources into the graph, the DevOcean platform starts to identify applications by searching for connected resources in the graph (or sub-graph). It then tries to identify if those resources are an application and if they are disconnected from other sub-graphs.
One example used to verify that is to check if application resources construct a cyclic sub-graph that has high cohesion between its resources but low coupling to other sub-graphs. If the algorithm finds an application that answers this specific rule, it is a new application.
The following screenshot shows an account (in the grey circle) with three applications inside. Each application contains assets and their connections. Our platform has grouped assets inside an application because these assets are connected. Connections are created between assets based on communication, logs, policies, and so on.

With the Neptune bulk loader and its fast query engine, the clustering process takes several minutes. After the clustering process, NLP is used to define the application name.
Faster risk generation means faster risk remediation
A risk in the DevOcean platform is configured from an Amazon EventBridge rule, either defined natively or by the customer. A rule is a path on the graph that combines resources, security events, usage and relations, and metadata.
A risk can be generated by a rule, for example: If there is an API gateway with security event X that is connected to AWS Lambda function Y that stores data in database Z, and if that database has a security event or has personally identifiable information (PII) data, generate a risk.
To generate this risk, DevOcean scans all the data retrieved from the customer. Scanning relations between resources in a graph database is much easier than in any other database.
With Neptune, DevOcean created a model that stores the metadata and usage on the graph in properties that are needed for queries and stores non-searchable metadata in another database. That way, they can ensure that they are only loading data to the graph that they will query.
The code is written in a way that each field of a resource, for example, can be stored in the graph unless it’s not searchable, in which case it will be stored in a key-value store.
IAC deployment, tenant provision, and disaster recovery
DevOcean’s backend services and their dependencies are configured using IaC and deployed to DevOcean’s AWS backend account. The deployment account and Region can be configured as well.
Neptune makes DevOcean’s IaC deployment, tenant provisioning, and disaster recovery fast and easy. As a managed service, Neptune provides seamless integration with DevOcean’s serverless ecosystem and can be deployed by the AWS CDK, which ensures DevOcean can be deployed to another Region or account quickly.
Quick tenant provision is crucial for onboarding new customers quickly. DevOcean uses the AWS CDK for its tenant provision process.
To achieve multi-tenancy in Neptune, DevOcean developed virtual tenants inside Neptune using the TinkerPop partition strategy. Partition keys are created, which they can use as the tenant IDs, which are properties that can be attached to any node or edge. Tenant’s roles then have access only to this key. No manual configuration is needed, so provisioning a new tenant is fast. This enables tenant segregation using role-based access control.
With a Neptune tenant strategy and their backend role-based access control, they can ensure tenants are separated in a Neptune cluster.
As an improvement to this, DevOcean are currently working on taking advantage of Amazon Neptune Serverless, so that in future, each customer can have their own Neptune cluster.
Another crucial capability that helped DevOcean choose Neptune is disaster recovery, which is straightforward thanks to their IaC strategy and Neptune’s capabilities.
For example, if there is a disaster, DevOcean needs to recreate a customer’s account in a different Region. Additionally, when it comes to disaster recovery, Neptune has other benefits beyond quick redeployment. It also helps ensure no data is lost. DevOcean uses Neptune snapshots and backs up the data in every customer collection process to ensure there won’t be any data loss. When recreating the environment, the system checks to see if there are any recent snapshots and if there are, they are loaded into Neptune. Within minutes, the customer’s account is fully loaded with the latest data.
The following diagram illustrates this architecture.

Next steps for DevOcean
Amazon SageMaker hosted Jupyter notebooks make it easy to connect, query, and visualize Neptune graphs. In the future, DevOcean plans to build a prediction engine that will check common attack vectors to better identify potential risks and attack trends by searching for common noise or security events that are similar across security tools. For more information, see Use Neptune graph notebooks to get started quickly.
Summary
In this post, we explored how DevOcean built its remediation platform for cloud-native applications using Neptune to correlate cloud assets to risk with enriched context. Getting visibility and context into cloud-native application risk is no longer a complex, manual process for organizations. With DevOcean, a security team can manage and prioritize consolidated security alerts from across siloed tools in a single platform.
With this offering, DevOcean is simplifying cloud-native risk management and automation for its customers. With the entire solution architecture built in AWS, using Neptune to cluster data makes building insights from disjointed data easy. The result is a real-time blueprint of a cloud-native application that displays each risk and its connected assets.
To learn more about Neptune cluster backup and restore, refer to Overview of backing up and restoring a Neptune DB cluster.
About the authors
 Gil Makmel is the CTO and Co-Founder of DevOcean Security. He holds a BSc in Computer Science and is a veteran of the Israeli Defense Force’s elite 8200 intelligence unit.
Gil Makmel is the CTO and Co-Founder of DevOcean Security. He holds a BSc in Computer Science and is a veteran of the Israeli Defense Force’s elite 8200 intelligence unit.
 Charles Ivie is a Senior Graph Architect with the Amazon Neptune team at AWS. He has been designing, implementing and leading solutions using knowledge graph technologies for over ten years.
Charles Ivie is a Senior Graph Architect with the Amazon Neptune team at AWS. He has been designing, implementing and leading solutions using knowledge graph technologies for over ten years.