AWS Partner Network (APN) Blog
Applying Fine-Grained Authorization to Legacy Apps with Strata Identity Orchestration and Amazon Verified Permissions
By Aliaksei Ivanou, Partner Solutions Architect, Security and Identity – AWS
By Michael Wallen, Technical Product Manager – Strata Identity
 |
| Strata Identity |
 |
Achieving a zero-trust architecture is a top priority for many organizations, and a big part is externalizing authorization to ensure least privilege access for all applications. To address this, Amazon Web Services (AWS) introduced Amazon Verified Permissions, a fine-grained authorization service for developers building custom applications.
Amazon Verified Permissions uses Cedar, an open-source policy language, to define access permissions and maintain authorization policies. It allows developers to call an authorization service instead of having to write this logic into their code.
With Amazon Verified Permissions and Cedar, AWS customers can build better authorization processes and best-of-breed security into their apps without having to continually rewrite policy code in applications.
In some use cases, however, Amazon Verified Permissions may have to make decisions on partial data, which could result in unexpected errors or responses. In this post, we will explore how to solve this challenge through identity orchestration.
Strata Identity has been selected as an orchestration and gateway partner for the Amazon Verified Permissions service launch. Strata is an AWS Partner and AWS Marketplace Seller that’s a leading provider of identity migration and modernization solutions to the hybrid and multi-cloud enterprise.
Challenge #1: Modernizing On-Premises Legacy Applications
The first challenge in managing authorization for apps is that legacy, on-premises applications need to be modernized as they move to the cloud.
Many organizations have significant investments in applications that still run on-premises, and recent research suggests that enterprises still run more than 75% of workloads on-premises.
During a cloud migration, it’s important to modernize the application on cloud-first technologies; ideally with the same identity and access management system consistently across all applications. Cloud migration projects that “lift and shift” their infrastructure to the cloud can be costly to maintain because they don’t take advantage of cloud-native technologies.
Amazon Verified Permissions provides centralized policy management and an authorization decision point for custom applications. Strata’s Maverics Identity Orchestration platform offers authorization enforcement for applications that run on-premises or in the cloud.
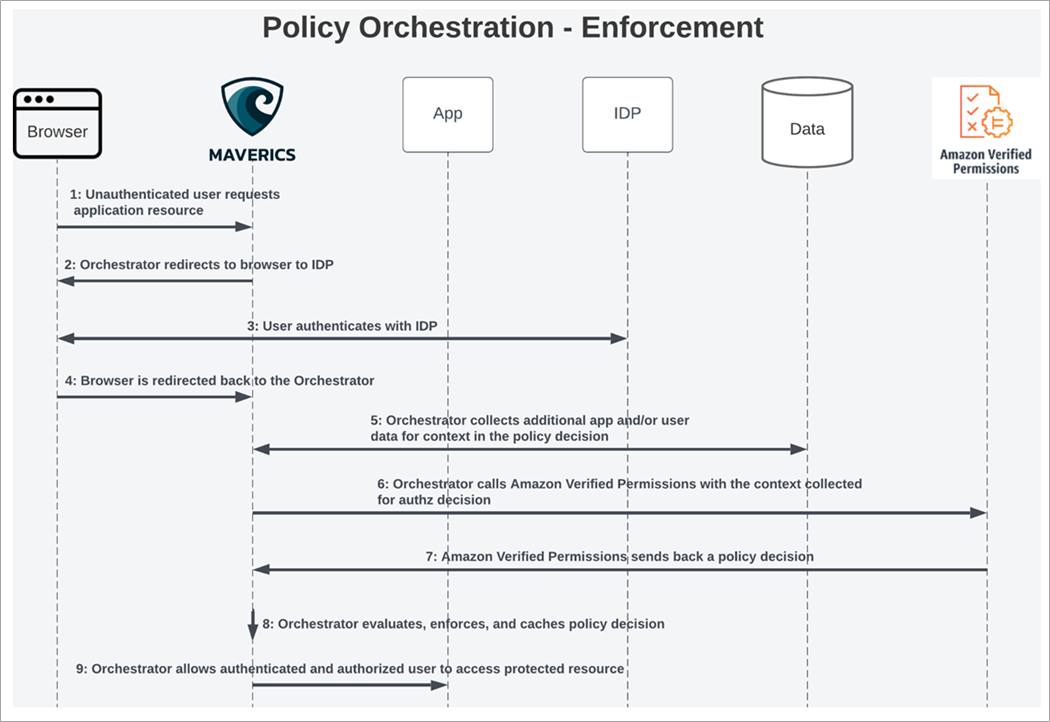
Figure 1 – Orchestrated policy enforcement.
The diagram below shows how a user is granted access to an application using Maverics and Amazon Verified Permissions.
Figure 2 – User flow sequence.
Challenge #2: Filling in Gaps in Data
The second challenge is that not all data are available to make authorization decisions.
Developers and policy administrators must ensure all necessary data are included in their requests to Amazon Verified Permissions. For example, if a user attribute from a third-party data store is required for a policy decision, then the application will need to provide this to Amazon Verified Permissions at runtime.
The Maverics Identity Orchestration platform specializes in legacy access management migrations; it can perform lookups on legacy identity systems to gather all of the required data at runtime to perform complete authorization requests to Amazon Verified Permissions.
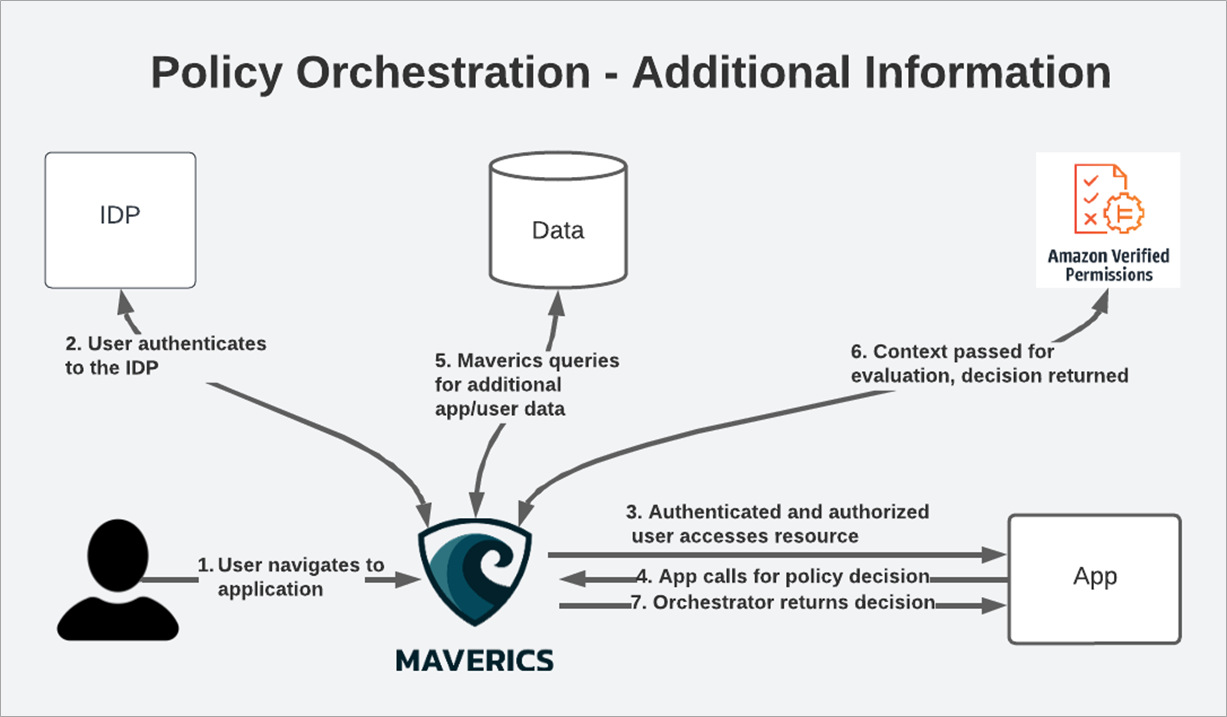
Figure 3 – Augmented data.
Maverics enhances the application authorization workflow by providing applicable attribute data to make a decision on access. Maverics offers continuous authorization enforcement between your custom applications and Amazon Verified Permissions, ensuring the service has all of the necessary data to secure access to your apps.
Some applications have the ability to call Amazon Verified Permissions but don’t have the context and data needed for the policy evaluation. In these cases, Maverics can augment these calls with additional context and data.
With Maverics, you can define database connections, LDAP databases, and other types of identity services. Creating a user flow enables you to link together these identity services to supply the data your application needs in the right format your application requires, whether it’s by token or header.
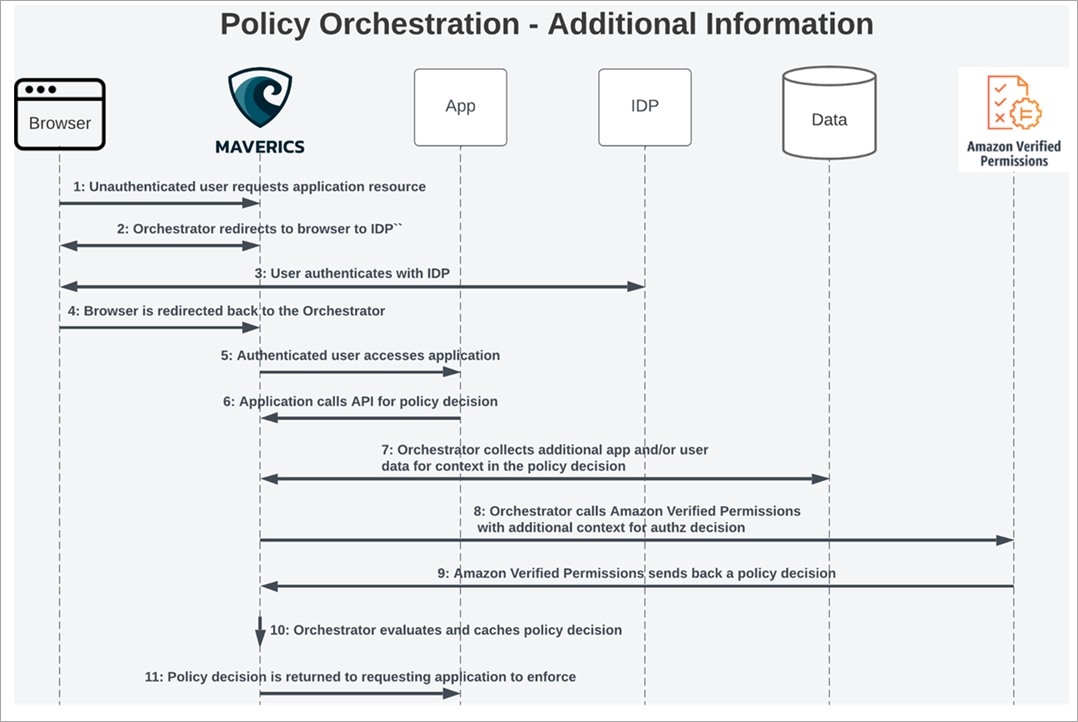
Figure 4 – Augmented data flow.
Maverics Integration with Amazon Verified Permissions
Strata’s Maverics Identity Orchestration platform provides an abstraction layer, called an identity fabric, that decouples apps from identity and natively integrates with cloud platforms, cloud identity systems, and on-premises identity and application infrastructures.
The Orchestrator instance runs in the cloud or on-premises, giving you greater control over your user flows and allowing you to cache the authorization decisions and data to mitigate your API costs and improve performance.
Strata has integrated Maverics with Amazon Verified Permissions to provide a comprehensive, fine-grained authorization solution for legacy applications. Maverics provides an application policy enforcement point and runtime orchestration engine to gather external identity attributes and mimic legacy application requests.
Customer Benefits
Maverics works with Amazon Verified Permissions to provide a flexible and customizable authorization process, speeding up development and improving overall security. With the increasing importance of security in the cloud, using Maverics can help companies stay ahead of the curve and ensure systems are secure and compliant.
With Amazon Verified Permissions and Maverics, you can:
- Build more advanced and automated authorization and security policies without having to rewrite your applications.
- Abstract authorization from application developers, allowing developers to focus on writing best-in-class applications.
- Maintain closer control of user flows and cache your authorization data, saving on API costs.
- Use policies written in Cedar with legacy, on-premises applications and applications that run on other cloud platforms.
By separating authorization from the application code with Maverics and Amazon Verified Permissions, it’s easier to maintain and update security policies, leading to a more secure overall system and reducing the risk of security breaches.
Implementing Maverics + Amazon Verified Permissions
Strata has made a number of assets available for download it its GitHub repository to streamline the Maverics setup process with detailed instructions. These assets include an orchestration recipe, Maverics environment configuration, Amazon Verified Permissions service extension, self-signed certificates, and step-by-step directions–everything you need to get Maverics started.
At a high level, let’s walk through the following steps:
- Go to GitHub and follow the Amazon Verified Permissions Quick Start Guide.
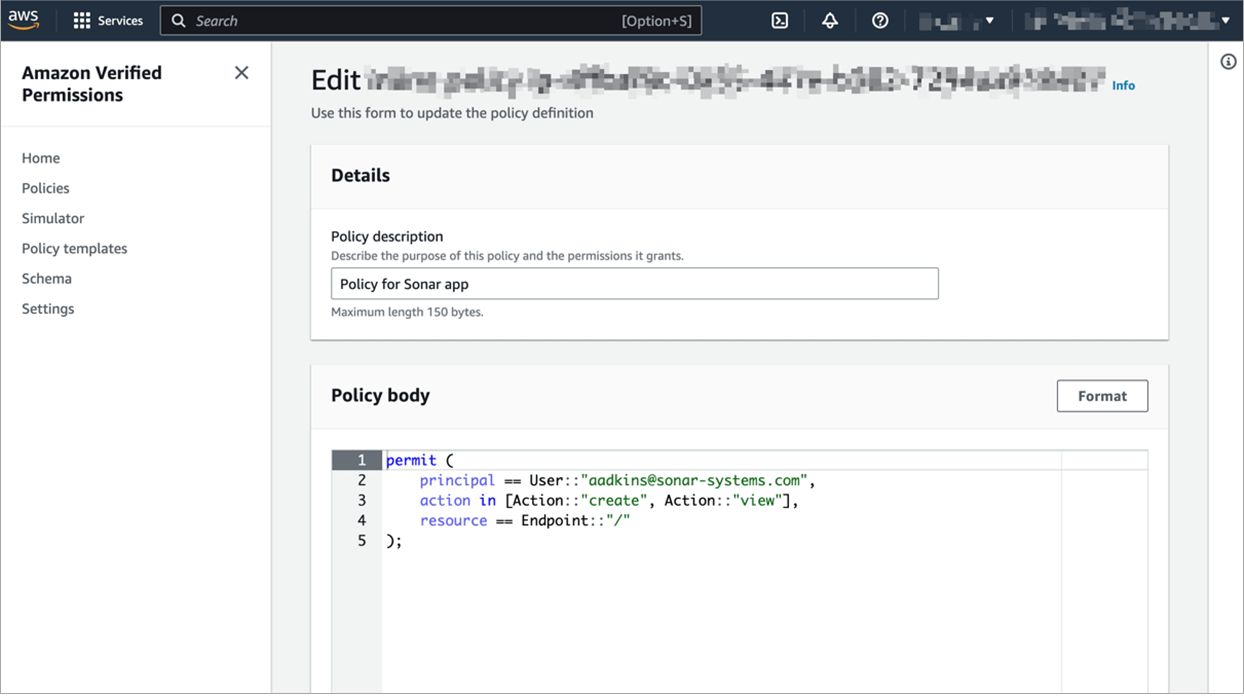
- Create a new Amazon Verified Permissions policy in your AWS Management Console.
Figure 5 – Sample policy in Amazon Verified Permissions..
- Import an Identity Orchestration Recipe into Maverics.
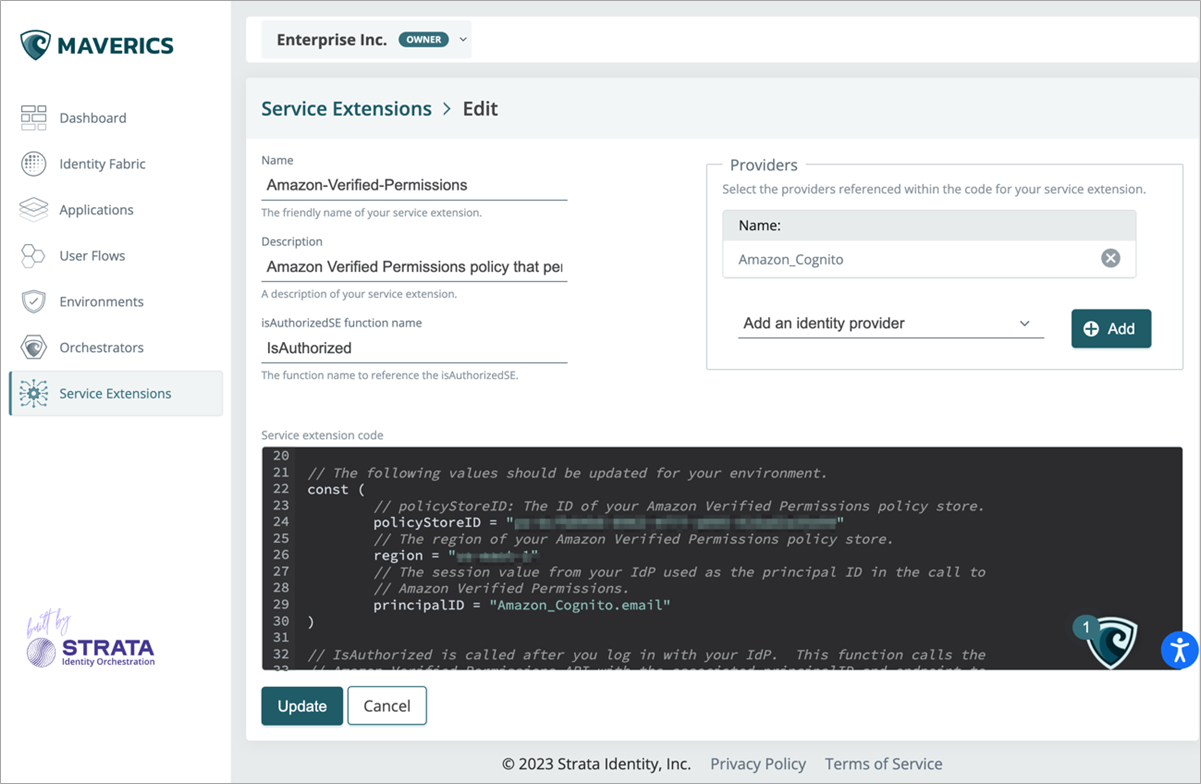
- Upload a service extension into Maverics that calls Amazon Verified Permissions for authorization.
Figure 6 – Maverics service extension.
- Set up your local test environment.
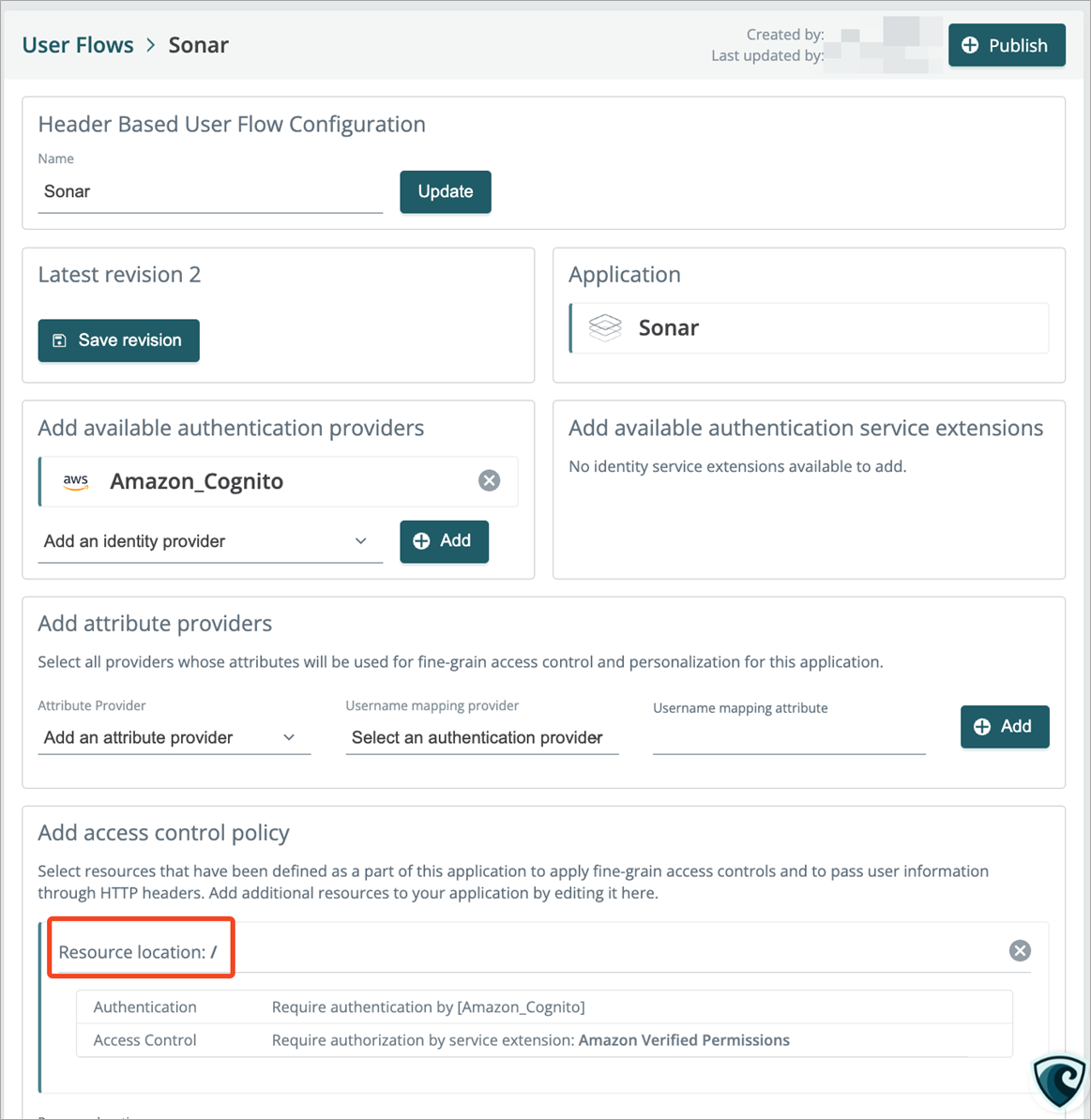
- Deploy the user flow and try out the new login flow.
Figure 7 – Maverics user flow configuration.
To see this in action and for instructions on how to test your user flows, watch Strata’s demonstration video of the complete app modernization process. For more detailed information on setting up Maverics, view the documentation at docs.strata.io.
Conclusion
Strata’s Maverics Identity Orchestration platform can help you get more out of Amazon Verified Permissions. It allows you to simplify cloud migration and modernization projects by augmenting your datasets to ensure comprehensive policy enforcement, migrating policy data from legacy platforms, and mimicking runtime calls to legacy applications.
If you’re ready to upgrade Amazon Verified Permissions with Maverics, contact Strata’s sales team. You can also learn more about Maverics in AWS Marketplace.
Sample code, software libraries, command line tools, proofs of concept, templates, or other related technology are provided as AWS content or third-party Content under the AWS Customer Agreement, or the relevant written agreement between you and AWS (whichever applies). You should not use this AWS content or third-party content in your production accounts, or on production or other critical data. You are responsible for testing, securing, and optimizing the AWS content or third-party content, such as sample code, as appropriate for production grade use based on your specific quality control practices and standards. Deploying AWS content or third-party content may incur AWS charges for creating or using AWS chargeable resources, such as running Amazon EC2 instances or using Amazon S3 storage.
Strata Identity – AWS Partner Spotlight
Strata Identity is an AWS Partner and a leading provider of identity migration and modernization solutions to the hybrid and multi-cloud enterprise.
Contact Strata Identity | Partner Overview | AWS Marketplace