AWS Partner Network (APN) Blog
Aruba and AWS Enhance Branch-to-Cloud Connectivity Performance with AWS Transit Gateway Connect
By Samuel Pérez Buñuel, Sr. Solution Architect – Aruba
 |
The Aruba SD-Branch solution treats public hosted cloud environments as a managed node in the SD-WAN overlay network, as we described in a previous blog post.
This is done in an automated fashion, orchestrating the complete lifecycle of bringing up an Aruba Virtual Gateway in an Amazon Virtual Private Cloud (VPC), connecting it to all of the relevant resources and even managing high availability for redundancy within or across AWS Availability Zones (AZs).
Bringing the SD-WAN into the public cloud environment has clear benefits:
- Single pane of glass for the entire SD-WAN environment (and even the LAN environment in the case of SD-Branch).
- End-to-end route and tunnel orchestration (integrated as part of Aruba Central).
- Quality of experience mechanisms such as Forward Error Correction (FEC) or Dynamic Path Steering (DPS).
At the same time, AWS Transit Gateway simplifies the connectivity across multiple VPCs, putting an end to complex peering relationships.
With the introduction of the AWS Transit Gateway Connect attachment type, there’s now a native way to connect the SD-WAN and VPC environments.
Customer benefits when using SD-Branch and AWS Transit Gateway Connect are:
- Enhanced performance with up to 20Gbps per Transit Gateway Connect VPC.
- Increased security, reducing unnecessary exposure of the Transit Gateway to internet traffic.
- WAN communications simplification, through orchestrated SD-WAN routing and tunnels as an integral part of the SD-Branch solution.
- Scalable dynamic routing between cloud and SD-WAN environments.
- Complete visibility from the network edge (and even the end user) to the cloud.
In this post, we’ll go through all of the technical details involved in integrating the Aruba SD-Branch solution with AWS Transit Gateway Connect.
Aruba SD-Branch
Aruba, a subsidiary of Hewlett Packard Enterprise, is a global leader in secure, intelligent edge-to-cloud networking solutions. Aruba uses a cloud-native approach to help each customer with all aspects of wired, wireless LAN, and WAN. Hewlett Packard Enterprise is an AWS Advanced Consulting Partner.
The SD-Branch solution is part of Aruba’s Edge Services Platform (ESP), a key evolution of end-to-end network architecture, especially when it comes to secure edge-to-cloud connectivity.
ESP provides a unified infrastructure with centralized management that leverages artificial intelligence (AI) for improved operational experience. This helps customers enable a Zero Trust security policy on their existing infrastructure.
Figure 1 – Aruba ESP architecture.
Multi-VPC Architecture Overview
Aruba SD-Branch has been able to integrate with the AWS Transit Gateway (TGW) since its introduction by means of establishing a Border Gateway Protocol (BGP) peering over IPsec tunnels established between the Aruba Virtual Gateways (Aruba vGWs) and TGWs.
This continues to be a valid option and is covered in other documentation assets. However, the use of IPsec does introduce overhead, as well the inevitable performance limitations derived from the need to encrypt the communication.
With the Transit Gateway Connect capability, IPsec tunnels are no longer required and much higher performance (up to 20Gbps per “Connect VPC”) can be achieved. This allows for more robust security as internet-facing interfaces in the Transit Gateway are not needed.
Figure 2 – Transit Gateway Connect high-level architecture.
Aruba vGWs are deployed inside a dedicated Amazon VPC labeled as the “Connect VPC.” This is attached to the Transit Gateway through a “Connect” attachment, which enables and secures the communications between the Aruba vGWs and AWS Transit Gateways.
The last step is establishing generic routing encapsulation (GRE) tunnels between the Aruba vGWs and Transit Gateway, and exchanging routing information using BGP. This effectively connects the SD-WAN and VPC environments with a straightforward mechanism.
Figure 3 – Transit Gateway Connect and SD-Branch vGW integration.
Dynamic Routing Between SD-WAN and Cloud
As mentioned, the communication between the AWS Transit Gateway and Aruba vGWs (and ultimately the SD-WAN network) is established by bringing up GRE tunnels between the Transit Gateway and Aruba vGWs.
Once the tunnels are up, BGP sessions are established and routing information is exchanged between the cloud and SD-WAN environments.
Figure 4 – Dynamic routing between SD-WAN and cloud.
When peering with the Transit Gateway, failover is handled by leveraging traditional routing mechanisms. Both Aruba vGWs advertise the same routing prefixes to the TGW. However, to ensure symmetric communication flow, the secondary Aruba vGW should advertise routes that look less preferable to the TGW.
While both internal and external BGP are supported, eBGP is recommended as it allows the use of automatic AS_PATH prepending to influence the routing decisions of the Transit Gateway. Advertising a longer AS_PATH from the secondary Aruba vGW ensures the Transit Gateway chooses the one advertised by the primary Aruba vGW as the best path.
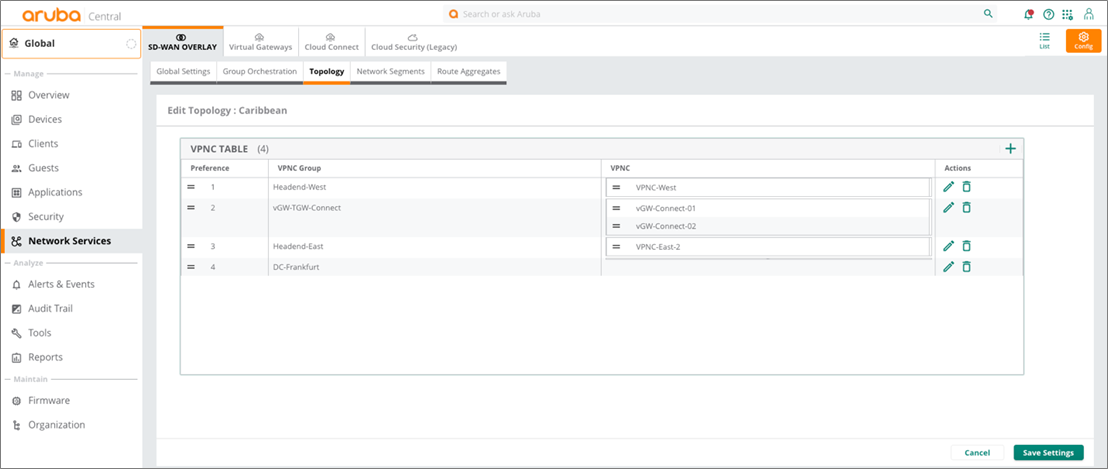
When building an SD-WAN topology with Aruba SD-Branch, the Orchestrator allows for a simple mechanism to establish the preference across nodes advertising the same prefixes.
Figure 5 – SD-WAN DC-Preference.
Once this DC-Preference has been set, Aruba SD-Branch helps Aruba vGWs automatically translate the SD-WAN routing costs (lower for the VPCs higher in the DC-Preference) into the corresponding BGP routing cost.
When eBGP is used between Aruba vGWs and the Transit Gateway, the Aruba vGWs translate the SD-WAN overlay routing cost into BGP metrics by prepending their own Autonomous System incrementally; for example:
- An Overlay cost of 10 is translated to AS-Path prepend = 0
- An Overlay cost of 20 is translated to AS-Path prepend = 1
- An Overlay cost of 30 is translated to AS-Path prepend = 2
- Additional incremental Overlay cost continue to result in incremental AS-Path prepend.
Figure 6 – Dynamic routing in normal and failover situations.
End-to-End Visibility
One key reason to bring SD-WAN nodes into the cloud environment is to have unified visibility of the WAN environment.
In the case of Aruba SD-Branch, that visibility is extended to the entire branch network, including LAN network elements such as Switches and Access Points, as well as a full monitoring, reporting, and troubleshooting for all client devices.
Figure 7 – End-to-end visibility of LAN and WAN in Aruba Central.
The demarcation point is the connection between the Aruba vGWs and the Transit Gateway, where routes get redistributed from SD-WAN into BGP (and into the Transit Gateway).
The Aruba Central portal provides easy access to details such as how the Aruba vGWs are exchanging route prefixes with the Transit Gateway.
Figure 8 – Route exchange between vGW and AWS Transit Gateway.
This information complements what is available in the AWS console. The dynamic routing information can be visualized.
Figure 9 – AWS Transit Gateway dynamic routing.
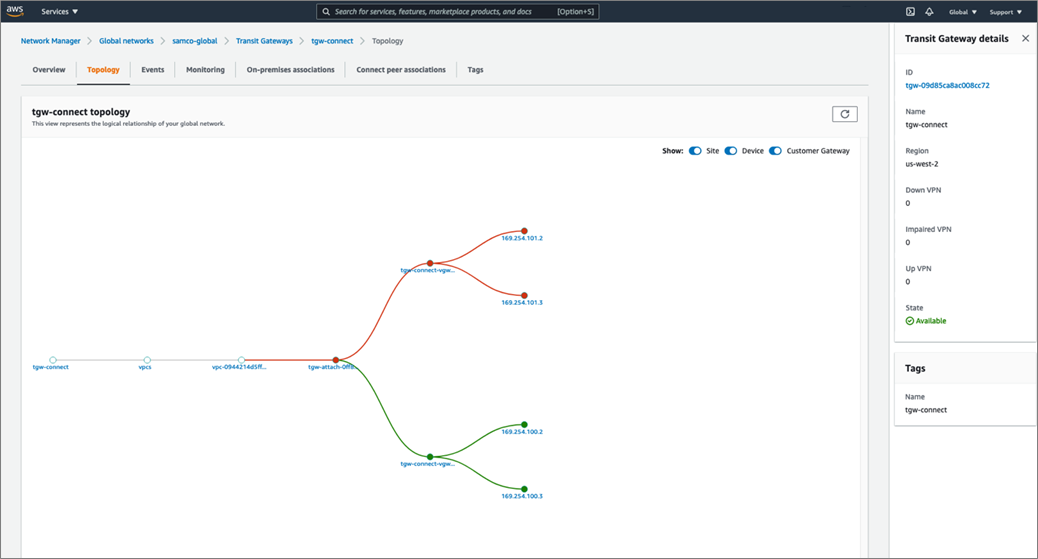
The topology for this particular deployment can be visualized.
Figure 10 – AWS Transit Gateway Network Manager.
Summary
The combination of Aruba SD-Branch with AWS Transit Gateway Connect provides a simple, orchestrated way to address edge-to-cloud communications.
Users can be located at a headend site, smaller branch site, or in a microbranch like a teleworker or SoHo environment. They can even be accessing their corporate network through a VPN client. Likewise, applications can be located in private data centers or public cloud. This design provides a consistent set of features and functionality for network access with complete independence of where the user may be coming from.
Aruba’s SD-Branch solution enhances the benefits of integrating with AWS, as it turns the public hosted cloud environment into a managed node in the SD-WAN overlay network. Aruba vGWs can scale to terminate thousands of IPsec VPN tunnels from all sorts of remote locations. This makes it easy for your locations to directly access hosted workloads on AWS.
Aruba vGWs simplifies the simpler environments where all workloads are located in a single VPC, while also addressing the more complex scenarios by integrating with the Transit Gateway. This enables robust, high-performance communications between the SD-WAN and cloud environment.