AWS Partner Network (APN) Blog
Partner Solutions Achitect Roundup – October
This month, AWS Partner Solutions Architects Tim Mattison, Roy Rodan, and Claudine Morales highlight offerings from AWS Technology Partners Cesanta, GorillaStack, and GuardiCore.
Cesanta Provides Streamlined IoT Solutions
By Tim Mattison, Partner Solutions Architect at AWS
 In Internet of Things (IoT) systems, it is important to be able to build, test, and secure systems with minimal friction. Customers need a way to get hardware that they can use to rapidly develop and test IoT solutions. Cesanta, creator of Mongoose OS, which we highlighted in our May Partner SA Roundup, is in the business of providing streamlined tools that simplify the onboarding process and unblock developers. Recently, they released their own hardware kit based on Espressif’s ESP32 platform, which provides a known-good component for customers to design, develop, and deploy IoT solutions.
In Internet of Things (IoT) systems, it is important to be able to build, test, and secure systems with minimal friction. Customers need a way to get hardware that they can use to rapidly develop and test IoT solutions. Cesanta, creator of Mongoose OS, which we highlighted in our May Partner SA Roundup, is in the business of providing streamlined tools that simplify the onboarding process and unblock developers. Recently, they released their own hardware kit based on Espressif’s ESP32 platform, which provides a known-good component for customers to design, develop, and deploy IoT solutions.
The ESP32 is the successor to the ESP8266 IoT board, and it comes with several enhancements: 520K of RAM, a dual-core 240 MHz processor, new security features, 2.4 GHz Wi-Fi, and Bluetooth support.
The faster processor means customers are able to efficiently do more time-sensitive compute operations at the edge. The ESP32 is powerful enough to perform digital signal processing (DSP) operations on input signals, and even decode QR codes in real time from its camera interface.
Additional storage allows customers to add more features to their edge devices. This space can also be used to buffer data while the device is offline, store logs for debugging, or store a backup firmware image to allow for more robust over-the-air firmware deployments.
Bluetooth v4.2 and Bluetooth Low Energy (BLE) let the ESP32 interact with Bluetooth devices and sensors. With Mongoose OS, the ESP32 can even act as a BLE gateway to AWS IoT.
On the security side, the ESP32 supports secure boot, flash encryption, and cryptographic hardware acceleration. Secure boot prevents tampering with the flash contents. Flash encryption protects the flash contents from being read in plaintext. Cryptographic hardware acceleration allows devices to connect to the cloud faster. These features allow customers to build secure IoT devices.
If you’re looking to build a new IoT solution, I’d invite you to take a look at the ESP32. For more information, please head on over to the Cesanta aebsite to learn more about their new hardware kit and Mongoose OS.
GorillaStack Enables DevOps and IT Teams
By Roy Rodan, Partner Solutions Architect at AWS
 Managing cloud infrastructures can be tedious when it’s done manually. In the AWS Cloud, customers are able to use services like AWS CloudTrail and Amazon CloudWatch to help with these tasks. GorillaStack is an AWS Partner that enables DevOps and IT teams to keep track of events in their AWS environments by using simple rules, so they are always up-to-date on the usage and cost of their resources.
Managing cloud infrastructures can be tedious when it’s done manually. In the AWS Cloud, customers are able to use services like AWS CloudTrail and Amazon CloudWatch to help with these tasks. GorillaStack is an AWS Partner that enables DevOps and IT teams to keep track of events in their AWS environments by using simple rules, so they are always up-to-date on the usage and cost of their resources.
Configuring rules in GorillaStack involves three simple steps:
- Identifying the accounts to manage using cross-account AWS Identity and Access Management (IAM) roles
- Defining triggers based on time, cost, server, or volume status
- Specifying the action to be taken
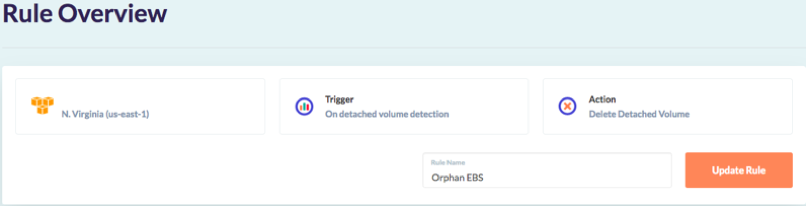
GorillaStack enables customers to apply these rules to resources across all AWS accounts and Regions. For example, the following image shows a rule set up to delete all detached Amazon Elastic Block Store (Amazon EBS) volumes in a particular AWS Region:
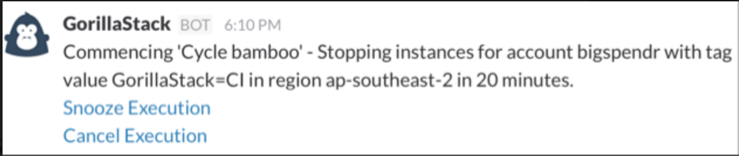
Another helpful GorillaStack feature is its Slack and HipChat integration. This integration makes it even easier to digest events and alerts from CloudTrail and CloudWatch. Instead of having to crawl through CloudTrail or CloudWatch logs for one specific event, you can configure a chatbot to send real-time alerts to a channel or to a specific group of Slack or HipChat users based on any CloudTrail or CloudWatch event. The alert can be expanded to reveal the raw log content, so your DevOps team can take the right actions, as seen here:

This Slack and HipChat integration also enables you to receive alerts on scheduled actions before the events take place, so you can delay or cancel these actions. For instance, let’s say you schedule an action to stop development instances from running during the night in order to reduce costs. An alert is sent to a Slack channel to inform you of the upcoming action, and you can then decide if the shutdown process should proceed, snooze, or cancel.
If you’d like to learn more about how GorillaStack can help you manage your infrastructure, go to the GorillaStack site to sign up for a free 14-day trial and request a live demo of their products.
GuardiCore Centra Security Platform Supports Configuration
By Claudine Morales, Partner Solutions Architect
 As part of the AWS Shared Responsibility Model, customers are responsible for their security configuration in the AWS cloud. This responsibility involves determining ways to protect and monitor network traffic, which can include obtaining internal workload visibility, effective east-west traffic policy management, and active breach detection and response. GuardiCore, an AWS Technology Partner, offers the Centra Security Platform to help bridge these gaps.
As part of the AWS Shared Responsibility Model, customers are responsible for their security configuration in the AWS cloud. This responsibility involves determining ways to protect and monitor network traffic, which can include obtaining internal workload visibility, effective east-west traffic policy management, and active breach detection and response. GuardiCore, an AWS Technology Partner, offers the Centra Security Platform to help bridge these gaps.
Once Centra agents are installed on Amazon Elastic Compute Cloud (Amazon EC2) instances, the Centra Security Platform performs an application discovery process and collects network traffic data, including layer 7 communication activities among applications running on these instances. The Centra user interface displays a map of all network processes, applications, and traffic flows, giving you the ability to easily visualize everything that is occurring in your network at any given time. This same approach can be applied to your on-premises infrastructure, to give you a centralized view of your entire data center, regardless of location.
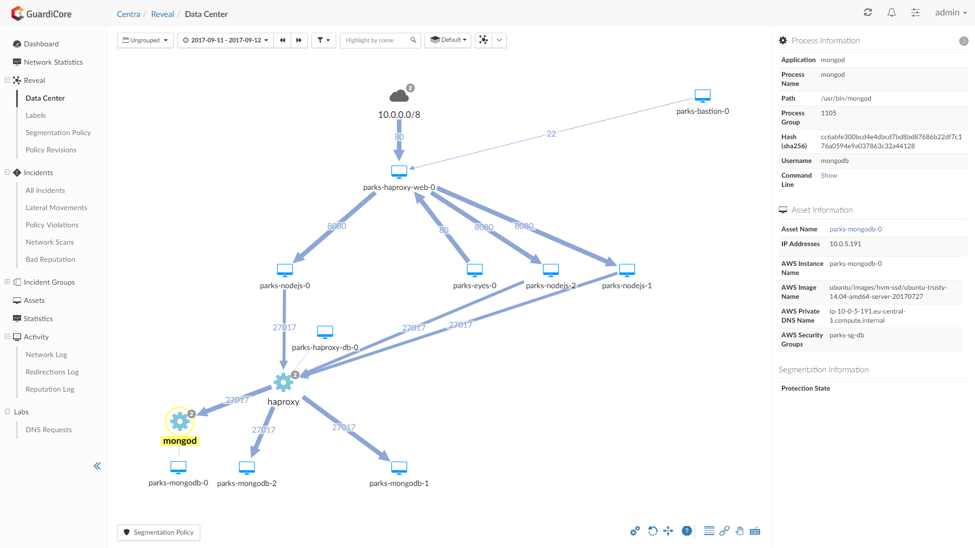
The Centra Security Platform provides micro-segmentation capabilities to give you more granular control over access policies. For instance, it can restrict access to a certain service not only by IP address and port number but also by process name.
Centra also helps safeguard environments from potential breaches by using multiple intrusion detection and prevention methods. One of these methods involves reputation analysis, where domain names, IP addresses, and file hashes that have been associated with malicious behavior are detected and eliminated instantaneously. Another method involves real-time dynamic deception, in which an attacker, when detected, is redirected to a GuardiCore-hosted deception environment where they continue to execute their attack, thinking that they have successfully penetrated the customer’s infrastructure.
Inside the deception environment, the attacker’s actions are logged, recorded, and even screenshotted, to enable analysis and insight on their motives and techniques. This allows customers to implement changes to prevent further intrusions from the attacker. The information on the attacker’s actions is also added to the GuardiCore Reputation Service database to enable detection of similar breach attempts in the future.
To learn more about the GuardiCore Centra Security Platform, visit the GuardiCore website or request a demo.