AWS for SAP
Audit your SAP systems with AWS Config – Part I
Introduction
Customers who run SAP on AWS can take advantage of a broad set of additional services that can enhance and simplify the operations of running SAP. Often, one such tedious task is to validate that your SAP systems are configured according to best practices, meet the requirements for vendor support, and meet internal audit requirements.
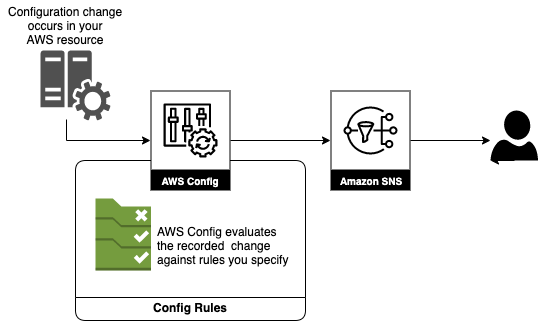
In this blog series, we discuss how AWS Config can simplify the process of continuous auditing and assessing the compliance of all SAP systems in your landscape. We also provide additional details to enable email notification when a resource is flagged as non-compliant using Amazon EventBridge and Amazon Simple Notification Service.
Part I of the series leverages AWS managed Config rules to create a solution that will automatically audit and assess your SAP landscape’s infrastructure-related components.
In Part II of the series, we will cover how to use AWS custom Config rules, and AWS Lambda to provide a holistic solution which will automatically audit and assess your SAP application configuration related components.
Before getting started, you should validate that the desired services and managed rules exist within your specific region.
Solution Overview Part I: AWS Managed Configuration Rules
AWS Config will automatically evaluate configuration changes of AWS resources against rules you define. If a change is identified as non-compliant an alert can notify you of the violation.
AWS Config provides over 160 managed rules, which are rules that have been authored by AWS. We provide a list of the most common rules for SAP workloads to ensure your SAP systems are well architected on AWS below.
Common managed rules specifically for SAP Workloads:
- Desired Instance Type – AWS provides specific instance types that are certified to run SAP workloads as outlined in SAP Support document 1656099 – SAP Applications on AWS: Supported DB/OS and AWS EC2 products
- Instance Detailed Monitoring – Detailed monitoring is required for full support by SAP as outlined in SAP Support document 1656250 – SAP on AWS: Support prerequisites
Other managed rules which are common for customers to ensure security compliance and cost savings measures are:
- EC2 Volume in Use Check – Validates that EBS volumes are not lingering around after EC2 instances were terminated.
- EC2 Volume Encryption Check – Validates that the EBS volumes attached to an EC2 instance are encrypted.
- EC2 Public IP – Validates that the EC2 instance does not have a public IP address assigned.
- EBS Encryption by Default – Validates all EBS volumes are encrypted.
- EFS Encrypted Check – Validates all EFS structures are encrypted.
- S3 Public Read – Validates that your S3 bucket is not available for public read access.
- S3 Public Write – Validates that S3 buckets do not allow the public to write access
- S3 Server Side Encrypt – Validates that your S3 buckets have encryption enabled.
- Restricted SSH – Validates that the security groups in use disallow unrestricted SSH traffic.
- EC2 Security Group Attached to ENI – Validates that security groups are attached to EC2 instances or elastic network interfaces.
- Cloudtrail Enabled – Checks whether AWS CloudTrail is enabled in your AWS account.
Configuration: AWS Config Rules
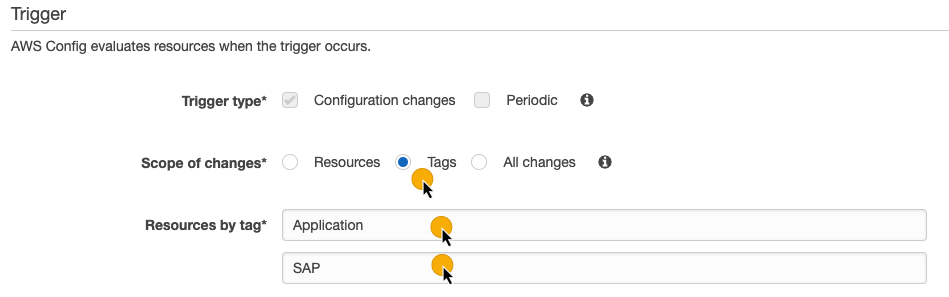
Let’s dive deep and discuss the configuration steps for Desired Instance Types. For this configuration, we will leverage tags to ensure only the EC2 instances associated with SAP workloads are being validated. Refer to Tagging recommendations for SAP on AWS for recommendations.
Pre-Requisites
- SAP instances are tagged with Key: Application Value: SAP
- Basic settings of AWS Config enabled
- AWS Config uses an IAM role which allows for publishing to SNS topics
- SNS Topic and Email Subscription created [Getting started with Amazon SNS]
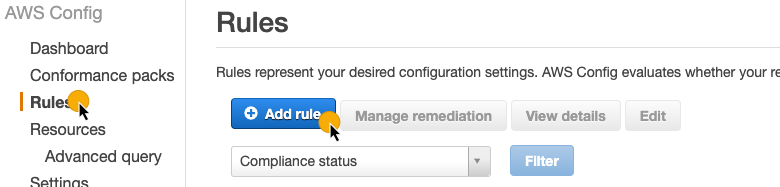
Step 1: From the AWS Config console, chose Rules then Add rule
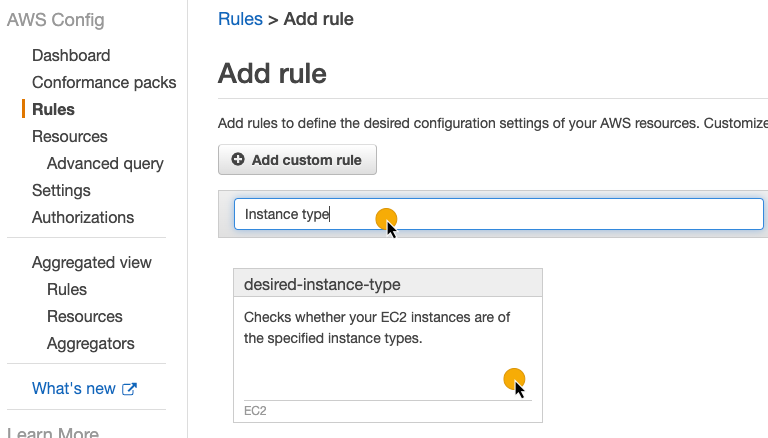
Step 2: Enter Instance type into the text box and chose the card desired-instance-type
Step 3: Scroll down to the Trigger section and choose tags and enter the tag key/value pair
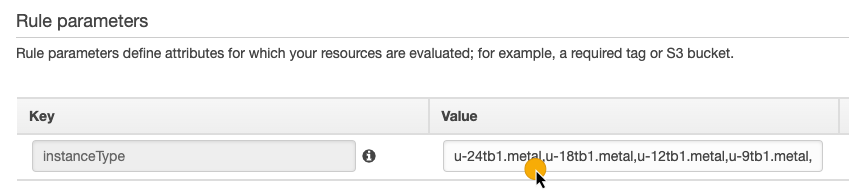
Step 4: Scroll to the section Rule parameters. Enter a list of comma-separated values for the valid instances types which you are validating
Step 5: Once your configuration is updated and validated scroll to the bottom and chose Save.
Configuration: Amazon EventBridge
Now, we will configure Amazon EventBridge notifications to generate compliance notifications.
Step 1: From the Amazon EventBridge console, chose Create rule
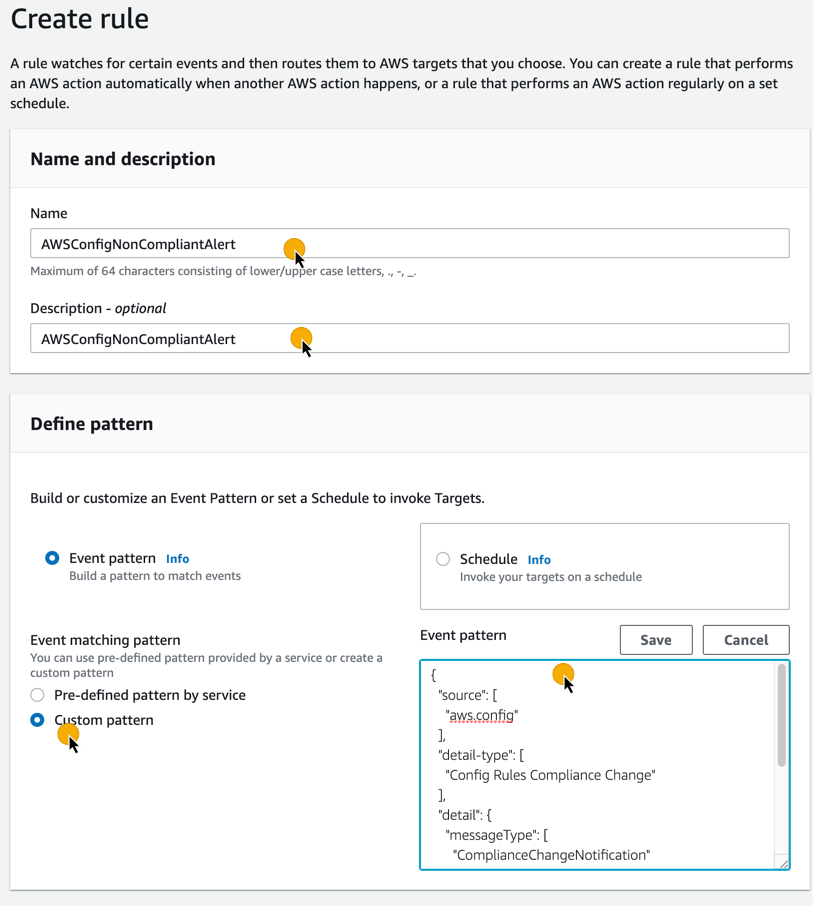
Step 2: Enter your desired name and description. Under event matching pattern choose Custom pattern. Enter the sample pattern and chose Save.
Step 3: Scroll to section Select targets. Under Target choose SNS topic. Under Topic select desired SNS topic. Choose Input transformer. Enter the following into the first box (Input Path):
Step 4: Enter the following sample into the second box (Input Template):
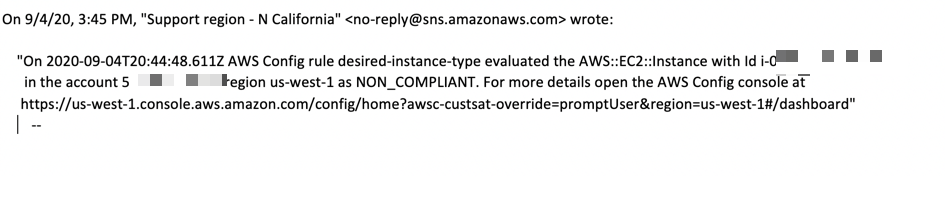
Here is a sample E-Mail notification:
Cost Scenario
AWS Config:
You are charged per configuration item recorded in your AWS account per AWS Region. Assuming you have the following usage in US East (N. Virginia) in a given month:
| Number of Configuration Items Recorded | Estimated Cost (Month) |
| 10,000 | 10,000 * .003 = $30.00 |
Note: A configuration item represents a point-in-time view of the various attributes of a supported AWS resource that exists in your account. The components of a configuration item include metadata, attributes, relationships, current configuration, and related events. AWS Config creates a configuration item whenever it detects a change to a resource type that it is recording. For example, if AWS Config is recording Amazon S3 buckets, AWS Config creates a configuration item whenever a bucket is created, updated, or deleted. Additional details are available on the AWS Config Concepts page.
AWS Config Rules:
You are charged based on the number of AWS Config rule evaluations recorded. Assuming you have configured the desired instance type solution, and change instance types once in a month in US East (N. Virginia), your estimated cost would be:
| SAP | Rules (R) | Evaluations (E) | Estimated Cost (Month) |
| Instances (I) | |||
| 50 | 1 | I*R*Changes/Mth | E*.001 |
| 50*1*1 = 50 | 50*.001 = $.050 |
Amazon EventBridge:
You are charged for events that are published to your event bus. Assuming each evaluation mentioned above results in a published event <= 64KB your estimated cost would be:
| Number published events (PE) | Estimated Cost |
| 50 | 50 * $1.00 / Million = $1.00 |
Amazon SNS:
You are charged for the number of notifications that you publish. Assuming each published event mentioned above results in an SNS message your estimated cost would be:
| Number of SNS messages | Estimated Cost |
| 50 | 50 * $2.00 / 100,000 = $2.00 |
Amazon S3:
Also, Amazon S3 Bucket will be used to store the Configuration and Compliance History related to the AWS Config Service and its Configuration Items.
| S3 Standard Storage(S) GB/month | PUT Requests (P) | GET Requests (G) | Evaluations (E) | Estimated Cost |
| 1 | 15000 | 15000 | (0.023*S) + (P*0.000005) + (G*0.0000004) | $0.11 |
Cost Summary:
Based on the assumptions above, it would cost you approximately $33.16 per month to ensure your instance types adhere to your requirements.
Refer to the following pricing details for each of the services discussed above as AWS periodically optimizes the costs:
AWS Config pricing details are available on the AWS Config pricing page.
Amazon EventBridge pricing details are available on the Amazon EventBridge pricing page.
Amazon SNS pricing details are available on the Amazon SNS pricing page.
Amazon S3 pricing details are available on the Amazon S3 pricing page.
Cleanup
Don’t forget to delete any AWS Config rules created which are not required for your end solution.
Conclusion
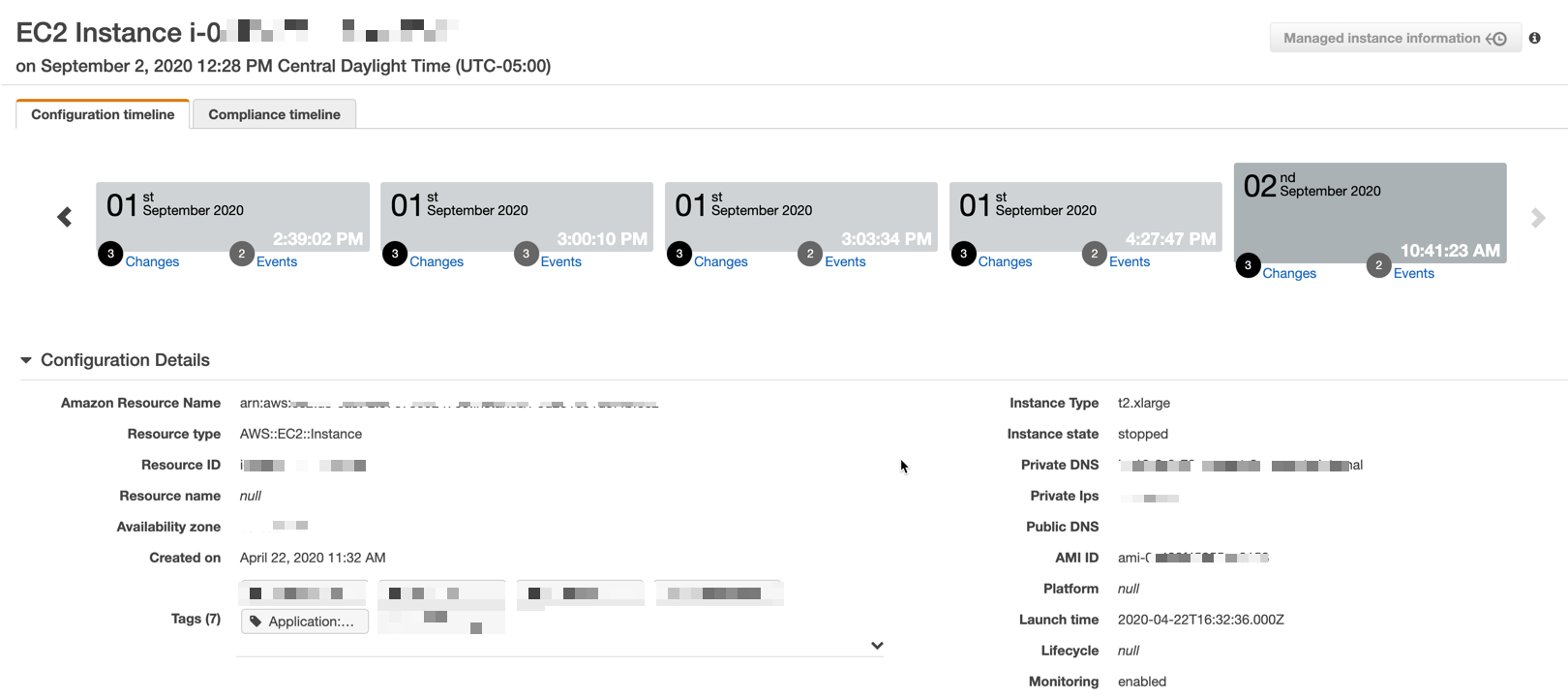
We have covered the use of AWS Config using AWS managed rules in this blog. Once configured, the outcome of the evaluation will be available in the dashboard view. In this example, you know we have an EC2 instance which is considered non-compliant out of potentially hundreds. We now can quickly identify the non-compliant resource and take the necessary steps to bring it back into compliance.
You can gain further insights into the compliance issue by following the links from the Rule name to review the configuration timeline.
In part II we will leverage AWS Config custom rules and AWS Lambda to illustrate how you can audit SAP application-level configuration files. If you have questions or would like to understand the options for your SAP systems, please contact us at sap-on-aws@amazon.com or visit aws.com/sap to learn more. Start building on AWS today and have fun!