AWS for M&E Blog
Back to basics: conditional access vs. digital rights management
In this blog, technologies used to protect content from unauthorized access in the direct-to-consumer (D2C) video delivery domain are discussed and presented in laymen’s terms.
To start, let’s answer the question: Why is D2C content protection needed in the first place?
Premium video content production is a complex and expensive process. Large budgets are dedicated to film production, sporting events, TV shows, musical events, and more. If D2C content is not protected in its distribution (in the sense that anyone can view it and reuse it where they like), it can find its way to consumers without proper authorization and payment, compromising return on investment to stakeholders.
Rights owners often legally oblige distributors to protect D2C content from unauthorized access. The entire distribution chain needs to be protected to avoid content leaks.
Figure 1: Basics of content protection
To learn how linear TV and on-demand video is delivered, please refer to our previous Back to basics: HTTP video streaming blog post.
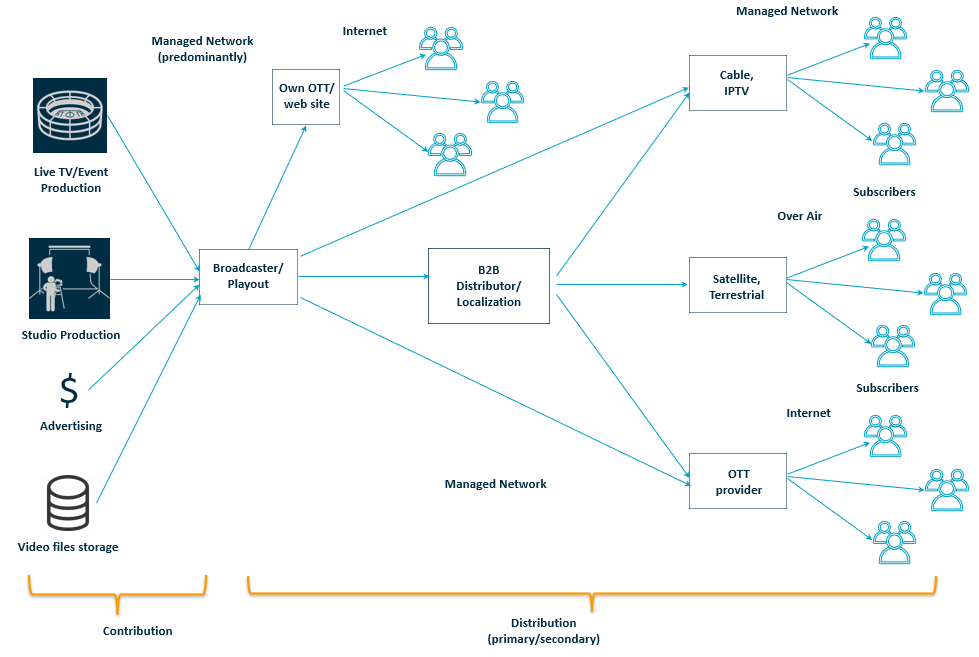
Figure 2: Delivery video chains
We can view the market for D2C content delivery in two different ways: traditional broadcast using either cable, over-the-air, or satellite, and over-the-top streaming (OTT) via the internet. There are a smaller number of providers using IPTV, but from a content protection point of view, they use the same technology as OTT.
Now, let’s focus on the major difference between these two.
Broadcast is a one-way delivery method. The end customer device can’t send any data back to the content distributor by default. Internet streaming is a two-way delivery method. The end customer device needs to communicate with the content distribution chain to work properly. So, the first method of delivery is unidirectional (without a return channel), and the second is bidirectional (with a return channel).
Both ways require content protection, and because of different return channel capabilities, there are two different types of content protection in use between OTT and traditional broadcast delivery.
Conditional Access System
A Conditional Access System (CAS) is designed for unidirectional systems like satellite, terrestrial, or cable TV. DVB standardized the SimulCrypt standard many years ago, which specifies most of such systems and has found broad adoption around the world.
There are two fundamental functions used in conditional access systems for digital broadcasting: scrambling and access control.
To protect content from unauthorized access, it is encrypted. The process of content encryption is also called scrambling. End users can only gain access to decrypt content once certain criteria are met. That criteria is usually based on hardware security via the presence of a smart card or dedicated chip in a set-top box (receiver/decoder) or TV.
This is where access control comes in, by provisioning information to allow authorized users to descramble protected content.
All SimulCrypt based systems encrypt the payload only. For protected delivery, the program payload is scrambled, requiring authorization at the receiver for viewing. To allow an individual receiver authorization in the access system, a multilayer encryption system is deployed and managed by the CAS and the subscriber management system (SMS). Figure 3 illustrates the basic block diagram of the CAS.
Scrambling is done with a control word (CW) that functions as a key for both the encryption process and the decryption process. To make it hard to hack the encryption system, the control words change periodically. All receivers need access to the CW, so it is included in the transport stream in entitlement control messages (ECM), which are also encrypted.
To decrypt the ECMs, each receiver receives unique Entitlement Management Messages (EMMs), which includes the key to decode the ECM and a list of content that the particular receiver is authorized to view. Again, the EMMs are also encrypted, but with a fixed key that is unique to and stored on the receiver, typically in the form of a smart card, allowing the receiver to work its way from EMM to ECM to the content itself. The specifics of ECMs and EMMs are not standardized, and implementation depends on the particular CAS provider (such as Irdeto, Nagra, Verimatrix, Synamedia, etc). For SimulCrypt, it enables multiple different CAS systems to share the same key generator, hence allowing different CAS system to authorize the same underlying scrambled service to different receivers.

Figure 3: Conditional Access System block diagram
Digital Rights Management
Digital Rights Management (DRM) is a digital licensing system that gives content owners complete control over how, who, when, and where content is consumed.
DRM is designed for two-way systems like IPTV and OTT. It encrypts digital media, which can then only be accessed by someone with the decryption key. In addition, DRM can support a broad range of business logic, allowing platforms to build in functionality including purchase, subscription, rental, and gifting. It also allows playback on single or multiple platforms via streaming or downloading, can provide playback restrictions via HDMI outputs, and a lot more.

Figure 4: DRM system block diagram
There are three major DRM technologies on the market today: PlayReady from Microsoft, Widevine from Google, and FairPlay from Apple.
Let’s take a closer look at each of the individual components of a DRM solution and how they collaborate to securely protect content.
Encryption usually happens as one of the video delivery preparation steps during packaging. The most common and efficient encryption algorithm today is AES (Advanced Encryption Standard). It is a symmetric-key algorithm, which means that the same key is used to encrypt and decrypt the data. Most modern DRM technologies use AES with at least 128-bit keys.
Usually, a separate service is used to generate these keys. Keys can be generated once and used as a static value or can be dynamically generated/rotated within a defined interval. This service synchronizes the keys it generates with the license service, which provides the keys to the video player (viewer) in a secure way.
It is common to use the Content Protection Information Exchange Format (CPIX) for content key exchange between the encryptor and the DRM key generation service. There are various other key exchange specifications in use; for example, Amazon Web Services (AWS) provides the Secure Packager and Encoder Key Exchange API specification (SPEKE), which is supported by many DRM vendors.
On the viewer side, to be able to watch a video, the video player should get decryption keys from the license service. The keys are encrypted and delivered as an individualized DRM license.
Before the DRM license request can be made, the viewer needs to communicate with the entitlement service and ask permission to watch specific content. Every video platform has different authorization rules that depend on their specific business model. Some of them will grant a DRM license for every legitimate user of the system. Some could implement complex rules based on the user’s subscription tier, number of used devices, geography, etc.
The entitlement service will provide a token to the player only if the viewer is granted access to the content.
The player will then include the received token in a DRM license request, which is forwarded to the DRM license service. The license service will then provide the license, which includes the key to decrypt the content.
It is crucial to maintain control over the decryption keys at all times to secure control of what users can do. Otherwise, any authorized user could hack the system, decrypt the video, and publish it to the internet. A trusted component on the client-side is needed to ensure this. It’s called the Content Decryption Module (CDM). Various DRM technologies, such as Widevine, PlayReady, and FairPlay come with their own CDM. Only the CDMs that perform all content processing, cryptography, and control in the Trusted Execution Environment (TEE) of the device’s processor can receive DRM license types that require a secure decoding pipeline, like PlayReady SL3000 or Widevine Level 1.
The player turns to the CDM after creating the DRM license request received from entitlement service token. The CDM creates a protected payload that the player must send to the DRM license service. The response contains the DRM license. It is encrypted in such a way that only the CDM that originally created the license request can decrypt and use it.
The decryption of video frames and playback is performed by the CDM. As such, the player itself or any part of a customer application never gets access to the unencrypted video.
Alternatives
In addition to DRM, alternative mechanisms for content protection can be used (sometimes along with DRM) for OTT, like tokenization. For information about how to protect content using secure tokenization, see Secure Media Delivery at the Edge on AWS.
Conclusion
Both CAS and DRM technologies exist to protect content in a way specific to their delivery environment. With an understanding of the differences between DRM and CAS, we encourage you to explore building your own video workflows using AWS. Purpose-built AWS Media Services like AWS Elemental MediaPackage, AWS Elemental MediaLive and AWS Elemental MediaConvert are a great place to start building your own platforms.
Also, please, check out this free one-hour foundational video that breaks down important video technology concepts to help you further understand the processes involved in getting content from a source to the viewer’s screen.