AWS Security Blog
How to use Google Workspace as an external identity provider for AWS IAM Identity Center
January 25, 2024: This post is no longer current. Please see this tutorial for the updated info.
March 21, 2023: We modified the description of a permission set in the Introduction.
March 8, 2023: We updated the post to reflect some name changes (G Suite is now Google Workspace; AWS Single Sign-On is now AWS IAM Identity Center) and associated changes to the user interface and workflow when setting up Google Workspace as an external identity provider for IAM Identity Center.
September 12, 2022: This blog post has been updated to reflect the new name of AWS Single Sign-On (SSO) – AWS IAM Identity Center. Read more about the name change here.
May 4, 2021: AWS IAM Identity Center (IAM Identity Center) currently does not support G Suite as an identity provider for automatic provisioning of users and groups, or the open source ssosync project, available on Github.
January 11, 2021: This post has been updated to reflect changes to the G Suite user interface.
August 3, 2020: This post has been updated to include some additional information about managing users and permissions.
July 6, 2020: Original publication date of this post.
By controlling access to your Amazon Web Services (AWS) accounts using an external identity store, such as Google Workspace, you can create, manage, and revoke access from a single location. Using a single location to manage identities simplifies integration with human resources processes and reduces the requirement for long-lived credentials within your accounts. You can use federation to obtain short-term credentials, which can help reduce the risk of unauthorized access, because if a third-party obtained your credentials, they would have only a limited time to use them.
In this blog post, we will show you how to set up Google Workspace as an external identity provider (IdP) for AWS IAM Identity Center (successor to AWS Single Sign-On). We will also discuss how to configure permissions for your users and the roles that they will assume, and how they can access different accounts.
Introduction
Google Workspace (previously known as G Suite) is used for collaboration functions like email, calendar, Slides, Meet, Drive, Chat, Sheets, Docs, Sites, and Forms. If your organization uses Google Workspace, it can serve as an identity provider (IdP) for AWS. You can connect Google Workspace to IAM Identity Center, allowing your users to access AWS accounts with their Google Workspace credentials.
Access to IAM Identity Center through Google Workspace is granted to accounts governed by AWS Organizations, a service that allows you to centrally-manage multiple AWS accounts. For more information, see the AWS Organizations documentation. The user’s permissions in an account are determined by permission sets defined in IAM Identity Center.
Permission sets simplify the assignment of AWS account access for users and groups in IAM Identity Center. For example, you can create a Database Admin permission set that includes policies for administering AWS RDS, DynamoDB, and Aurora services, and use that single permission set to grant access to a list of target AWS accounts within your AWS Organization for your database administrators. A permission set is a template that you create and maintain that defines a collection of one or more IAM policies. When you assign a user or group to a permission set in an account, IAM Identity Center creates a corresponding IAM Identity Center-controlled IAM role in the account, and attaches the policies specified in the permission set to the role. IAM Identity Center manages the role, and allows the users that you authorized to assume the role, by using the IAM Identity Center Access Portal or AWS Command Line Interface (CLI). As you modify the permission set, IAM Identity Center ensures that the corresponding IAM policies and roles are updated accordingly.
Permissions granted to each user should follow the least privilege principle. By only granting users the permissions needed to complete specific tasks, you can reduce the impact of compromised credentials and provide better visibility of activity in your workloads. Using Google Workspace as your IdP with IAM Identity Center allows you to centrally-manage user accounts for your employees in the Google Admin console and have fine-grained control over the access permissions of individual users to AWS resources.
In this post, we walk you through the process of setting up a Google Workspace as an external IdP in IAM Identity Center.
How it works
IAM Identity Center authenticates your Google Workspace users by using SAML 2.0 authentication. SAML is an open standard for secure exchange of authentication and authorization data between IdPs and service providers without exposing users’ credentials. When you use AWS as a service provider and Google Workspace as an external IdP, the login process is as follows:
- A user with a Google Workspace account opens the link to the IAM Identity Center user portal of your organization.
- If the user isn’t already authenticated, they will be redirected to the Google Workspace account login. The user will log in using their Google Workspace credentials.
- If the login is successful, a response is created and sent to IAM Identity Center. It contains three different types of SAML assertions: authentication, authorization, and user attributes.
- When IAM Identity Center receives the response, the user’s access to the IAM Identity Center user portal is determined. A successful login shows accessible accounts.
- The user selects the account to access and is redirected to the AWS Management Console.
This authentication flow is shown in the following diagram.
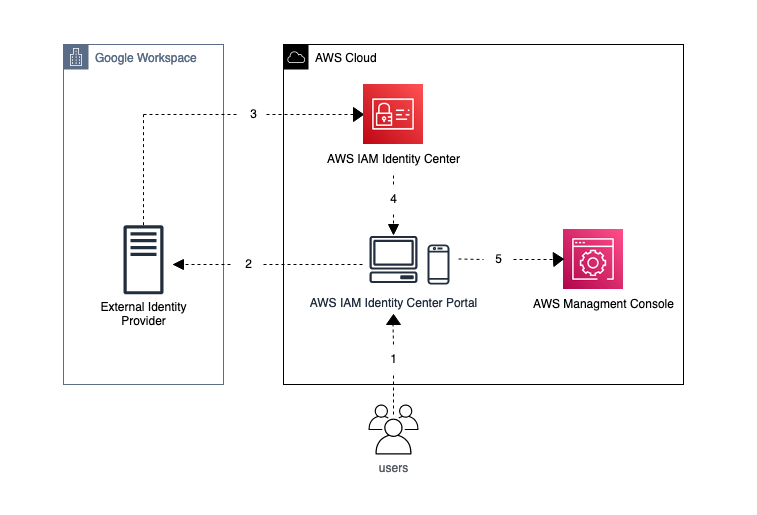
Figure 1: IAM Identity Center authentication flow
The user’s journey starts at the IAM Identity Center user portal after the user is authenticated by Google Workspace, and ends with access to the console, providing unified access to the AWS Cloud without managing user accounts in IAM or AWS Directory Service.
When you use Google Workspace to authenticate and manage your users, you have to create a user entity in IAM Identity Center. The user entity is not a user account, but a logical object. It maps a Google Workspace user through its primary email address as the username to the user account in IAM Identity Center. The user entity in IAM Identity Center allows you to grant a Google Workspace user access to accounts and define its permissions in those accounts.
IAM Identity Center initial setup
If you have not yet enabled IAM Identity Center in your account, complete the following prerequisites to get started with IAM Identity Center:
- Enable IAM Identity Center – When you choose Enable, a window populates and requests that you Create AWS organization. You must complete this step because IAM Identity Center requires AWS Organizations.
- Choose your identity source.
- Create an administrative permission set.
- Set up AWS account access for an administrative user.
- Sign in to the AWS access portal with your administrative credentials.
- Set up AWS account access for additional users (optional).
- Set up single sign-on access to your applications (optional).
If you previously set up IAM Identity Center but have not yet created an AWS organization, complete the following steps. You must use Organizations because this service grants users access to IAM Identity Center through Google Workspace and allows you to manage multiple AWS accounts.
- Create an organization.
- Enable all features in your organization.
- Sign in with your organization’s management account (formerly known as the master account) credentials.
- Sign in to the Google Admin console.
- Verify or assign super administrator privileges in Google Workspace.
If you are currently using IAM Identity Center, which is the default IdP for Organizations, see Considerations for Changing Your Identity Source before making changes.
To set up an external identity provider in IAM Identity Center
- On the Dashboard page of the IAM Identity Center console, select Choose your identity source.

Figure 2: Choose your identity source
- In the Settings, choose the Identity source tab, select the Actions dropdown in the top right, and then select Change identity source.

Figure 3: Settings
- By default, IAM Identity Center uses its own directory as the IdP. To use Google Workspace as your IdP, you have to switch to an external identity provider. Select External identity provider from the available identity sources.
- To configure the custom SAML application, you will need the Service provider metadata, as shown in Figure 4.

Figure 4: IAM Identity Center SAML metadata
For the next steps, while keeping the Change identity source page open, you will need to switch to your Google Admin console and use the service provider metadata information to configure IAM Identity Center as a custom SAML application.
Google Workspace SAML application setup
Open your Google Admin console in a new browser tab, so that you can copy the metadata information from the previous step. You will use the information to configure a custom SAML application.
To configure a custom SAML application in Google Workspace
- In the Google Admin console, choose the Apps dropdown, and then choose Web and mobile apps.
- In the Add app dropdown, select Add custom SAML app.
- Configure the name of the application. Enter AWS IAM Identity Center as the application name or use a name that clearly identifies this application for your users. Choose Continue.
- To download the Google IdP metadata, choose Option 1: Download IdP metadata and then choose DOWNLOAD METADATA. This downloads an XML file named GoogleIDPMetadata.xml, which you will use to configure Google Workspace as the IdP in IAM Identity Center. Choose Continue.
The GoogleIDPMetadata.xml file is a static IdP metadata file that allows Google (the IdP) to establish a circle of trust with IAM Identity Center. This allows Google to authenticate users for IAM Identity Center. This is a public certification that is not considered sensitive data.

Figure 5: Download IdP metadata
- Fill in the Service provider details using the data from IAM Identity Center, and then choose Continue. The mapping for the data is as follows:
- For ACS URL, enter the IAM Identity Center Assertion Consumer Service (ACS) URL.
- For Entity ID, enter the IAM Identity Center issuer URL.
- Leave the Start URL field empty.
- For Name ID format, select EMAIL.

Figure 6: Add service provider details
- On the Attribute mapping page, leave the default settings and choose Finish.
- The final step is to enable the application for your users. On the application page, expand the User access section by choosing the expand icon in the top corner.

Figure 7: Edit user access
- To help maintain the principle of least privilege, make sure that the Service status is OFF for everyone for All users in this account. Only users that need access to AWS should have the service enabled.

Figure 8: Service status
- If you want to manage access for particular users, you can do so through organizational units. These units are part of the tree structure within your Google Workspace account and allow you to manage users in a hierarchical structure. For example, you can enable the IAM Identity Center application for your engineering department. To use organizational units, select the arrow next to Organizational Units, and under Service status, select ON and choose SAVE.

Figure 9: Service on for everyone
You’re done configuring IAM Identity Center in Google Workspace. Return to the browser tab with the IAM Identity Center configuration.
IAM Identity Center configuration
After you create the Google Workspace application, you can finish the setup by uploading the Google IdP metadata in the console.
To add IdP metadata in IAM Identity Center
- In the IAM Identity Center console, navigate back to the Configure external identity provider page.
- When you configured the custom application in Google Workspace, you downloaded the GoogleIDPMetadata.xml file. On the configuration page, select Choose File, select this file from the destination where you downloaded it, and then choose Next.
- Under Review and confirm, read through the list of consequences. If you are moving from Active Directory, using Google Workspace as an external IdP with IAM Identity Center will not be reversible.

Figure 10: Confirm changes
- When you are ready, enter ACCEPT at the bottom of the list of changes and choose Change identity source to complete the setup.
- Next is a message that your change to the configuration is complete. You will automatically be rerouted to IAM Identity Center Settings.
Manage users and permissions
IAM Identity Center supports automatic user provisioning through the System for Cross-Domain Identity Management (SCIM). However, this is not yet supported for Google Workspace custom SAML applications. AWS and Google are collaborating in the Fast Federation (FastFed) Working Group to enable this. In the meantime, you can either manually create users and groups or use the ssosync project from awslabs to automate the process. Manual provisioning is the simplest option to get started, but it requires additional identity management processes to help ensure that user attributes and group memberships stay up-to-date over time. The ssosync option reduces these processes, but it is open source code that you must properly evaluate before use in production. In this section, we will walk you through the manual option. You will learn more about ssosync and how to use it later in this post.
To add a user to IAM Identity Center
- In the IAM Identity Center console, in the left navigation pane, select Users and then choose Add user.
- Enter the user details and use your user’s primary email address (<username>@<googleworkspace_domain.com>) as the username. Choose Next to add the user to a group.
- Skip the Add user to groups step by selecting Next. We aren’t going to create user groups in this walkthrough.
- Choose Add User.
- You will reach the user list page that displays your newly created user with status Enabled.

Figure 11: User list
- The next step is to assign the user to a particular account in your organization. This allows the user to access the assigned account. In the left navigation pane, under the Multi-account permissions dropdown, select AWS accounts. Then select the account that you want to assign your user to and choose Assign users or groups.

Figure 12: Assign users
- Select the user that you just added, and then choose Next to continue configuring the permissions of the user in the assigned account.

Figure 13: Select user
- Because you did not configure a permission set yet, you need to configure one now. Choose Create permission set.
- IAM Identity Center has managed permission sets that are similar to AWS managed policies. Make sure that Predefined permission set is selected, and then select the desired permission set that will give users the ability to only perform necessary tasks with the most restrictions. For this walkthrough, we will use the permission set ViewOnlyAccess because it is the most restrictive permission set. You have the option to use a custom permission set for more granular control. A custom permission set allows you to combine AWS managed and customer managed polices in IAM with inline policies and permissions boundaries. After you have selected the permission set, choose Next

Figure 14: Create permission set
- You have the option to specify additional configurable details for the permission set, such as Session duration, which limits the time a user can be logged into the console; and Relay State, which allows you to create a specific URL so that each user can have access to the console relative to their role. The default session duration is one hour, and relay state is an optional setting that you can leave blank. After you adjust these settings to your desired values, select Next.
- Review the configuration for the permission set and choose Create. You will see a message stating that the permission set was created successfully.
- Now that the permission set has been created, you need to assign it to a user or group. In the left navigation pane, under the Multi-account permissions dropdown, choose AWS accounts.
- Select the account that you want to assign the permission set to, and then select Assign users or groups.

Figure 15: Account overview
- Choose the desired Users or Groups under the account that you want to add the ViewOnlyAccess permission set to and select Next.

Figure 16: Select users and groups
- Under Permission set, select ViewOnlyAccess and then choose Next.
- Review the permission set assignment and choose Submit. You will see a message that the assignment was successful.
Access an AWS account with Google Workspace
You can find your user portal URL in the IAM Identity Center settings, as shown in the following figure. Unauthenticated users who use the link will be redirected to the Google account login page and will need to use their Google Workspace credentials to log in.
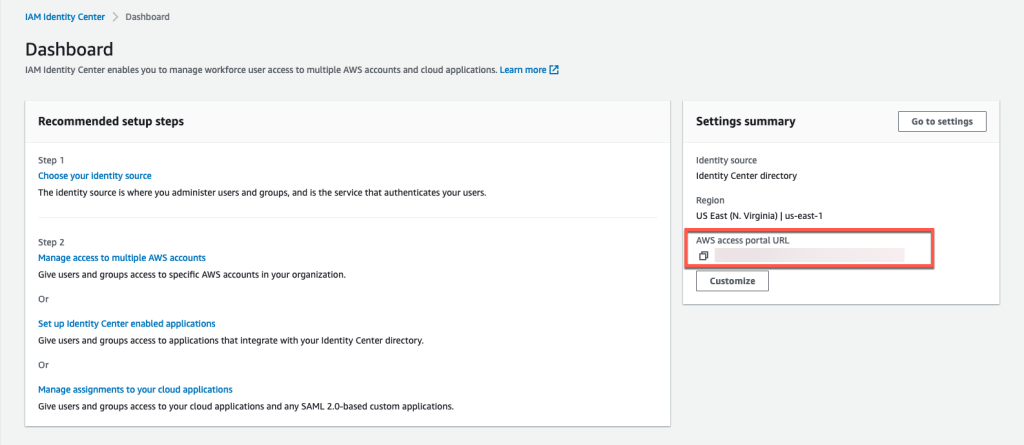
Figure 17: The user portal URL
After authenticating, users are redirected to the user portal. They can select from the list of assigned accounts, as shown in the following example, and access the console of these accounts.
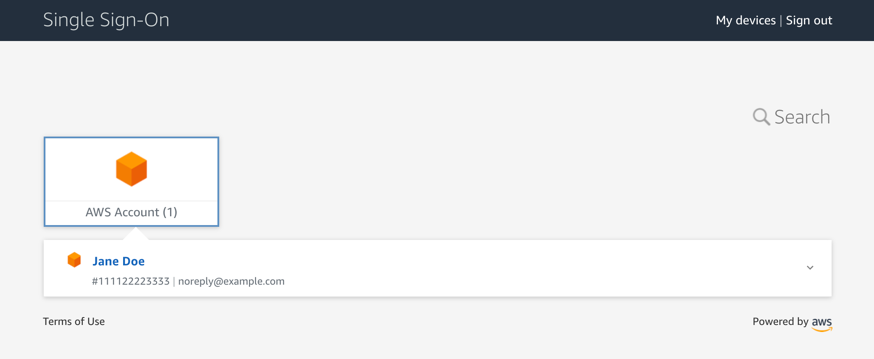
Figure 18: Select an assigned account
You’ve successfully set up Google Workspace as an external identity provider for IAM Identity Center. Your users can access your AWS accounts using the credentials that they already use for their Google Workspace.
Another way your users can use AWS SSO is by selecting it from their Google Apps to be redirected to the user portal, as shown in the following figure. That is one of the quickest ways for users to access accounts.
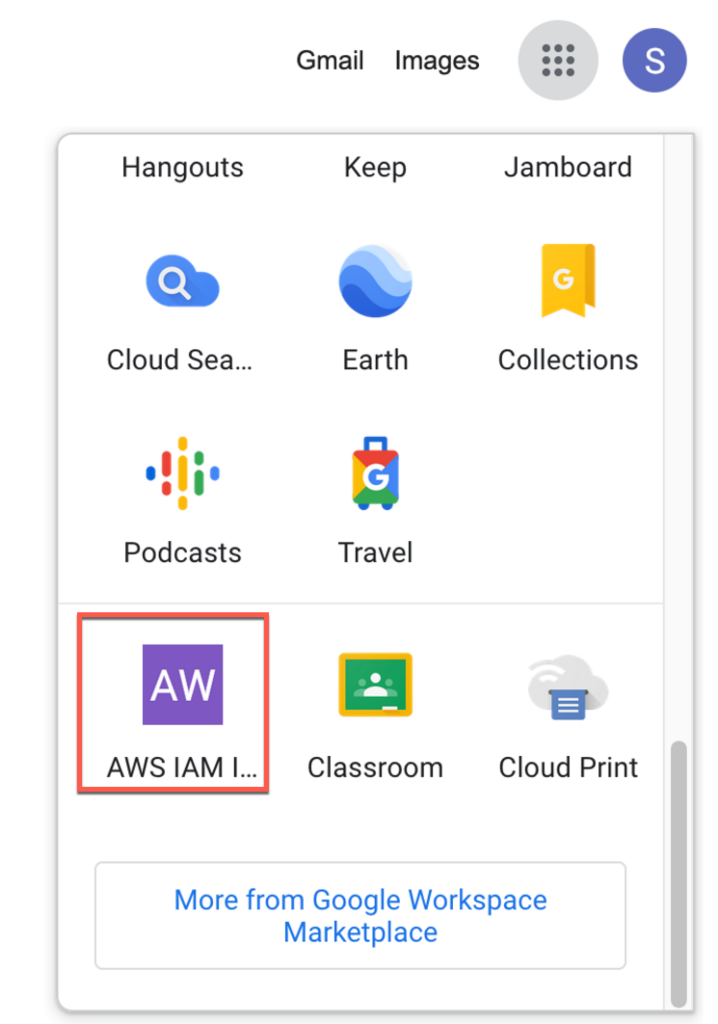
Figure 19: Apps in the user portal
Automatic creation of users and groups
You can use the ssosync project from awslabs to automatically synchronize your users and groups, helping to eliminate the need for manual creation and upkeep. It uses the Directory API in the Google Workspace Admin SDK to fetch your users and groups and then creates them in IAM Identity Center. To get started with ssosync, follow the directions in the ssosync GitHub repository. The ssosync project is under active development. If you choose to use it, you should regularly check for updates, consider contributing through pull requests, and provide feedback through GitHub.
Use AWS CLI with SSO
You can use the AWS Command Line Interface (AWS CLI) to access AWS resources. AWS CLI version 2 supports access through IAM Identity Center. You can automatically or manually configure a profile for the CLI to access resources in your accounts. To authenticate your user, the AWS CLI opens your default browser and verifies your IAM Identity Center login. If you are not authenticated, you’re redirected to the Google Workspace login page. After a successful login, you can select the account that you want to access from the terminal.
To upgrade to AWS CLI version 2, follow the instructions in the AWS CLI user guide.
Conclusion
You’ve set up Google Workspace as an external IdP for IAM Identity Center, granted access to an AWS account for a Google Workspace user, and enforced fine-grained permission controls for this user. This makes it simpler for your business to access the AWS Cloud.
If you have feedback about this post, submit comments in the Comments section below. If you have questions about this post, contact AWS Support.
Want more AWS Security news? Follow us on Twitter.