AWS Storage Blog
AWS re:Invent recap: Data protection and compliance with AWS Backup
At my session at AWS re:Invent 2020-2021, now available on-demand, I had the pleasure of exploring data protection and compliance for cloud workloads with AWS Backup. We were fortunate to have Paul O’Flynn, Principal DevOps Engineer at Workday, join us to elaborate on real-word AWS Backup use cases.
In this blog post, I cover some of the key points I made during my session and provide some helpful links so you can further explore this topic.
AWS Backup background
When starting out in the cloud, new customers appreciate how many AWS resources come with their own backup capabilities. But as their organizations grow and sprawl across the cloud, it becomes burdensome to configure and monitor the backups for each individual resource. Some AWS customers manage thousands of accounts, and some of those accounts contain thousands of resources. Customers responsible for managing such complex deployments ask us for a centralized command center and single pane of glass for their backup, data protection, and business continuity needs.
That is why, less than 2 years ago, we launched AWS Backup, the centralized backup solution from Amazon Web Services. We offer a cost-effective, fully managed, and policy-based service that enables customers to protect their data. AWS Backup can also help customers support their regulatory compliance obligations and meet business continuity goals. With AWS Backup, you can centrally deploy data protection (backup) policies to configure, manage, and govern your backup activity across your AWS resources. This means you can easily manage backups for your Amazon EC2 instances, Amazon EBS volumes, Amazon RDS databases (including Amazon Aurora clusters), Amazon DynamoDB tables, and AWS Storage Gateway volumes. You can also centrally manage your workloads deployed on Amazon EFS, Amazon FSx for Lustre, and Amazon FSx for Windows File Server.
Key re:Invent session takeaway: Introducing cross-account backups
The key takeaway of my re:Invent session, and the focus of this post, is an AWS Backup featured called cross-account backup. This is the first backup feature from AWS that allows customers to copy a backup from one of their AWS accounts to another. Customers can make copies both on-demand or as part of a scheduled backup policy.
With cross-account backup, customers benefit from an additional layer of protection should one of their AWS accounts be accidentally or maliciously deleted. Furthermore, customers have the flexibility to fan in and fan out their backups. By fanning in, a customer takes their backups across multiple accounts and centralizes them in a single repository account, simplifying monitoring. Then, by fanning out, a customer takes those backups and copies them to other accounts, such as those in different AWS Regions, achieving increased resilience.
Customer case study
In my re:Invent session, our customer, Paul O’Flynn, Principal DevOps Engineer at Workday, demonstrated how he and his organization use AWS Backup today. Paul also discusses ways Workday plans to use AWS Backup in the future.
Paul shared his sentiment, “I love AWS Backup for the simple reason that it centralizes all backup infrastructure in one place and thus takes the responsibility of backups away from individual development teams.”
Since deploying AWS Backup at Workday environment, Paul and his team at Workday have been able to meet their top data protection and compliance needs. See the following table of solutions AWS Backup enabled Workday to implement:

Enabling cross-account backup
In order to use AWS Backup, you must have at least two accounts that belong to the same organization in the AWS Organizations service. For more information, see the tutorial on creating and configuring an organization in the AWS Organizations user guide. You must also log into your AWS Backup console using your AWS Organizations management account credentials to enable cross-account backup for your organization.
Choose a source account and a destination account. Your source account is where your primary backups reside, and often contains production resources. Your destination account is where you would like to keep a copy of your backup. You can select more than one destination account.
Assign a AWS KMS key to encrypt backups in the destination account, and a resource-based access policy to allow access to resources copied from the source account. If your resources are encrypted with a customer managed KMS key in the source account, you must share this KMS key with the destination account.
Cross-account backup in action
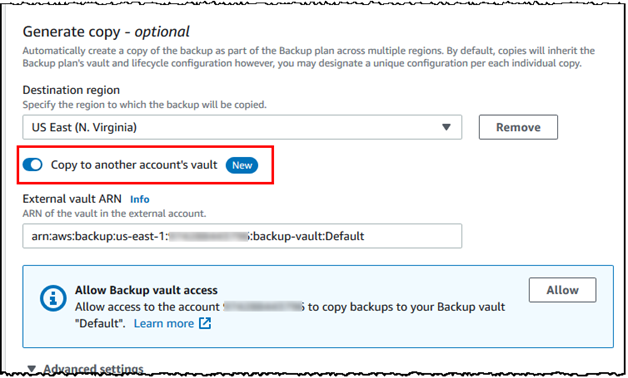
To start your cross-account backups, log into the AWS Backup console. Create an on-demand or scheduled backup as you normally would. In the Generate copy – optional section, select the new cross-account Backup toggle to enter the backup vault ARN for your destination account:
AWS Backup copies your cross-account backups to your source account either on-demand or during your backup policy’s scheduled backup window.
Conclusion
Thank you to everyone who attended re:Invent this year! The AWS Backup team was delighted to receive our audience’s encouragement and suggestions before, during, and after our session. Thank you also to Paul O’Flynn for his demonstration. Bravo!
Cross-account backup is now available to enhance your data protection and compliance needs. It is in all commercial AWS Regions and AWS GovCloud (US). Try it out today, along with cross-Region and cross-account management and monitoring with AWS Organizations.
For pricing information, visit AWS Backup’s pricing page. To get started, see the feature documentation in the public documentation.
If you missed our session at re:Invent, watch it on-demand at re:Invent 2020-2021! If you have any comments or questions about my re:Invent session or this blog post, please don’t hesitate to reply in the comments section.
Empowering your data governance,
— Nancy
