AWS Storage Blog
Simplify auditing your data protection policies with AWS Backup Audit Manager
Have you had to prove to an auditor that you are protecting and retaining data adequately to meet regulatory or organizational requirements? The audit process can be resource intense. To meet an auditor’s criteria, the burden of proof is on you to show that you had proper controls in place to protect and retain your data.
AWS Backup launched a new compliance auditing capability called AWS Backup Audit Manager on August 24, 2021. This feature allows you to evaluate and report on the compliance of your defined data protection policies to help you meet your business and regulatory needs. AWS Backup enables you to centralize and automate data protection of AWS services across compute, storage, and database based on organizational best practices and regulatory standards. AWS Backup Audit Manager helps you maintain and demonstrate compliance with your data protection policies.
In this blog post, we show you how to create AWS Backup frameworks with governance controls and create reports of your backup and compliance status. These reports can be used as demonstrable evidence of your compliance practices, or to identify individual backup activities and resources that are not yet in compliance.
Risk management framework for backups
For the purposes of this blog, we focus on a specific subset of controls in the Risk Management Framework (RMF) as outlined by the National Institute of Standards and Technology (NIST). The RMF outlines comprehensive controls for cybersecurity and is intended to have broad applications, which is why many organizations use RMF as a foundation for their cybersecurity policies. The Contingency Planning (CP) Family of controls addresses policies, procedures, and general technical guidelines for operational continuity. CP-9 (System Backup) outlines a broad definition for data backup that is dependent on the organization and their specific requirements to define things like:
- System components to be backed up (for both user-level and system-level data)
- Frequency and retention of backup, which should align with Recovery Point Objectives (RPOs)
We examine the Control Enhancements under CP-9 from the latest Special Publication (SP 800-53) that are recommended for backups. The control enhancements that we use AWS Backup Audit Manager to validate are:
- CP-9(1) | TESTING FOR RELIABILITY AND INTEGRITY
- CP-9(4) | PROTECTION FROM UNAUTHORIZED MODIFICATION
- CP-9(8) | CRYPTOGRAPHIC PROTECTION
Note: This blog is not meant to be a comprehensive approach to satisfying NIST or any other cybersecurity framework, but rather highlighting tools available to meet certain criteria as it pertains to auditing backup procedures.
The highlighted features with regards to compliance could be used across multiple industry standards, such as Health Insurance Portability and Accountability Act (HIPAA), American Institute of Certified Public Accountants (AICPA) Service Organization Controls (SOCs), etc. Be sure that your security personnel are adhering to the requirements set forth by your organization’s particular regulatory requirements.
Walkthrough
In this section, we show how to use the AWS Backup Audit Manager feature to verify that resources are backed up with the specified frequency and retention and that the backups are encrypted. We also show how to use controls to check if manual deletion of recovery points is prevented.
Prerequisites
- Access to AWS Backup, Amazon Simple Storage Service (Amazon S3), and AWS Config services.
- At least one AWS Backup plan associated with a backup vault. For this blog, we created a backup plan named “MyOrg-Critical-BackupEC2” and a Backup Vault named “MyOrg-Production-CriticalBackups.”
- An S3 bucket where audit reports can be sent. For this blog, we have created a bucket named “myorg-auditcompliance-bucket.”
- Enable recording through AWS Config for your backup plans (AWS::Backup::BackupPlan resource type), backup selection (AWS::Backup::BackupSelection), vaults (AWS::Backup::BackupVault), recovery points (AWS::Backup::RecoveryPoint), and AWS Config resource compliance (AWS::Config::ResourceCompliance).
Note that there is cost associated with AWS Config recording and report storage in Amazon S3.
In this blog, we use an Amazon Elastic Compute Cloud (Amazon EC2) instance tagged with a key of ‘environment’ and a value of ‘production.’
For further information about setting up AWS Backup, you can visit the Getting Started Guide.
Frameworks
AWS Backup Audit Manager is used to audit the compliance of your AWS Backup policies against controls that you define. A control is a procedure designed to audit the compliance of a backup requirement, such as the backup frequency or the backup retention period. AWS Backup Audit Manager framework is a collection of controls that can be managed as a single entity. If you must comply with different internal or regulatory standards, such as NIST, HIPAA, or SOC, you can create multiple frameworks. Multiple frameworks allow you to separately track the compliance of these different standards.
In the AWS Management Console, navigate to AWS Backup dashboard page and select Get started with frameworks.
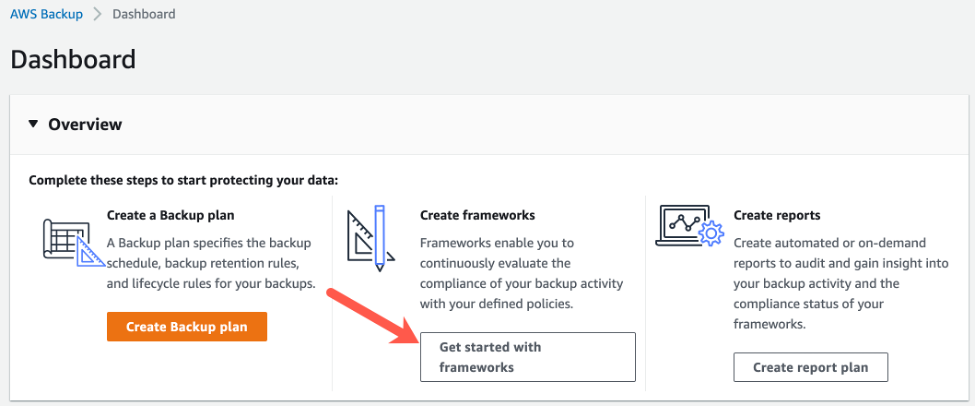
Figure 1: AWS Backup – Get started with frameworks
On the Frameworks home page, verify that you have turned on AWS Config recording by checking Resource tracking status on the Framework page. Next, select Create framework to begin.
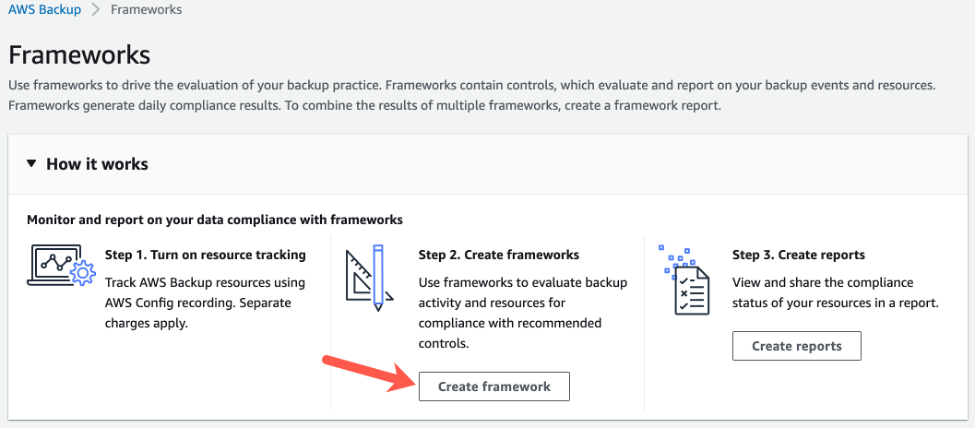
Figure 2: Frameworks home page (Create framework)
First, give your new framework a name and decide what type of framework to create. The AWS Backup framework contains all five controls by default. For this example, we create a custom framework to show each of these controls. We will use this framework to validate that our mission critical EC2 instances are adequately backed up according to our organizational policy.

Figure 3: AWS Backup Audit Manager Framework creation wizard
The Backup resources protected by backup plan control evaluates if selected resources are protected by backup plan(s). By default, All resources will be highlighted, but you can also use tags or choose resources by type to simplify your framework management. For this example, we recommend changing the control scope to Resource Type and then selecting EC2 as the resource type that is already tagged by specifying the environment key with a value of production. We want to make sure that this resource is backed up daily and backups are kept for at least 30 days. The Backup plan minimum frequency and minimum retention control is used to evaluate the minimum frequency and minimum retention of your backups.
By default, this will evaluate all backup plans, but you can also select specific backup plans.
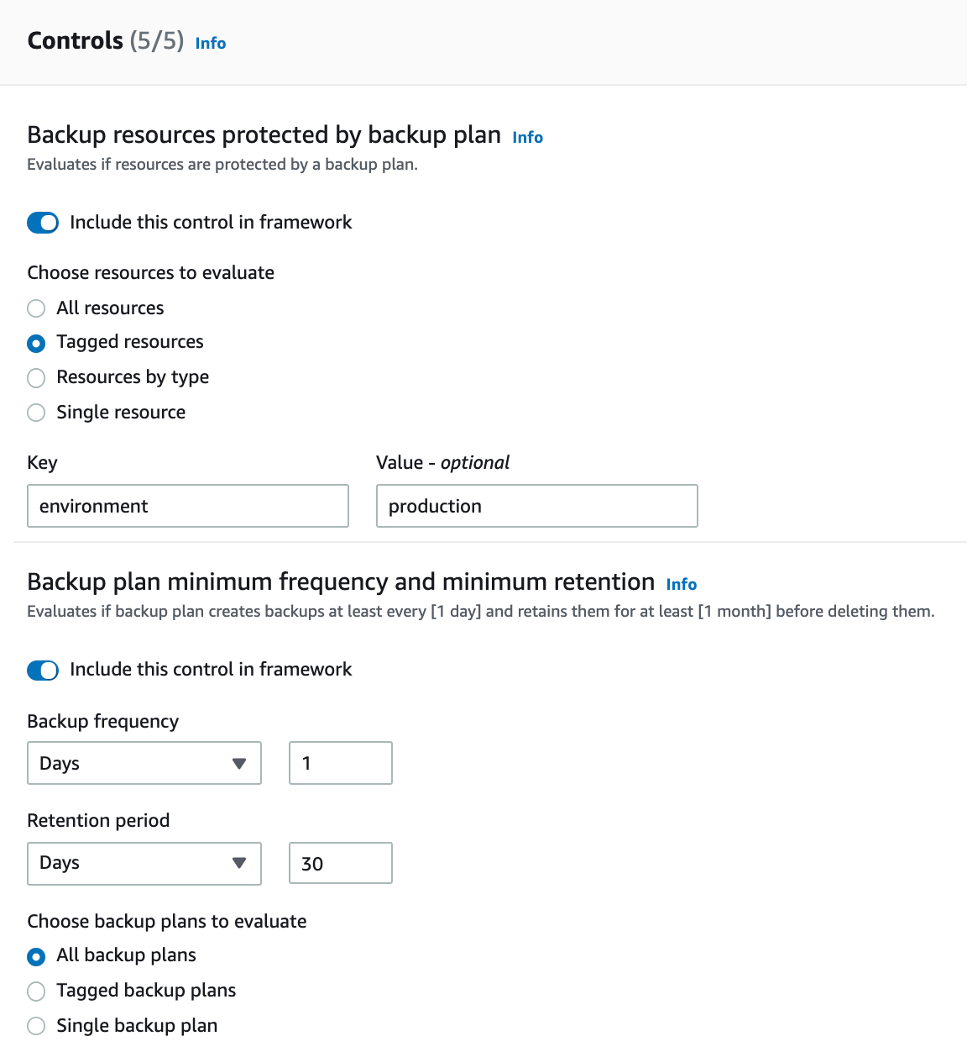
Figure 4: Controls for frequency/retention of selected resources and backup plan(s)
Next, you can evaluate if selected backup vaults prevent manual deletion of recovery points. The Backup prevent recovery point manual deletion control allows you to add up to five IAM roles that could be allowed to manually delete recovery points if there are exceptions.

Figure 5: Controls for prevention of manual recovery point deletion
The Backup recovery point encrypted control evaluates if the backup recovery points are encrypted. You can check that all recovery points are encrypted (by default). This control also lets you evaluate selected recovery points with specific tags.
Figure 6: Recovery point encryption
Finally, you can specify parameters to ensure that selected resources have valid recovery points in your backup vault and that the recovery points are retained for at least the specified Backup recovery point minimum retention period.
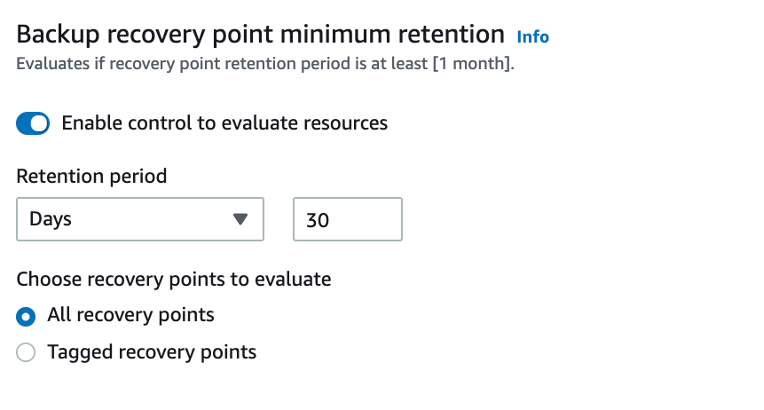
Figure 7: Recovery point retention
Once you have created a framework, AWS Backup Audit Manager evaluates the controls. You can check the compliance status of the frameworks and controls on the console. You can also create audit reports to be used for verification that your backup plan, backup vault, and recovery points are meeting the required controls for the specified resources. This means that you can create backup plans that adhere to your organizational compliance requirements, then use AWS Backup Audit Manager to verify that your resources are actually protected while adequately meeting your controls.
Reports
Now that we have a framework established to assess our backup activity, we will want to create a report to see if our controls have been met using report plans.
In the console, navigate to AWS Backup once again, and now choose Create report plan from the dashboard.

Figure 8: AWS Backup dashboard (Create report plan)
In the next screen, select the type of report to run. You can create Backup activity reports, as well as Compliance reports.
In this example, we select the Resource compliance report to audit whether or not the controls we selected for our framework are adequately enforced. Control compliance report contains summary of frameworks and resource compliance report has compliance details of each resource. You can define what all frameworks you want to include in a single report while creating a report plan.
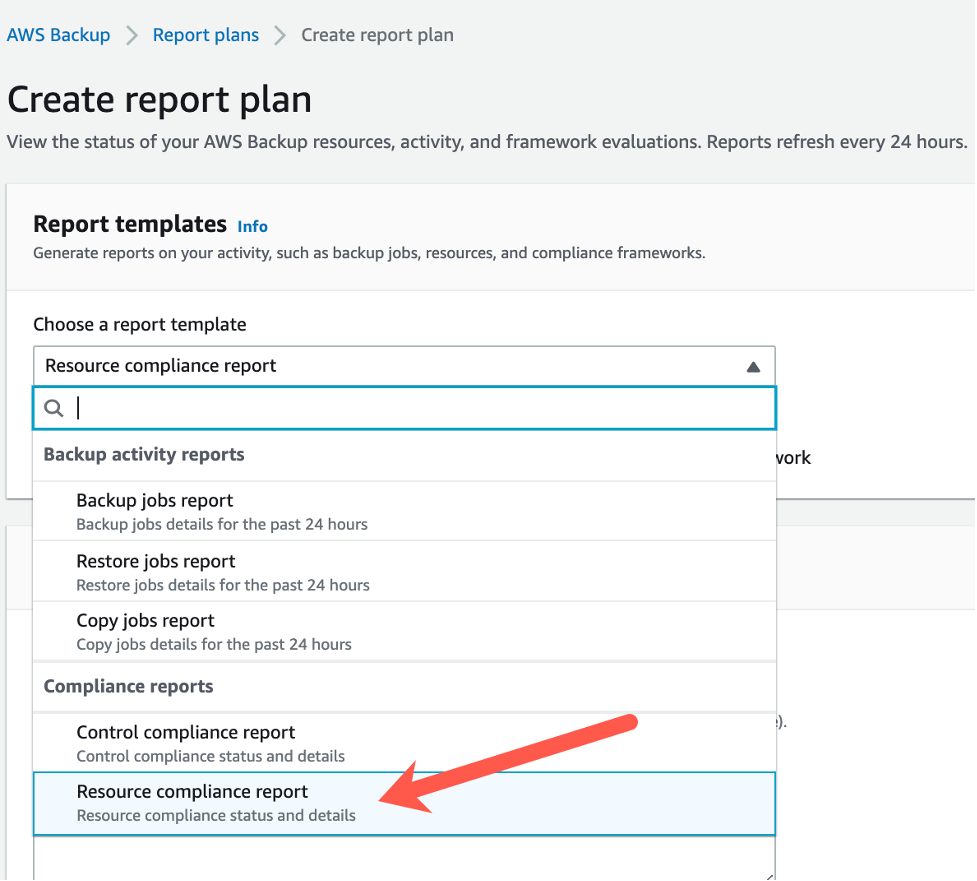
Figure 9: Report plan templates
Give this report a name and choose the framework(s) you want to evaluate. Note that you can aggregate compliance results from multiple frameworks and AWS Regions.

Figure 10: Resource compliance report plan creation
Next, you need to choose the File formats for your report, which can be in CSV and/or JSON. You also need to select the S3 bucket you want reports delivered to. Selecting Edit bucket policy takes you to the selected bucket policy where you can make sure that the appropriate permissions are assigned.
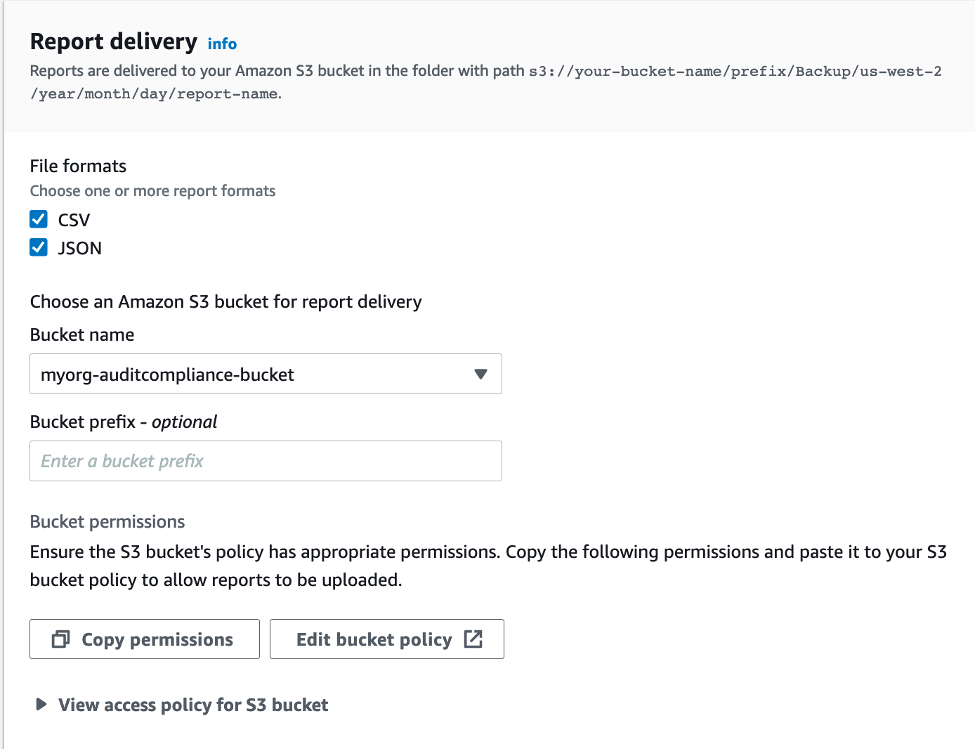
Figure 11: Report delivery format and bucket location
Make sure you have added the necessary permissions and then select Save changes.
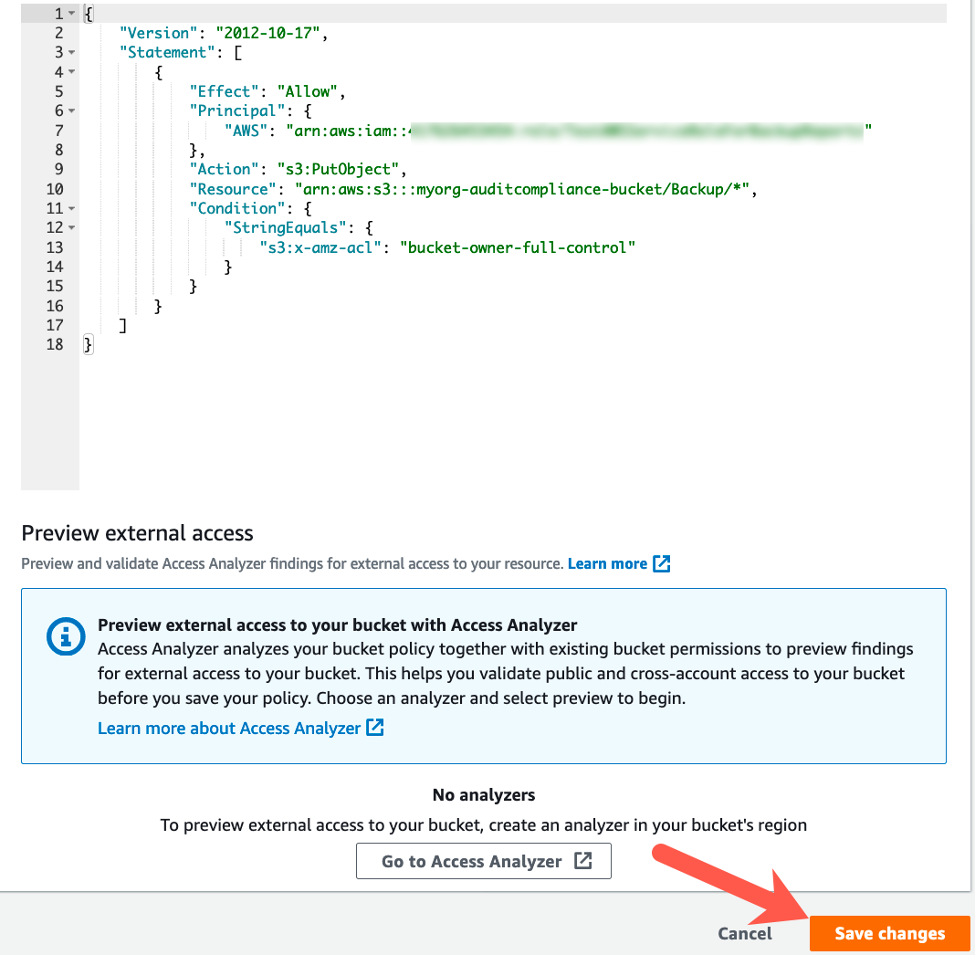
Figure 12: Amazon S3 Bucket permissions
Finally, go back to the report creation wizard and select Create report plan. Reports are generated every 24 hours. The timing of the daily report might fluctuate over several hours because AWS Backup Audit Manager performs randomization to maintain its performance. You can also run an on-demand report anytime. Let’s navigate to our newly created report plan and select Create on-demand report to generate an audit report. Once this operation completes, there will be a link to the generated report under the Reports section, as seen in the following screenshot. This link takes you to the Amazon S3 bucket where your reports are stored in your selected formats.
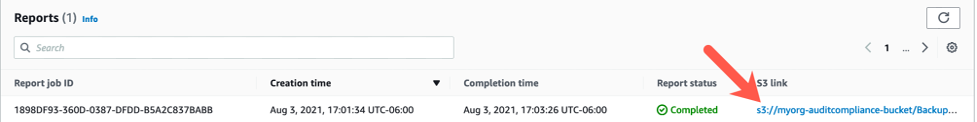
Figure 13: Example link to a report
The following example shows the information contained in CSV format for the controls compliance report.
This report shows whether or not your AWS Backup plans are enforcing the controls in your framework. If you chose to prevent manual deletion of restore points and encrypt backup data in your vault, this should help to satisfy the controls for RMF CP-9(4) and CP-9(8).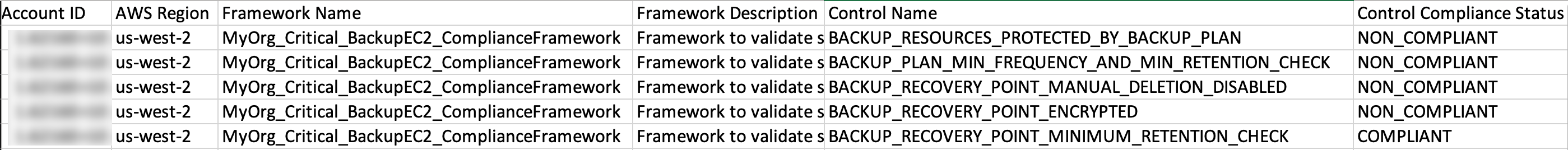
Figure 14: Example of a ‘Compliance report’ in CSV format
Another example can be seen of the backup jobs report, which shows all jobs from the past 24 hours.
Figure 15: Example of a ‘Backup jobs report’ in CSV format
The report tells us when the job ran, whether it completed or failed (with a status message if it did fail), the size of the backup, how long the job ran for, the vault it was written to, etc. This can be useful to show you have a valid backup of a selected resource on durable storage that spans multiple Availability Zones, which can be useful for satisfying RMF CP-9(1).
Again, there are several report templates to choose from. Backup activity reports allow you to view the history and status of AWS Backup backup jobs, copy jobs from one backup vault to another, and restore jobs from a backup vault. Compliance reports allow you to view your control compliance or resource compliance status. In other words, you can choose to report from the perspective of your selected framework controls to get a summary of your compliance status, or you can choose to report on resources in your environment to see if they meet the selected framework controls. These different views can be useful for identifying where there may be gaps in coverage between what your organization requires and what policies are assigned.
Cleaning up
AWS Config recording, AWS Backup evaluations, storage for reports in Amazon S3 are charged. There is no cost associated with the AWS Backup auditing. To avoid incurring additional cost due to resources created in this walkthrough, delete the EC2 instance, S3 bucket, and AWS Backup resources including Frameworks and report plans.
Conclusion
In this post, we showed how you can use AWS Backup Audit Manager to create a framework for validating if you are backing up resources with appropriate frequency and retention, and enforcing proper cybersecurity controls. We also used AWS Backup Audit Manager to generate reports used to validate that backup jobs have completed successfully, that restore points cannot be manually deleted by unspecified users, and that restore points are encrypted at rest on top of highly durable, highly available storage.
By leveraging AWS Backup Audit Manager, you can validate your controls and report on compliance for audit purposes. This simplifies the process of auditing your backup resources and helps with generation of on-demand reports for your backup governance purposes.For more information on AWS Backup Audit Manager, check out the AWS documentation and video introducing AWS Backup Audit Manager.
Thanks for reading this blog post on AWS Backup Audit Manager. If you have any comments or questions, feel free to leave them in the comments section.