AWS Partner Network (APN) Blog
How AWS Transit Gateway Optimizes Aruba SD-WAN at Global Scale
By Bala Mugunthan, Sr. Partner Solutions Architect at AWS
By James Wenzel, Sr. Partner Solution Architect – Networking at AWS
 |
In this post, we will describe simplifying global network architecture using AWS Transit Gateway with Aruba SD-WAN branch-to-cloud connectivity. We’ll also explore how Aruba’s customers have leveraged the benefits of AWS Transit Gateway at a global scale.
Aruba, a subsidiary of Hewlett Packard Enterprise, is a global leader in secure, intelligent edge-to-cloud networking solutions. Aruba uses a cloud-native approach to help each customer with all aspects of wired, wireless LAN, and wide area networking (WAN). Hewlett Packard Enterprise is an AWS Advanced Consulting Partner.
Enterprise cloud adoption continues to increase globally, yet as the number of organizations planning to run production applications on the cloud grows, customers still intend to maintain a measurable on-premises IT environment.
Furthermore, the increasingly distributed nature of organizations and their applications make IT environments more complex and difficult to manage. These organizations need to ensure their cloud-based resources are networked to their on-premises environments, and to one another, without incurring additional IT network complexity and associated costs.
Typically, connecting on-premises offices and data centers to the cloud requires the use of point-to-point (P2P) connections, such as IPsec Virtual Private Network (VPN) tunnels or private network fiber connections.
Connecting virtual networks (groups of networked cloud resources) with one another also requires P2P connections. However, as the number of on-premises offices and virtual networks increase, the number of P2P connections grows, resulting in a large mesh network that can be difficult, cumbersome, and costly to manage.
Global Networking
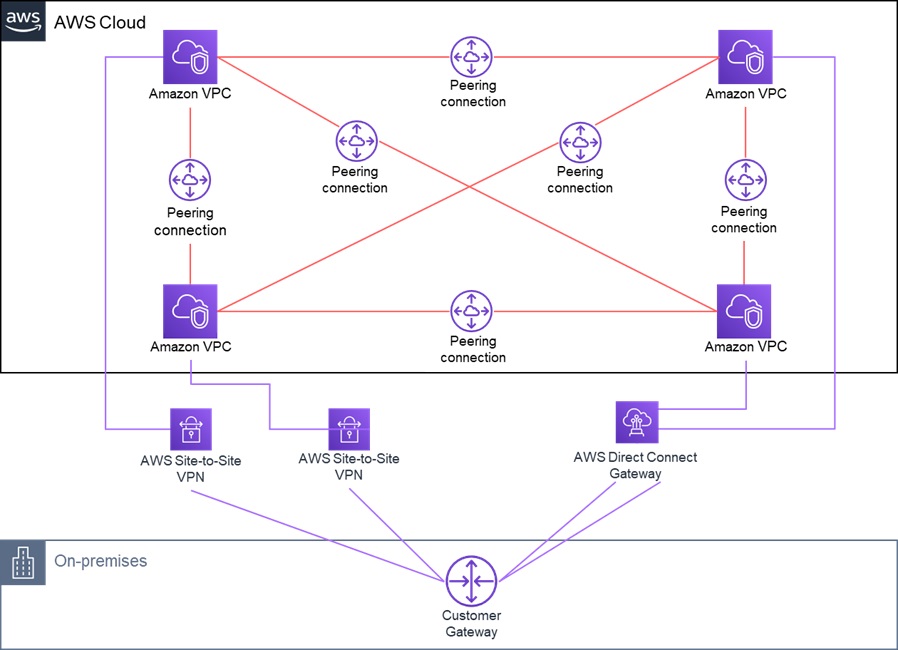
Customers using Amazon Web Services (AWS) have typically used AWS Direct Connect and AWS Site-to-Site VPN connections for connecting their on-premises environment to individual Amazon Virtual Private Clouds (VPCs), and VPC peering for connecting their Amazon VPCs with one another.
Figure 1 – On-premises deployment to AWS constructs.
As customers deployed more geographically dispersed VPCs, AWS initially offered a networking construct called a transit VPC to manage their growing AWS environments. This served as a central hub for VPC peering connections, as well as connections between Amazon VPCs and on-premises locations.
While the transit VPC helped to centralize network connectivity, customers would still need to manually configure redundant third-party virtual routers within the transit VPCs. Should issues arise with the transit VPC, customers would need to coordinate external support between multiple vendors.
Ideally, customers should be able to connect their cloud and on-premises resources without adding network complexity and ongoing management and operational effort.
AWS Transit Gateway
AWS Transit Gateway is a managed, regional, and scalable service that enables organizations to interconnect a large number of Amazon VPCs and on-premises networks without relying on numerous point-to-point connections or the transit VPC.
AWS Transit Gateway simplifies how customers connect their Amazon VPCs with one another and to their on-premises networks within a region by serving as a central point for Layer 3 network connectivity. By enabling a hub-and-spoke topology, the solution can help customers reduce the number of VPC peering connections and consolidate access to the on-premises network.
Even though the number of VPCs is small and there’s only one enterprise location shown in Figure 1 above, it’s easy to see how the AWS Transit Gateway simplifies the environment. Imagine how much complexity is removed when there are additional enterprise locations and Amazon VPCs that can be up to 5,000 concurrent connections serving.
Now, customers can simply connect their on-premises networks and Amazon VPCs via AWS Transit Gateway.
Figure 2 – AWS Transit Gateway reduces the number of P2P connections.
Routing Traffic with AWS Transit Gateway
Amazon VPCs and on-premises locations connect to AWS Transit Gateway via transit gateway attachments. These enable AWS Transit Gateway to route traffic to the correct destination either on-premises or on the AWS Cloud.
When connecting an Amazon VPC with AWS Transit Gateway via a transit gateway attachment, AWS Transit Gateway’s default route table is automatically populated with the destination IP addresses of the attached Amazon VPC to which AWS Transit Gateway can direct traffic.
Routing outgoing traffic from an Amazon VPC requires an administrator update the VPC route table with the relevant destination IP addresses. When attaching an on-premises location to AWS Transit Gateway either via a VPN tunnel or AWS Direct Connect, a similar exchange of IP address information occurs.
Figure 3 – AWS Transit Gateway routing.
Customers can also segment and isolate network traffic by creating 20 route tables within AWS Transit Gateway (this is a soft limit and can be increased). Each route table corresponds to a routing domain that directs traffic to specific Amazon VPCs or on-premises locations based on business needs.
Because AWS Transit Gateway can support multiple route tables in a region, an administrator can control routing on a per-attachment basis. Customers find it easy to consolidate ingress and egress to a single VPC due to managed routing, and this allows you to save operational costs on the number of firewalls or NATed Gateways needed for deployment.
Many customers have requirements to leverage on-premises existing firewall technology to get started in AWS using existing firewall expertise. A large number of firewall vendors have versions of their software in AWS Marketplace that work either Bring Your Own License (BYOL) or pay-as-you-go pricing models. These appliances integrate nicely with existing AWS technologies like AWS Transit Gateway and Elastic Load Balancing.
Reducing the overall number of P2P connections to create and configure individually, as well as dynamic routing between AWS Transit Gateway and a customer’s on-premises locations and Amazon VPCs, helps to decrease network complexity while increasing operational efficiency.
Creating AWS Direct Connect, AWS Site-to-Site VPN, and VPC peering connections may require little manual effort (such as navigating multiple interfaces and configuring routers and gateways) for a small number of on-premises locations and Amazon VPCs.
However, for enterprises with IT environments spanning hundreds of VPCs and multiple on-premises offices, that manual effort, along with the associated resources and costs, can very quickly become difficult to manage.
Ultimately, using AWS Transit Gateway helps to lower operational efforts and costs while increasing business agility.
Building Global Enterprise Network Architectures
Customers can use AWS Transit Gateway to build out their IT networks without dealing with extensive network architecture planning and upgrades. They can take advantage of other networking and security services offered by AWS or AWS Partners to deploy a global enterprise-grade network, as opposed to manually integrating different solutions from multiple vendors.
Because AWS Transit Gateway is a managed service, enterprises can also avoid the hardware and software refresh and upgrade cycles typically associated with similar hardware or software-based solutions.
Key AWS Transit Gateway features that can be leveraged to build out a global network architecture while centralizing control, maximizing network and application performance, and ensuring overall network security include:
SD-WAN Integration
Customers typically use software-defined wide area networking (SD-WAN) solutions to maximize the use of network transport resources by automatically rerouting VPN tunnels over alternative network paths should application or network performance degrade on a designated primary path.
With select SD-WAN solutions, organizations also have the option to create AWS Site-to-Site VPN tunnels directly between a branch and AWS Transit Gateway with minimal manual effort using the SD-WAN solution’s management interface.
The integration of SD-WAN solutions from AWS Partners with AWS Transit Gateway Network Manager can enable customers to visualize, manage, and monitor IT environments spanning both on-premises and on AWS.
Figure 4 – SD-WAN integration with AWS Transit Gateway.
Branch-to-Cloud Connectivity with Aruba SD-Branch
Large organizations with multiple on-premises locations have been adopting SD-WAN solutions to simplify branch-to-branch connectivity.
As enterprises increase the adoption of infrastructure as a service (IaaS) for select workloads, the need arises to scale branch-to-cloud connectivity while retaining the benefits of scalability, orchestration, and cost optimization derived from the use of SD-WAN.
With the combination of AWS Transit Gateway and Aruba SD-Branch, large enterprises can simplify, automate, and scale the interconnection of on-premises data centers and ROBOs with multiple Amazon VPCs.
The main components of the solution are:
- Aruba Branch Gateways: Deployed in data centers and branch offices, the gateways help IT administrators create and support multiple connections (or IPSec VPN tunnels) between any two locations. These gateways establish the SD-WAN overlay used to create virtual connections between locations in the IT network.
. - Aruba Virtual Gateways: Deployed in Amazon VPCs, these virtual gateways enable secure connectivity between the branches and data center locations connecting to public clouds. Virtual gateways support public internet and private connections such as AWS Direct Connect.
. - Aruba SD-WAN Orchestrator: With the web-based orchestrator, organizations can dynamically create IPSec VPN tunnels between Aruba branch gateways to build the SD-WAN overlay. The Orchestrator automatically learns routes between the Aruba branch gateways and distributes all route information within the overlay.
.
Should traffic on one network path in the overlay be unable to support traffic, the Aruba SD-WAN Orchestrator will reroute traffic dynamically to minimize service disruption to end-users.
- Aruba Central: This is a cloud-native graphical user interface (GUI) that provides unified management, artificial intelligence support, and security for wired, wireless, and SD-WAN operations across campus, branch, and data center environments.
Aruba has also designed a number of operations to be automated either out-of-the-box capabilities or programmatically via Aruba applications programming interfaces (APIs).
IT staff that manage large and complex distributed enterprises spanning both on-premises and on AWS can benefit, as the automation can reduce the number of manual steps related to daily network operations. Examples include setting up routes and tunnels between multiple branches and Amazon VPCs, and applying network access control lists (ACLs) to multiple sites.
With Aruba SD-Branch, organizations can reduce the amount of time and resources spent on configuring and managing connections between branches, data centers, cloud service providers, and SaaS providers. For example, they can spend less time manually configuring individual network routers and installing at individual locations.
They can also maximize the use of existing network bandwidth from a wide range of communication services while decreasing their dependence on costly MPLS resources for establishing available, fault-tolerant connections.
Aruba SD Branch Benefits Using AWS Transit Gateway
Aruba SD-Branch customers using AWS Transit Gateway can reap additional benefits with the integration of the two solutions. The integration first simplifies how organizations connect on-premises locations to Amazon VPCs in two ways:
- Refer Aruba Virtual Gateway in AWS Marketplace: Deploy Aruba Virtual Gateways (VGWs) and extend the Aruba SD-WAN fabric into the AWS Cloud via a transit VPC. By importing an AWS account into Aruba Central, an IT administrator has full visibility into all Amazon VPCs within that account.
.
Aruba VGWs can be centrally configured and deployed (via Amazon EC2 instances) into any Aruba-based transit VPC. Each transit VPC becomes another “location” that can connect to other on-premises locations included in the SD-WAN overlay. Simultaneously, the transit VPCs connect to AWS Transit Gateway, which connects with the organization’s Amazon VPCs.
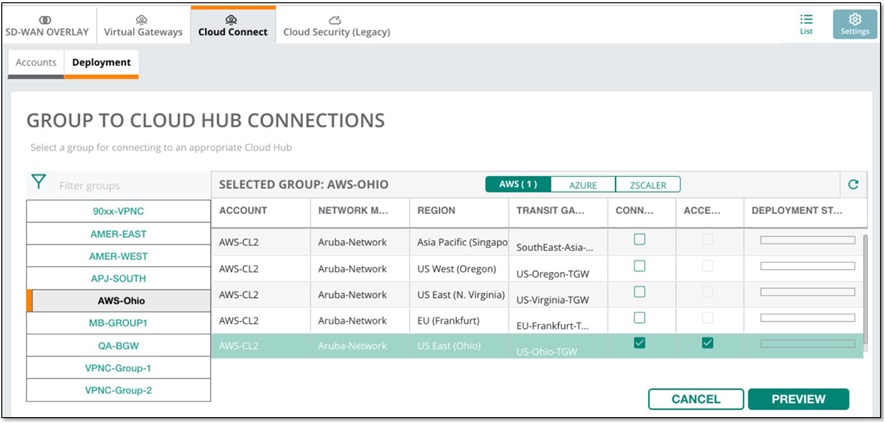
- Directly connect on-premises Aruba gateways to AWS Transit Gateway: Organizations can take advantage of the integration and automation between AWS Transit Gateway Network Manager and Aruba Central.
.
Instead of deploying Aruba VGWs in Amazon Transit VPCs and connecting those VGWs with select branches, an administrator can connect a group of Aruba branch gateways (that share a common configuration and policy within an AWS region) to an AWS Transit Gateway.
Figure 5 – Using Aruba SD-Branch to connect to multiple VPCs via AWS Transit Gateway.
Using the Cloud Connect application of Aruba Central, an IT administrator imports an AWS account. Aruba Central then detects AWS Transit Gateways (or hubs) accessible to the branch groups.
By clicking on the Connections checkbox, the branch groups are automatically connected to the selected hub. Once the connections are established, IP prefixes of allowable addresses are automatically exchanged between AWS Transit Gateway and the Aruba branch gateways in the branch group.
Connecting branch groups to AWS Transit Gateway is not limited to an AWS region. With AWS Transit Gateway inter-region peering, these branch groups can now potentially reach Amazon VPCs deployed in AWS Regions globally.
Figure 6 – Establishing VPN connections between branch groups and AWS Transit Gateway.
Traffic from any on-premises location can potentially reach any Amazon VPC connected to the selected AWS Transit Gateway. The number of P2P connections between the branch offices and AWS Transit Gateway decreases, as well as the amount of time spent on actually creating these branch-to-cloud connections.
Connections between the branch groups and AWS Transit Gateway can also be managed via policies created by the administrator.
If the Aruba Orchestrator detects that thresholds for network and application performance metrics cannot be met for a traffic flow, defined policies will signal the Aruba Orchestrator to dynamically reroute traffic over alternative network transport.
Less time is spent on monitoring performance and reconfiguring connections when performance-impacting issues arise, thus increasing service uptime.
With the integration of AWS Transit Gateway Network Manager and Aruba Central, organizations can gain end-to-end visibility of their networks spanning both on-premises and the AWS Cloud.
For example, the IT administrator can view the network’s geography, as well as a list of the number of AWS resources (hubs an Amazon VPCs), the number and types of connections between the branch groups and hubs, and the number of on-premises locations.
With Aruba Central, an administrator can also view the SD-WAN overlay connecting branch groups and AWS Transit Gateway, along with other relevant information such as originating and terminating IP addresses.
The integrated view helps to improve end-to-end visibility of the network while minimizing the number of management interfaces to be used. Time spent on management effort decreases, helping to lower operational costs over time.
For example, as discussed in a recent Enterprise Strategy Group whitepaper, Aruba customer Verisk Analytics was challenged to deploy and expand end users’ SD-WAN connectivity at a global scale. The customer deployed an Aruba VGW into Amazon VPC, an edge VPC that sits between branches and AWS Transit Gateway, enabling VPC peering and attachments into Central Hub.
Now, Verisk Analytics uses AWS Transit Gateway peering to interconnect Amazon VPCs in different global regions and to take advantage of the AWS global backbone to add a layer of network availability, in case of failure in their private network backbones.
Summary
Customers’ adoption of cloud infrastructure services continues to increase, yet most plan to maintain some level of on-premises environments.
Building and updating the network underlying hybrid clouds can be a complex and time-consuming exercise that decreases business agility. To remove this burden, organizations can benefit from a solution that enables a global network architecture connecting cloud and on-premises environments while decreasing overall network complexity.
AWS Transit Gateway simplifies hybrid cloud networks by centralizing Layer 3 connectivity of Amazon VPCs, on-premises data centers, and ROBOs.
When used together, AWS Transit Gateway with Aruba SD-Branch helps organizations simplify how they connect on-premises locations to Amazon VPCs without using numerous P2P connections. By utilizing branch groups, which contain Aruba branch gateways that share a common configuration and policy within an AWS region, organizations can directly connect these groups with AWS Transit Gateway.
The Aruba SD-WAN Orchestrator automates how branches and VPCs connect via the AWS Transit Gateway by orchestrating IP source and destination IP addresses exchanged between the branch groups and AWS Transit Gateway.
The integration of AWS Transit Gateway Network Manager and Aruba Central provides organizations with centralized configuration and end-to-end visibility of their networks spanning both on-premises and the AWS Cloud.