AWS Compute Blog
Introducing message data protection for Amazon SNS
Amazon Simple Notification Service (SNS) message data protection is now generally available and also supports real-time data de-identification via redaction and masking. For more information, see Message Data Protection in the Amazon SNS Developer Guide.
This post is written by Otavio Ferreira, Senior Software Development Manager, Marc Pinaud, Senior Product Manager, Usman Nisar, Senior Software Engineer, Hardik Vasa, Senior Solutions Architect, and Mithun Mallick, Senior Specialist Solution Architect.
Today, we are announcing the public preview release of new data protection capabilities for Amazon Simple Notification Service (SNS), message data protection. This is a new way to discover and protect sensitive data in motion at scale, without writing custom code.
SNS is a fully managed serverless messaging service. It provides topics for push-based, many-to-many pub/sub messaging for decoupling distributed systems, microservices, and event-driven serverless applications. As applications grow, so does the amount of data transmitted and the number of systems sending and receiving data. When moving data between different applications, guardrails can help you comply with data privacy regulations that require you to safeguard sensitive personally identifiable information (PII) or protected health information (PHI).
With message data protection for SNS, you can scan messages in real time for PII/PHI data and receive audit reports containing scan results. You can also prevent applications from receiving sensitive data by blocking inbound messages to an SNS topic or outbound messages to an SNS subscription. Message data protection for SNS supports a repository of over 25 unique PII/PHI data identifiers. These include people’s names, addresses, social security numbers, credit card numbers, and prescription drug codes.
These capabilities can help you adhere to a variety of compliance regulations, including HIPAA, FedRAMP, GDPR, and PCI. For more information, including the complete list of supported data identifiers, see message data protection in the SNS Developer Guide.
Overview
SNS topics enable you to integrate distributed applications more easily. As applications become more complex, it can become challenging for topic owners to manage the data flowing through their topics. Developers that publish messages to a topic may inadvertently send sensitive data, increasing regulatory risk. Message data protection enables SNS topic owners to protect sensitive application data with built-in, no-code, scalable capabilities.
To discover and protect data flowing through SNS topics with message data protection, topic owners associate data protection policies to their topics. Within these policies, you can write statements that define which types of sensitive data you want to discover and protect. As part of this, you can define whether you want to act on data flowing inbound to a topic or outbound to a subscription, which AWS accounts or specific AWS Identity and Access Management (AWS IAM) principals the policy is applicable to, and the actions you want to take on the data.
Message data protection provides two actions to help you protect your data. Auditing, to report on the amount of PII/PHI found, and blocking, to prevent the publishing or delivery of payloads that contain PII/PHI data. Once the data protection policy is set, message data protection uses pattern matching and machine learning models to scan your messages in real time for PII/PHI data identifiers and enforce the data protection policy.
For auditing, you can choose to send audit reports to Amazon Simple Storage Service (S3) for archival, Amazon Kinesis Data Firehose for analytics, or Amazon CloudWatch for logging and alarming. Message data protection does not interfere with the topic owner’s ability to use message data encryption at rest, nor with the subscriber’s ability to filter out unwanted messages using message filtering.
Applying message data protection in a use case
Consider an application that processes a variety of transactions for a set of health clinics, an organization that operates in a regulated environment. Compliance frameworks require that the organization take measures to protect both sensitive health records and financial information.
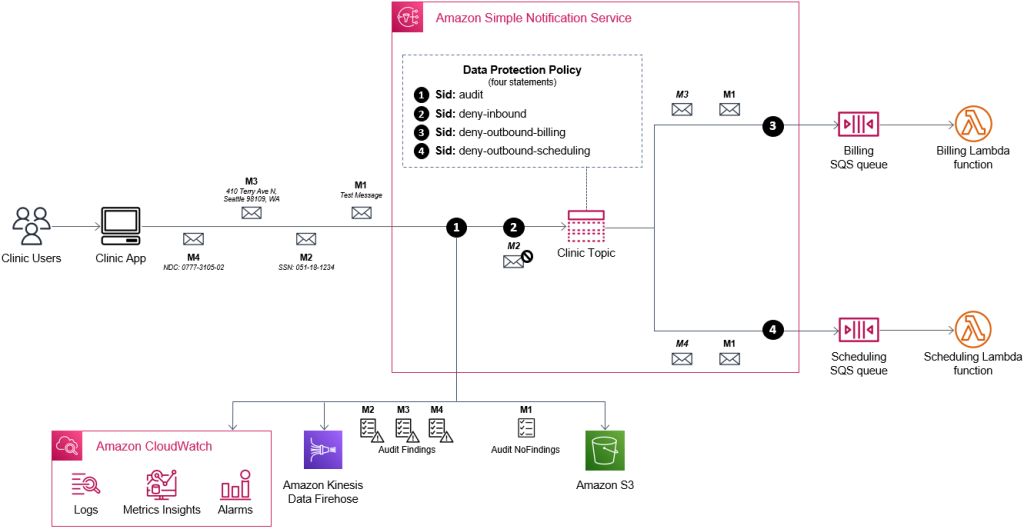
The application is based on an event-driven serverless architecture. It has a data protection policy attached to the topic to audit for sensitive data and prevent downstream systems from processing certain data types.
The application publishes an event to an SNS topic every time a patient schedules a visit or sees a doctor at a clinic. The SNS topic fans out the event to two subscribed systems, billing and scheduling. Each system stores events in an Amazon SQS queue, which is processed using an AWS Lambda function.
Setting a data protection policy to an SNS topic
You can apply a data protection policy to an SNS topic using the AWS Management Console, the AWS CLI, or the AWS SDKs. You can also use AWS CloudFormation to automate the provisioning of the data protection policy.
This example uses CloudFormation to provision the infrastructure. You have two options for deploying the resources:
- Deploy the resources by using the message data protection deploy script within the aws-sns-samples repository in GitHub.
- Alternatively, use the following four CloudFormation templates in order. Allow time for each stack to complete before deploying the next stack.
- When deploying the Scheduling and Billing subscriber templates, you must configure CloudFormation to deploy the resources using the respective IAM roles that were created in the first step. To do this, select the respective IAM role for the template you are running when prompted to Configure stack options in the CloudFormation console, as shown below.
1. Prerequisites template (please note the two IAM roles that are created, as you must use them in steps 3 & 4)
- Two IAM roles with a managed policy that allows access to receive messages from the SNS topic, one for the billing and another for scheduling system, respectively.
2. Topic owner template
- SNS topic that delivers events to two distinct systems.
- A data protection policy that defines both auditing and blocking actions for specific types of PII and PHI.
- S3 bucket to archive audit findings.
- CloudWatch log group to monitor audit findings.
- Kinesis Data Firehose to deliver audit findings to other destinations.
3. Scheduling subscriber template (when deploying this template, you must use the IAM role that we created for the scheduling system)
- SQS queue for the Scheduling system.
- Lambda function for the Scheduling system.
4. Billing subscriber template (when deploying this template, you must use the IAM role that we created for the billing system)
- SQS queue for the Billing system.
- Lambda function for the Billing system.
CloudFormation creates the following data protection policy as part of the topic owner template:
ClinicSNSTopic:
Type: 'AWS::SNS::Topic'
Properties:
TopicName: SampleClinic
DataProtectionPolicy:
Name: data-protection-example-policy
Description: Policy Description
Version: 2021-06-01
Statement:
- Sid: audit
DataDirection: Inbound
Principal:
- '*'
DataIdentifier:
- 'arn:aws:dataprotection::aws:data-identifier/Address'
- 'arn:aws:dataprotection::aws:data-identifier/AwsSecretKey'
- 'arn:aws:dataprotection::aws:data-identifier/DriversLicense-US'
- 'arn:aws:dataprotection::aws:data-identifier/EmailAddress'
- 'arn:aws:dataprotection::aws:data-identifier/IpAddress'
- 'arn:aws:dataprotection::aws:data-identifier/NationalDrugCode-US'
- 'arn:aws:dataprotection::aws:data-identifier/PassportNumber-US'
- 'arn:aws:dataprotection::aws:data-identifier/Ssn-US'
Operation:
Audit:
SampleRate: 99
FindingsDestination:
CloudWatchLogs:
LogGroup: !Ref AuditCWLLogs
Firehose:
DeliveryStream: !Ref AuditFirehose
NoFindingsDestination:
S3:
Bucket: !Ref AuditS3Bucket
- Sid: deny-inbound
DataDirection: Inbound
Principal:
- '*'
DataIdentifier:
- 'arn:aws:dataprotection::aws:data-identifier/PassportNumber-US'
- 'arn:aws:dataprotection::aws:data-identifier/Ssn-US'
Operation:
Deny: {}
- Sid: deny-outbound-billing
DataDirection: Outbound
Principal:
- !ImportValue "BillingRoleExportDataProtectionDemo"
DataIdentifier:
- 'arn:aws:dataprotection::aws:data-identifier/NationalDrugCode-US'
Operation:
Deny: {}
- Sid: deny-outbound-scheduling
DataDirection: Outbound
Principal:
- !ImportValue "SchedulingRoleExportDataProtectionDemo"
DataIdentifier:
- 'arn:aws:dataprotection::aws:data-identifier/Address'
- 'arn:aws:dataprotection::aws:data-identifier/CreditCardNumber'
Operation:
Deny: {}This data protection policy defines:
- Metadata about the data protection policy, for example name, description, version, and statement IDs (sid).
- The first statement (sid: audit) scans inbound messages from all principals for addresses, social security numbers, driver’s license, email addresses, IP addresses, national drug codes, passport numbers, and AWS secret keys.
- The sampling rate is set to 99% so almost all messages are scanned for the defined PII/PHI.
- Audit results with findings are delivered to CloudWatch Logs and Kinesis Data Firehose for analytics. Audit results without findings are archived to S3.
- The second statement (sid: deny-inbound) blocks inbound messages to the topic coming from any principal, if the payload includes either a social security number or passport number.
- The third statement (sid: deny-outbound-billing) blocks the delivery of messages to subscriptions created by the BillingRole, if the messages include any national drug codes.
- The fourth statement (sid: deny-outbound-scheduling) blocks the delivery of messages to subscriptions created by the SchedulingRole, if the messages include any credit card numbers or addresses.
Testing the capabilities
Test the message data protection capabilities using the following steps:
- Publish a message without PII/PHI data to the Clinic Topic. In the CloudWatch console, navigate to the log streams of the respective Lambda functions to confirm that the message is delivered to both subscribers. Both messages are delivered because the payload contains no sensitive data for the data protection policy to deny. The log message looks as follows:
"This is a demo! received from queue arn:aws:sqs:us-east-1:111222333444:Scheduling-SchedulingQueue" - Publish a message with a social security number (try ‘SSN: 123-12-1234’) to the Clinic Topic. The request is denied, and an audit log is delivered to your CloudWatch Logs log group and Firehose delivery stream.
- Navigate to the CloudWatch log console and confirm that the audit log is visible in the
/aws/vendedlogs/clinicauditCloudWatch log group. The following example shows that the data protection policy (sid: deny-inbound) denied the inbound message as the payload contains a US social security number (SSN) between the 5th and the 15th character.{ "messageId": "77ec5f0c-5129-5429-b01d-0457b965c0ac", "auditTimestamp": "2022-07-28T01:27:40Z", "callerPrincipal": "arn:aws:iam::111222333444:role/Admin", "resourceArn": "arn:aws:sns:us-east-1:111222333444:SampleClinic", "dataIdentifiers": [ { "name": "Ssn-US", "count": 1, "detections": [ { "start": 5, "end": 15 } ] } ] } - You can use the CloudWatch metrics, MessageWithFindings and MessageWithNoFindings, to track how frequently PII/PHI data is published to an SNS topic. Here’s an example of what the CloudWatch metric graph looks like as the amount of sensitive data published to a topic varies over time:

- Publish a message with an address (try ‘410 Terry Ave N, Seattle 98109, WA’). The request is only delivered to the Billing subscription. The data protection policy (sid: deny-outbound-scheduling) denies the outbound message to the Scheduling subscription as the payload contains an address.
- Confirm that the message is only delivered to the Billing Lambda function by navigating to the CloudWatch console and inspecting the logs of the two respective Lambda functions. The CloudWatch log of the Billing Lambda function contains the sensitive message that was delivered to it as it was an authorized subscriber. Here’s an example of what the log contains:
410 Terry Ave N, Seattle 98109, WA received from queue arn:aws:sqs:us-east-1:111222333444:Billing-BillingQueue - Publish a message with a drug code (try ‘NDC: 0777-3105-02’). The request is only delivered to the Scheduling subscription. The data protection policy (sid: deny-outbound-billing) denies the outbound message to the Billing subscription as the payload contains a drug code.
- Confirm that the message is only delivered to the Scheduling Lambda function by navigating to the CloudWatch console and inspecting the logs of the two respective Lambda functions. The CloudWatch log of the Scheduling Lambda function contains the sensitive message that was delivered to it as it was an authorized subscriber. Here’s an example of what the log contains:
NDC: 0777-3105-02 received from queue arn:aws:sqs:us-east-1:111222333444:Scheduling-SchedulingQueue
Cleaning up
After testing, avoid incurring usage charges by deleting the resources that you created. Navigate to the CloudFormation console and delete the four CloudFormation stacks that you created during the walkthrough. Remember, you must delete all the objects from the S3 bucket before deleting the stack.
Conclusion
This post shows how message data protection enables a topic owner to discover and protect sensitive data that is exchanged through SNS topics. The example shows how to create a data protection policy that generates audit reports for sensitive data and blocks messages from delivery to specific subscribers if the payload contains sensitive data.
Get started with SNS and message data protection by using the AWS Management Console, AWS Command Line Interface (CLI), AWS SDKs, or CloudFormation.
For more details, see message data protection in the SNS Developer Guide. For information on pricing, see SNS pricing.
For more serverless learning resources, visit Serverless Land.