AWS Public Sector Blog
Navigating ISM and Essential Eight compliance with AWS Config for Australian government agencies
To help our Australian customers, Amazon Web Services (AWS) provides pre-built conformance packs for the Australian Cyber Security Centre (ACSC) Essential Eight Maturity Model and the ACSC Information Security Manual (ISM). The ACSC’s Essential Eight was first published in 2017 and is a set of prioritised security mitigation strategies designed to help protect organisations against various security threats. These eight strategies are considered a good baseline of a minimum set of preventative measures that organisations should implement. They are by no means the only security measures organisations should be implementing.
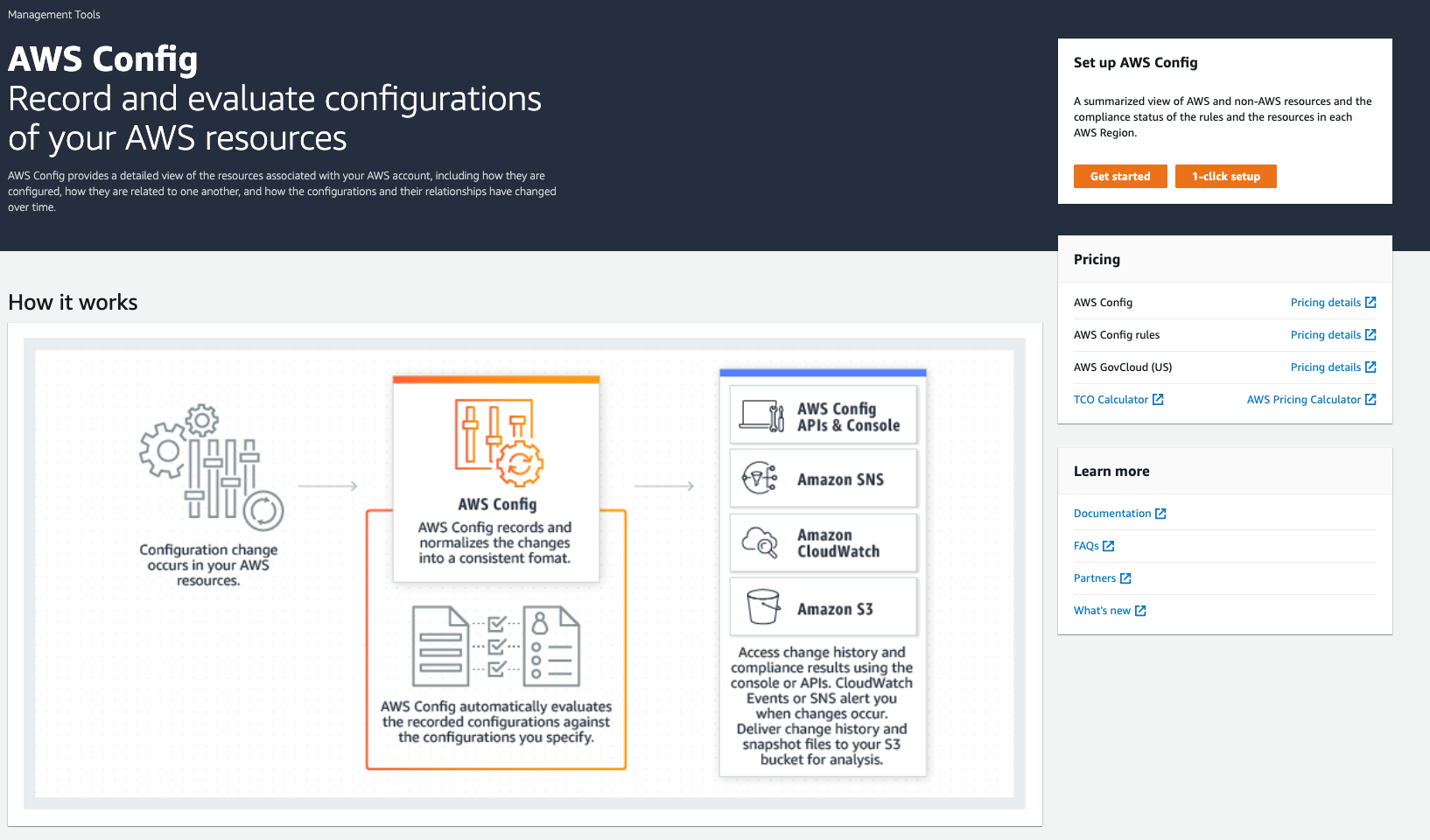
At AWS, security is our top priority. AWS provides an extremely wide and deep set of security services, as well as detailed information on configuration and architecture. One AWS service, AWS Config, allows you to assess, audit, and evaluate the configurations of your AWS resources. AWS Config continuously monitors and records your AWS resource configurations and allows you to automate the evaluation of recorded configurations against your desired configurations to help customers with their compliance strategies. One feature of AWS Config is the support for conformance packs, which are collections of AWS Config rules and remediation actions that can be readily deployed together in an account and a Region or across an organization in AWS Organizations.
In this blog post, I walk you through how to set up a conformance pack in AWS Config that is designed to help you implement and track the ASCS Essential Eight model. The AWS Config service lets you see the rules that are applied, and you can see clear reports on any resources that fail to comply with the required configurations. Once you install the conformance pack, AWS Config lets you see how the configuration of your current resources compares with the rules in the conformance pack.
Setting up ACSC Essential Eight conformance packs in AWS Config
Prerequisites
For this walkthrough, you should have the following prerequisites:
- An AWS account
- Familiarity with the AWS Management Console
I also recommend reading the AWS Config Essential Eight conformance pack and associated mappings documentation, and documentation on the Operational Best Practices for ACSC ISM.
Walkthrough
In the AWS Console, navigate to the AWS Config home page.
Figure 1. AWS Config initial page.
1. Select the Get Started button in the Set up AWS Config box. This takes you to the AWS Config general settings page (Figure 2).
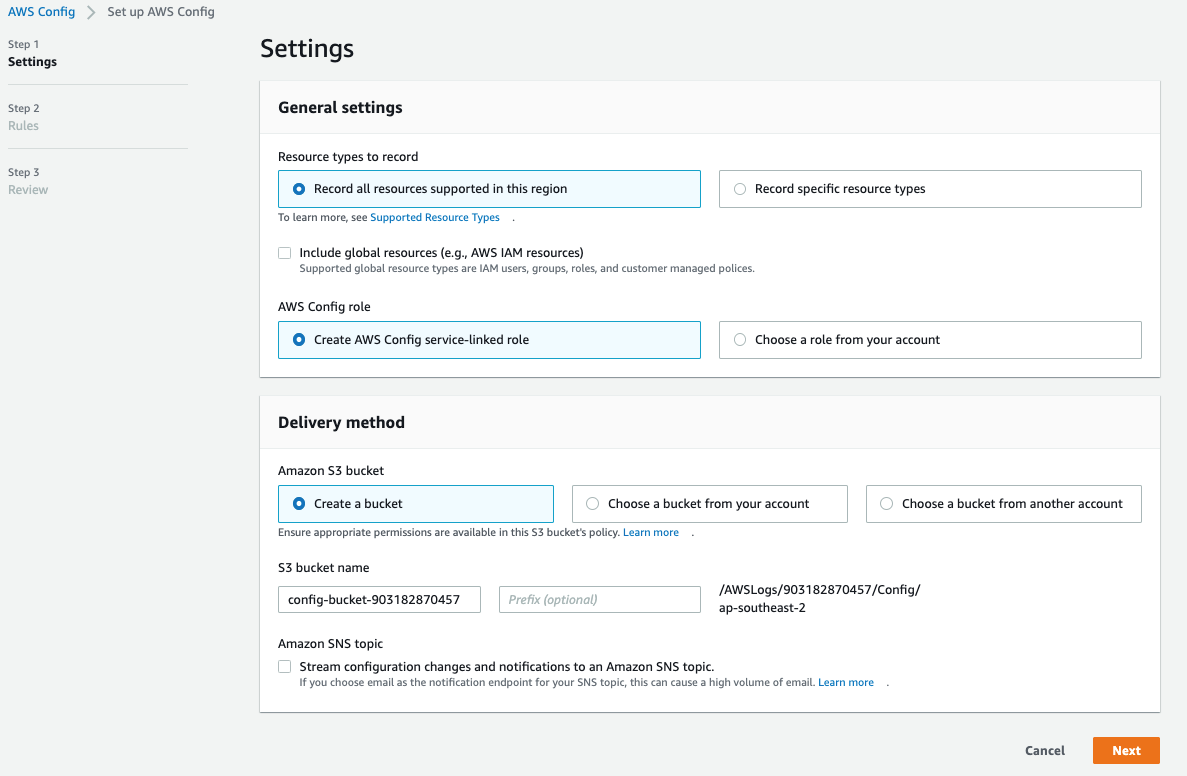
There are three main steps required to configure the AWS Config service: Settings, Rules, and Review.
Figure 2. The AWS Config general settings screen.
2. In the Settings page, you can choose to track all supported resources in your current Region, or specify a set of detailed resource types to track, by selecting the appropriate options in the “Resource types to record” section. In this case, we opt to record all resources supported in this Region.
3. Under “Delivery method,” you can choose to create a new Amazon Simple Storage Service (Amazon S3) bucket into which your results are delivered, or choose a pre-existing bucket in your account or another AWS account. Optionally, you can stream the changes to an Amazon Simple Notification Service (Amazon SNS) notification topic for further alerting or actions.
4. Choose Next to move on to the next section.
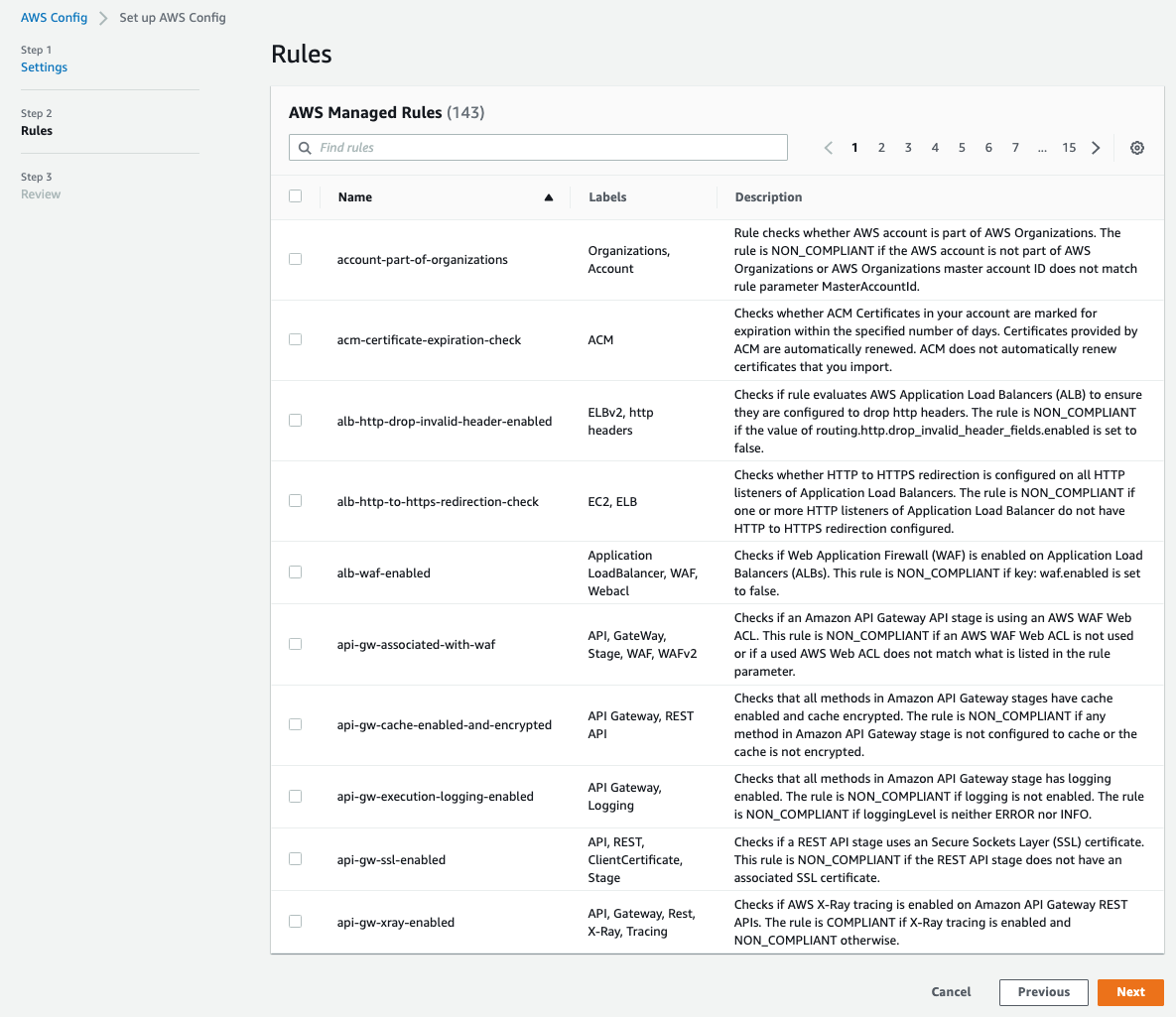
Figure 3. AWS Managed rules section.
5. In the Rules page (Figure 3), do not select any of the AWS Managed Rules. Select Next.
Figure 4. AWS Config review section.
6. On the Review page (Figure 4), look over your selections. Then select Confirm.
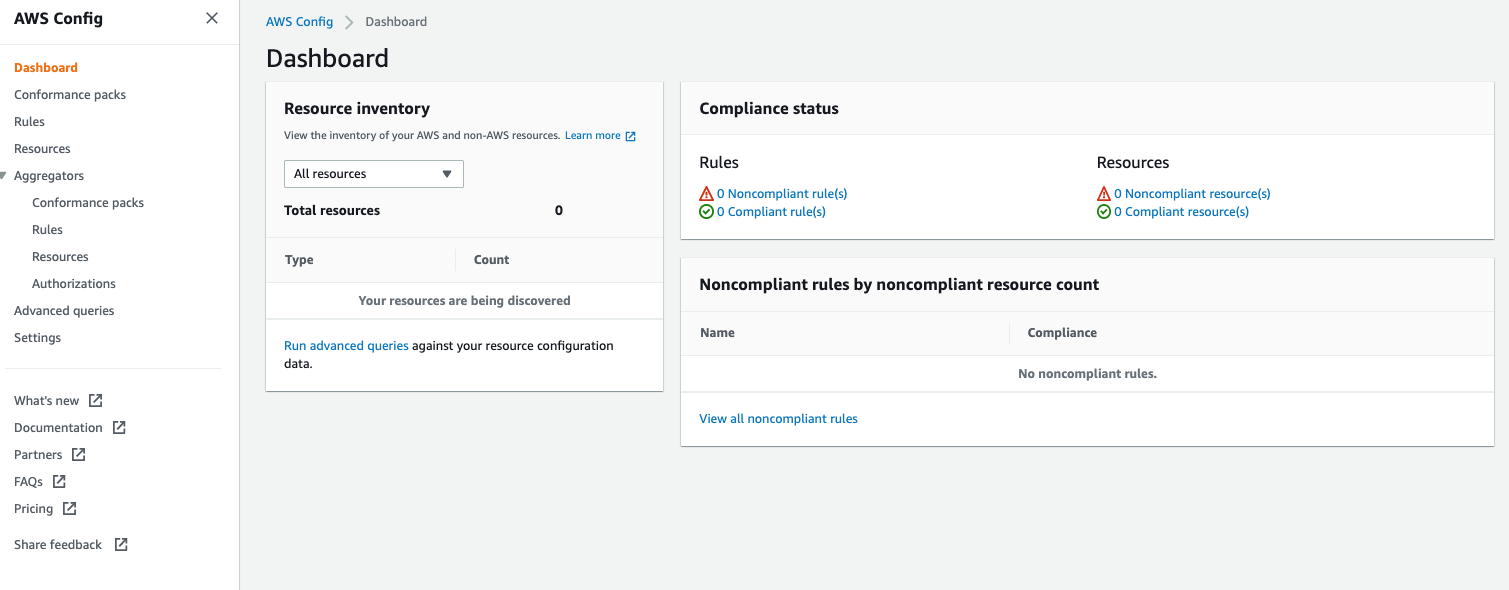
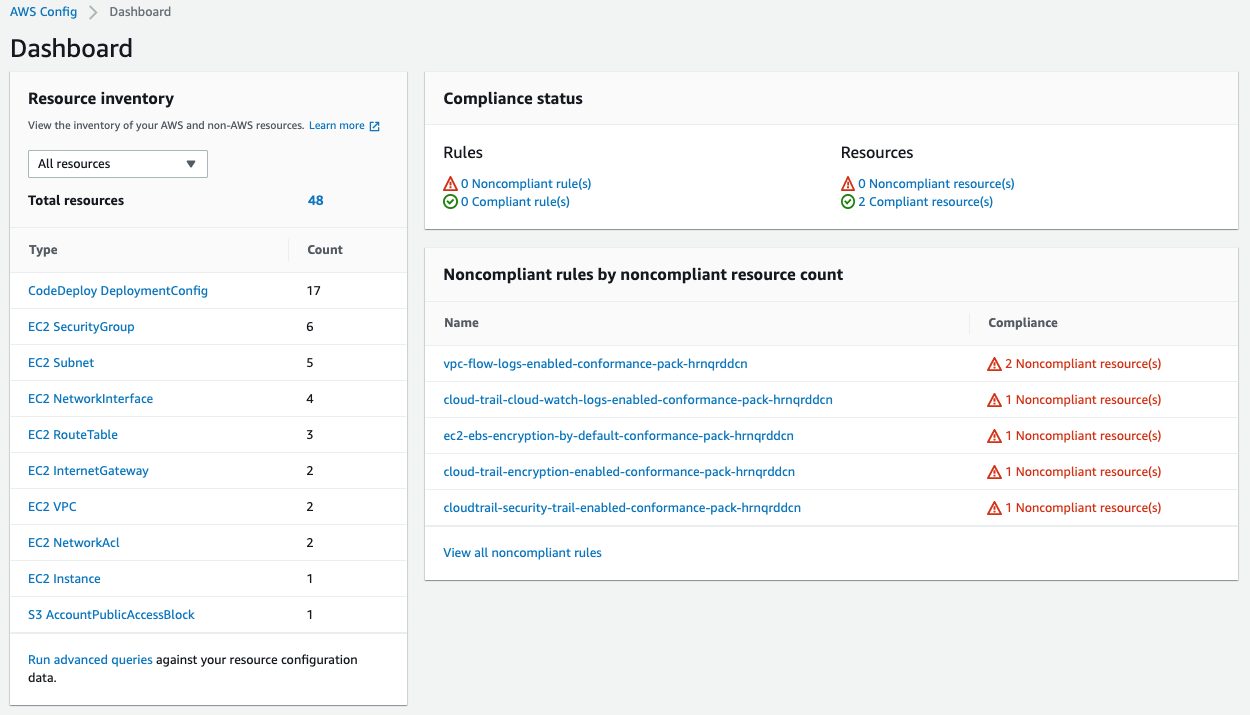
After 1-2 minutes, the AWS Config dashboard should appear (Figure 5) and show you the current compliance status. There is a section labelled Rules that lists out all the compliant and noncompliant rules currently applied, as well as a section labelled Resources that lists which resources are compliant and which are noncompliant.
Figure 5. The AWS Config main dashboard.
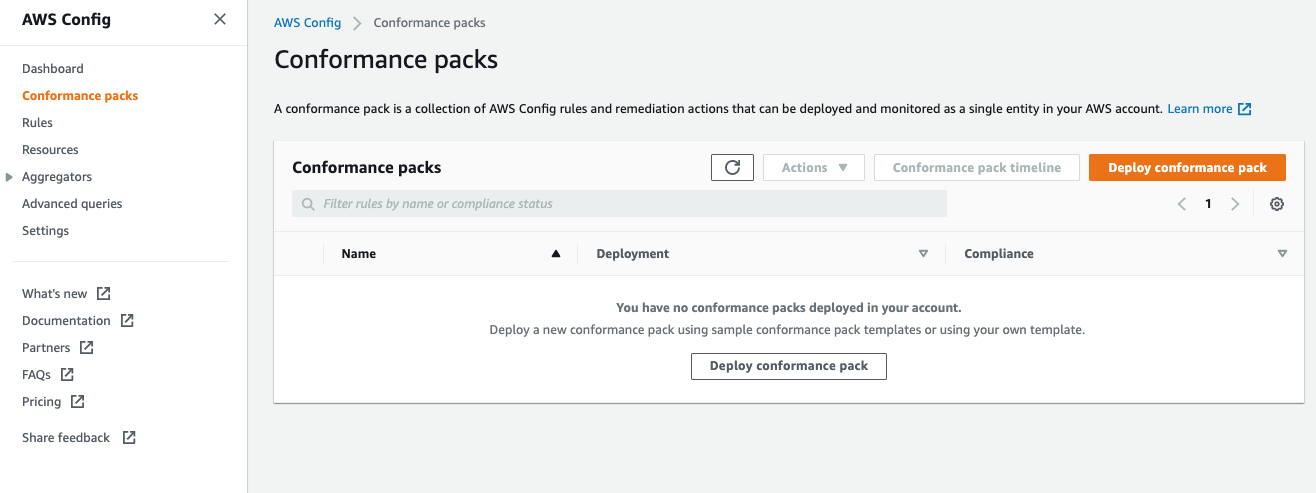
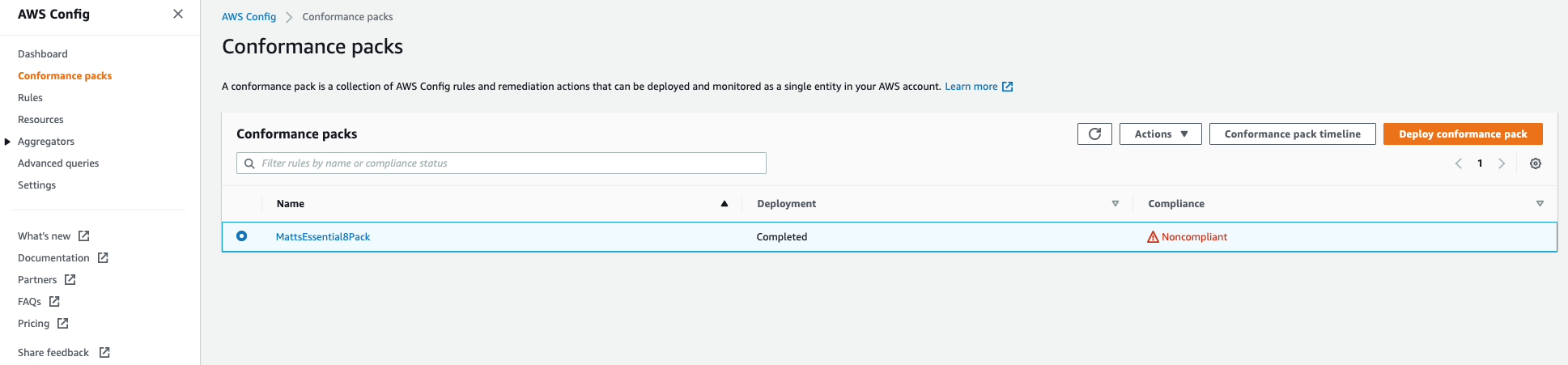
7. In the navigation bar on the left side of the screen, select Conformance packs to open the “Conformance packs” screen (Figure 6).
Figure 6. The conformance packs summary screen.
8. Select Deploy conformance pack.
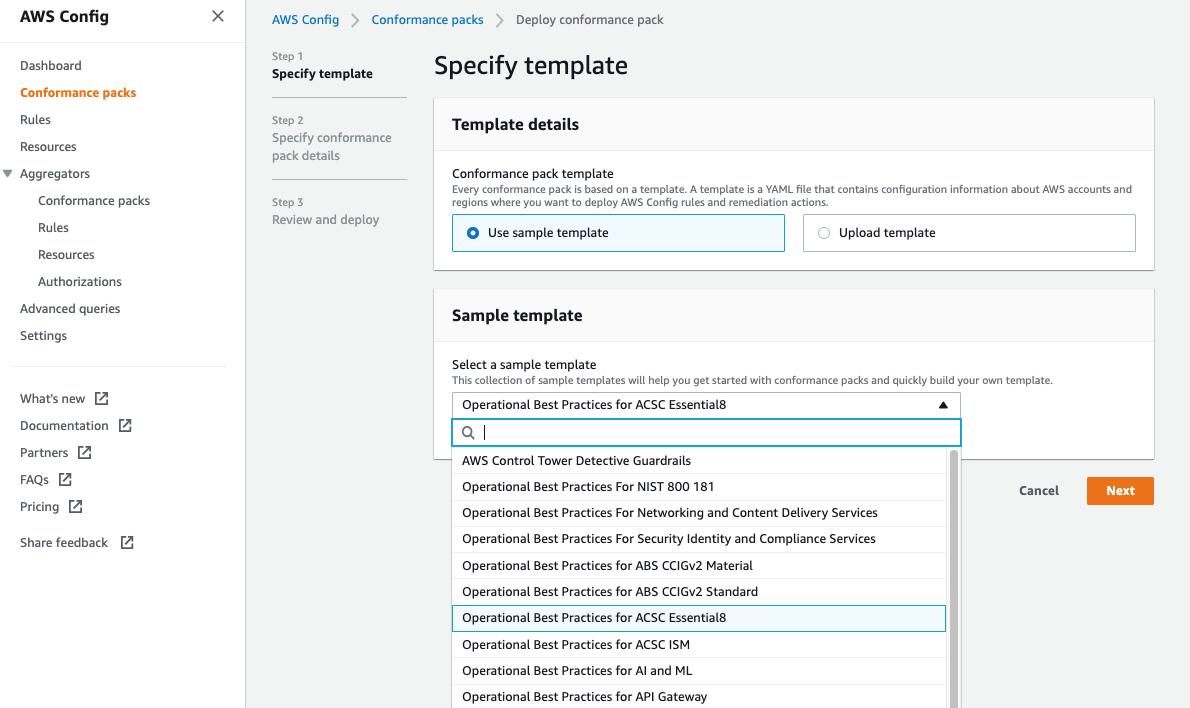
9. In the Specify template window that opens for Step 1: Specify template, keep Use sample plate selected under Template details. Within the Select a sample template dropdown, select Operational Best Practices for ACSC Essential8 and then choose Next.
Figure 7. Select template dropdown list.
10. In the Step 2: Specify conformance pack details page, enter a name of your choice for your conformance pack. Select Next.
Figure 8. The specify conformance pack name page.
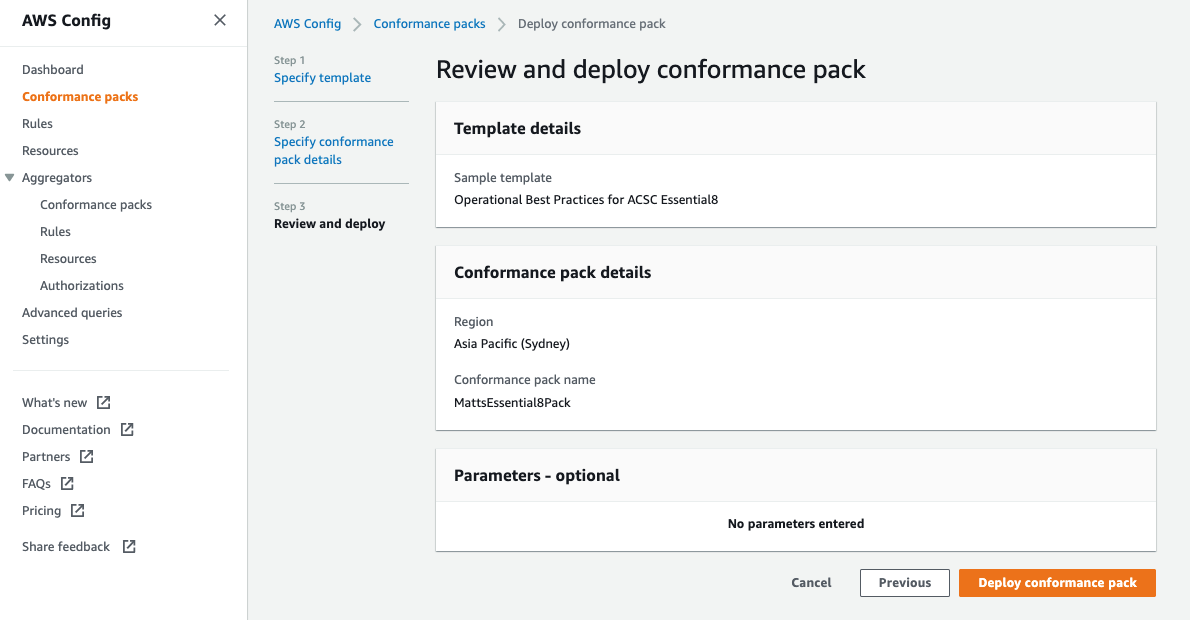
11. In the Step 3: Review and deploy page (Figure 9), review all your settings, and then select Deploy conformance pack. After approximately five minutes, the conformance pack should finish deploying (Figure 10).
Figure 9. Review conformance pack details screen.
Figure 10. Conformance pack deployment in progress.
Managing compliant and noncompliant resources in AWS Config
Once the conformance pack finishes deploying, when you go back to the AWS Config dashboard, you should find a list of resources and a central widget labelled Compliance status showing a high-level view of the Rules and Resources (Figure 11). Note that it can take 20-30 mins for results to start feeding findings into this high-level summary dashboard.
Figure 11. Conformance pack compliance summary status.
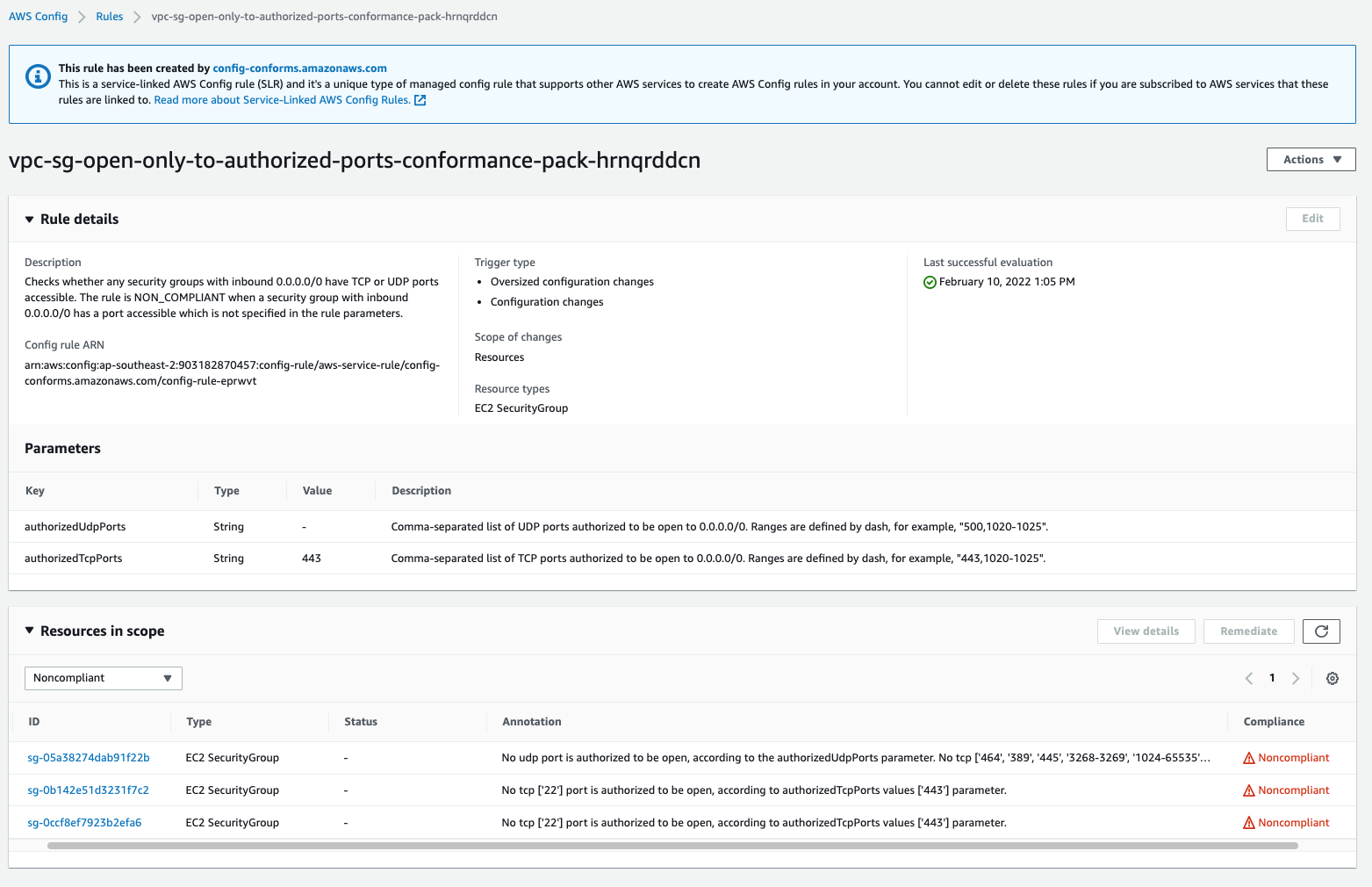
To get more information about a rule, in the AWS Config dashboard, select one of the noncompliant rules under the Noncompliant rules by noncompliant resource count section to view more details, such as the noncompliant security group details shown in Figure 11.
Figure 12. Conformance pack rule detailed view.
There are two main sections in the details screen that opens (Figure 12). The first section has details on the rule in question, as well as any relevant parameters. Following this, there is a list of resources in scope, so you can determine which resources are noncompliant. This helps customers with troubleshooting and remediation actions to help bring the resources back into compliance.
Create your own conformance packs in AWS Config
The AWS Config service comes with many built-in conformance packs, but for customers that want even more flexibility, there is a mechanism to develop and load your own conformance packs. Customers can choose to use the AWS standard conformance packs as a starting point. For example, the Essential Eight conformance pack can be found in this GitHub repository. Customers can dive deeper into the details of the specific rules contained in this conformance pack, or use this pack as a starting point for their own customised conformance pack.
Within AWS Config, you can upload your own custom conformance pack by either using the downloaded yaml file from the AWS Config conformance packs GitHub repository, or create your own from scratch. To upload a custom conformance pack, select Deploy conformance pack on the Conformance packs main dashboard. In the Specify template window that opens for Step 1: Specify template (as seen in Figure 7), there is an option to directly upload your custom template file at the top of the console wizard by selecting Upload template.
In this way, AWS Config can help you set up systems to measure continuous compliance with your internal security frameworks, and support you in preventing or immediately remediating issues. There are many sample templates to be found in the Conformance Pack Sample Templates. In-depth documentation on the conformance packs, along with instructions on how to create and upload them, can be found in our detailed AWS Config Developer Guide.
Clean up
Figure 13. Conformance packs list.
For customers that no longer wish to utilise the conformance packs, select the pack you wish to remove, and select the Actions dropdown, and then select Delete. Confirm the deletion by choosing the orange Delete button.
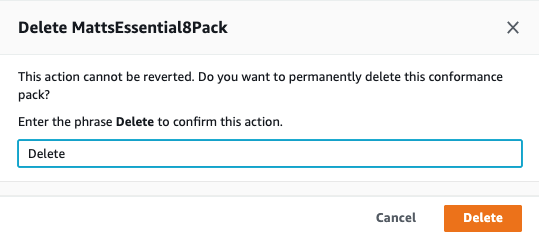 Figure 14. Deleting a conformance pack.
Figure 14. Deleting a conformance pack.
After several minutes, the conformance pack should be removed from AWS Config.
Conclusion
In this blog post, I introduced the AWS Config conformance packs and presented a step-by-step process for how to apply the conformance packs, and provided an example of what results may look like from the conformance packs after they have scanned an environment. Additionally, I touched on the ability for customers to create custom conformance packs. Finally, we stepped though how to remove any applied conformance packs.
Next steps
AWS Config can support customers in the systems they use to manage their security and compliance posture. Once you are familiar with the AWS Config product, you can start applying conformance packs in your development accounts initially, and then move the configurations through into your production environments. Learn more about AWS Config here.
Do you have a question about how AWS Config and other AWS services can support you in your compliance needs? Reach out to the AWS Public Sector team for more information, or contact your AWS account manager.
Read more about AWS for governments:
- How NRCan used an AWS open source solution to complete a PBMM evidence package in 60 days
- Running government workloads securely at the edge
- How public sector agencies can identify improper payments with machine learning
- Architecture framework for transforming federal customer experience and service delivery
- 5 best practices to create a cloud cost allocation strategy for government customers
Subscribe to the AWS Public Sector Blog newsletter to get the latest in AWS tools, solutions, and innovations from the public sector delivered to your inbox, or contact us.
Please take a few minutes to share insights regarding your experience with the AWS Public Sector Blog in this survey, and we’ll use feedback from the survey to create more content aligned with the preferences of our readers.