AWS Architecture Blog
Find Public IPs of Resources – Use AWS Config for Vulnerability Assessment
Systems vulnerability management is a key component of your enterprise security program. Its goal is to remediate OS, software, and applications vulnerabilities. Scanning tools can help identify and classify these vulnerabilities to keep the environment secure and compliant. Typically, vulnerability scanning tools operate from internal or external networks to discover and report vulnerabilities. For internal […]
Insights for CTOs: Part 2 – Enable Good Decisions at Scale with Robust Security
In my role as a Senior Solutions Architect, I have spoken to chief technology officers (CTOs) and executive leadership of large enterprises like big banks, software as a service (SaaS) businesses, mid-sized enterprises, and startups. In this 6-part series, I share insights gained from various CTOs and engineering leaders during their cloud adoption journeys at […]
Modernized Database Queuing using Amazon SQS and AWS Services
This blog post was last reviewed/updated August, 2022. The updated version shown below is based on working backwards from a customer need to ensure data consistency post migration, to a modernized microservice architecture. A queuing system is composed of producers and consumers. A producer enqueues messages (writes messages to a database) and a consumer dequeues […]
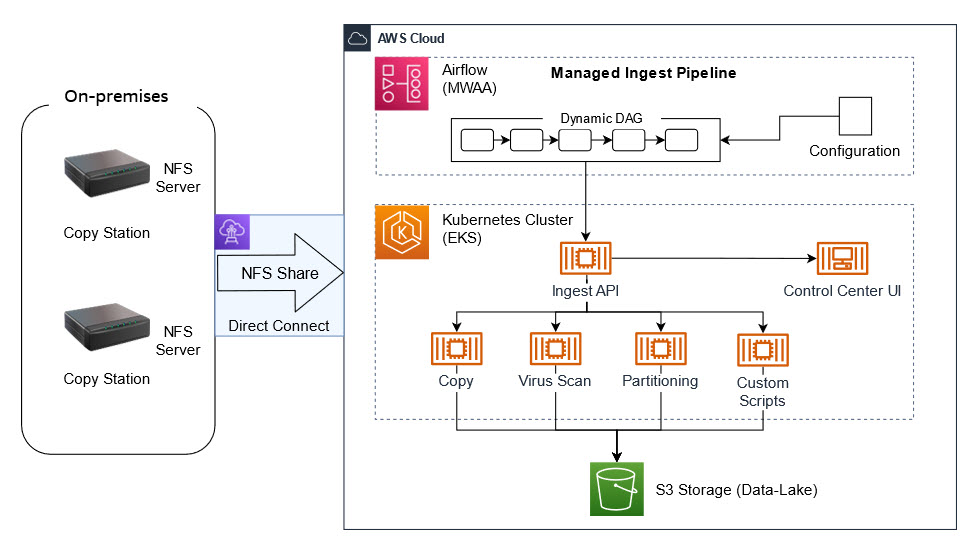
Ingesting Automotive Sensor Data using DXC RoboticDrive Ingestor on AWS
This post was co-written by Pawel Kowalski, a Technical Product Manager for DXC RoboticDrive and Dr. Max Böhm, a software and systems architect and DXC Distinguished Engineer. To build the first fully autonomous vehicle, L5 standard per SAE, auto-manufacturers collected sensor data from test vehicle fleets across the globe in their testing facilities and driving […]
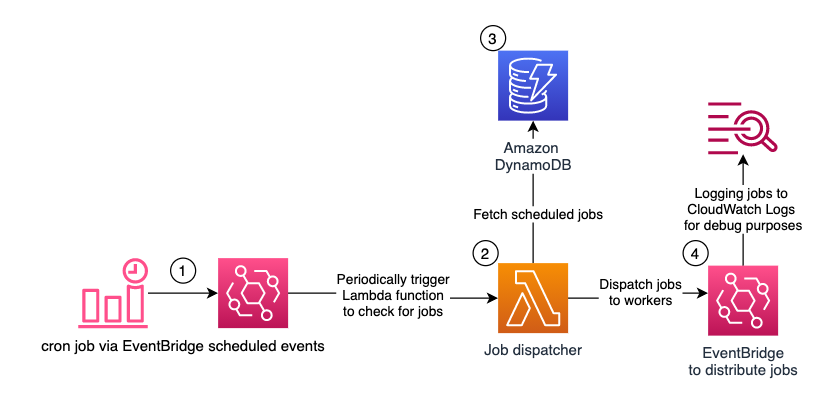
Serverless Scheduling with Amazon EventBridge, AWS Lambda, and Amazon DynamoDB
Many applications perform scheduled tasks. For instance, you might want to automatically publish an article at a given time, change prices for offers which were defined weeks in advance, or notify customers 8 hours before a flight. These might be one-off tasks, or recurring ones. On Unix-like operating systems, you might have opted for the […]
Modernize your Penetration Testing Architecture on AWS Fargate
Organizations in all industries are innovating their application stack through modernization. Developers have found that modular architecture patterns, serverless operational models, and agile development processes provide great benefits. They offer faster innovation, reduced risk, and reduction in total cost of ownership. Security organizations must evolve and innovate as well. But security practitioners often find themselves […]
Architecture Monthly Magazine: Agriculture
Amazon Web Services (AWS) helps agriculture customers forecast supply and demand and create and maintain responsive, resilient food systems. This edition of Architecture Monthly focuses on the agriculture industry and their role in providing products to the world that are nutritious, healthy, accessible, affordable, and sustainable. We’d like to thank our expert, Karen Hildebrand, Worldwide […]
Use Amazon EKS and Argo Rollouts for Progressive Delivery
A common hurdle to DevOps strategies is the manual testing, sign-off, and deployment steps required to deliver new or enhanced feature sets. If an application is updated frequently, these actions can be time-consuming and error prone. You can address these challenges by incorporating progressive delivery concepts along with the Amazon Elastic Kubernetes Service (Amazon EKS) […]
Migrating a Database Workflow to Modernized AWS Workflow Services
The relational database is a critical resource in application architecture. Enterprise organizations often use relational database management systems (RDBMS) to provide embedded workflow state management. But this can present problems, such as inefficient use of data storage and compute resources, performance issues, and decreased agility. Add to this the responsibility of managing workflow states through […]
Applying Federated Learning for ML at the Edge
Federated Learning (FL) is an emerging approach to machine learning (ML) where model training data is not stored in a central location. During ML training, we typically need to access the entire training dataset on a single machine. For purposes of performance scaling, we divide the training data between multiple CPUs, multiple GPUs, or a […]