AWS Partner Network (APN) Blog
How to Use Aviatrix Orchestration of AWS Transit Gateway for Network Operations and Compliance
By Nick Matthews and Matt Lehwess, Principal Solution Architects at AWS
By Shanti Johnson, DevOps Manager at Motili
By Karthik Balachandran, Sr. Solution Architect at Aviatrix
 |
 |
 |
Amazon Web Services (AWS) now offers more flexible routing as part of AWS Transit Gateway, and Aviatrix offers orchestration of the Transit Gateway service. Aviatrix Systems is an AWS Partner Network (APN) Advanced Technology Partner with the AWS Networking Competency.
AWS Transit Gateway can be used to connect Virtual Private Clouds (VPCs) in a hub-and-spoke architecture, simplifying the connectivity between VPCs and on-premises networks.
Also, the new route domain construct within Transit Gateway gives organizations the flexibility to create “zero trust” transit networks by grouping connected VPCs of similar sensitivity. Zero trust in this context means that the VPC network connectivity can be dictated via VPC segmentation according to design rather than by default.
With the Aviatrix Secure Networking Platform AMI or Aviatrix software-as-a-service (SaaS) listings, both available on AWS Marketplace, you can orchestrate the Transit Gateway in minutes without delving into the configuration detail required in each VPC and route table.
In this post, we will explore how our joint customer Motili designed a zero trust network that leverages AWS Transit Gateway and Aviatrix software-defined cloud routing technology to build a simplified, policy-driven network to securely connect VPC and on-premises environments. We’ll dive deep on the basics of Transit Gateway, VPC isolation, and how Aviatrix Transit Gateway orchestration is a natural go-with solution.
What is AWS Transit Gateway?
AWS Transit Gateway is a new AWS service that significantly raises the scale and performance compared to Transit VPCs built from legacy products. The native Transit Gateway service can connect thousands of VPCs together, and can transfer data between VPCs at over 50 Gbps.
Every VPC in an AWS Region can be natively attached to Transit Gateway using elastic network interfaces, instead of using VPN or overlay networks. The Transit Gateway offers flexible segmentation with route domains and route propagations. It also provides an efficient way to facilitate connectivity between Amazon VPCs and on-premises resources.
Unlike the Transit VPC architecture, Transit Gateway uses static route management for the spoke VPC route tables. BGP-based route propagation is implemented only between the Transit Gateway and on-premises VPN attachments.
Zero Trust Cloud Networking Using Route Domains
AWS Transit Gateway comes with a default route table that allows attached VPCs and on-premises networks to reach other attached networks in an “any-to-any” way. The basic benefit of a transit network is that it reduces connections compared to the number of peerings for a full mesh of VPCs.

Figure 1 – Flat, full connectivity. No segmentation.
Instead of the default route domain approach described above, additional route tables can be created within a Transit Gateway to group attached VPCs, which provide segmented domains.
An example of multi-domain VPC layout would be a Transit Gateway with three route domains:
- A default “non-production” route domain with development and test VPCs attached.
- “Production” route domain with business-critical VPCs attached.
- “Shared-services” route domain with DevOps tools in a shared-services VPC used to centrally manage the instances in all the other VPCs.
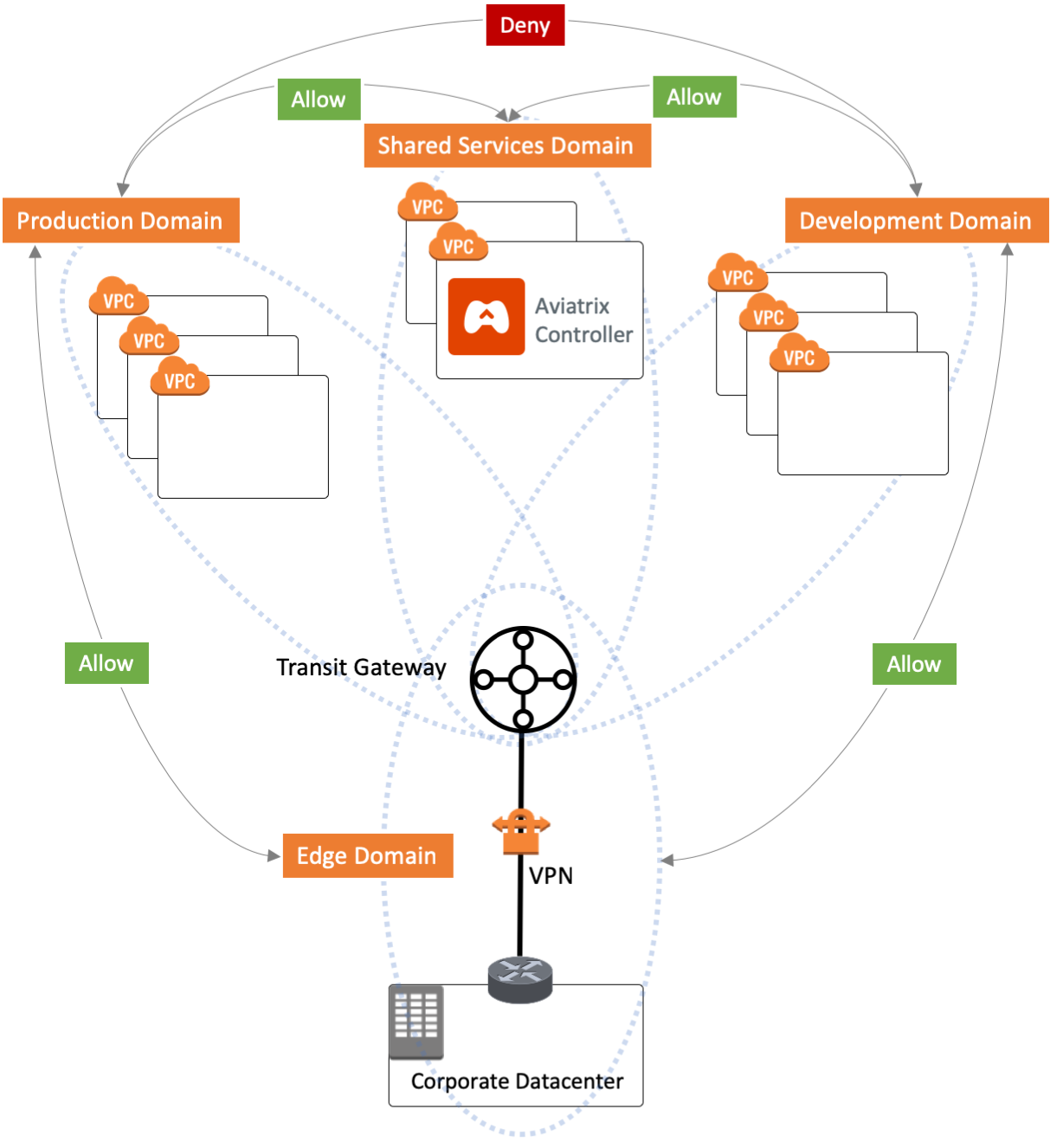
Figure 2 – The Aviatrix AVX Controller natively integrates with spoke VPCs and AWS Transit Gateway to enable three route domains.
Aviatrix Transit Gateway Orchestrator implements security domains by orchestrating route tables and route propagation across the spokes and Transit Gateway route tables. It also orchestrates the propagation of on-premises routes to the VPC spokes in a software-defined fashion.
These security domains are isolated from each other, creating a zero trust VPC segmentation model by preventing lateral movement in the case of unauthorized access. No development VPCs can reach production VPCs, and vice versa. The three route domains can be segmented into smaller domains of VPCs to further isolate the blast radius. For example, you could create five domains: development, test, production, shared service, and an egress domain.
How Does a Shared-Services Route Domain Work?
While non-production and production domains in this example are fairly straightforward, you would typically want the instances in a shared-services VPC to reach all other VPC instances while adhering to the policy that non-production VPCs cannot reach production VPCs. This is handled by updating the route domain tables and enabling route table propagation. The production and non-production route domain tables need to be updated with the shared-services VPC address range.
To complete the return path, the shared-services route domain table needs to be updated with all of the address ranges of other VPCs. These updates can be configured manually with the AWS Management Console and AWS Command Line Interface (CLI), or automatically handled with Aviatrix orchestration through the AVX Controller. Note that as more VPCs are added or changed, other existing route tables need to be updated, creating an increasing number of routes that require configuration.
Better Together: Aviatrix Orchestration & AWS Transit Gateway
Extending a well-known DevOps analogy, if Amazon Elastic Compute Cloud (Amazon EC2) instances are cattle and VPCs are the cattle fences, then Transit Gateway route domains are the outer ranch borders separating properties. In this analogy, Aviatrix Orchestrator for Transit Gateway ensures borders are drawn correctly and lets them be redrawn as new pastures are added. The Orchestrator provides continuous watch over the prairieland!
Developed by Aviatrix in partnership with AWS, the Aviatrix Secure Networking Platform AMI and Aviatrix SaaS offerings on AWS Marketplace orchestrate the provisioning and configuration of the Transit Gateway. Together, they provide everything you need to go from a simple set of connected VPCs to a secure, zero trust network of VPCs—a policy-based network where VPCs can be added or changed every week without interrupting service, and with monitoring, troubleshooting, and visualization tools to ensure compliant connectivity.
Best of all, you don’t have to be a networking expert to do all of this. Aviatrix helps you herd your VPCs, and it’s all done via the Aviatrix AVX Controller that lets you plan, build, and visualize your VPCs and route domains.
With the point-and-click GUI, or via APIs (AWS CloudFormation, Terraform), the AVX Controller provides pre-built shared-services, non-production, and production route domains while monitoring your whole transit network. As the Aviatrix Orchestrator is a real-time, hybrid system, it does more than the Infrastructure-as-Code scripts can do. For example, since Transit Gateway does not use BGP to automatically update the spoke VPC route tables, Aviatrix handles the dynamic route propagation as network changes take place in your on-premises environments.
Burden of Proof: Compliant Connectivity
In working with early beta, customers of both the AWS Transit Gateway and Aviatrix orchestration provided consistent feedback about needing auditable policies with simple administration. With the power of automation and AWS, most cloud teams are finding themselves in a predicament—more time is spent on proving infrastructure adheres to their security team’s compliance requirements than on building the infrastructure itself.
In other words, being able to show auditors that you are compliant is just as important as actually being compliant. Aviatrix orchestration includes the ability to visualize the connectivity across multiple accounts and VPCs, showing the network reachability of all instances.
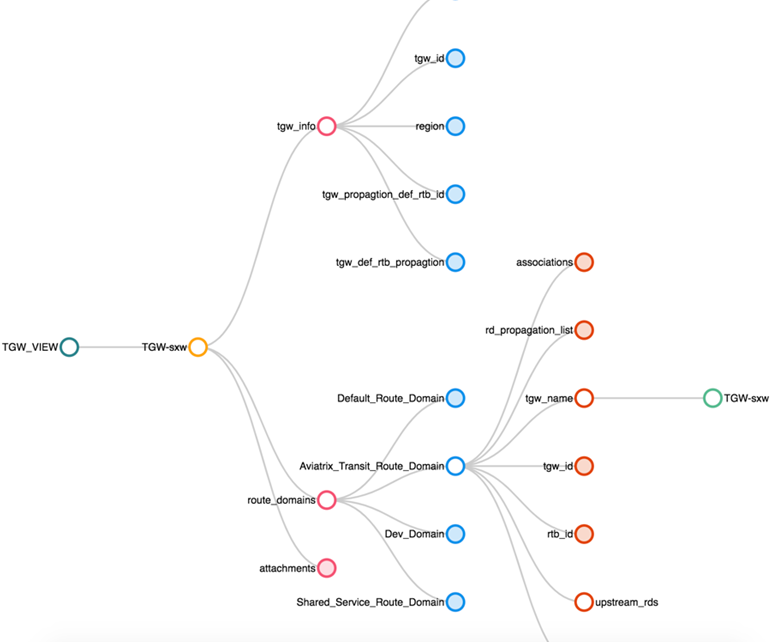
Figure 3 – Aviatrix AVX Controller visualization of the Transit Gateway connections.
Motili: Migrating to Transit Gateway & Aviatrix
Motili, Inc. offers a technology platform to help single-family, multi-family, and commercial property owners and operators easily manage HVAC and hot water assets through planned and unplanned repair and replacement projects. Motili had a growing number of VPCs and needed connectivity to their HQ office.
Shanti Johnson, a Motili development operations manager, worked with AWS and Aviatrix to establish their requirements for a new zero trust cloud network. Since they provide commercial solutions, capabilities such as policy-based segmentation and compliance reporting were key requirements. AWS and Aviatrix worked together to define a handful of route domains, including an on-premises domain to handle the propagation of on-premises routes to their HQ office.
“We implemented Aviatrix Orchestrator to automate the routing, security, and operations of our AWS Transit Gateway,” says Shanti Johnson, DevOps Manager at Motili. “The integrated architecture helps us simplify our hybrid network environment and provides the right infrastructure to grow our cloud footprint.”
Additionally, while the Transit Gateway easily handles in-the-cloud VPC-to-VPC connectivity, the edge connectivity to on-premises and other cloud provider networks had a few limitations. This is where the Aviatrix Next-Gen Transit VPC became a key piece to connect the edge networks.
In addition to zero trust, a critical requirement for Motili was simplified operations. The Aviatrix orchestration of Transit Gateway provides the unified management (Controller) to simplify operations of both AWS native and instance-based networking.
If you are using AWS Direct Connect between your on-premises environment and VPCs, Transit Gateway does not support AWS Direct Connect or Direct Connect Gateway at this time. Aviatrix supports existing hybrid environments by orchestrating and provisioning your AWS Direct Connect link to the Transit Gateway.
Figure 4 shows the architecture diagram of the network built using the combined solution.

Figure 4 – Aviatrix AVX Controller seamlessly orchestrates all spokes and Direct Connect to on-premises networks.
Summary
AWS Transit Gateway and Aviatrix go better together. It’s now simple to create zero trust networks using route domains for shared services and other VPCs. Whether you have a transit VPC already or were waiting to implement one, AWS Transit Gateway offers scale and performance. Aviatrix Orchestrator further simplifies networking with a single pane of glass for your entire cloud network.
Establishing connections among VPCs no longer requires expert-level networking skills. Rather, you can take advantage of the Aviatrix AMI or SaaS offerings on AWS Marketplace.
.
 |
Aviatrix Systems – APN Partner Spotlight
Aviatrix Systems is an AWS Networking Competency Partner. Their software solution enables enterprises to realize the benefits of agility, scale, and mobility when deploying applications in the public or hybrid cloud.
Contact Aviatrix Systems | Solution Overview | Buy on Marketplace
*Already worked with Aviatrix Systems? Rate this Partner
*To review an APN Partner, you must be an AWS customer that has worked with them directly on a project.