AWS Partner Network (APN) Blog
Security and Compliance at Scale with CloudHealth Secure State
By Elvis Pappachen, Sr. Partner Solutions Architect – AWS
By Hadar Freehling, Cloud Security Architect – CloudHealth
 |
| CloudHealth |
 |
Amazon Web Services (AWS) global infrastructure allows you to quickly innovate, experiment, and iterate your workloads. Security is the highest priority for AWS, which works closely with industry-leading partners such as CloudHealth by VMware to build security solutions for customers like CloudHealth Secure State (CHSS).
Customers often ask how they can secure their AWS workloads, remediate misconfigurations, ensure continuous compliance, search and investigate alerts and events, and have the necessary steps in place to ensure they can respond to security events.
Customers run various types of workloads on AWS, from Amazon Elastic Compute Cloud (Amazon EC2) to container services like Amazon Elastic Container Server (Amazon ECS) or Amazon Elastic Kubernetes Service (Amazon EKS).
Security protection of the data within AWS is a concern for all customers; not knowing where to go to check and remediate configurations is part of this concern.
Businesses want a single pane of glass to see the alerts, events, and misconfigurations, and then perform remediations to the misconfigurations.
In this post, we’ll look at how you can set up CHSS projects, suppress rules and alerts, find misconfigurations through CHSS Explore, and set up remediation jobs all built on CloudHealth’s unified security monitoring approach for AWS.
CloudHealth Secure State
CloudHealth by VMware is an AWS Partner with the AWS Security Competency that delivers various services, including CloudHealth Secure State (CHSS), that offers security to protect, remediation capabilities, and can scale across AWS.
CHSS is a security service platform that enables AWS customers to mitigate security and compliance risk through intelligent, real-time security insight.
CHSS has more than 900 security rules and 18+ compliance frameworks built on AWS that can help mitigate compliance risks, including CIS, GDPR, HIPAA, ISO 27001, MITRE ATT&CK Cloud, NIST, PCI, and SOC 2. The tool finds misconfigurations and consolidates alerts and findings across your AWS accounts.
The platform allows you to integrate with AWS services like Amazon Simple Queue Service (SQS) and Amazon Simple Storage Service (Amazon S3), as well as to third-party AWS Partners like Slack and Splunk.
For technical details, see the CHSS User Guide and architectural overview of how the CHSS services is used with your AWS account.
How it Works
CloudHealth Secure State is attached to the AWS account leveraging two methods.
First, a read-only role is set up. Next, an event stream is set up that sends the alerts and events from Amazon CloudWatch and AWS CloudTrail using Amazon Simple Notification Service (SNS) to stream the events into the CHSS platform.
That data is in the CHSS platform for customers to then act on.
Figure 1 – CHSS architectural overview.
As you start using CHSS, we recommend focusing on these features that can help you protect your AWS Cloud account:
- CHSS compliance frameworks
- Segment AWS accounts with CHSS
- How to find misconfigurations through CHSS Explore
- How to fix the misconfigurations
CHSS Compliance Frameworks
One of the first things customers should decide are what rules and frameworks they want to enable and report on.
CHSS allows customers to disable rules and suppress rules at an org, project, or individual object level. This ensures you aren’t flooded with information you don’t care about.
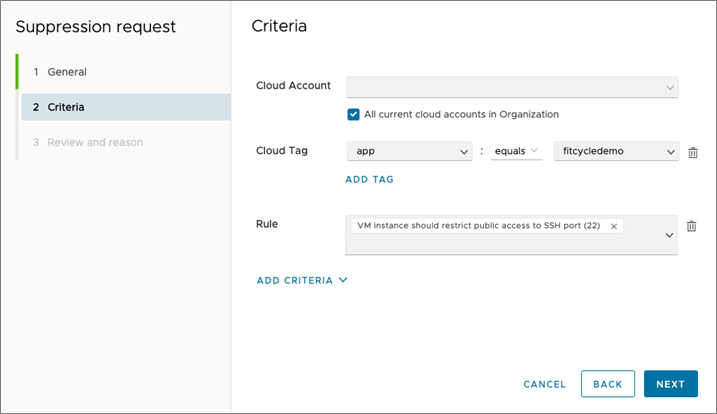
CHSS suppression criteria allows you to customize how new suppressions may be handled. In Figure 2, any object with a cloud tag of app = fitcycledemo will be automatically suppressed when a finding appears around public SSH port (not recommended) as an example.
Figure 2 – CHSS criteria.
When it comes to compliance, most customers start with a predefined standard framework—usually the Center for Internet Security (CIS) or similar.
What if you don’t need all of the controls or want to add more? With CHSS, you can clone an existing framework or create a new one from scratch. Figure 3 shows a customer framework that combines Payment Card Industry (PCI) and CIS controls.
Figure 3 – Create a new framework.
Segment AWS Accounts with CHSS Projects
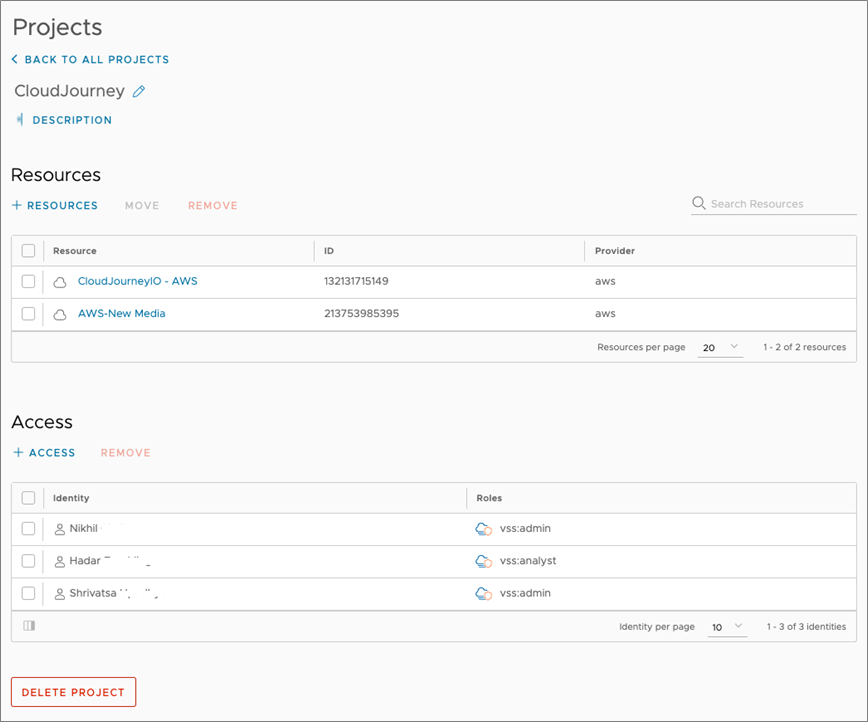
Another feature that can help organizations operationalize a tool like CHSS is Projects. This allows you to segment cloud accounts and assign users access to just those accounts. This is key in reducing the number of alerts and findings a user would see by assigning users specific access to their AWS account data.
Figure 4 shows an example of a CHSS Project that was set up to restrict specific users to specific resources that were also defined.
Figure 4 – CHSS Projects.
Users can switch between projects by selecting the project under the Project Selector tab. For teams that are responsible for the overall cloud security, organizational-level access is provided. At this level, you are able to see and monitor all accounts.
Find Misconfigurations Through CHSS Explore
One of the powerful features of CHSS is Explore, which allows customers to query the underlying database that CHSS runs upon.
Within Explore, you can launch free form searches, connected searches, and even aggregation searches. These searches can then be saved or converted into rules.
For example, when looking for any object that has “PCI” mentioned in its metadata, one would just type PCI in the search bar and click on the search button. To aggregate those results by region, all you need to add is count(region) to the end of the query, as shown below.
Figure 5 – Explore example.
What if you want to find something that may be a bit more complex? For example, if you want to know where you have a policy statement with resource = * applied to any Amazon EKS node running a pod on namespace sock-shop. Below is an example of the query:
Kubernetes.Workload.Deployment -> Kubernetes.Cluster.Namespace HAS EntityName = sock-shop -> AWS.EKS.Cluster -> Kubernetes.Cluster.Node -> AWS.EC2.Instance -> AWS.IAM.InstanceProfile -> AWS.IAM.Role -> AWS.IAM.ManagedPolicy -> AWS.IAM.PolicyStatement HAS Resource = “*”
Here are the results of running the example query above:
Figure 6 – Results of query in Explore.
The query starts with the workload deployment entity, filtered for the sock-shop Namespace, and then mapped that to the EKS cluster, Cluster Node, Instance, and all the way back to the Policy Statement that contained Resource = *.
Set Up Remediation Jobs to Fix Misconfigurations
Gaining security visibility where there was none before will inundate security and cloud teams. CHSS provides a secure and expandable remediation framework for customers to manage the process of fixing misconfigurations.
The customer deploys a CHSS docker “worker” image into their AWS account, such as Amazon ECS, and provide the “worker” permissions to make changes. The “worker” has write permissions to make changes to your AWS account not CHSS. Look at the remediation worker documentation for the architecture and deployment information.
There are 60 prebuilt jobs the worker can run out of the box. They can range from closing an open security group to encrypting an Amazon S3 bucket. The rules are open sourced which allows customers to create their own or customize it for their needs.
The remediation feature can be initiated automatically (guardrail/auto remediation) or at an individual object level. Customers enable auto remediation for low impacting fixes, like encrypting S3 buckets, and manually enable remediation for fixes that may have a negative impact, like closing security group ports
Conclusion
In this post, we went through how to leverage security and compliance frameworks that are part of CloudHealth Secure State (CHSS) and how to set up projects, rules, alerts, and remediation jobs to fix misconfigurations.
You were able to see the powerful capabilities of CHSS Explore, and how CloudHealth Secure State can help to solve the business concerns around security and remediations to compliance risks that is a part of your AWS accounts.
We encourage to acquire an account and license for CloudHealth Secure State from AWS Marketplace, or you can request a free demo.
CloudHealth – AWS Partner Spotlight
CloudHealth by VMware is an AWS Partner and trusted software platform for accelerating global business transformation in the cloud.
Contact CloudHealth | Partner Overview | AWS Marketplace
*Already worked with CloudHealth? Rate the Partner
*To review an AWS Partner, you must be a customer that has worked with them directly on a project.