AWS Architecture Blog
Category: Security, Identity, & Compliance
Throttling a tiered, multi-tenant REST API at scale using API Gateway: Part 1
Many software-as-a-service (SaaS) providers adopt throttling as a common technique to protect a distributed system from spikes of inbound traffic that might compromise reliability, reduce throughput, or increase operational cost. Multi-tenant SaaS systems have an additional concern of fairness; excessive traffic from one tenant needs to be selectively throttled without impacting the experience of other […]
Journey to Adopt Cloud-Native Architecture Series #5 – Enhancing Threat Detection, Data Protection, and Incident Response
In Part 4 of this series, Governing Security at Scale and IAM Baselining, we discussed building a multi-account strategy and improving access management and least privilege to prevent unwanted access and to enforce security controls. As a refresher from previous posts in this series, our example e-commerce company’s “Shoppers” application runs in the cloud. The company […]
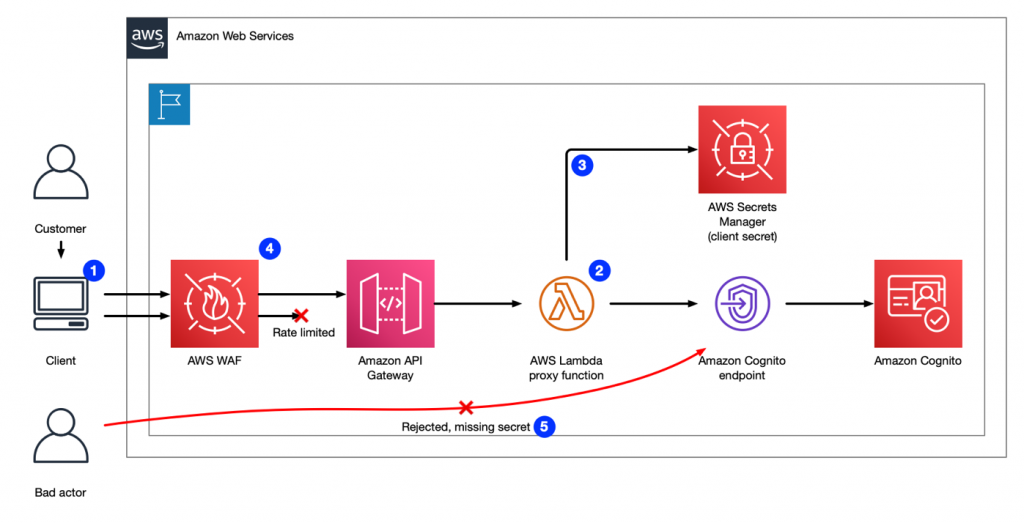
Enriching Amazon Cognito features with an Amazon API Gateway proxy
This post was co-written with Geoff Baskwill, member of the Architecture Enabling Team at Trend Micro. At Trend Micro, we use AWS technologies to build secure solutions to help our customers improve their security posture. Sep 6 2022: Amazon Cognito user pools now support native integration with AWS Web Application Firewall (WAF), with this native […]
Dream11: Blocking application attacks using AWS WAF at scale
As the world’s largest fantasy sports platforms with more than 120 million registered users, Dream11 runs multiple contests simultaneously while processing millions of user requests per minute. Their user-centric and data-driven teams make it a priority to ensure that the Dream11 application (app) remains protected against all kinds of threats and vulnerabilities. Introduction to AWS […]
Reduce Cost and Increase Security with Amazon VPC Endpoints
This blog explains the benefits of using Amazon VPC endpoints and highlights a self-paced workshop that will help you learn more about them. Amazon Virtual Private Cloud (Amazon VPC) enables you to launch Amazon Web Services (AWS) resources into a virtual network that you’ve defined. This virtual network resembles a traditional network that you’d operate […]
Deploy consistent DNS with AWS Service Catalog and AWS Control Tower customizations
Many organizations need to connect their on-premises data centers, remote sites, and cloud resources. A hybrid connectivity approach connects these different environments. Customers with a hybrid connectivity network need additional infrastructure and configuration for private DNS resolution to work consistently across the network. It is a challenge to build this type of DNS infrastructure for […]
QsrSoft launches Digital Huddle Board in 3 months with AWS serverless and Fire devices
QsrSoft is a software as a service (SaaS) company that develops solutions for clients in the restaurant, hospitality, and retail industries to help them achieve operational excellence. QsrSoft has provided these services for more than two decades and now services over 14,000 locations. QsrSoft started using AWS in 2015 and fully migrated all their workloads […]
Using DevOps Automation to Deploy Lambda APIs across Accounts and Environments
by Subrahmanyam Madduru – Global Partner Solutions Architect Leader, AWS, Sandipan Chakraborti – Senior AWS Architect, Wipro Limited, Abhishek Gautam – AWS Developer and Solutions Architect, Wipro Limited, Arati Deshmukh – AWS Architect, Infosys As more and more enterprises adopt serverless technologies to deliver their business capabilities in a more agile manner, it is imperative […]
Let’s Architect! Architecting for Security
At AWS, security is “job zero” for every employee—it’s even more important than any number one priority. In this Let’s Architect! post, we’ve collected security content to help you protect data, manage access, protect networks and applications, detect and monitor threats, and ensure privacy and compliance. Managing temporary elevated access to your AWS environment One […]
Multi-Region Migration using AWS Application Migration Service
AWS customers are in various stages of their cloud journey. Frequently, enterprises begin that journey by rehosting (lift-and-shift migrating) their on-premises workloads into AWS, and running Amazon Elastic Compute Cloud (Amazon EC2) instances. You can rehost using AWS Application Migration Service (MGN), a cloud-native migration tool. You may need to relocate instances and workloads to […]