AWS Partner Network (APN) Blog
Driving Business Transformation and Cloud Security with Secure Cloud Foundation by Infosys Compaz
By Senthill Kumar K, VP, Secure Cloud Foundation Chief Architect – Infosys Compaz
By Christina Lam, VP, Digital Transformation – Infosys Compaz
By Vikrama Adethyaa, Sr. Partner Solutions Architect – AWS
 |
 |
 |
Secure Cloud Foundation is a fully managed platform-as-a-service (PaaS) offering from Infosys Compaz (iCompaz), an Infosys Limited joint venture.
Secure Cloud Foundation offers a managed platform with foundational secure landing zone capabilities, as well as application and workload hosting capabilities. It helps customers achieve enterprise-grade security for their workloads running on Amazon Web Services (AWS).
The platform also ensures regulated workloads meet and stay compliant with industry-specific compliance standards. It’s designed from the ground up for the cloud to address the dynamic and scalable characteristics of AWS.
Key differentiators of Secure Cloud Foundation are:
- Secure and compliant by design.
- End-to-end automation leverages cloud-native services to make it highly scalable and cost efficient. Secure Cloud Foundation addresses perimeter, endpoint, network, application, and data security, and can be leveraged by customers irrespective of their scale.
Infosys is an AWS Premier Consulting Partner with AWS Competencies in Data & Analytics, DevOps, Digital Customer Experience, and more. Infosys is also a member of the AWS Managed Service Provider (MSP) and AWS Well-Architected Partner Programs.
In this post, we will walk you through typical customer cloud adoption scenarios that could leverage the Secure Cloud Foundation. We’ll also explore common challenges for different cloud adoption scenarios and how the platform addresses those challenges through a holistic and unique approach to cloud adoption.
Typical Cloud Adoption Scenarios
While requirements can differ across cloud adoption scenarios, Secure Cloud Foundation accommodates these variances by providing flexibility to turn on or off specific platform capabilities during the initial onboarding.
It can be leveraged by customers to secure almost any cloud workload irrespective of the scale and scope of their cloud adoption.
Typical Cloud Adoption Challenges
Here are some challenges organizations face while adopting a public cloud platform to host enterprise workloads and/or data. Even though the challenges may overlap across different adoption scenarios, key challenges are highlighted below for specific scenarios.
Secure Cloud Foundation addresses these cloud adoption challenges by taking a holistic approach.
Green-Field Cloud Adoption
- Shared Responsibility Model – Security in the cloud is handled by the “Holistic Capability Framework” of Secure Cloud Foundation to create a secure landing zone. New AWS service/capability onboarding into the platform abstracts the service provisioning and operates skillset requirements through appropriate engineering element, such as an operator service catalog.
- Time to market – Secure Cloud Foundation capabilities are fully codified with the appropriate configuration parameter to meet customer-specific requirements. This reduces the time-to-market for building a secure landing zone from months to weeks.
- Secure landing zone overhead for small workloads – Secure Cloud Foundation leverages AWS-native services to realize all possible secure landing zone capabilities and optimize the cost of the secure landing zone.
Brown-Field Cloud Adoption
- Uplifting developer-grade cloud adoption for enterprise workloads – It’s simple to create a new secure landing zone leveraging codified Secure Cloud Foundation platform and then onboard/migrate the existing workloads or applications into the newly-created secure landing zone.
- Possible disruption to the existing workloads – By creating a new secure landing zone, it’s possible to onboard the existing workloads or applications with minimal or no disruption.
- Balancing business agility vs. security governance – Secure Cloud Foundation offers an end-user as well as operator self-service catalog for service provisioning. Similarly, the platform will configure appropriate guardrails to enforce security best practices and standards. This provides the right balance between business agility and security governance.
Figure 1 – Cloud adoption scenarios for Secure Cloud Foundation.
AWS IaaS/PaaS Cloud Adoption
- Define and enforce secure configuration of cloud resources – The Secure Cloud Foundation self-service catalog ensures secure configuration of cloud resources irrespective of the users and their AWS knowledge levels. The “secure-by-design” principle is applied by the engineering team, and the secure design is codified while onboarding an AWS service/capability into the platform.
- Enable cloud-scale operations – Secure Cloud Foundation leverages AWS-native tools as well as automation to achieve cloud-scale operations. All possible operational activities are automated, and operator intervention is required only for exceptions or errors. Also, all possible operational activities are abstracted through appropriate engineering work so the operators’ skillset requirements are greatly reduced.
Compliant and Regulated Application Hosting
- Building and maintaining an audit-ready platform – Relevant audit requirements are embedded within Secure Cloud Foundation code for different AWS services/capabilities. This results in an audit-ready platform.
- Continuous compliance validation against standards, guidelines, and best practices – The platform leverages AWS-native capabilities for validating AWS resource configuration compliance as well as Cloud Security Posture Management (CSPM). Hence, the compliance checks are codified to facilitate continuous compliance.
- Secure-by-design adoption – The “secure by design” principle is applied by the engineering team, and the secure design is codified while onboarding an AWS service/capability into Secure Cloud Foundation. Hence, secure configuration of cloud resource is guaranteed irrespective of the users and their AWS knowledge levels.
Cloud-First Adoption
- Building and maturing DevSecOps platform to facilitate agile delivery model (CI/CD) – Secure Cloud Foundation leverages AWS-native CI/CD capabilities along with third-party security tools to address any gaps in the code pipeline. This results with an optimal DevSecOps pipeline that facilitated agile code movement across environments with appropriate governance.
- Container platform hosting for microservices – Secure Cloud Foundation leverages an AWS Fargate-based serverless container platform for all possible container hosting requirements in order to eliminate the operational complexity of managing a container hosting platform. For special use-cases such as GPU workloads, Amazon Elastic Kubernetes Service (Amazon EKS) is leveraged.
- Container security – The platform leverages cloud-native as well as third-party container security tools to scan container images for vulnerabilities, and to provide runtime protection for running containers.
Data Center Transformation
- Integration between on-premises and cloud-hosted app – Secure Cloud Foundation leverages AWS-native integration services to facilitate integration between applications hosted across on-premises data center, AWS, and other SaaS cloud platforms. Amazon API Gateway provides API-based integration capability, while AWS Glue enables data integration including ETL capability. AWS Transfer Family facilitates file-based integration across applications.
- Integration between software-as-a-service (SaaS)-hosted apps – As mentioned above, the platform leverages AWS-native integration services to facilitate integration between applications hosted across on-premises data center, AWS, and other SaaS cloud platforms.
- Hybrid and/or multi-cloud operations model – Secure Cloud Foundation extends all possible AWS-native tools into on-premises environments to facilitate optimal hybrid cloud operations. This helps to optimize total cost of ownership (TCO) for the hybrid solution.
Security is at the Center of Secure Cloud Foundation
It’s imperative organizations ensure security is not overlooked while enabling agility for business teams.
As the name highlights, Secure Cloud Foundation keeps security at the center while enabling business agility for platform users. This is achieved through defining and enforcing appropriate guardrails while providing self-service agility for cloud resource consumption.
From the history of security events across the globe, it’s evident that configuration errors and violation of best practices are major reasons for security and data breaches. Secure Cloud Foundation addresses this challenge through abstracting the secure configuration of cloud services from the platform consumers (both users as well as platform operators).
Hence, security is not just preached to the platform users but enforced through codification of cloud service configuration and appropriate governance for the code change.
Secure Cloud Foundation is a well-architected, multi-account platform that follows AWS best practices. Ongoing technology governance in the platform is codified through guardrails that implement governance rules for security, compliance, and operations. Guardrails provide governance controls by preventing deployment of resources that don’t conform to selected policies or detecting non-conformance of provisioned resources.
These guardrails represent a set of best practice policies for governing the environment through rules such as disallowing configuration changes to log archive, and requiring account activity to be logged using audit trail logs.
Secure Cloud Foundation on AWS implements guardrails using multiple building blocks, such as AWS CloudFormation to establish a baseline, AWS Organizations service control policies to prevent configuration changes, and AWS Config rules to continuously detect non-conformance.
The platform also reduces the attack surface by adopting security best practices, as well as next-gen capabilities—like Zero Trust Network Access (ZTNA) for remote access—to reduce attack surface. It also restricts lateral movement within the cloud-hosted solution through micro-segmentation.
Secure Cloud Foundation leverages a holistic five-layered security approach—data, application, endpoint, network, and perimeter—to enhance the security posture and meet industry compliance needs. It encapsulates the industry-recognized standards, guidelines, and best practices within platform build and operate phases through codified the “secure-by-design” principle.
Key Characteristics of Secure Cloud Foundation
Secure and Compliant by Design
Codified security and compliance rules, defense-in-depth security design principle with multi-layer security, and best practice adoption. This includes reduced threat surface leveraging next-gen technologies and hardening operating environments.
Plug and Play Architecture
Capability-based model with flexibility to turn on/off a specific capability based on business requirements. This enables Secure Cloud Foundation adoption for varying size and scale of cloud adoption
Everything-as-Code
The platform codifies everything: cloud resource provisioning, configuration management, configuration compliance, security and best practice compliance, cloud resource life cycle management, and operational activity. This is achieved through different AWS-native services and third-party tools.
Balance – Agility vs. Governance
Guardrails vs. complete restrictions to balance business agility with security governance. Isolated sandboxes to facilitate innovation while removing the risk to organization by isolating it from organization data/production applications.
Cloud resource secure configuration is enabled through a self-service catalog. Similarly, security compliance is enforced through automated compliance rules to ensure continuous compliance.
Holistic Approach for Cloud Adoption
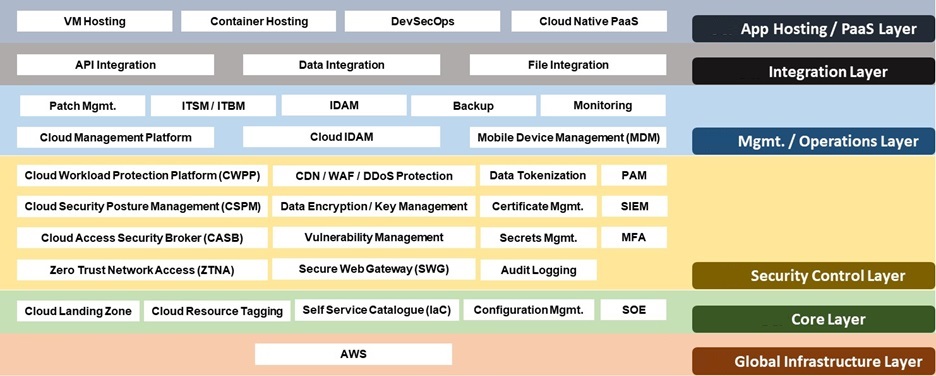
Secure Cloud Foundation’s holistic approach to cloud adoption is evident from its layered capability model.
Figure 2 – Key capabilities across different layers of cloud hosted solution.
The Secure Cloud Foundation security control layer has multiple security capabilities to provide 360-degree security coverage. These can be turned on/off based on specific workload hosting requirements.
The platform offers a capability framework with multiple technology options for realizing the capability in plug-and-play architecture. It helps to shorten the cloud adoption path for any organization with repeatable practices that can be utilized over and over again to drive down the initial cloud implementation cost.
Secure Cloud Foundation facilitates cloud-scale operations by automating the majority of operational activities and leaving just exception handling to platform operators. This improves operational efficiency during platform operations.
Here’s how Secure Cloud Foundation transforms and changes the way the business delivers to various stakeholders:
- Business Teams – Self-service catalog-based cloud resource provisioning in minutes instead of weeks.
- Digital Developers – Fully orchestrated DevOps pipeline with appropriate governance to promote code from development to test and then to production.
- Data Analysts – Self-service Amazon SageMaker notebook provisioning to train and run big data models to make business critical data insights.
- CXOs – Centralized executive dashboard on cloud usage, service adoption, policy compliance, and delivery excellences across multiple cloud platforms.
- IT Operation Teams – Digital IT command center, a monitor of monitors solution to focus on actionable insights and critical incidents by gaining control over alert storms.
- IT Security Operations Teams – Enhanced security architecture to safely adopt IaaS, PaaS, and SaaS cloud platforms.
Secure Cloud Foundation Platform Onboarding
The Secure Cloud Foundation platform is a fully codified “everything-as-code” platform with a set of configuration parameters for different platform components and capabilities. Here are the high-level steps and timelines involved for onboarding.
Onboarding Workshops
The Secure Cloud Foundation platform onboarding team from Infosys Compaz will set up workshops with customer stakeholders to collect and confirm specific parameter values before configuring the platform with the corresponding values. The onboarding team provides default values for the parameters based on industry best practices. Customers can either accept the default values, or modify the values based on the customer requirements.
Timeline for onboarding workshop ranges from 1-2 weeks based on the number of platform components/capabilities in-scope for onboarding across different platform layers.
Platform Configuration
During this step, the Secure Cloud Foundation platform will be configured based on customer-specific parameter values collected during the workshop. The onboarding team performs basic validations to assess the accuracy of the configuration. Customers will then validate the platform through user acceptance testing (UAT) and other third-party non-functional testing.
Timeline for platform configuration ranges from 3-4 weeks.
Transition to Platform Operations
This is an internal activity between the Infosys Compaz platform onboarding team and platform operations team. Since the onboarding team builds a dedicated Secure Cloud Foundation for every customer with customer-specific configuration, the platform has to be handed over to operation team for ongoing operations.
This includes handing over of customer-specific onboarding parameter values, lean design document, and platform code base with customer specific configuration. Timeline for the transition ranges from 1-2 weeks.
Conclusion
As organizations accelerate their cloud adoption, it’s critical they take a holistic approach to cloud security. This ensure bad actors are kept away from applications and data.
In this context, Secure Cloud Foundation from Infosys Compaz (iCompaz) ensures to provide a holistic, multi-layer security for cloud-hosted workloads by creating a secure landing zone. The platfrom also enables organizations to run cloud-scale operations irrespective of the size of the business and the cloud workload size or volume.
.

.
Infosys – AWS Partner Spotlight
Infosys is an AWS Premier Consulting Partner that helps enterprises transform through strategic consulting, operational leadership, and co-creation of solutions in mobility, sustainability, big data, and cloud computing.
Contact Infosys | Partner Overview
*Already worked with Infosys? Rate the Partner
*To review an AWS Partner, you must be a customer that has worked with them directly on a project.