AWS Partner Network (APN) Blog
How to Build a Fintech App on AWS Using the Plaid API
By Rana Dutt, Sr. Solutions Architect – AWS
By Justin Plock, Principal Solutions Architect – AWS
 |
| Plaid |
 |
Open Finance initiatives have been gaining momentum across the world. These initiatives require that banks provide access to customer data through a common, open API for third-party applications, which are referred to as fintech apps.
The fintech app providers are generally not banks, but they offer users a variety of convenient payment and finance features on smartphone apps. These apps enhance the customer experience and foster greater choice and innovation. Users simply need to link the app to their bank and brokerage accounts, and grant the necessary permissions.
Fintech apps offer users benefits such as:
- Viewing balances across multiple bank accounts.
- Initiating payments to friends.
- Applying for loans without gathering and scanning bank and income statements.
- Paying for things online using a “Buy Now Pay Later” plan.
- Showing monthly income and expense categories to help set budgets.
- Displaying overall investment performance across multiple brokerage accounts.
- Buying crypto-assets.
In this post, I will show you how to build and deploy a basic fintech app on Amazon Web Services (AWS) in under an hour by using the Plaid Link API. This app allows users to sign up, log in, select their bank from a list, connect to that bank, and display the account balances.
About Plaid
Plaid is a San Francisco-based financial services company and AWS Partner that helps fintech providers connect users safely to their bank accounts.
The Plaid Link acts as a secure proxy between a fintech app and a bank. With Plaid, application developers no longer need to worry about implementing scores of different ways to access data in myriad financial institutions.
Plaid is currently able to connect to more than 12,000 banks and financial institutions throughout the world. It provides a single API to connect to them. Currently, about 5,500 fintech apps use Plaid’s API to enable their users to access their bank accounts.
What We Will Build in This Post
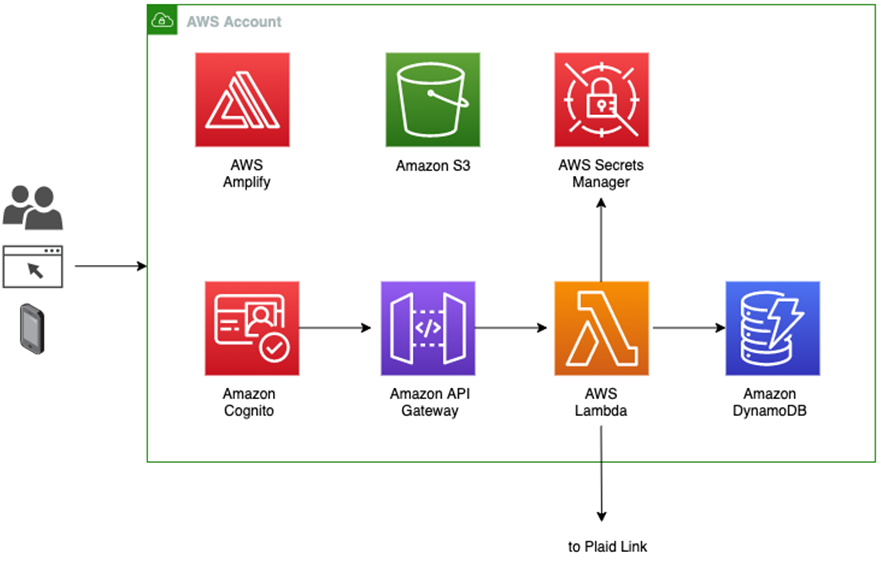
Through this post, we will build a demo fintech app on AWS using the AWS Amplify framework and Plaid Link. AWS Amplify helps us quickly build a serverless web app with a React frontend, user sign-up and sign-in using Amazon Cognito, an Amazon API Gateway-based REST API, and an Amazon DynamoDB database for storage.
Figure 1 – Architecture of demo fintech app.
AWS Amplify generates the code for signing up and authenticating users who are then stored in a Cognito user pool. It also helps create a REST API invoked by the React frontend and implemented by an AWS Lambda function behind Amazon API Gateway. The backend Lambda function sets up the Plaid Link which allows the end user to interact with a selected bank.
AWS Amplify also helps store the Plaid API key securely in AWS Secrets Manager so that it never needs to appear in the code or in a file. Plaid access tokens (described in the next section) are encrypted and stored in the DynamoDB database.
This is a completely scalable and secure architecture which does not require the user to manage any server instances.
How Plaid Link Works
To build an app using Plaid Link, you first need to go to Plaid.com, click on the Get API Keys button, and create an account. You can create a free sandbox account to start.
You can then log into your dashboard and find your sandbox API key under the menu for Team Settings – Keys.
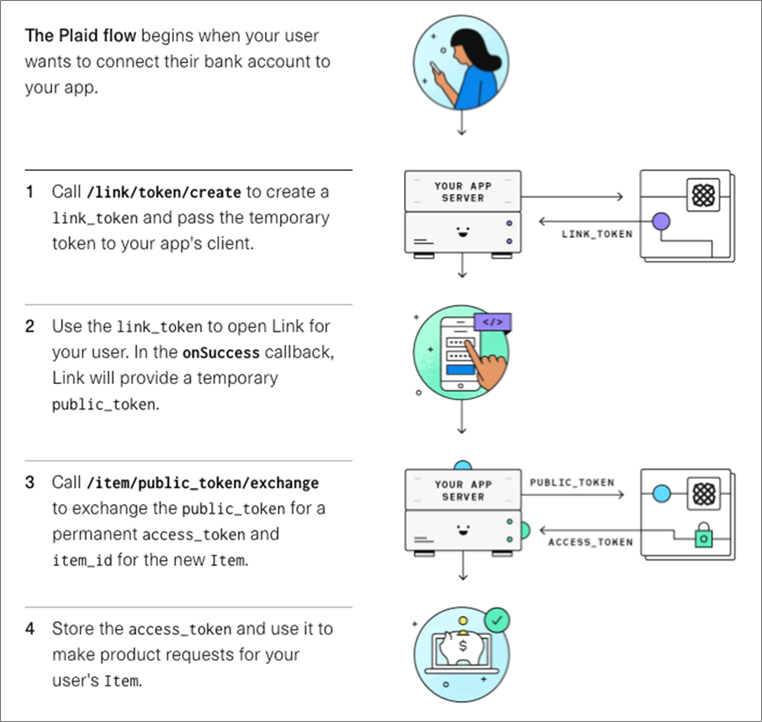
The following diagram shows what our demo Web app needs to implement.
Figure 2 – Plaid Link flow.
All API calls are made through a Plaid client object. The message flow is as follows:
- The app first creates a Plaid client object by passing in the Plaid API key and Plaid client ID. It then calls the client’s createLinkToken method to obtain a temporary link token.
- When the user selects a bank, the app uses the link token to open a Plaid Link to the bank and obtain a temporary public token.
- The app then calls the client object’s exchangePublicToken method to exchange the public token for a permanent access token and an item ID that represents the bank.
- The app encrypts and stores the access token in DynamoDB for subsequent requests pertaining to that item. For example, the app can pass the access token to the client object’s getTransactions method to obtain a list of transactions within a specific date range.
Building and Deploying the App
Prerequisites
- Make sure you have created a sandbox account at Plaid as described above, and obtained your API keys.
- You also need to install AWS Amplify and AWS Serverless Application Model (AWS SAM).
- Docker Desktop is also required by AWS SAM to build the application.
- If you have not already done so, create a default AWS configuration profile by running the aws configure command.
- A personal GitHub account and Personal Access Token (PAT) with the “repo” scope.
Building the App
Fork the repository and clone it to your local machine, and then run sam build:
SAM will prompt you to provide values for the missing parameters. You can hit Enter to accept the default value provided in the brackets.
SAM will monitor the CloudFormation stack as it is being deployed. Once CloudFormation finishes, you can access the application within the Amplify console to monitor the deployment process.
Application Design Principles
The sample application demonstrates architectural best practices for transporting and storing sensitive information, including:
- Amazon Cognito is used to store user information, including passwords and multi-factor authentication (MFA).
- AWS Secrets Manager is used to encrypt and store the Plaid client ID and client secret.
- Amazon DynamoDB Encryption Client is used to client-side encrypt the Plaid access token before storing it within DynamoDB (which is using server-side encryption).
- Frontend React application communicates to the API for all of its data access patterns.
- Amazon API Gateway is used to verify JSON Web Tokens (JWTs) from Cognito before invoking AWS Lambda functions to service the request.
- AWS Identity and Access Management (IAM) policies follow the principle of least privileged access by only granting required access.
Testing the App
Go to the FrontendUrl URL displayed by the sam deploy command, and sign up as a new user. After logging in, select a bank from the list displayed.
If you are using the sandbox environment, use the credentials user_good / pass_good to access the bank and display the accounts.
Conclusion
The walkthrough in this post demonstrates how easy it is to use AWS Amplify to create a secure, scalable, and completely serverless fintech app on AWS that allows users to sign up, select from among the 10,000 banks that Plaid Link connects to, and obtain the account balances.
From here, you can add features such as making payments to friends or vendors, displaying transactions across multiple accounts, sending low balance alerts and helping set a budget.
Plaid – AWS Partner Spotlight
Plaid is an AWS Partner that helps fintech providers connect users safely to their bank accounts.