AWS for Industries
FSI Spotlight: Amazon ECR
This blog post discusses five key considerations for using Amazon Elastic Container Registry (ECR) in the financial services industry. Considerations include achieving compliance, data protection, isolation of computing environments, automating audits with APIs, and operational access and security. We provide specific guidance and suggested reference architectures for each consideration, which can help you streamline the service approval process for Amazon ECR. Adapt these considerations to your business, compliance, and security requirements.
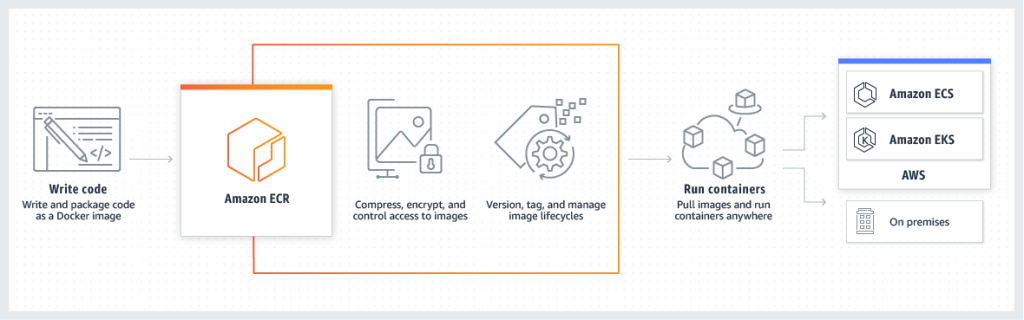
Amazon ECR is a fully managed container image registry service that makes storing and managing container images easy. Amazon ECR Integration with different AWS Services enables fast deployment of containerized workloads.
You can create public or private repositories. Public repositories are accessible to anyone, while private repositories are only accessible to authorized users. Once you have created a repository, you can push your container images. You can deploy these Amazon ECR container images to different compute environments such as Amazon Elastic Container Service (Amazon ECS), Amazon Elastic Kubernetes Service (Amazon EKS), AWS Fargate, AWS Lambda, Amazon EC2, etc.
Amazon ECR also provides features to help you manage your container images.
- Image scanning: Scan your images for vulnerabilities.
- Image replication: Replicate your images to multiple regions for high availability.
- Image tagging: Tag your images with metadata to make them easier to manage.
- Image policy: Create policies to control who has access to your images.
- Image signing: Amazon ECR integrates with AWS Signer to provide a way for you to sign your container images.
Amazon ECR is a secure, scalable, and reliable way to store and manage container images. It is a great choice for any organization that uses containers.
Figure 1: Amazon ECR is a fully managed container registry
Amazon ECR Use Cases
Cleo One reduced developer infrastructure by 66 percent and saved over 40 percent on costs by migrating to Amazon Web Services (AWS). Cleo One is a financial technology provider that makes complex and fragmented trading tools available to everyone. Amazon ECR helps Cleo One automate its deployment process and allows the team to deploy four times faster than they previously could.
Verrency, a global platform provider based in Australia, offers a secure application programming interface (API) platform to help banks, card issuers, and payment networks drive higher customer engagement to support high-performance requirements, Verrency uses Amazon ECS and Amazon ECR to deploy and scale containerized applications across regions.
Avaloq developed a fully integrated banking software – bank in a box- providing an enhanced digital experience to banks and wealth managers. Bank-in-a-box fosters collaboration and innovation among customers, partners, and third-party developers. Avaloq leverages Amazon EKS and Amazon ECR to automate the provisioning of a bank-in-a-box in just minutes. This automation has significantly streamlined their operations and increased efficiency.
Achieving compliance with Amazon ECR
Amazon ECR is a managed service, and third-party auditors regularly assess its security and compliance. As part of the AWS shared responsibility model, Amazon ECR is in the scope of the following compliance programs. You can obtain corresponding compliance reports under an AWS non-disclosure agreement (NDA) through AWS Artifact. Amazon ECR compliance status doesn’t automatically apply to applications you run in the AWS Cloud. Your scope of the shared responsibility model when using Amazon ECR is determined by the sensitivity of your data, your organization’s compliance objectives, and applicable laws and regulations. Your use of Amazon ECR is subject to compliance with standards like HIPAA, PCI, or FedRAMP, and AWS provides resources to help.
| C5 | Cloud Computing Compliance Controls Catalog |
| CCCS | Canadian Centre for Cyber Security |
| DESC CSP | Dubai Electronic Security Centre Cloud Service Provider Security Standard |
| DoD CC SRG | Department of Defense Cloud Computing Security Requirements Guide |
| FedRAMP | Federal Risk and Authorization Management Program |
| FINMA | Swiss Financial Market Supervisory Authority |
| GSMA | Global System for Mobile Communications Association |
| HIPAA BAA | Health Insurance Portability and Accountability Act |
| HITRUST CSF | Health Information Trust Alliance Common Security Framework |
| IAR | United Arab Emirates Information Assurance Regulation |
| IRAP | Information Security Registered Assessors Program |
| ISMAP | Information System Security Management and Assessment Program |
| ISO and CSA STAR certificates | International Organization for Standardization (ISO) and Cloud Security Alliance (CSA) Security Trust Assurance and Risk (STAR) |
| K-ISMS | Korea-Information Security Management System |
| MTCS | Multi-Tier Cloud Security |
| OSPAR | Outsourced Service Provider’s Audit Report |
| PCI | Payment Card Industry Data Security Standard |
| PiTuKri | Criteria for Assessing the Information Security of Cloud Services |
| SOC | System and Organization Controls |
Table 1: Amazon ECR is in the scope of these compliance programs
Data protection with Amazon ECR
The AWS shared responsibility model applies to data protection in Amazon Elastic Container Service. AWS protects the global infrastructure that runs AWS Cloud, and you are responsible for maintaining control over the content that is hosted on this infrastructure. This content includes the security configuration and management tasks for your AWS services. For more information about data privacy, see the Data Privacy FAQ. For information about data protection in Europe, see the AWS Shared Responsibility Model and GDPR blog post on the AWS Security Blog.
Protect and secure your AWS account credentials and setting up individual users with AWS IAM Identity Center (successor to AWS Single Sign-On) or AWS Identity and Access Management (IAM). This approach ensures users are given only the permissions necessary to fulfill their job duties. We also recommend that you secure your data in the following ways:
- Use multi-factor authentication (MFA) with each account.
- Use SSL/TLS to communicate with AWS resources. We require TLS 1.2 and recommend TLS 1.3.
- Use AWS encryption solutions and all default security controls within AWS services.
- Use a FIPS endpoint when you require FIPS 140-2 validated cryptographic modules when accessing AWS through a command line interface or an API. For more information about the available FIPS endpoints, see Federal Information Processing Standard (FIPS) 140-2.
Don’t put confidential or sensitive information, such as your customers’ email addresses, into tags or free-form text fields. When you work with AWS services using the console, data you enter for free-form text fields used for names may be used for billing or diagnostic logs.
Encryption of data-in-transit
Amazon ECR transfers your container images over HTTPS. You can configure policies to manage permissions and control access to your container images using IAM users and roles without managing credentials directly on your Amazon EC2 instances.
Encryption at rest
Amazon ECR supports encryption at rest for your container images. Amazon ECR encrypts your images using either:
- Amazon S3-managed encryption keys (SSE-S3): This is the default encryption method for Amazon ECR. Amazon ECR creates and manages the encryption keys for your images.
- AWS Key Management Service (KMS)-managed encryption keys (SSE-KMS): You can use your own KMS keys to encrypt your images. SSE-KMS gives you more control over the encryption keys and the encryption process.
When you create an Amazon ECR repository, you can encrypt the images. Amazon ECR will encrypt the container image layer data and manifest. The encryption keys are stored in Amazon S3 and are not accessible to you. When you pull an image from an encrypted repository, Amazon ECR decrypts the image layer data and its manifest before sending it to your instance. You do not need to do anything special to decrypt the images. Encryption at rest is an excellent way to protect your container images from unauthorized access. You can find more information on Amazon ECR encryption at rest.
Environment isolation
Amazon ECR is a managed service and benefits from AWS’s global network security. For details on how AWS ensures infrastructure security, references are provided to AWS Cloud Security and the Infrastructure Protection in Security Pillar AWS Well‐Architected Framework.
Access to Amazon ECR is through AWS-published API calls, and clients accessing Amazon ECR must adhere to specific security protocols—support for Transport Layer Security (TLS). We recommend TLS 1.3 and support 1.2 for compatibility use cases. Use of cipher suites with perfect forward secrecy (PFS), such as DHE (Ephemeral Diffie-Hellman) or ECDHE (Elliptic Curve Ephemeral Diffie-Hellman), and systems like Java 7 and later versions support these modes.
All requests to Amazon ECR must be signed using an access key ID and a secret access key linked to an IAM principal. Alternatively, you can generate temporary security credentials using the AWS Security Token Service (AWS STS) to sign requests.
You can use Amazon VPC endpoints to isolate your Amazon ECR traffic from the public internet. Amazon VPC endpoints allow you to connect to Amazon ECR service within your VPC without exposing your traffic to the public internet. Amazon VPC Endpoints can help to improve the security of your Amazon ECR environment.
Operational access and security
Shift left to secure your supply chain, blog post outlines how to secure your container images using a build pipeline. A build pipeline is a set of automated steps that are used to build, test, and deploy software. By integrating security checks into your build pipeline, you can ensure that your container images are secure before they are deployed to production. Amazon ECR provides security features to secure your container images. Use these features to configure Amazon ECR to meet your security and compliance objectives. You can also use other AWS services that help you to monitor and secure your Amazon ECR resources.
Identity and Access Management (IAM) for Amazon ECR
With AWS IAM, you can create policies defining who has permission to access resources and what actions they can perform. You can create IAM users, groups, and roles to manage access to Amazon ECR repositories. By attaching policies to these IAM entities, you can define granular permissions like push, pull, and delete for specific repositories. Use service-linked roles for, which grants permissions to other AWS services to act on your behalf.
Repository Policies
Amazon ECR provides resource-based permissions using repository policies. These allow you to specify detailed access controls for your repositories. You can allow or deny access based on AWS account, IAM user, or IAM role and specify the actions allowed or denied.
Multi-factor authentication (MFA)
You can require MFA for all API calls to Amazon ECR. MFA helps to protect your account from unauthorized access.
Audit and Monitor with CloudTrail and CloudWatch
AWS CloudTrail captures API calls made on your account and delivers the log files to an Amazon S3 bucket, including calls from the AWS Management Console, AWS CLI, and AWS SDKs. You can set up CloudWatch alarms to monitor unusual or unauthorized activities.
Lifecycle Policies
Amazon ECR provides lifecycle policies to help you manage the lifecycle of images in your repositories. While this is more about operational efficiency, it can also be a part of a security strategy by ensuring the automated removal of old and potentially insecure images.
Conclusion
In this post, we reviewed Amazon ECR and highlighted key information that can help FSI customers accelerate the approval of the service within these five categories: achieving compliance, data protection, isolation of compute environments, automating audits with APIs, and operational access and security. Although this guidance is not a one-size-fits-all approach, it can be adapted to meet your organization’s security and compliance requirements and provide a consolidated list of critical areas for Amazon ECR.
In the meantime, visit our AWS Financial Services Industry blog channel and stay tuned for more FSI news and best practices.