Microsoft Workloads on AWS
An AWS perspective on securely managing Windows Server infrastructure at scale
In this blog, we will provide a holistic approach to help customers manage their Windows Server infrastructure securely and at scale for both cloud-only and hybrid cloud using AWS services. This approach helps our customers use more efficient, unified, and automated operational solutions for managing server infrastructure.
Cloud innovations have opened new possibilities for enterprise customers running Windows Server infrastructure. Enterprise IT infrastructure nowadays is changing towards an internet-scale identity provider for all users and devices. Servers are dynamically provisioned upon demand or when new configurations become available. IT administrators use centralized end-to-end configuration management tools with automated processes regardless of the servers’ physical and network location. Users work remotely without persistent connection to an isolated corporate network.
The following AWS services are designed to help facilitate secure and scalable management of a server fleet in the cloud, on premises, and in hybrid environments. Specifically, we will consider the following services:
- Manage access with AWS Single Sign-On and Identity and Access Management.
- Deploy servers with EC2 Image Builder.
- Configure Windows EC2 instances using AWS Systems Manager State Manager.
- Manage Windows Servers with AWS Systems Manager Fleet Manager.
- Update OS and application with AWS Systems Manager Patch Manager.
- Monitor Windows Servers with Amazon CloudWatch.
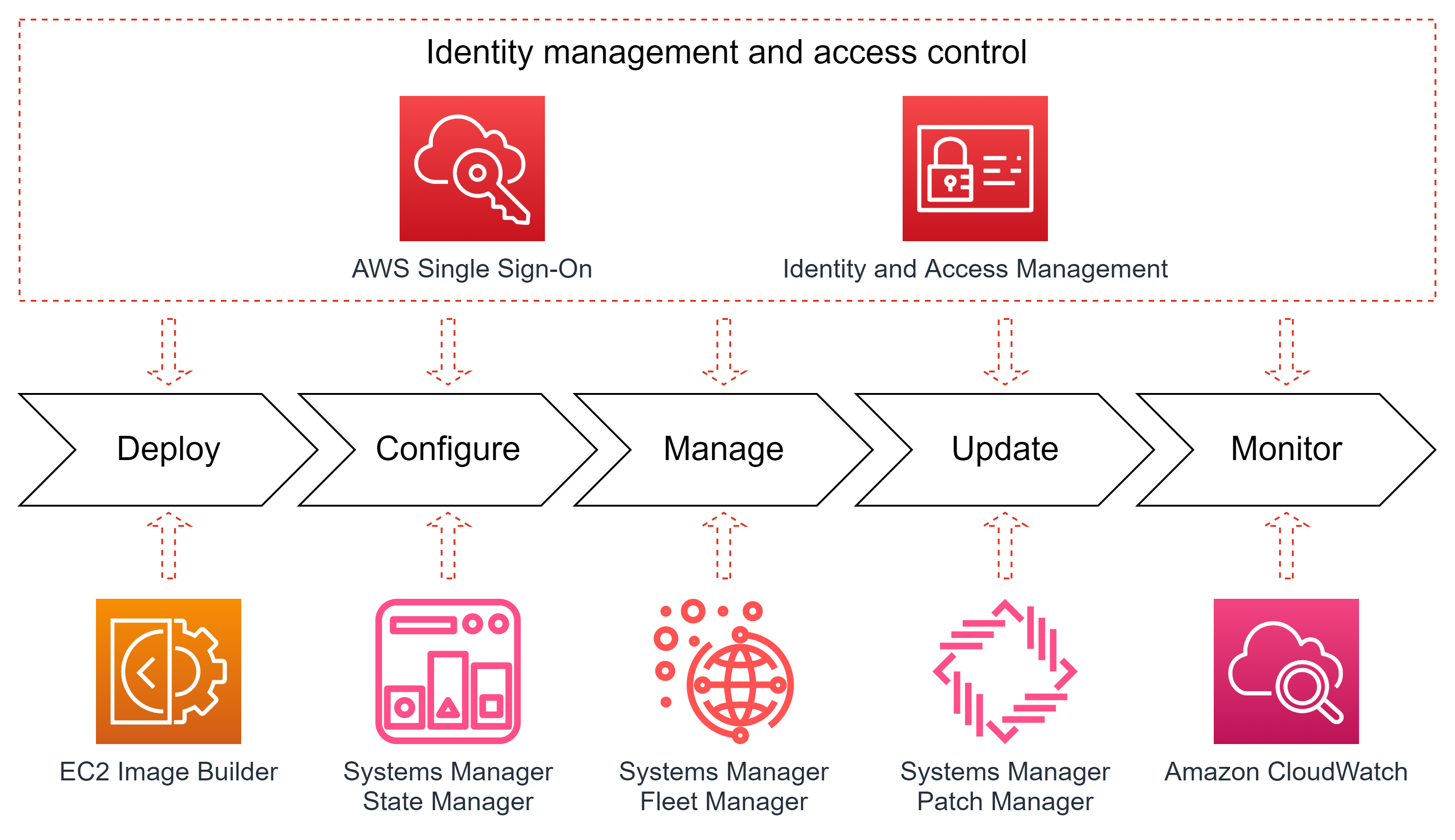
Figure 1. AWS services on different phases of a server lifecycle.
Each of these services can be added to your infrastructure individually or in combination and can be used both for Active Directory domain-joined or domainless servers.
1. Identity and Access Management with AWS Single Sign-On
Every customer has a unique history of their corporate identity services, usually designed at a different time and based on different technologies and security protocols. Many customers have spent years building and implementing on-premises enterprise identity services, like Active Directory (AD), and created or deployed corporate applications relying on them. Others have already adopted identity providers as a service. AWS Identity Services provides an easy way to integrate with any combination of legacy identify configurations and modern identity services.
AWS Single Sign-On (AWS SSO) is an identity hub enabling customers to create and manage a new identity store in the cloud or bring their existing identities from a cloud identity provider or on-premises AD. Your IT staff can continue to use their existing identities to manage Windows Servers deployed in the cloud. AWS SSO works as an identity abstraction layer connecting users, applications, and services, regardless of the identity source, by using open standard protocols for identity federation. AWS SSO works with Azure AD, Okta, OneLogin, Ping Identity, or any other provider supporting SAML 2.0 and SCIM standards.
After you create user credentials in AWS SSO (or integrated it with an external IdP), your IT engineers can use them to log into Windows Server instances running on Amazon EC2. To precisely control which users will have access to which groups of servers, you can pass user attributes in the AWS session when your workforce signs into the cloud using AWS SSO. For example, only a designated group of database administrators may be able to log into Amazon EC2 instances with Windows Server running SQL Server for the production environment.
AWS SSO credentials can be used in Amazon EC2 and AWS Systems Manager Fleet Manager console to securely log into cloud-based Windows desktop sessions directly from the management console. This feature enables users to log into the server desktop with their modern individual credentials without joining servers to Active Directory, connecting the EC2 instances to the internet, or using bastion hosts.
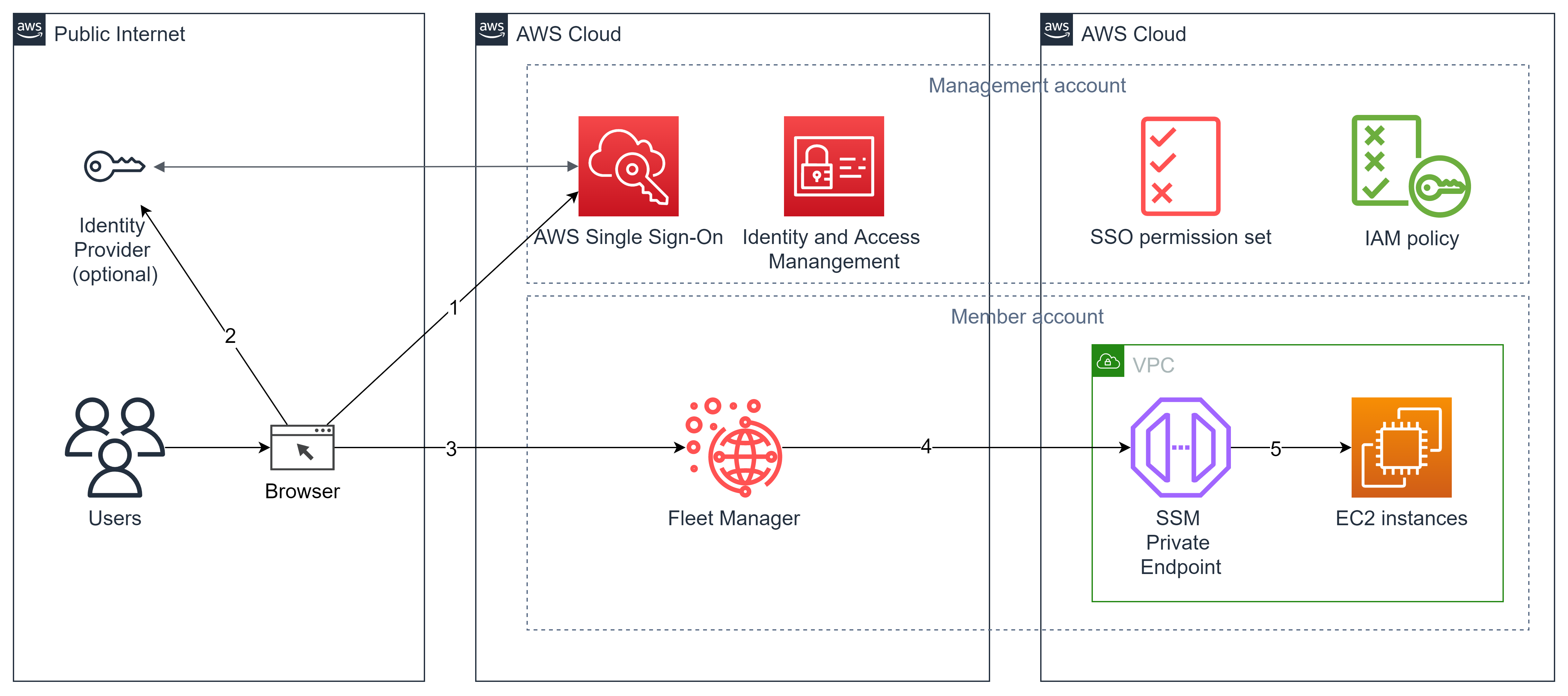
Figure 2. AWS SSO roles permission sets and IAM role assumption to access Windows Server EC2 with SSO credentials.
In the example in Figure 2, a user navigates (1) to the corporate AWS Single Sign-On portal (AWS SSP). In a case when AWS SSO is configured to use an external identity provider, it will redirect (2) the user to authenticate using the external identity. IdP performs the credential validation and redirects the user back to the AWS SSP portal. The user navigates (3) to the Fleet Manager page in their AWS Account to see a list of the EC2 instances running in their AWS Account. After selecting the EC2 instance, the user clicks the “Connect to the Remote Desktop” button and a browser opens (4) a new tab with the interactive remote session under the user account name provided when the user logged into AWS SSO. Fleet Manager automatically creates a local administrative user with a temporary password for this session and automatically logs user in.
Please, refer to the AWS Security blog post to learn how to enable secure seamless single sign-on to Amazon EC2 Windows instances with AWS SSO.
2. Deploy servers with EC2 Image Builder
One of the key components of reliable and secure compute infrastructure are server images used to deploy all the server infrastructure. Our customers need to be sure that their domainless and domain-joined on-premises servers and EC2 instances are deployed using the right OS versions, have the right configuration and security setting, and are patched with the latest available software updates.
EC2 Image Builder allows customers to automate the lifecycle of OS images. Customers can start with an Amazon-provided OS image or upload their own image, install and configure the required software, apply server configuration and security policies, automatically run pre-configured or customer-provided tests, and, if tests are successful, create an image. If required, EC2 Image Builder can replicate a generated image to AWS Regions where this image will be used for manual or automated server deployment (Figure 3).
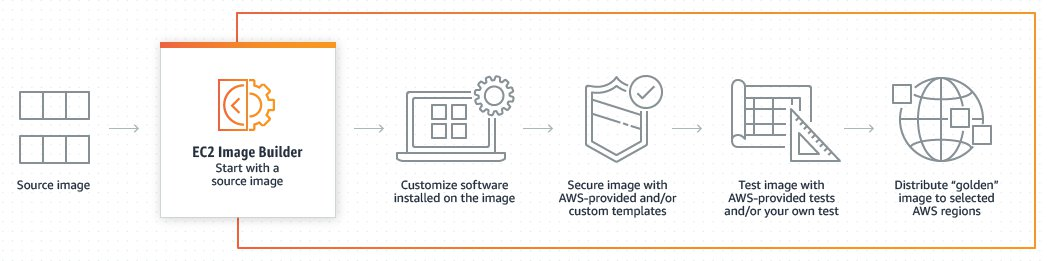
Figure 3. EC2 Image Builder pipeline to create an AMI image.
The EC2 Image Builder automation pipeline allows customers to have their machine images always configured, tested, and updated without the need for any manual actions. AWS-provided tests can be used to readily validate functionality, such as if images boot, if requisite drivers are installed, and if images are hardened to satisfy security standards.
EC2 Image Builder allows you to create images with only the essential components, reducing your exposure to security vulnerabilities. You can apply AWS-provided security settings to further secure your images to meet security standards requirements, like the Security Technical Implementation Guide (STIG), as illustrated on Figure 4.

Figure 4. Amazon-managed component for hardening Windows Server for STIG compliance.
Using AWS-provided build components, you can: deploy server roles; configure PowerShell, .NET, Go, or Python runtimes; install agents for Amazon Corretto, Amazon Kinesis, and Amazon CloudWatch; and optimize your image for Amazon Elastic Container Service or Amazon Elastic Kubernetes Service.
EC2 Image Builder supports not only Amazon Machine Images, but also multiple virtual machine image formats, including Microsoft Hyper-V (VHD/VHDX), VMware vSphere (VMDK), Open Virtualization Format (OVF), and Raw formats. This feature helps you use consistent OS images across hybrid IT infrastructures spanning the AWS Cloud and on-premises virtualization platforms.
3. Configure Windows EC2 instances using AWS Systems Manager State Manager
Manually managing a large fleet of domainless servers can be challenging because of the large number of settings, potential human errors, and unavoidable configuration drift. AWS Systems Manager State Manager is a secure and scalable configuration management service that automates the process of keeping your Amazon EC2 and hybrid infrastructure in a defined state.
AWS Systems Manager State Manager provides multiple capabilities to ensure the server configuration matches corporate IT policies:
- Install and update third-party software and agents.
- Configure network settings.
- Run custom configuration scripts on managed instances.
You can manually assign EC2 instances or resource groups, or specify tags that will be used to find servers to apply the correct configuration (Figure 5). This approach is very useful for dynamic environments with auto scaling. You can additionally configure the number or percentage of targets that will execute the configuration task at the same time, as well as the error threshold to stop a configuration task if the configuration fails.
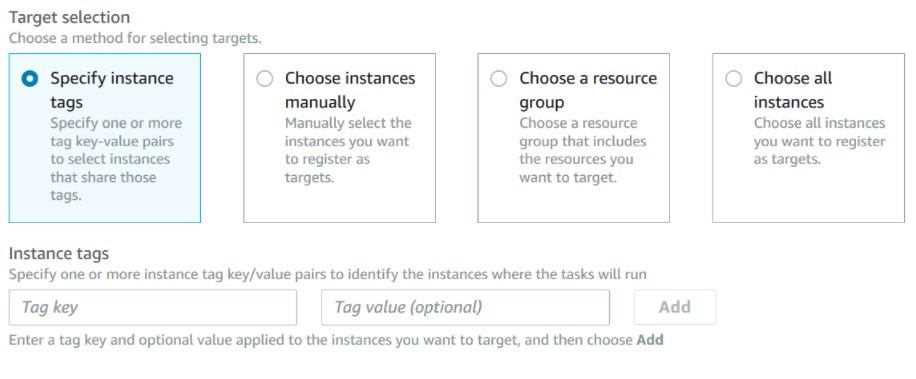
Figure 5. State Manager target selection options.
State Manager is natively integrated with PowerShell Desired State Configuration (DSC). A PowerShell DSC configuration is a specialized PowerShell configuration templates called MOF files. You can run DSC MOF files to enforce a desired state on Windows Server managed instances with State Manager, a capability of AWS Systems Manager. State Manager logs and reports the status of each MOF file execution and reports the output of each MOF file execution as a compliance event, which you can view on the AWS Systems Manager Compliance page.
A detailed walkthrough for deploying AWS Systems Manager State Manager with PowerShell DSC is described in the blog post “Combating Configuration Drift Using Amazon EC2 Systems Manager and Windows PowerShell DSC“. If you are using Active Directory with Group Policies for configuring your Windows Servers, you can simply convert your existing Group Policy objects to PowerShell DCS files using ConvertFrom-GPO commandlet from the BaselineManagement module. After that, you can use exported DSC MOF files in AWS Systems Manager State Manager as described in the State Manager guide.
4. Manage Windows Servers with Fleet Manager
AWS Systems Manager Fleet Manager (Fleet Manager) helps to manage physical and virtual Windows Servers regardless of their network location. When you run thousands of Windows and Linux servers and IoT devices, you need a tool that allows you to perform administrative tasks over diverse fleet of instances and configurations (Figure 6).

Figure 6. Overview of the server fleet in AWS Systems Manager Fleet Manager.
IT engineers can use Fleet Manager as a control panel to gain visibility across all their server fleet with real-time views of log files, event logs, performance counters, and processes (Figure 7), enabling them to quickly troubleshoot issues without manual login to each server.

Figure 7. Exploring system processes on EC2 instance with Windows Server.
Also, Fleet Manager is useful to quickly change Windows Registry settings (Figure 8), or manage local users and groups on servers from the AWS console, which allows IT engineers to quickly fix the issue.
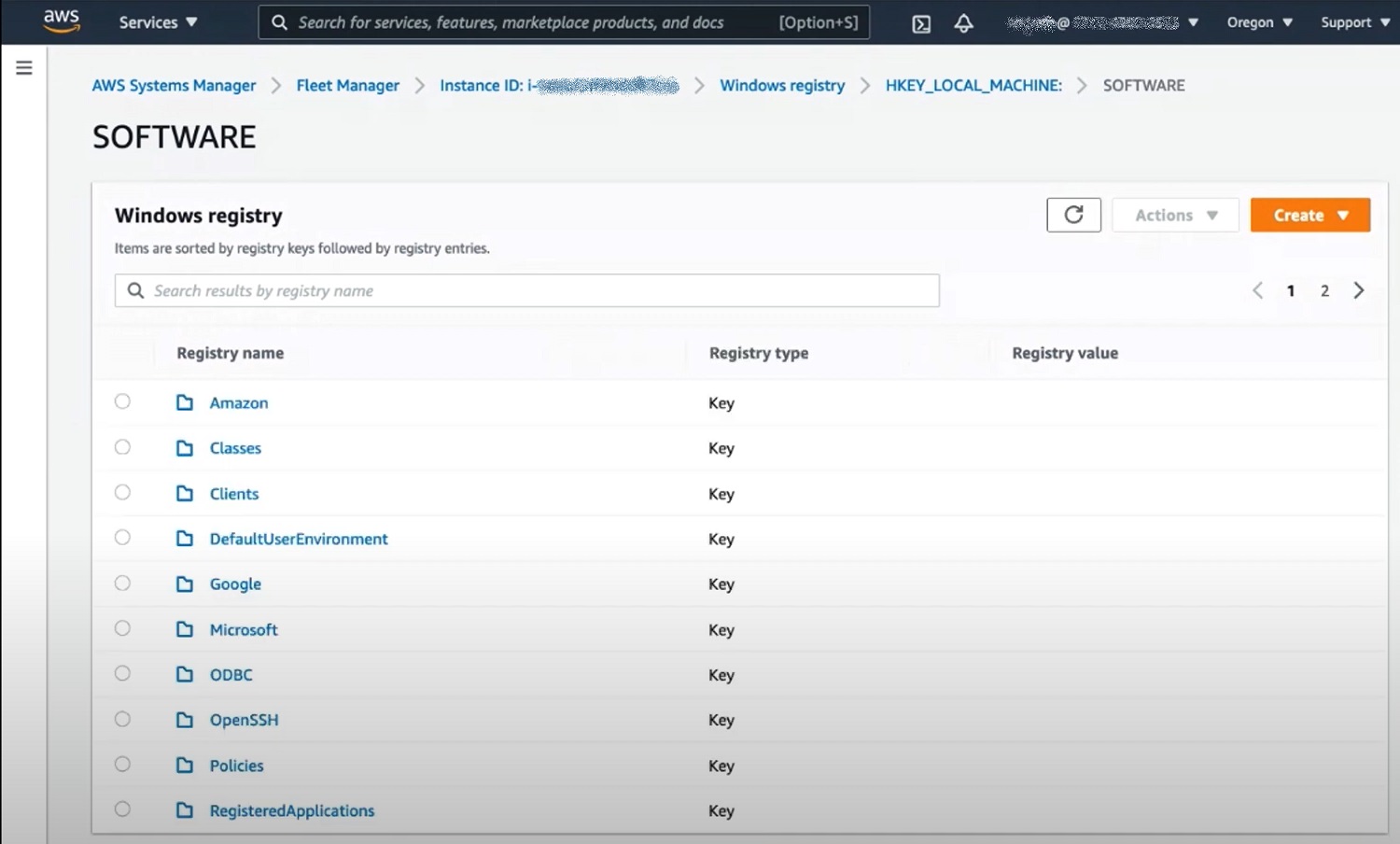
Figure 8. Browsing registry on the EC2 instance with Windows Server in the AWS Systems Manager Fleet Manager console.
Learn more about Fleet Manager at the AWS Systems Manager page.
5. Update OS and application with Systems Manager Patch Manager
Keeping servers up-to-date with security patches is one of the most critical security requirements. Patch Manager is a capability of AWS Systems Manager that automates the process of patching servers with both security related and other types of updates for operating systems and applications like Microsoft Office and Microsoft SQL Server.
Patch Manager automatically downloads Windows patches and service packs from the Microsoft Update website and automatically manages patch baselines based on the release time. In addition, you can manually approve or reject specific patches. You can install patches to groups of servers by using tags for assigning patch baselines. Patch Manager will automatically scan your instances for applicable patches and install them based on the configurable schedule. You can generate a one-time patch compliance report, or generate reports on a regular schedule.
Patch Manager includes pre-created patch baselines for Windows Server: AWS-WindowsPredefinedPatchBaseline-OS and AWS-WindowsPredefinedPatchBaseline-OS-Applications. Both of them approve all critical and security patches for Windows Server and an MSRC severity of “Critical” or “Important.” Patches are auto-approved seven days after release. AWS-WindowsPredefinedPatchBaseline-OS-Applications also auto-approve all patches for Microsoft Applications distributed through Microsoft Update.
Approval rules (Figure 9) can be very fine-grained to match your needs. For example, you may define a shorter auto approval delay for critical updates for Windows Server 2016 and apply this baseline to test EC2 instances, where you want to test patches before rolling them out to the production environment.
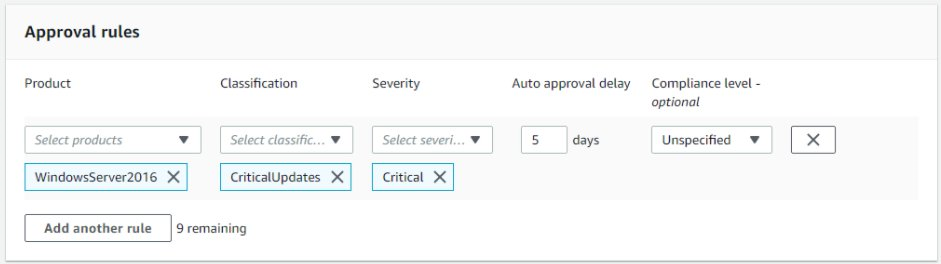
Figure 9. Patch Manager approval rules for deploying updates.
For more information about patching Windows Server infrastructure on AWS we recommend to refer to the detailed blog post “Patching your Windows EC2 instances using AWS Systems Manager Patch Manager”.
6. Monitor Windows Servers with Amazon CloudWatch
Our customers are using Windows Servers hosted in the AWS Cloud, multi-cloud, and on-premises datacenters in both domain-joined or domainless scenarios. By deploying an Amazon CloudWatch agent, you can collect all events and performance metrics from all your servers and applications, monitor them in a single console, and leverage alarms to take automated actions to scale or repair your infrastructure instantly, reducing time to resolution. A CloudWatch agent enables you to collect metrics associated with any Windows Performance counters and stream events from Windows Event Log to CloudWatch logs (Figure 10).

Figure 10. CloudWatch metrics for Windows Server EC2 instances.
Customers can configure a private connection from Amazon VPC to CloudWatch Logs using AWS PrivateLink interface VPC endpoints. This allows you to monitor Windows Server EC2 instances, even when they are deployed in an isolated VPC.
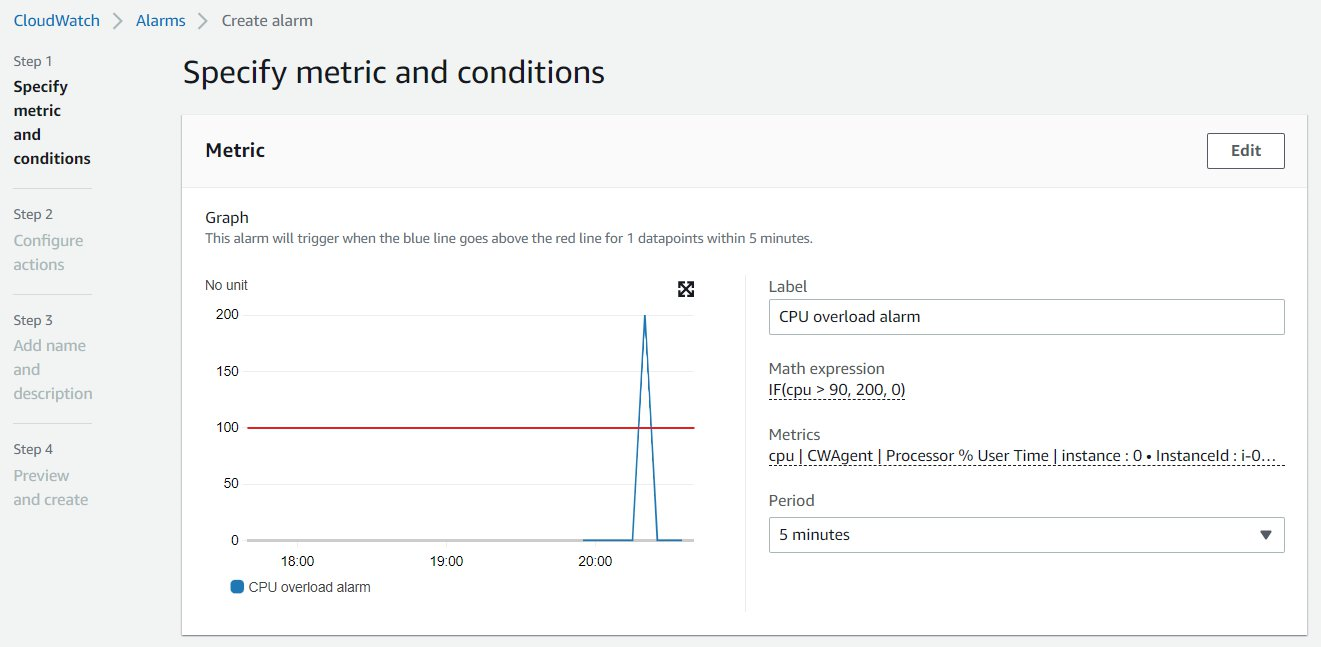
Figure 11. CloudWatch alert based on Windows Server CPU utilization.
CloudWatch can be used to monitor AWS services and your server’s health together (Figure11). You may define calculated and aggregated metrics over multiple servers and AWS services; for example, to trigger autoscaling of your server infrastructure, or run an auto healing script with Lambda function, or notify your engineers that there is an anomaly detected by machine learning. This approach makes your IT infrastructure self-healing and it helps to remediate issues faster with less impact on end users.
Amazon Kinesis agent for Windows allows you to monitor a large fleet of servers and gather data in different formats (like text log files, events, and metrics, or service performance counters), automatically transform them into JSON format, and stream to another service for processing and analyzing (like Amazon CloudWatch, Amazon S3, Amazon Redshift, or Splunk). Kinesis Agent for Windows comes with built-in parsers for log files generated by common Microsoft enterprise services, such as Microsoft Exchange, SharePoint, Active Directory domain controllers, DHCP servers and others. Using Kinesis together with CloudWatch allows you to create CloudWatch alarms for very complex events that require detecting multiple factors in different data sources.
Conclusion
In this post we discussed the AWS services and features that can be used to deploy and manage Windows Server EC2 instances in the cloud-native or hybrid environment without the need to join servers to Active Directory domain.
We covered all stages of the Windows EC2 instance lifecycle, including image-based deployment with EC2 Image Builder, configuration with Systems Manager State Manager, keeping OS and applications updated with Systems Manager Patch Manager, and monitoring the infrastructure and server health with CloudWatch, and managing or integrating customer identity services with AWS Single Sign-On.
AWS can help you assess how your company can get the most out of cloud. Join the millions of AWS customers that trust us to migrate and modernize their most important applications in the cloud. To learn more on modernizing Windows Server or SQL Server, visit Windows on AWS. Contact us to start your modernization journey today.