AWS Partner Network (APN) Blog
Automating AWS Fargate Image Scanning to Block Container Threats
By Vicente Herrera, Product Manager at Sysdig
 |
 |
 |
As DevOps teams roll out applications on AWS container services and tap into the serverless capabilities of AWS Fargate, they must take the necessary steps to secure workloads and manage risk.
Protecting against running vulnerable container images by deploying image scanning is an essential DevOps workflow.
Base container images, commonly built from open source and publicly shared software, provide a convenient starting point, but they can also open the door to the risk of running misconfigured containers and vulnerable code.
In this post, I will discuss how image scanning implemented at various points of the container and Kubernetes lifecycle can provide you with critical insights to ensure security and compliance, without impacting the flexibility you need to build and run your applications.
Sysdig, an AWS Advanced Technology Partner with AWS Competencies in DevOps and Containers, is driving the secure DevOps movement, empowering organizations to secure containers, Kubernetes, and cloud services.
The Sysdig Secure DevOps Platform, built on open source, enables cloud teams to secure build pipelines, detect runtime threats, validate compliance, and monitor performance.
Scanning Container Images to Reduce Risk
AWS Fargate, Amazon Elastic Container Service (Amazon ECS), and Amazon Elastic Kubernetes Service (Amazon EKS) help you automate the deployment of containerized workloads. AWS Fargate is particularly convenient, as it frees you from the constructs and management of host infrastructure.
While the workload isolation offered by AWS Fargate improves security by design, it’s still important to address the risk of running vulnerable containers unchecked in production.
Consider these common threat scenarios:
- A container image mistakenly left with default “root” credentials is pushed to the registry and later deployed on AWS Fargate. The running container now exposes the potential for privilege-escalation attacks.
- An AWS Fargate task runs with an old HTTP library that ignores request size limits. While you expect requests no larger than 1MB, a malicious actor exploits the known vulnerability to send 80GB requests, causing your service to throttle and taking a toll in your hosting bill.
You may be reluctant to implement too many security checks, concerned with losing some flexibility, but the good news is you can automate security scanning to ensure vulnerabilities like the above are detected and blocked.
Image Scanning Basics
An image scanner inspects container image contents to detect threats like the examples described above. You can implement image scanning best practices at several points of your DevOps pipeline, blocking threats before they are deployed into production.
By defining image scanning policies, you can fine tune the validation of image contents against vulnerability databases, and detect misconfigurations like being set to run as a privileged user or including sensitive secrets or passwords.
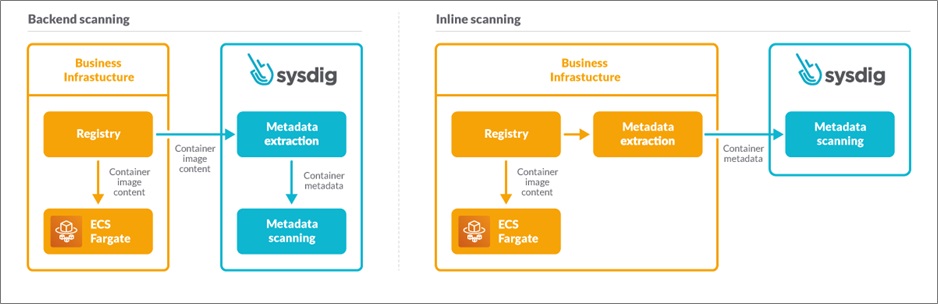
There are two main approaches image scanners can take:
- Backend scanning: Container images are retrieved, and copies are stored local to the scanner backend where the scanning takes place. If your image scanner is a software-as-a-service (SaaS) solution, there may be some security implications to address.
- Inline scanning: With inline scanning, the image scan takes place on your infrastructure, local to where the container image is already stored. In this approach, only metadata about the scan results are sent to scanning solution backend.
Figure 1 – AWS Fargate inline scanning vs. backend scanning.
Inline scanning provides a distinct advantage in that the contents of your container images never leave your infrastructure. This protects your privacy, and helps prevent credential leaking. It’s also necessary when security concerns require an air-gapped environment.
While inline scanning involves a few more components, in practice its configuration is similar to a backend scanning approach.
Overview of AWS Fargate Image Scanning with Sysdig
Let’s now focus on inline image scanning, and how AWS Fargate image scanning works with Sysdig Secure.
The goal of the Sysdig solution in this use case is to trigger an image scan to take place when a deploy command is directed at AWS Fargate.
As shown in the diagram below, the solution takes advantage of several AWS components to enable automation. In particular, the deploy command is detected by Amazon EventBridge, which triggers an AWS CodeBuild pipeline using an AWS Lambda function. It’s within this CodeBuild pipeline that the image scanning runs.
Figure 2 – AWS Fargate inline scanning with Sysdig Secure.
The Sysdig inline image scanner inspects the container image to be deployed and sends its scanning metadata to the backend. The actual image contents never leave the CodeBuild pipeline. The Sysdig backend then evaluates the container metadata against your configured security policies and generates a scan report.
Sysdig retains the container metadata to enable runtime vulnerability checking. This means that as new CVEs are reported by vulnerability databases, there’s no need to re-scan images to determine whether previously scanned images running in production now container a known vulnerability.
In addition to this approach, you can further strengthen your container security by implementing image scanning earlier in your DevOps lifecycle, such as with your CI/CD pipelines and registry.
Deploy Image Scanning with AWS CloudFormation
To deploy the Sysdig image scanner (inline or backend), we’ll use AWS CloudFormation, which provides a common language to model and provision all of the resources needed for applications in an automated and secure way.
Sysdig provides a pre-built CloudFormation template to simplify deployment of the AWS Fargate scanning solution. This makes the setup process as simple as following a link and choosing a few settings.
You can find up-to-date instructions on the Sysdig Fargate scanning installation page.
Let’s dig in!
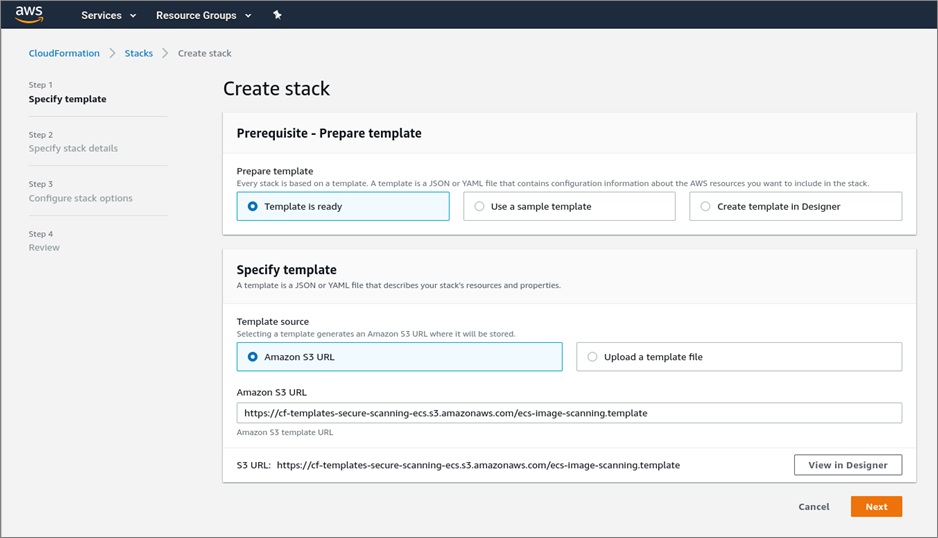
First, make sure to be logged into your AWS console account with your browser. Then, navigate to the CloudFormation template for ECS Fargate image scanning with Sysdig to preview the CloudFormation template.
On the Create stack page, click the Next button to start the template setup.
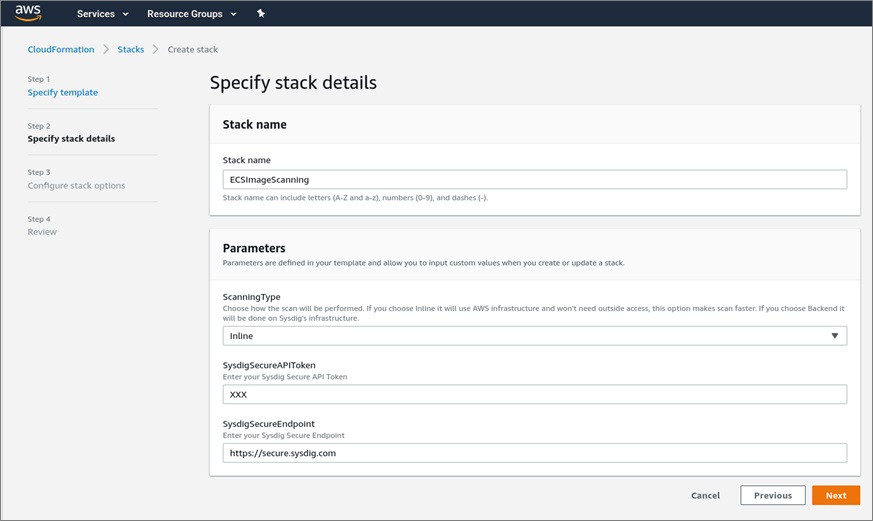
On the Specify stack details step, you can set several configuration options. For example, you can choose between inline scanning or backend scanning.
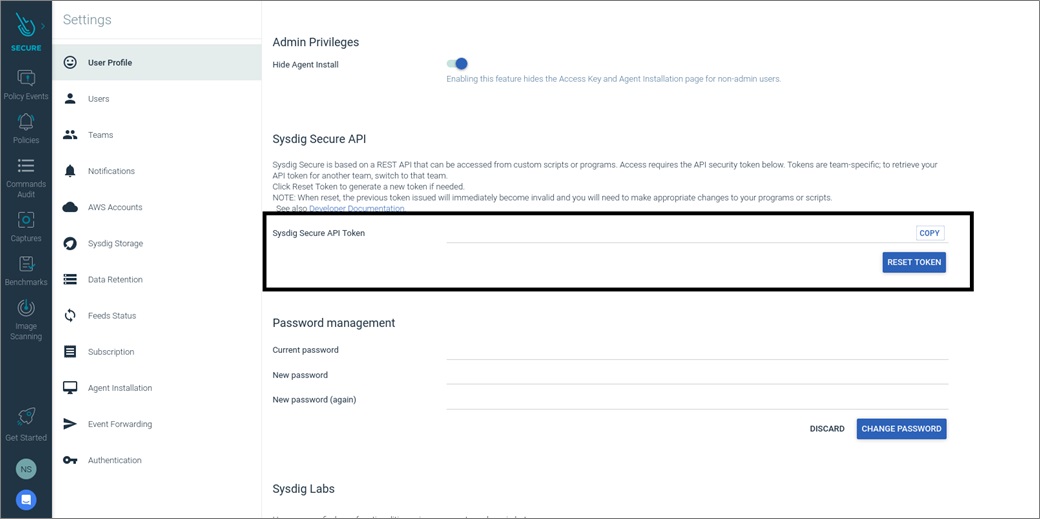
Here, you must also provide your Sysdig Secure API Token found within the Sysdig Secure user interface. To locate this token, click on your profile icon at the bottom left of the screen and select Settings. The API Token will be shown in the first section as shown below.
Note that if using a self-hosted installation of Sysdig, you’ll need to specify your endpoint instead of the default https://secure.sysdig.com. In case you have an air-gapped AWS infrastructure environment, the endpoint has to be accessible from within it.
Once you’ve copied your API token, paste it into the AWS Stack configuration and click Next.
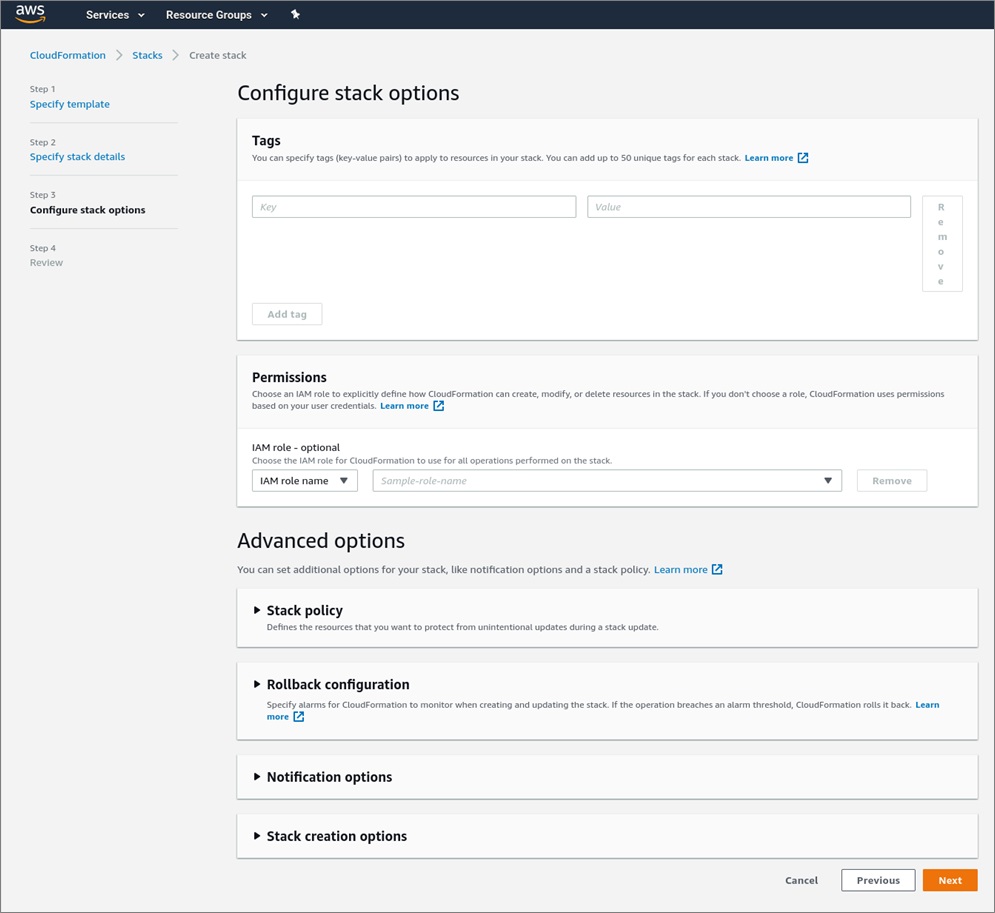
In Configure stack options, a section for adding additional tags and permissions will be shown. If you want to add extra tags or permissions, you can do this here.
When you are ready, click Next.
The last step will present a summary of all the parameters you introduced previously.
Notice that dedicated identity and access management (IAM) roles will be created to perform the scanning. These roles follow the “least privilege principle” to ensure security while enabling automation of the scanning function. Check the box to acknowledge this capability.
Once you’ve checked that everything is correct and are satisfied with the settings, click the Create stack button.
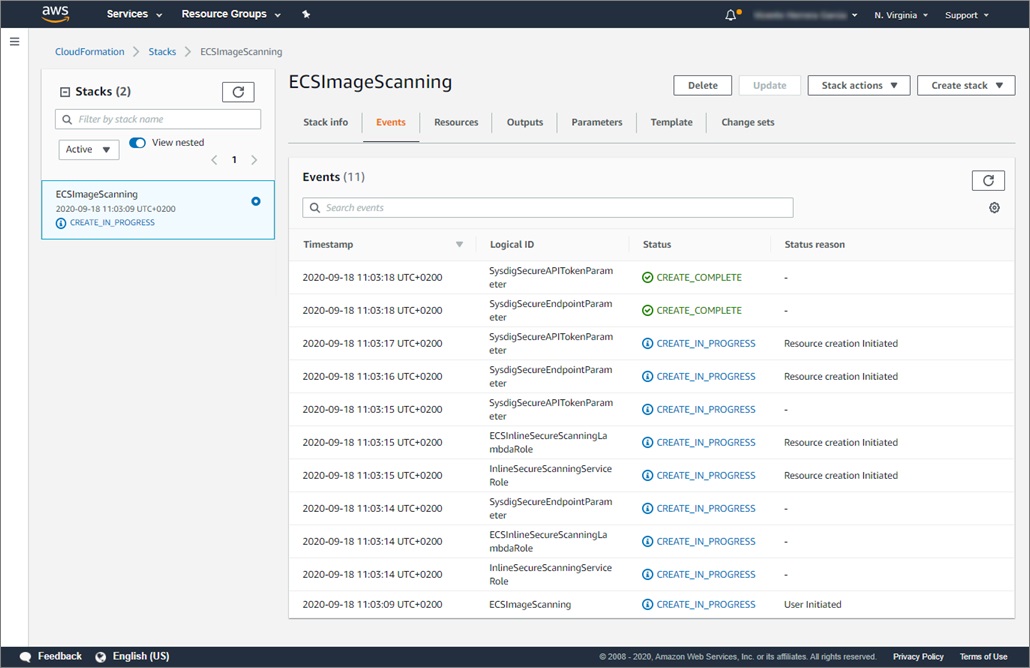
The CloudFormation stack is then created and will immediately start to provision the required resources. This will take several minutes.
You can revisit the CloudFormation screen to check the status of the deployment.
Automatic Scanning for AWS Fargate with Amazon ECS
Once the stack is created, you will be ready to securely run AWS Fargate tasks in your cluster, as all of the images you deploy will be automatically scanned.
Let’s drill into how this works together with Amazon ECS.
When a task in Fargate starts, an event is automatically sent to a Lambda function, which triggers the image scanning.
The Lambda functions created are different depending on whether you’ve configured inline scanning or backend scanning.
If the selected scanning mode is inline, the Lambda function launches a CodeBuild pipeline for each of the task images. If the selected mode is backend, the Lambda function triggers a single API call to the Sysdig Secure backend, which pulls and scans each images on the Sysdig backend.
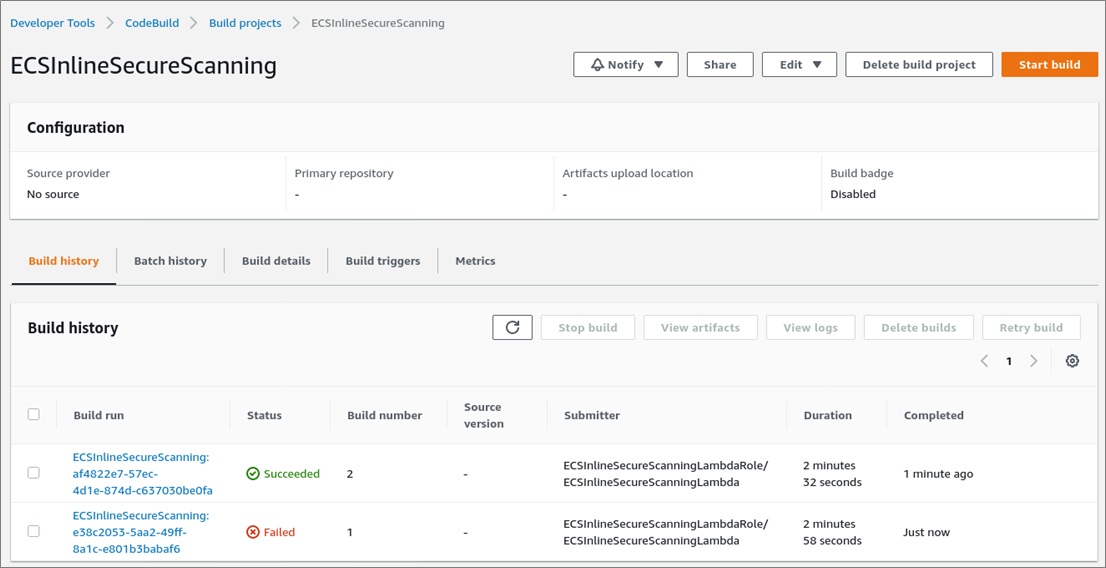
For inline scans, scan reports are available within the CodeBuild pipeline interface.
Scan reports are also be available in Sysdig Secure.
Conclusion
DevOps teams are taking a much greater role in securing applications that run in the cloud.
The AWS Fargate serverless compute engine helps you reduce development costs and focus more effort on building applications. However, the task of ensuring container images are free from risky vulnerabilities is still a critical step in the DevOps workflow.
Automating image scanning for AWS Fargate tasks helps ensure you have visibility into vulnerabilities and misconfigurations that should be addressed to reduce risk in production.
Inline and backend scanning for AWS Fargate from Sysdig provides an easy way to implement security checks for your projects. A single source of truth will help you improve the security and compliance posture of your cloud workloads.
Start using Sysdig with AWS container services today by requesting a free trial of Sysdig Secure via AWS Marketplace.
The content and opinions in this blog are those of the third-party author and AWS is not responsible for the content or accuracy of this post.
Sysdig – AWS Partner Spotlight
Sysdig is an AWS Advanced Technology Partner that is driving the secure DevOps movement, empowering organizations to secure containers, Kubernetes, and cloud services.
Contact Sysdig | Partner Overview | AWS Marketplace
*Already worked with Sysdig? Rate the Partner
*To review an AWS Partner, you must be a customer that has worked with them directly on a project.