AWS Partner Network (APN) Blog
Tech Mahindra’s BMC Helix ITSM Deployment on AWS for End-to-End Data Protection
By Srinivasan AC, Principal Cloud Architect – Tech Mahindra
By Sahana P, Cloud Architect – Tech Mahindra
By Nitin Chahar, Sr. Partner Solution Architect – AWS
By Arvind Raghu, Principal EC2 Specialist – AWS
 |
| Tech Mahindra |
 |
This post describes how Tech Mahindra transitioned a segment of telecom customers in the EMEA region from a legacy monolithic application, BMC Remedy on-premises, to a self-managed microservices application, BMC Helix IT Service Management, utilizing Kubernetes operations (KOps) with end-to-end data protection on Amazon Web Services (AWS).
Tech Mahindra is an AWS Premier Tier Services Partner with the Migration Consulting Competency that specializes in digital transformation, consulting, and re-engineering solutions.
In addition, Tech Mahindra is a member of the AWS Managed Service Provider (MSP) and AWS Well-Architected Partner Programs.
Project Scope and Background
The scope of this project included a migration and transformation journey for a European telecom provider who had their legacy non-containerized application workload running in their on-premises data center.
The IT Service Management (ITSM) solution within the customer’s organization runs on two separate BMC Remedy instances with different processes for two different business units, network domain and IT domain, in their on-premises data center.
The customer wanted to achieve the following objectives:
- Bring best-in-class security services to host the ITSM solution in public cloud.
- Fulfill their client’s cyber security control and GDPR-compliance requirements to host in public cloud.
- Unified enterprise service management platform for network, IT operations, and other lines of business.
- Protect the customer’s personally identifiable information (PII).
High-Level Solution Overview
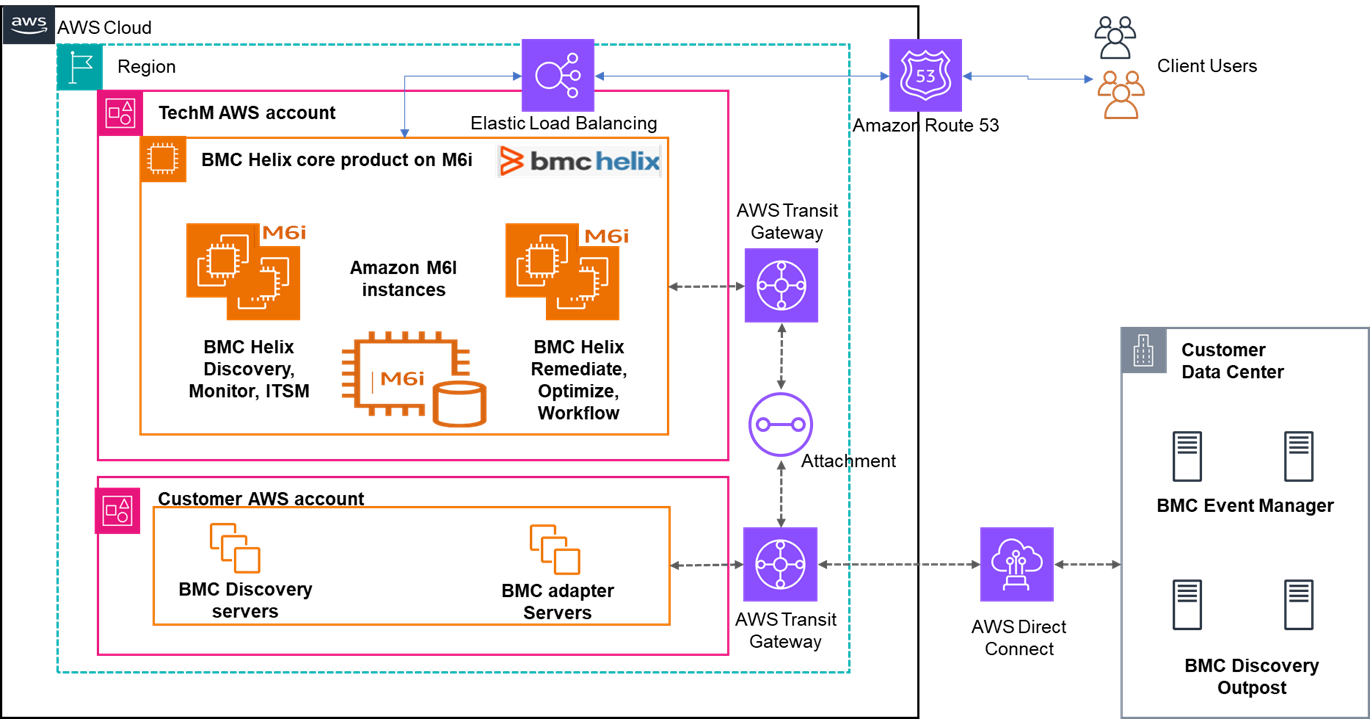
The following deployment architecture diagram depicts how the BMC Helix Core Platform and its related components are leveraged by the customer to merge their distributed legacy ITSM instances to one digital platform combining different process technologies.
The BMC Helix ITSM was hosted in Tech Mahindra’s AWS Landing Zone and integrated with multiple spoke accounts in the customer’s Landing Zone and on-premises location.
Figure 1 – AWS deployment architecture for BMC Helix platform.
Tech Mahindra leveraged AWS Well-Architected tools and best practices to migrate from a monolithic architecture to a microservice architecture on AWS, helping the customer achieve highly available and secure platform.
To handle the customer’s PII data on the public cloud, Tech Mahindra proposed to deploy BMC Helix workloads into an AWS Nitro-based instance to meet the customer’s cyber security control.
Im addition to handling PII data, the customer also required protection of content from cloud operators and from AWS system software. These requirements are met by Nitro-based instances which meet the customer’s cyber security control objectives.
The nature of compute and memory requirements are high for the BMC Helix ITSM, and Tech Mahindra identified the Amazon EC2 M6i instances are the best fit to run critical BMC Helix workloads.
To adopt microservice deployment and align with BMC Helix product requirements, the self-managed kOps platform was proposed as it supports running scalable workloads on AWS, with multiple nodes distributed across three AWS Availability Z0nes (AZs). It would also reduce operational overhead in managing a distributed environment.
This post focuses on how to secure the environment deployed with BMC Helix on AWS.
Self-Managed Amazon Kubernetes Platform Using kOps
The self-managed Kubernetes platform enables the organization to provision and manage their Kubernetes workloads on AWS using kOps with end-to-end encryption. The goal is to adhere to clients’ security requirements and ensure any application handling PII data is protecting data at all times.
Tech Mahindra designed principles to deploy the M6i servers and services across three AZs to ensure the high availability of the BMC platform delivered on all three layers (frontend, application, and backend layers).
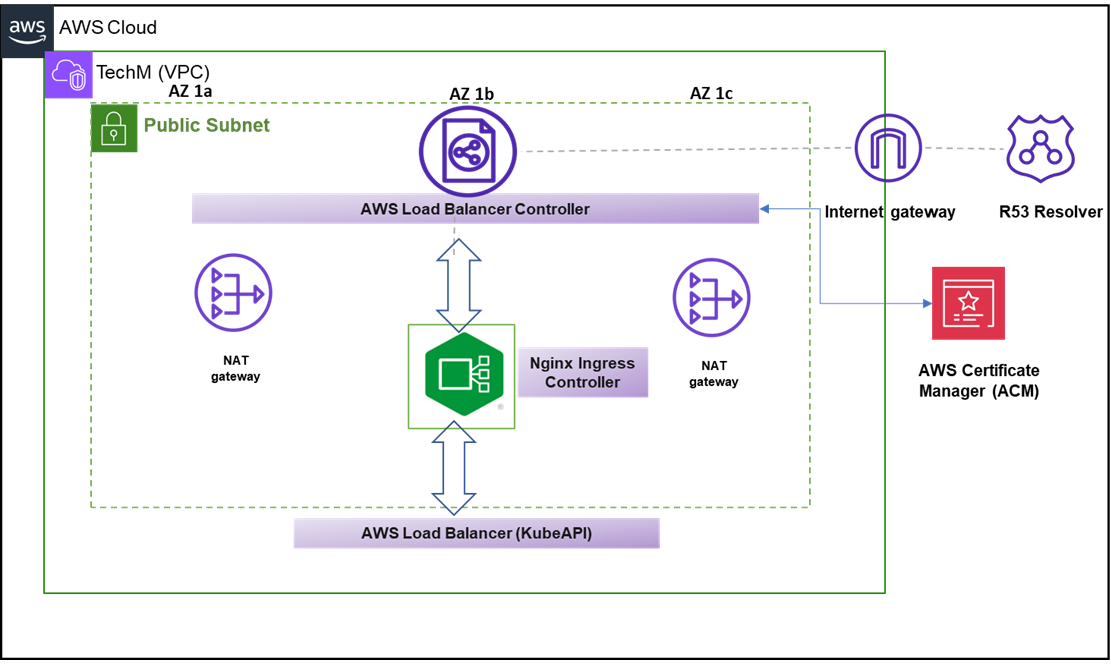
Figure 2 – Frontend layer and key services.
The web layer uses AWS Load Balancer Controller to deploy NGINX ingress controller for application using load balancing for compatibility with kOps and HTTP headers and redirection support.
Data encryption-in-transit is enabled through importing trusted third-party SSL certificates using AWS Certificate Manager to ensure data is protected while it’s being transmitted over the network.
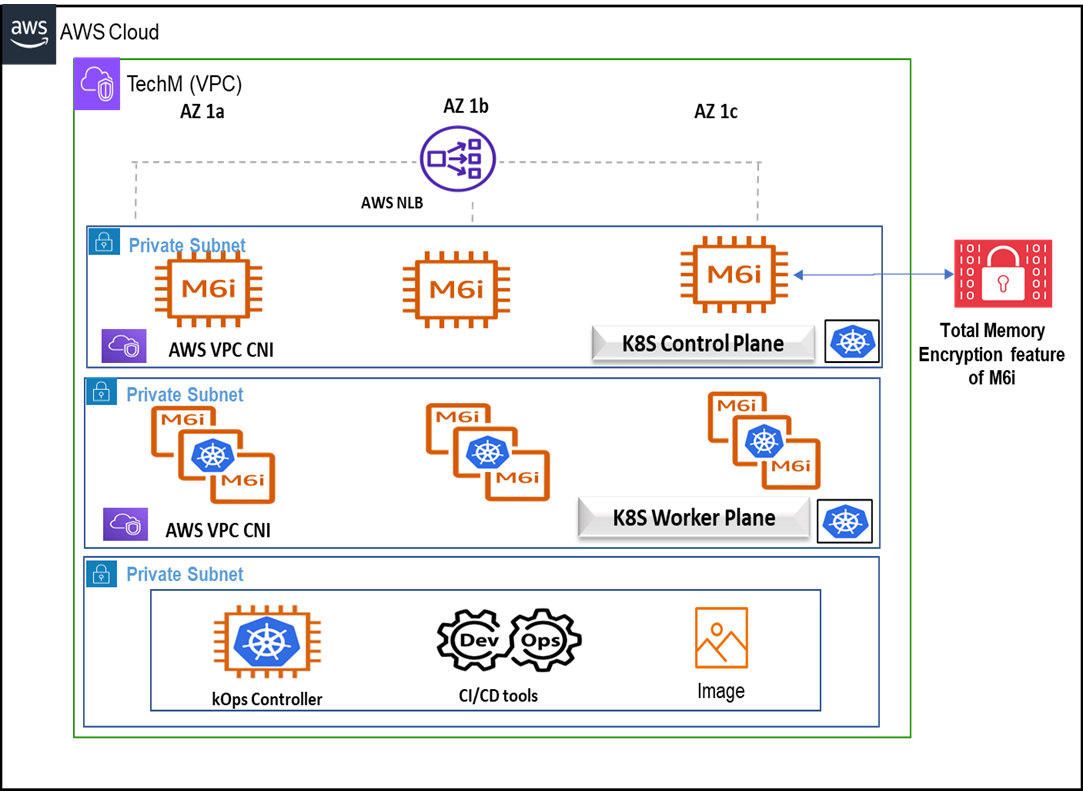
Figure 3 – Core application layer and Kubernetes platform and key services.
The application layer uses a fleet of Amazon EC2 M6i instances to host the Kubernetes control and data plane. The kOps cluster is provisioned using the kOps controller node and other DevOps tools to host the BMC Helix ITSM application.
Using the confidential compute M6i instance ensure application layer data processing is encrypted successfully with the total memory encryption (TME) feature.
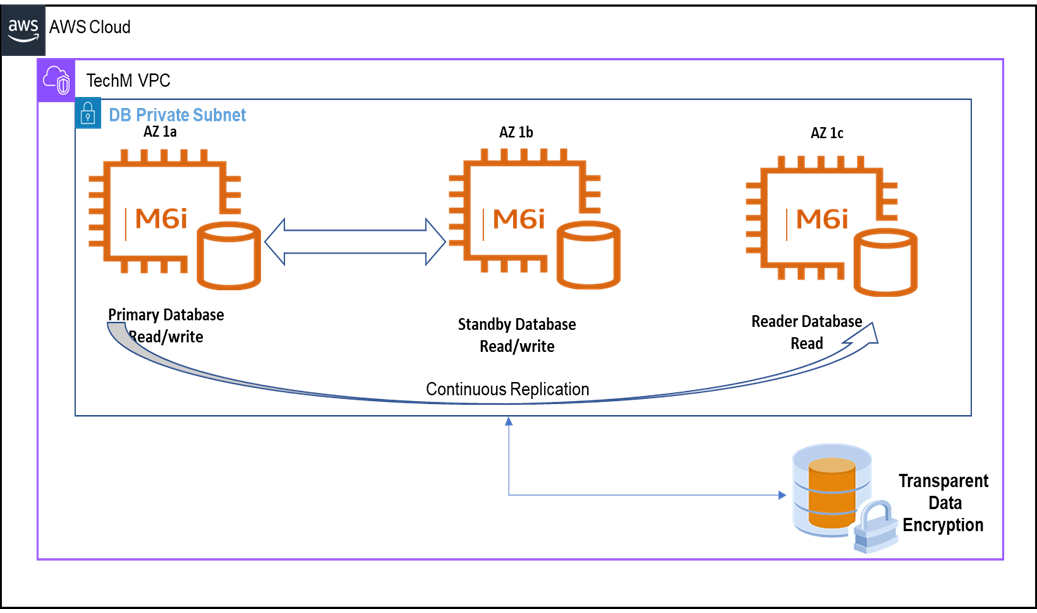
Figure 4 – Backend or database layer and key services.
The high availability of the database layer is achieved through standby database in a different AZ, as well as continuous replication to offload read operations to the reader database. It ensures the system runs smoothly and efficiently.
In addition, the database boasts state-of-the-art data encryption capabilities. Transparent data encryption (TDE) was enabled to encrypt the data stored in the database.
End-to-End Encryption Strategy in AWS
Data security at multiple layers ensures sensitive data is protected and only accessible by authorized personal.
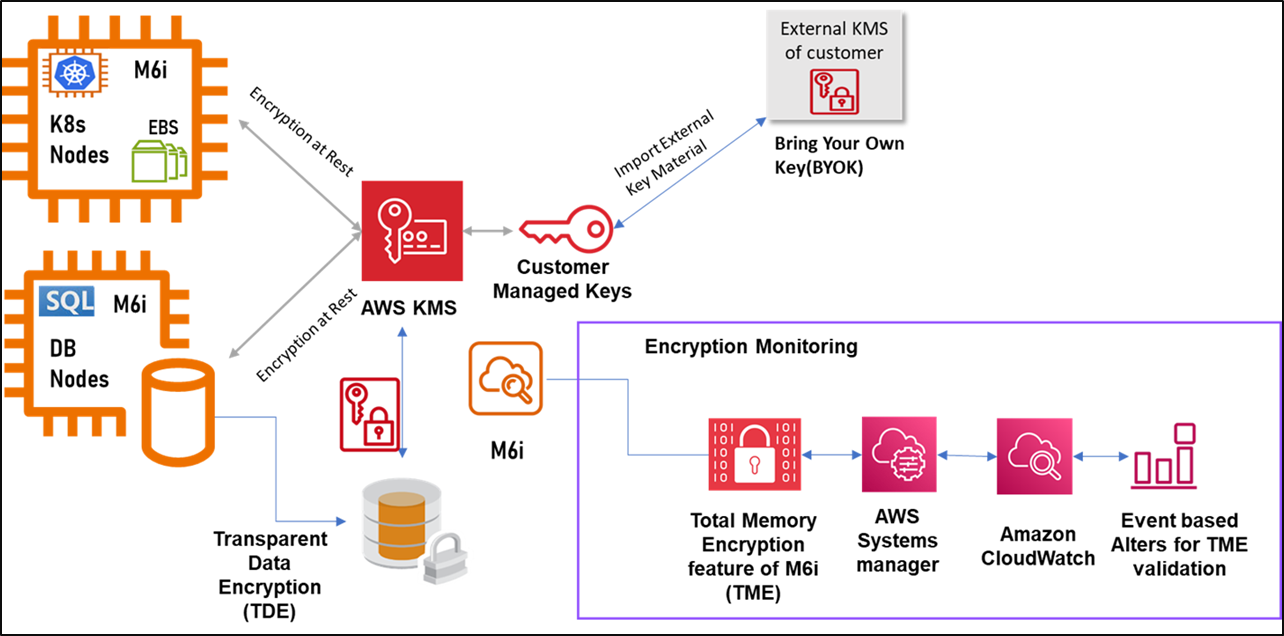
Figure 5 – Confidential computing strategy and related AWS components details.
Encryption-at-Rest
Amazon Elastic Block Store (Amazon EBS) provides a feature that enables users to encrypt their EBS volumes using their own keys stored in AWS Key Management Service (AWS KMS) known as Bring Your Own Key (BYOK) encryption. This allows customers to maintain complete control over their encryption keys while using the security and scalability of AWS KMS.
BYOK allows users to create and manage AWS KMS customer master keys (CMKs) to encrypt and decrypt EBS volumes. These CMKs are imported from an external key management system using KMS Custom Key Store.
By using BYOK encryption with EBS volumes, Tech Mahindra’s customer has benefited from the flexibility and control of managing their own keys, while still using the security and scalability of AWS KMS. This feature helped customer ensure their data is protected while it’s at-rest in EBS.
Encryption-in-Transit
By using encryption-in-transit, users can help ensure their data is protected while it’s being transmitted over the network.
To use encryption-in-transit, configured the Secure Socket Layer (SSL) or TLS protocol for the applications running on Amazon Elastic Compute Cloud (Amazon EC2) instances.
Trusted SSL certificates are procured from external vendors to enable the in-transit encryption with frontend load balancers which supports HTTPs or TLS protocols and use of SSL certificates along with AWS-supported ciphers.
M6i Encryption Monitoring
To ensure the M6i instance are deployed in the environment, a seamless monitor solution is enabled on AWS. The solution was delivered through AWS Systems Manager and its run command, which automates the validation of the TME feature on the M6i systems.
This has been enabled using the bash shell script and performs regular validation, and the results are captured using the Amazon CloudWatch event trigger and promptly reported via Amazon Simple Notification Service (Amazon SNS).
Standardized Kubernetes Deployment Using kOps
The architecture includes the following key components:
- Self-managed Kubernetes control plane: A Kubernetes control plane managed by kOps runs inside an Amazon Virtual Private Cloud (VPC) and is designed to eliminate any single points of failure that may compromise the availability and durability of the control plane.
- Self-managed Kubernetes worker node: Compute capacity to run the application workload was provisioned using an kOps-managed node group, which helps to automate the provisioning and lifecycle management of the data plane.
- Cluster autoscaler: The cluster autoscaler solution was implemented to ensure the Kubernetes cluster has the required numbers of nodes to run application workloads. The cluster autoscaler helps to monitor nodes for optimal utilization and application pods for any failure.
- Persistent volume: The application workload running on Kubernetes required data persistence. Amazon EBS was defined as storage classes for persistent volume claims. The EBS container storage interface (CSI) driver was configured to allow Kubernetes clusters to manage the lifecycle of EBS volumes for persistent volumes.
- Networking:
- VPC and subnet: The kOps cluster was deployed in one AWS region in a VPC with subnet across AZs. Nodes and control plane communication was established with network interfaces in the subnet. The kOps-managed instance groups are associated with security groups to allow all traffic between the control plane and worker nodes. All the node group’s security groups must have an inbound rule to allow traffic from the source master nodes and KubeAPI load balancer security group.
- POD networking: Amazon VPC CNI was selected for POD networking to address the effective use of IPs for customer. This provides the capability to use the private pool of IPs allocated to the subnets for high-performance scalable pod networking. Users can choose multiple subnets to provide high availability to the cluster spanning across multiple AZs.
- Load balancing with NGINX ingress controller: Kubernetes ingress is an API object that provides a collection of routing rules that govern users access Kubernetes services running in a cluster. NGINX ingress controller was deployed to listen to all of the ingress events from the namespaces and add corresponding directives and rules into the NGINX configuration file. This made it possible to use a centralized routing file which includes the ingress rules, hosts, and paths. With the NGINX ingress controller, multiple ingress objects were available for multiple environments or namespaces with the same Elastic Load Balancer and frontend ingress controller.
- Cluster authentication: kOps uses AWS Identity and Access Management (IAM) to provide authentication to the Kubernetes cluster for authentication and relies on native Kubernetes role-based access control (RBAC) for authorization. All permissions for interacting with your kOps cluster’s Kubernetes API is managed through the native Kubernetes RBAC system.
- Logging and monitoring: Amazon CloudWatch is leveraged for logging and monitoring. The node-level metrics are captured, and logs are collected to send to CloudWatch log streams using the AWS unified CloudWatch agent.
Customer Benefits
- One-stop solution for merging different IT service business units (network, IT operations, and other lines of businesses) by adopting AWS.
- Seamless migration from monolith legacy systems to microservices implementation provided as a software-as-a-service (SaaS) platform with ITSM suite running on AWS. Standardized Kubernetes deployment running on multi-node latest generation EC2 instances across multiple environments following AWS best practices and the customer’s data compliance and security standards.
- End-to-end data encryption capability at multiple layers such as data encryption at rest, transparent data encryption, and data encryption in-transit and validation/monitoring the encryption state by leveraging AWS services.
- Integration of external key management service with AWS KMS BYOK feature helped customer meet GDPR regulatory compliance requirements and ensured secure keys are always protected.
- Increased reliability and scalability as compared to on-premises data center.
- Reduced operational overhead, cost, and risk associated with managing legacy applications with high volume of change management tickets and integrations.
Conclusion
Customers running workloads in a monolithic fashion in their on-premises environment have been challenged with IT service business domains complexity, lack of scalability, lack of resiliency, operational overhead, and high cost.
With Tech Mahindra’s expert guidance, customers can leverage the benefits of the AWS Cloud and transition their on-premises legacy applications into AWS self-managed Kubernetes in the multi-stage migration approach with the implementation of end-to-end encryption.
Tech Mahindra – AWS Partner Spotlight
Tech Mahindra is an AWS Premier Tier Services Partner and MSP that specializes in digital transformation, consulting, and business re-engineering solutions.