AWS Partner Network (APN) Blog
How TCS Cloud Exponence Monitors Security and Compliance Across AWS Accounts
By Ganesh Sivakumar, Cloud Solution Architect at TCS
By Kalanithi Maran, Cloud Automation Lead at TCS
 |
| TCS |
 |
The move to primarily cloud-based operations has pushed enterprises to prioritize digital security mechanisms and regulatory compliance controls to safeguard weaknesses and reduce effects of an attack.
TCS Cloud Exponence is a multi-cloud operations solution with a focus on a range of critical security operations such as cloud perimeter monitoring, patch management, vulnerability assessment, compliance monitoring, alerting, and reporting.
Tata Consultancy Services (TCS) is an AWS Premier Consulting Partner and Managed Service Provider (MSP). TCS is an IT services, consulting, and business solutions organization that has been partnering with many of the world’s largest businesses in their transformation journeys for the last 50 years.
In this post, we will describe the steps for adopting TCS Cloud Exponence as a centralized mechanism for security and compliance monitoring and visualization across AWS environments that use AWS Security Hub.
The Security Challenge
Implementing cloud security controls and meeting compliance requirements means targeting zero loss of data, protecting against associated transfer risks, ensuring rightful access, and preventing breaches.
Once such controls have been implemented, organizations need a streamlined process to centrally manage security events/alerts and efficiently view how the tools perform with a business-aware dashboard.
Organizations spend a lot of their efforts assessing security controls and determining the right combination of tools and processes to support an array of activities.
This includes access controls, intrusion prevention and detection, patch management, vulnerability management, anti-malware, network security, and much more.
Many companies now find they need to comply with the complexities of data privacy and other statutory regulations, while also aligning the monitoring of these controls for decision support and business insights.
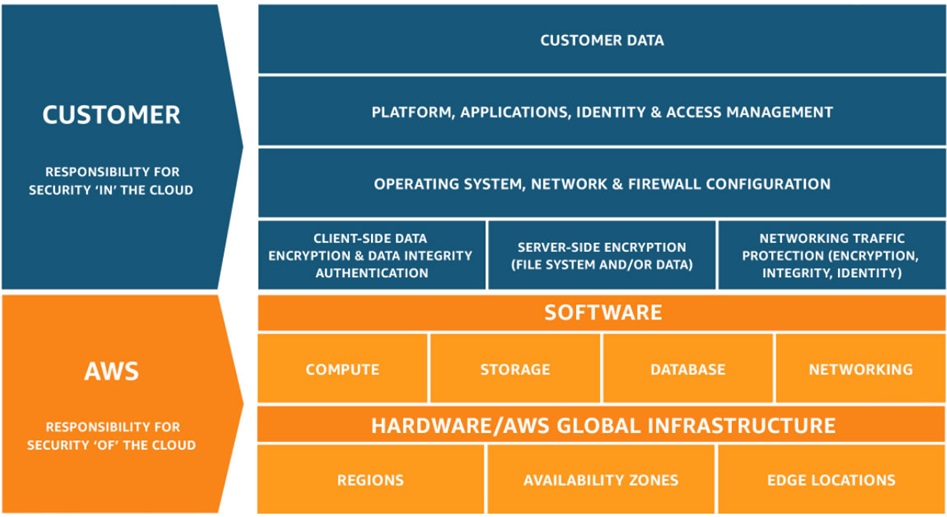
AWS Shared Responsibility Model
Security and compliance is an area of shared responsibility between AWS and the customer.
The AWS Shared Responsibility Model helps relieve a customer’s operational burden because AWS operates, manages, and controls the components from the host operating system and virtualization layer down to the physical security of the facilities in which the service operates.
The customer assumes responsibility and management of data/network security controls and encryption, guest operating systems (including updates and security patches), application software, environment and application access, and security controls.
The nature of this shared responsibility also provides the flexibility and customer control that permits the deployment. As shown in Figure 1, this differentiation of responsibility is commonly referred to as security “of” the cloud versus security “in” the cloud.
Figure 1 – AWS Shared Responsibility Model.
Cloud Security Controls
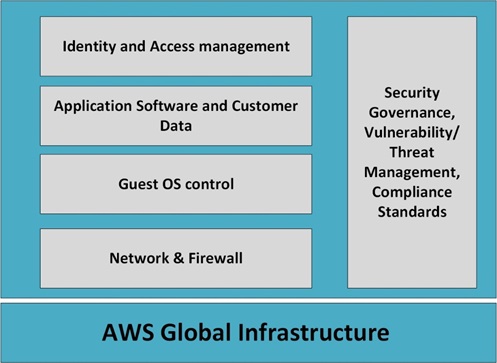
In the AWS security governance model, security controls need to be addressed at multiple levels:
- Perimeter and network security.
- Operating system and middleware.
- Application and data security.
- Identity and access control.
- Governance policy across all the levels.
To ensure customer and regulatory requirements for security and compliance standards are met, individual AWS services are equipped with standardized, robust security and monitoring mechanisms.
This approach provides centralized configuration, and congruent visibility of security and compliance controls, across all applications and environments.
Figure 2 – AWS security governance model.
When solution-, industry-, or geography-specific requirements for compliance and security controls are present, consistency and visibility of controls and activity becomes more critical to effective operations.
Apart from consistency and auditability of security controls, continuous monitoring of environments with timely reporting and alerting minimizes the impacts of security events and enables feedback-driven mitigation measures to be rolled out to prevent the recurrence of similar issues.
AWS Security Tools
To help customers meet these critical security and compliance requirements, AWS provides several tools and technologies. Three are worth highlighting.
AWS Security Hub
AWS Security Hub provides a comprehensive view of high-priority security alerts and compliance status across AWS accounts to help you aggregate and prioritize security and compliance findings.
AWS Security Hub aggregates findings from other AWS services like Amazon GuardDuty, Amazon Macie, Amazon Inspector, as well as security solutions from APN Partners. It also gives you a summarized view of security issues and compliance status.
AWS Security Hub does compliance checks based on industry standards such as the Center for Internet Security (CIS) AWS Foundations Benchmark, which complements various security standards such as HIPAA, GDPR, FISMA, and others.
AWS Config
AWS Config enables us to assess, audit, and evaluate the configurations of AWS resources. With AWS Config, we can review changes in configurations and relationships between AWS resources and determine overall compliance against the configurations specified as per guidelines.
AWS Systems Manager
AWS Systems Manager provides a view of operational data across multiple AWS services, and automates operational tasks across your AWS and on-premises resources.
Systems Manager helps you maintain security and compliance by scanning managed instances and reporting on any policy violations it detects, and automating corrective actions through integration with AWS Config.
How TCS Cloud Exponence Uses AWS Security Tools
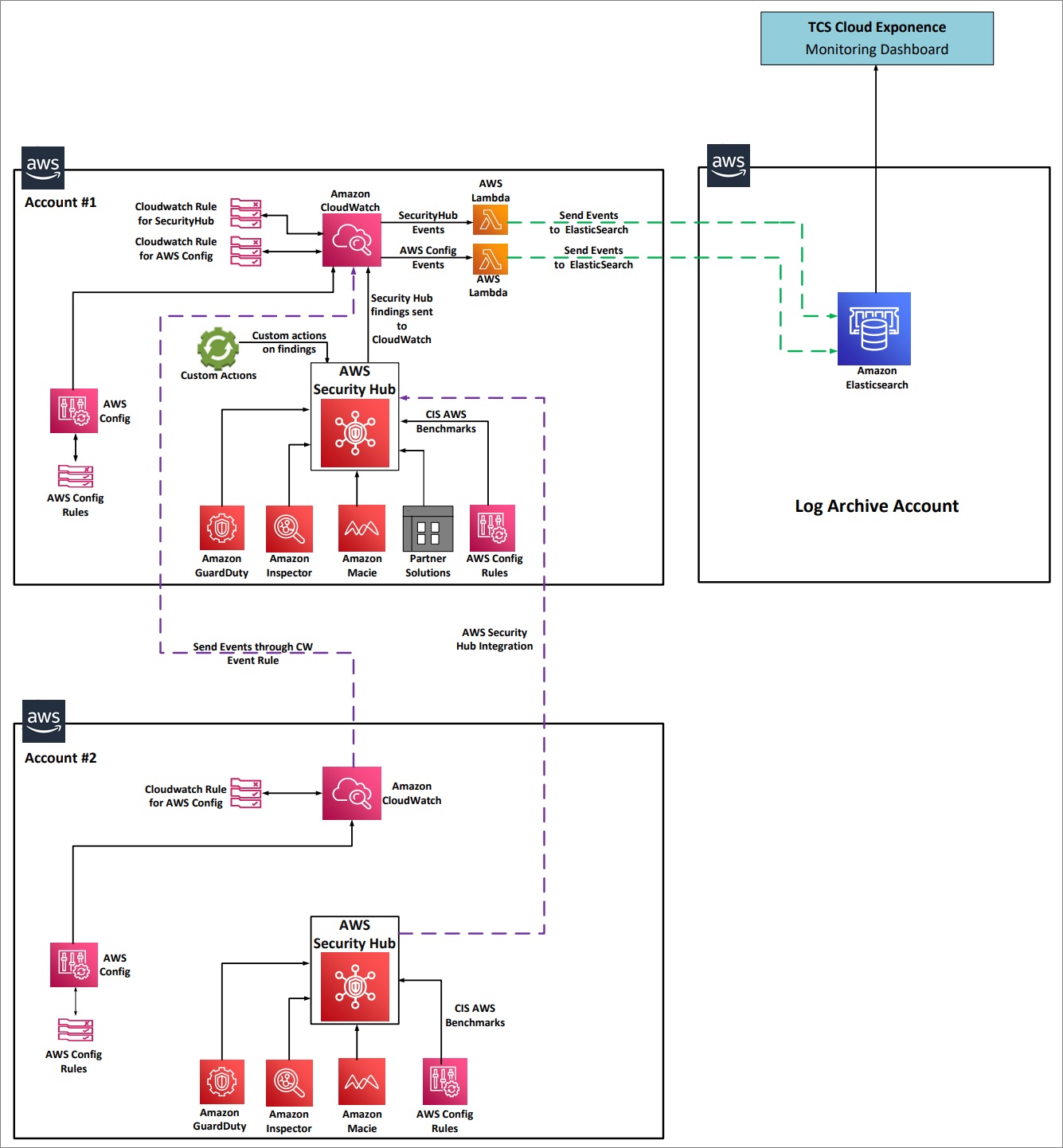
Considering the importance of security and compliance monitoring, TCS has used AWS Security Hub and AWS Config as the basis for the security monitoring and visualization capabilities in TCS Cloud Exponence.
Our security capabilities enable security analysts to readily understand the state of security and compliance across their AWS environments.
The following architecture illustrates how AWS Security Hub and AWS Config are integrated across multiple accounts, aggregate the logs to a Log Archive Account, and visualize security status in TCS Cloud Exponence.
Figure 3 – Security and compliance dashboard architecture.
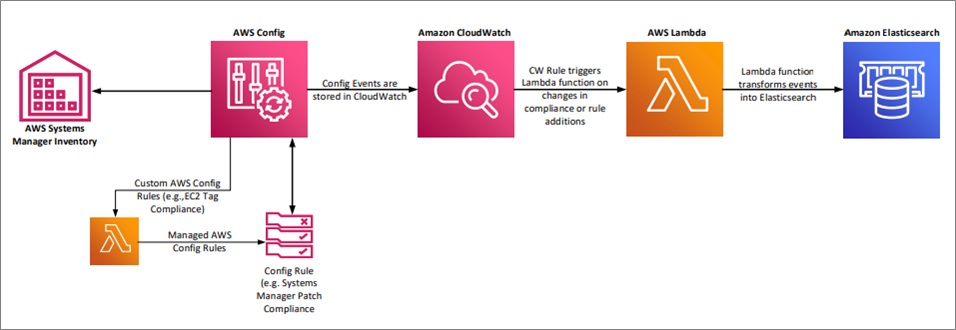
Although AWS Config includes a powerful predefined rule set, its extensible nature allows enterprises to define customized security and compliance rules to get advanced insights, as shown in Figure 4.
Figure 4 – AWS Config for compliance check.
In case of any breach in security, both AWS Security Hub and AWS Config can be used to alert by sending findings to a ticketing system, chat, email, or other messaging platform. AWS Security Hub and AWS Config also provide summarized views in their respective dashboards.
Amazon OpenSearch Service (successor to Amazon Elasticsearch Service) aggregates the data from AWS Security Hub and AWS Config, which helps with data management. During deployment, you will configure TCS Cloud Exponence to visualize the data collected from OpenSearch.
Deploying TCS Cloud Exponence
Follow these steps, using the preceding architecture in Figure 3 as a guide.
Step 1: Set up two AWS accounts with these components:
Optional security or compliance packages such as Amazon GuardDuty, Amazon Inspector, or solutions from APN Partners configured to meet CIS Benchmarks for AWS.
Step 2. Configure the primary AWS Security Hub account
Configure one of the AWS accounts as the primary AWS Security Hub account. This is Account #1 in Figure 3.
Step 3: Create Log Archival account for Amazon CloudWatch
Create a separate AWS account to collect and maintain the security event logs for CloudWatch. Keeping this information in its own, separate account makes it easier to restrict access to authorized personnel only.
Configure the account in this way:
- Within that account, set up an Amazon OpenSearch Service domain to index the event data coming from the primary account.
- Configure the access policies in the OpenSearch domain so that only trusted users and applications can access them.
- Create trust identity between the Log Archival account and other accounts, along with a restricted AWS Identity and Access Management (IAM) policy, so the events are not accessed by any other users or services.
- Configure OpenSearch with public access so the AWS Lambda functions can send their event data to index. If you have a huge number of data or security accounts to process, you can also use Amazon Kinesis Data Firehose to avoid losing any data.
Step 4: Write Amazon CloudWatch Event Rules
In each of the two main accounts, write CloudWatch Event Rules to identify when a security event from either AWS Security Hub or AWS Config has occurred.
- In the secondary account, have the event rules send details about the security event to CloudWatch in the primary account.
- In the primary account, have the event rules, whether from the primary or secondary account, trigger a Lambda function to forward details about the security event to Amazon ES in the Log Archive account.
Step 5: Configure TCS Cloud Exponence
Configure TCS Cloud Exponence to collect security events and compliance data from Amazon OpenSearch Service and present it visually on its dashboard.
Figure 5 – TCS Cloud Exponence monitoring dashboard.
As shown in the preceding Figure 5, we have collected events from AWS Security Hub to provide a dashboard for CIS compliance status and threat detection from Amazon GuardDuty events.
We can also create customized policy through AWS Config, and monitor the status through TCS Cloud Exponence. Apart from Monitoring, TCS Cloud Exponence also manages alerts and creates ITSM tickets based on severity.
Summary
Setting up AWS security tools and services to feed security and compliance alerts to TCS Cloud Exponence allows you to examine cross-domain data in a single, comprehensive dashboard. This reduces the complexity of securing your cloud environment and ensure it remains compliant.
The content and opinions in this blog are those of the third party author and AWS is not responsible for the content or accuracy of this post.
Tata Consultancy Services (TCS) – AWS Partner Spotlight
TCS is an AWS Premier Consulting Partner and Managed Service Provider (MSP). An IT services, consulting, and business solutions organization, TCS has been partnering with many of the world’s largest businesses in their transformation journeys for the last 50 years.
Contact TCS | Practice Overview
*Already worked with TCS? Rate this Partner
*To review an AWS Partner, you must be a customer that has worked with them directly on a project.