AWS for M&E Blog
Secure media delivery at the edge on AWS
Amazon Web Services (AWS) provides solutions for media distribution from encoding, packaging, and encryption using AWS Media Services, and broad distribution using the Amazon CloudFront content distribution network (CDN) for improved performance reaching the largest audiences. With the Secure Media Delivery at the Edge on AWS solution, customers can now add an easy-to-use and commonly supported solution to protect high-value live and on-demand content.
Protecting video assets from unauthorized use is key for media customers, as video subscriptions and purchases are a large part of the business. In a subscription-based delivery model, access by non-subscribed viewers to premium content translates into loss of revenue as well as increased costs to serve traffic to unauthorized viewers. In addition, many content owners dictate specific security requirements as part of the agreement to carry their assets (such as geo restrictions, tokenization, and other restrictions).
Token-based access is one of the more common approaches used as the first layer of content protection. It is based on the generation of cryptographically signed tokens scoped to a specific video asset and issued to individual viewers using viewer-specific attributes (for example, source IP address, geo location, browser attributes). In order to access the requested content, a client must attach a valid token to each request that is validated before access is granted. When content is distributed through a CDN like CloudFront, the token validation occurs at the edge by a supported mechanism.
Designing and implementing robust token-based controls for media workloads pose unique challenges in finding effective solutions with broad support. Many existing solutions require cookies, query string parameters, or specific headers in order to function properly. While cookies and custom headers are viable options for websites and apps, some clients block cookies when playing back media and some low-cost set-top boxes don’t support cookies at all. Also, some video services must operate over multiple domain names (serving the manifest, segments, and ads from various domain names), further increasing complexity. Another alternative approach commonly used is signed URLs carrying the token payload in query string parameters. This requires the use of an additional element between the video origin and the CloudFront caching layers continuously appending individual tokens to the manifest. This creates additional scaling considerations, decreasing cache hit ratio, and requires careful parsing and modification of the manifests.
Media consumption operates on a higher scale than other applications, so traditional solutions relying on external permission validation systems have proven problematic compared to those designed specifically for media where validation occurs within the CDN itself. The ideal solution should provide customizations needed by a variety of customers where token structure can be adjusted dynamically and extended as needed using standards-based claims. Also, customers want to enhance their capabilities to respond to an identified source of stream redistribution with the ability to monitor usage and even revoke tokens mid-stream, ceasing playback in the case tokens where leaked and reused.
Secure Media Delivery at the Edge on AWS is designed to address these challenges as a comprehensive implementation of an end-to-end token-based access control workflow that allows only authorized viewers access to content and serves to mitigate pervasive online piracy threats. The solution scales to hundreds of thousands of concurrent viewers with a low incremental cost, which is made possible with CloudFront Functions, the most scalable and lightweight runtime available on CloudFront. While the solution requires minimal effort to integrate into an existing video delivery workflow, it offers the flexibility for advanced customers and AWS Partners to adjust it to unique content restriction requirements or extend it as needed.
This solution is compatible with and has been tested all major AWS and third party origins.
Secure Media Delivery at the Edge on AWS is intended to improve CloudFront-based media workloads, preventing link sharing and designed to allow only authorized users to consume specific content during the time allotted. It also offers additional (optional) modules allowing for revocation of permissions if authorized playback sessions were compromised as a result of piracy.
Optional layered security may be added in the form of digital rights management (DRM) through the use of AWS Elemental MediaPackage. For more information, refer to the content encryption and DRM in MediaPackage documentation.
Architecture
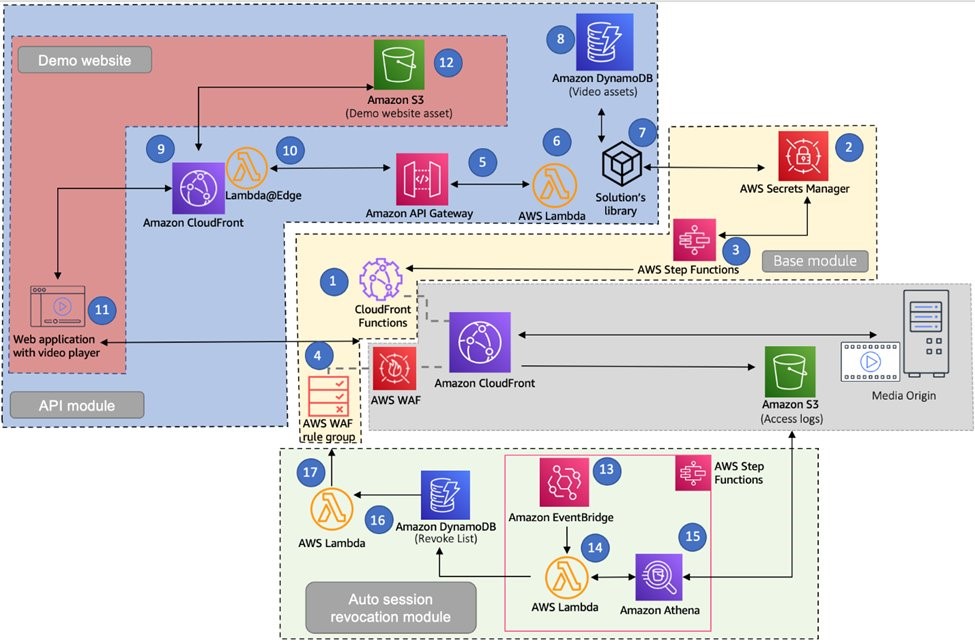
Secure media stream delivery is designed using a modular architecture, allowing either individual components to be deployed or the entire solution. You may choose to deploy the base module with only the token validation function and key management elements or to implement the entire workflow as depicted in the following diagram. Each component may be edited as needed by developers to add customizations. The solution serves as an incremental layer of protection to pre-existing video streaming distribution pipelines using CloudFront. The gray section in the following diagram represents components that should already exist before the solution is deployed. The media origin server is a source hosting the video content fronted with a CloudFront distribution for delivery. If the auto session revocation module is used, the ‘enable the CloudFront access logs’ option must be used.
Base module
The base module includes the AWS CloudFront Function required to validate secure tokens, permitting or denying access to media content. The function code is produced when the solution stack is deployed and the respective function is associated with the cache behaviors where token validation occurs.
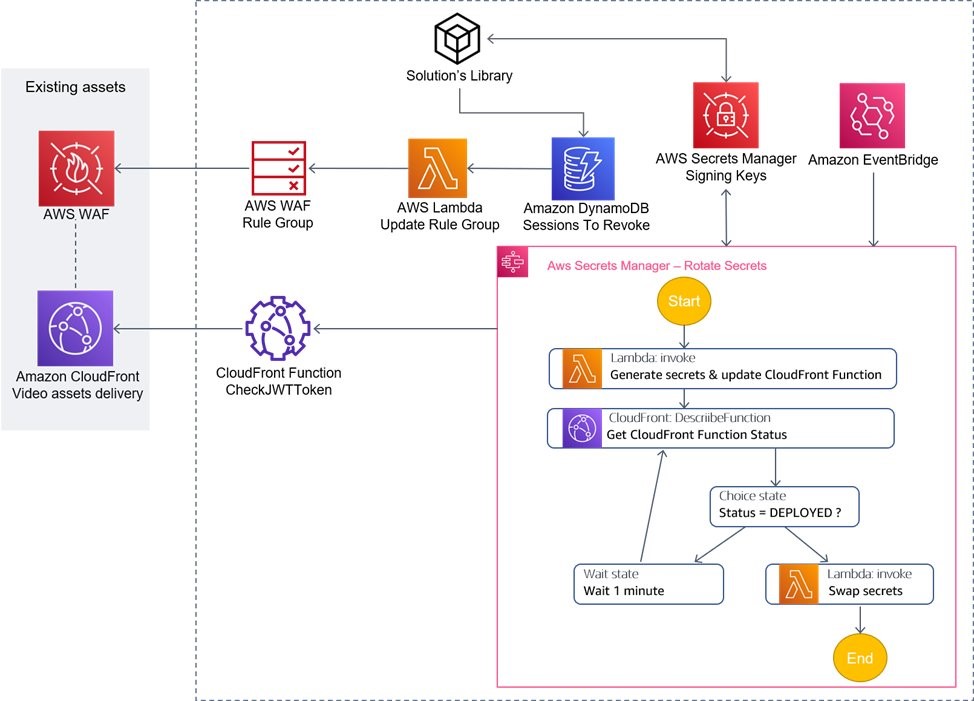
Along with the function, the base module includes an AWS Secrets Manager configuration responsible for secure storage of the secret keys used for token generation and validation, rotated periodically according to a schedule.
If utilized, an AWS WAF (an web application firewall) rule group is created to block invalidated tokens. Tokens that are past the revocation period are automatically removed from the rule group, thus lowering costs. The revocation period is a configurable setting defined when deploying the solution.
In order to incorporate the token validation step, another process is required for vending the token compatible with the CloudFront Function logic. To make it as easy, the API module includes an AWS Lambda function behind Amazon API Gateway, exposing a simple process to generate new tokens. Tokens may also be generated remotely (for instance, on a content management system) using the included Node.js library. Note that the tokens are based on JWT (http://jwt.io), so you can create tokens in this format using any language supporting JWT.
Conceptually, the process of acquiring the playback URL with unique token and its validation can be presented as follows:
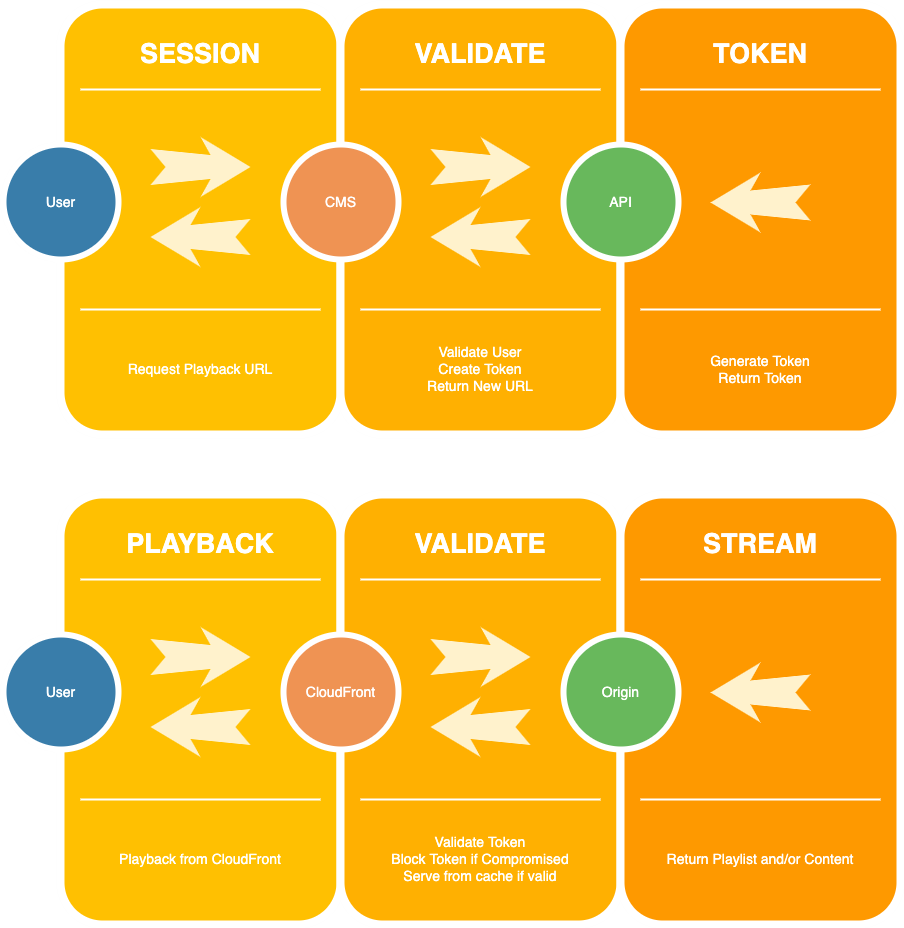
Note that this solution does not cover the viewer authorization step in the process of acquiring the playback URL with the token. You would need to integrate your own mechanism of managing the user base and their permissions to watch specific video streams.
API module
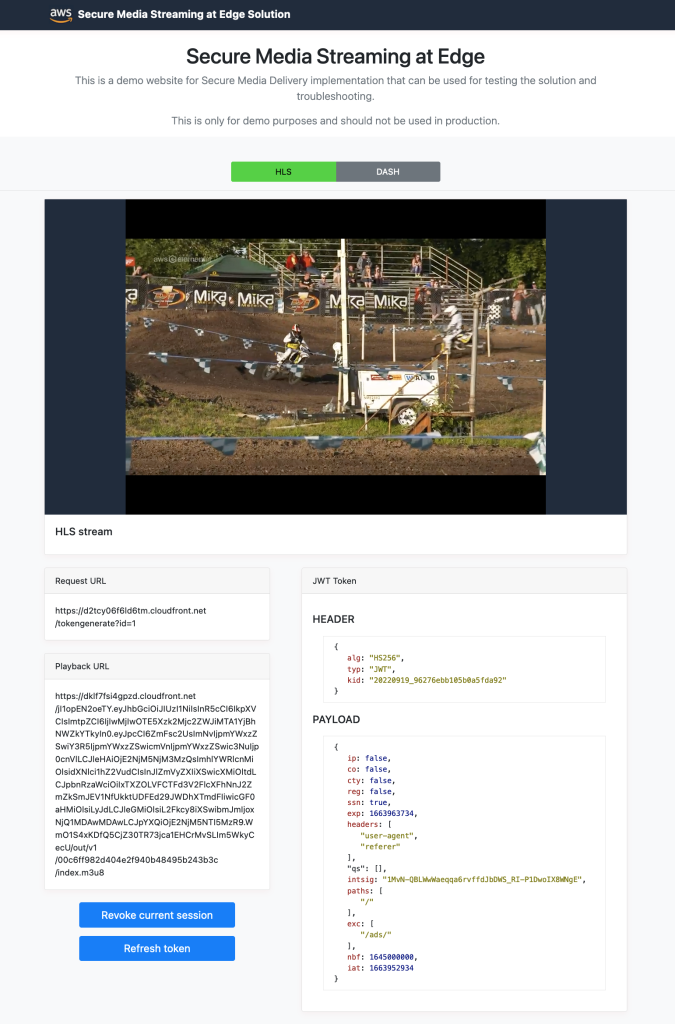
An optional API module is available that represents a simple content management system (CMS) functionality built on Amazon DynamoDB and Amazon API Gateway integrated with Lambda functions. Using this solution, customers without an existing CMS or who are just experimenting can begin use immediately. Refer to the implementation guide to review possible options to add token generation logic in your application. An optional demo website may be deployed as well to discover what a full solution would look like, making integration even easier. This demo website also helps you quickly test the solution with minimal set up efforts along with the ability to troubleshoot.
If you choose to deploy the demo website (which we recommend deactivating after launching the solution in a production environment), the solution automatically deploys an Amazon Simple Storage Service (Amazon S3) bucket for storing the static website assets and uses the same CloudFront distribution created in front of the API Gateway endpoint.

Auto session revocation module
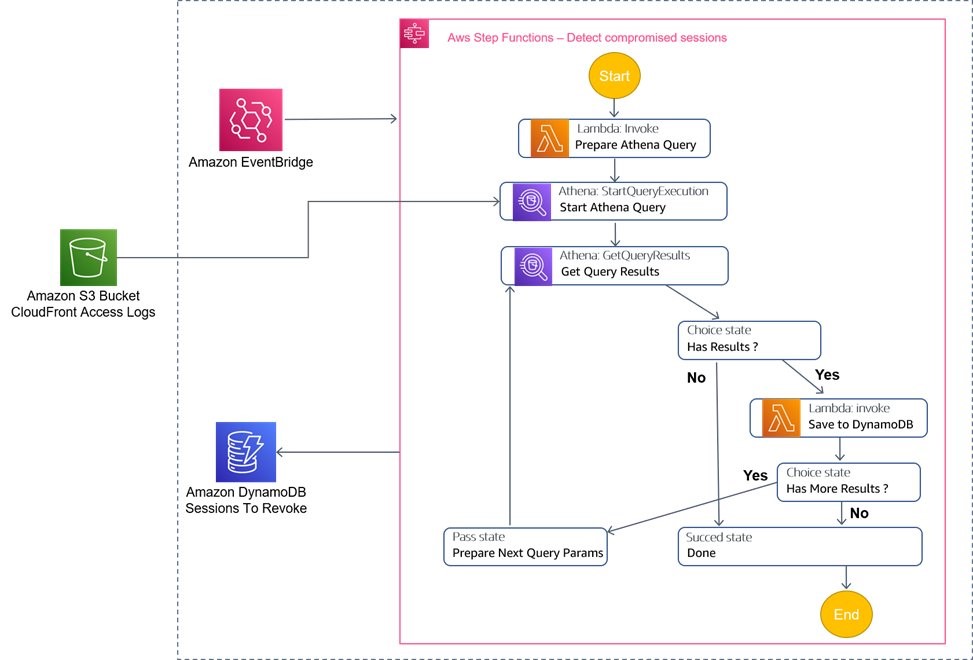
Another optional module that may be added to the solution is the auto session revocation module. If this is chosen, an Amazon EventBridge rule is run periodically (as per the configuration inputs) launching an AWS Step Functions workflow. The step function then sequentially runs predefined steps revolving around Lambda functions that query Amazon Athena for suspicious video playback activity. Amazon Athena is used as it can directly query CloudFront logs stored in an Amazon S3 bucket. Information about suspicious activity and corresponding session IDs is then published into an Amazon DynamoDB table that is used to ultimately block suspicious traffic via AWS WAF.
The auto session revocation module can only be added through AWS Cloud Development Kit (AWS CDK) deployment. You can find and download the AWS CDK app that launches the solution in the stack in the solution’s code repository. Refer to the implementation guide for more information on how to deploy the solution using AWS CDK.
Example Playback Session
How can I learn more and deploy this solution?
The implementation guide with more details can be found here:
https://docs.aws.amazon.com/solutions/latest/secure-media-delivery-at-the-edge/welcome.html
Also visit the solutions implementations page with links to the AWS CloudFormation template and code repository:
https://aws.amazon.com/solutions/implementations/secure-media-delivery-at-the-edge/
The public Github location with source code can be found here:
https://github.com/aws-solutions/secure-media-delivery-at-the-edge