AWS Partner Network (APN) Blog
Streamline Multi-Account Governance, Management, and Security with AWS Control Tower and Mphasis Stelligent
By Richard Wolf, Head of Solutions – Mphasis Stelligent
By Shilpa Tyagi, Sr. Partner Solutions Architect – AWS
 |
| Mphasis |
 |
Cloud transformation can be a large undertaking. The setup and governance of a multi-account strategy can be complex and time-consuming, slowing down the very innovation you’re trying to speed up.
Many organizations decide to implement AWS Control Tower because it provides an easy way to set up and govern a secure, multi-account Amazon Web Services (AWS) environment called a landing zone. AWS Control Tower creates your landing zone using AWS Organizations, enabling ongoing account management and governance while implementing AWS best practices.
Implementing AWS Control Tower is the first step for many large organizations, but determining the what and how of enhancing the default functionality to meet the enterprise’s needs requires additional considerations.
Mphasis Stelligent offers an AWS Control Tower-based landing zone quick start with modules for automating account access, observability, security suite enablement, deploying industry-specific guardrails, and multi-account networking. Once implemented, companies can provision secure accounts fully baselined for utilization in less than an hour.
In this post, you will learn about the core AWS solutions for empowering your organization, including AWS Control Tower. We’ll then dive into how to customize the solutions to meet your enterprise requirements at scale.
Mphasis is an AWS Premier Tier Services Partner with the AWS Control Tower service delivery specialization. Mphasis applies next-generation technology to help enterprises transform businesses by leveraging DevOps on AWS with Mphasis Stelligent. Learn more about Mphasis Stelligent on AWS Marketplace.
AWS Control Tower OUs and Guardrails
AWS Control Tower is a multi-account management and governance service provided by AWS which automates the creation of core and workload accounts with pre-configured guardrails. With a single click, you can enable this service and be on the path to having a secure multi-account environment in hours.
From an organizational unit (OU) and account perspective, AWS Control Tower deploys two OUs—one for your shared accounts and one for accounts that will be provisioned by your users. It also deploys three shared accounts, which are the management account and isolated accounts for log archive and security audit.
These OUs and accounts are the foundation for best practice patterns for both access and data point aggregation.
AWS Control Tower can help you implement preventive and detective controls as part of account baselining. The standard AWS Control Tower console orchestration implements 20 preventive controls to enforce policies and three detective controls to detect configuration violations.
Additionally, a native cloud directory with pre-configured groups and single sign-on (SSO) access is deployed, which can be integrated to identity providers (IdPs) such as Active Directory or Okta.
Guardrails are pre-configured governance rules for security, compliance, and operations. Preventive guardrails prevent policy violations through enforcement rules implemented using AWS CloudFormation and service control policies (SCPs).
These JSON files contain AWS Identity and Access Management (IAM) policies which supersede IAM permissions at the role and user level, and umbrella policies allowing you to safeguard the most critical services and configurations on AWS. A mission-critical example would be configurations pertaining to your AWS Direct Connect service.
Detective guardrails detect policy violations and are implemented using AWS Config rules. These are deployed to every account provisioned through the AWS Control Tower Account Factory, and findings are aggregated to a core account to provide holistic visibility of compliance findings.
Compliance status is displayed in a variety of locations including the AWS Control Tower dashboard, AWS Config, and AWS Security Hub console. Alerts can be triggered to send notifications when findings are non-compliant and auto-remediation is achievable with AWS Lambda functions.
Customizations for AWS Control Tower (CfCT) empower customers to extend their compliance coverage requirements seamlessly. In the next section, you’ll get a better understanding of the mechanics behind how this solution works.
Customizations for AWS Control Tower
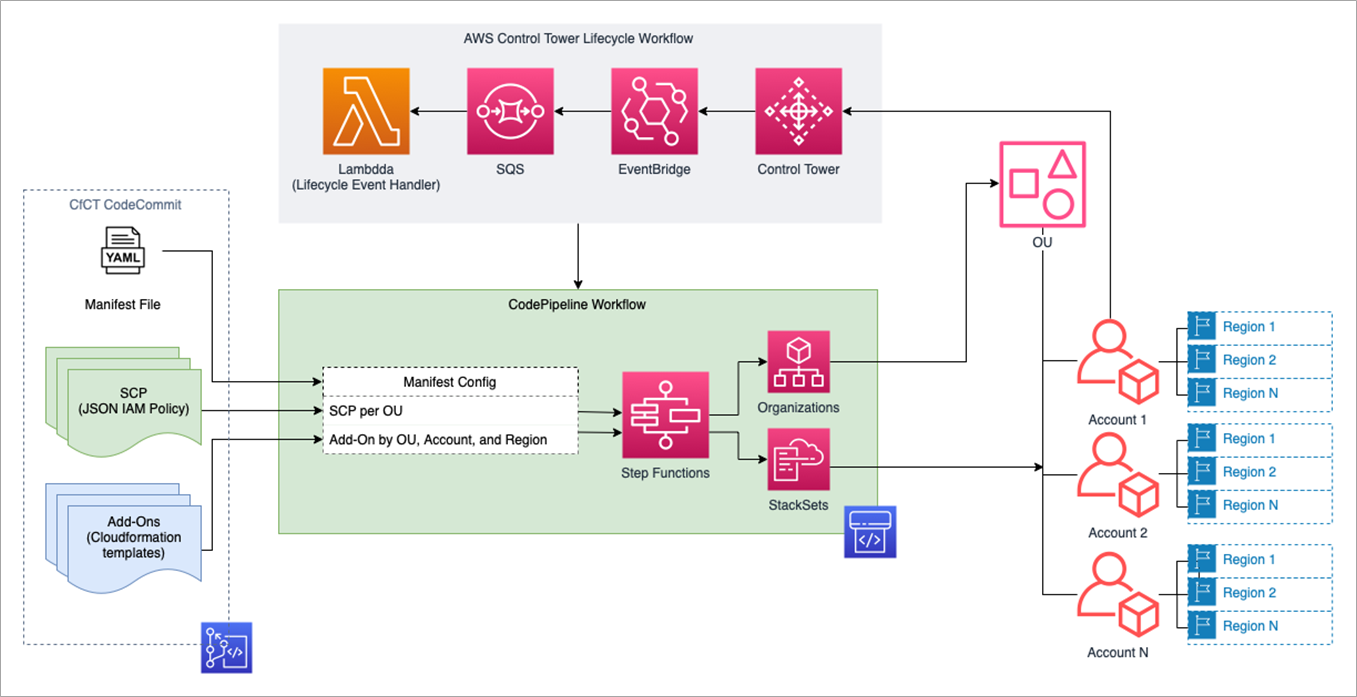
Customizations for Control Tower is an orchestration pipeline that integrates with AWS Control Tower for deploying custom account baseline and configuration requirements for advanced enterprises.
Organizations can easily add customizations to the AWS Control Tower landing zone using CloudFormation templates and SCPs. You can deploy the custom template and policies to individual accounts and OUs within your organization utilizing the manifest file.
This solution integrates with AWS Control Tower lifecycle events to ensure resource deployments stay in sync with your landing zone.
Figure 1 – Customizations for Control Tower deployment orchestration.
CfCT grants customers the ability to reduce lead time for changes to account baselines and resolve misconfiguration promptly.
Some of the benefits of CfCT include:
- Single repository and pipeline for all customizations and SCPs.
- Baseline deployment into Core and Custom Accounts.
- Templates are in CloudFormation format and align with other AWS solutions.
- Configured with YAML manifest file.
- Observability of all infrastructure as code (IaC) through the CloudFormation console.
- All logs captured in native AWS.
- Original landing zone code base.
Mphasis Stelligent has developed numerous CfCT add-on templates, and through its collaboration with AWS has developed the expertise to quickly deliver the solution with future optimizations in mind to reduce technical debt.
Enterprise OU and Foundational Account Structures
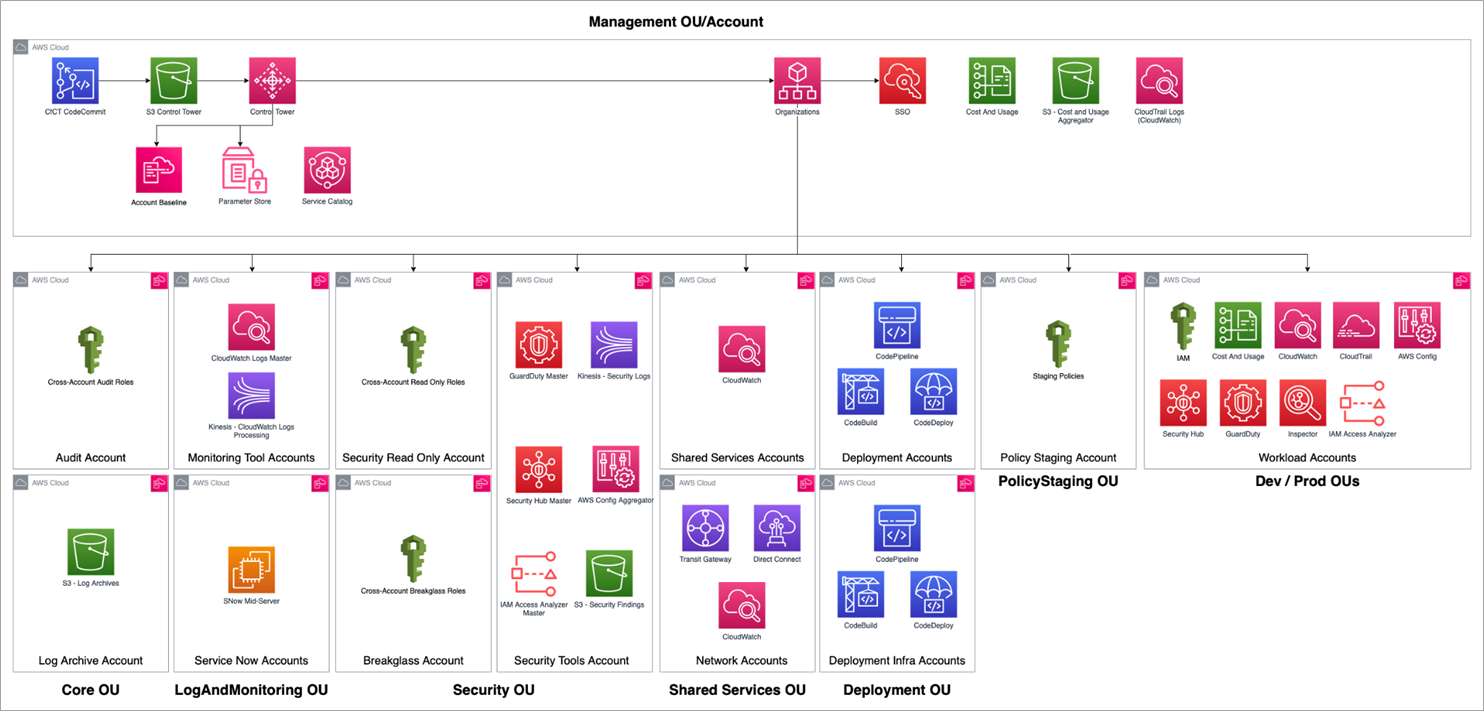
The base AWS Control Tower deployment is designed to cover basic management and governance requirements. In reality, however, highly-regulated enterprises have complex team structures, compliance, networking, security, and auditing requirements which entail significantly more complex OU and account structure to accommodate.
Some benefits of customizing your AWS Control Tower deployment include decoupling IAM access, reducing blast radius, consolidated IaC, and enabling the full suite of security and observability tools.
Figure 2 – Standard Control Tower OU and account structure.
These two diagrams show both the AWS Control Tower standard OU and account structure (Figure 2) vs. real-world enterprise deployments (Figure 3). As you can see, there are many additional core OU and accounts.
Figure 3 – Enterprise Control Tower OU and account structure.
- Monitoring tools: Hosting native and third-party solutions for your site reliability engineering (SRE) and application teams. Metric, logs, and tracing from the account and application level are aggregated here for complete visibility of all AWS accounts provisioned.
- Security accounts: Includes Security Read Only, Breakglass, Forensics, and Red Team. These accounts provide roles for security teams to investigate and resolve security findings, and in the case of a breach isolate accounts. This is achieved through assumed roles allowing access to all accounts managed by AWS Control Tower for select security team members.
- Shared services account: Shared services which are dependencies of an application are hosted here. These can range from IdP to data integrators.
- Networking account: The networking account contains AWS Transit Gateway with Direct Connect configuration to on-premises. Additionally, customers who plan to implement a centralized firewall model will have virtual private clouds (VPCs) for inspection, egress, and ingress with Transit Gateway route tables set up for best practice East-West and North-South connectivity.
- Deployment account: Contains the CI/CD tooling of choice for application builds and deployments.
- Policy staging: An account intended for testing SCP policies before moving into production environments.
With these additional OUs and accounts in place, you will have peace of mind that access to critical accounts are minimized to required team members.
Extending Preventative and Detective Guardrails
AWS Control Tower’s mandatory and elective guardrails provide a strong starting point from a horizontal coverage perspective. Every company will have its own unique industry and business-specific requirements which creates a need for custom guardrails deployments through CfCT.
Financial services, healthcare and life sciences, government, technology and media, and travel and hospitality share similar technical challenges—regulations, auditing requirements, compliance, and security stand out as top priorities.
Implementing controls for FFIEC, HIPAA, CIS, CMMC, NIST, FedRAMP, and other compliance requirements can be streamlined leveraging AWS Config managed rules.
From a high-level, AWS provides groups of detective managed rules which can be implemented to meet many of these requirements:
- AWS Control Tower: 23 mandatory preventative and detective controls.
- AWS Security Hub: 188 which can be sorted by CIS, PCI, and more.
- Conformance packs: Regulatory-specific compliance.
- Managed rules: 290+ additional managed rules for consideration.
Often, both custom AWS Config rules and SCPs need to be deployed to meet highly regulated compliance requirements.
Mphasis Stelligent has identified reusable AWS Config and SCPs based on experiences from dozens of past projects for commonly requested compliance needs. These include ensuring encryption, validating least privilege, and limiting traffic to accounts by checking security group and access control list (ACL) configurations.
Automating Account Access
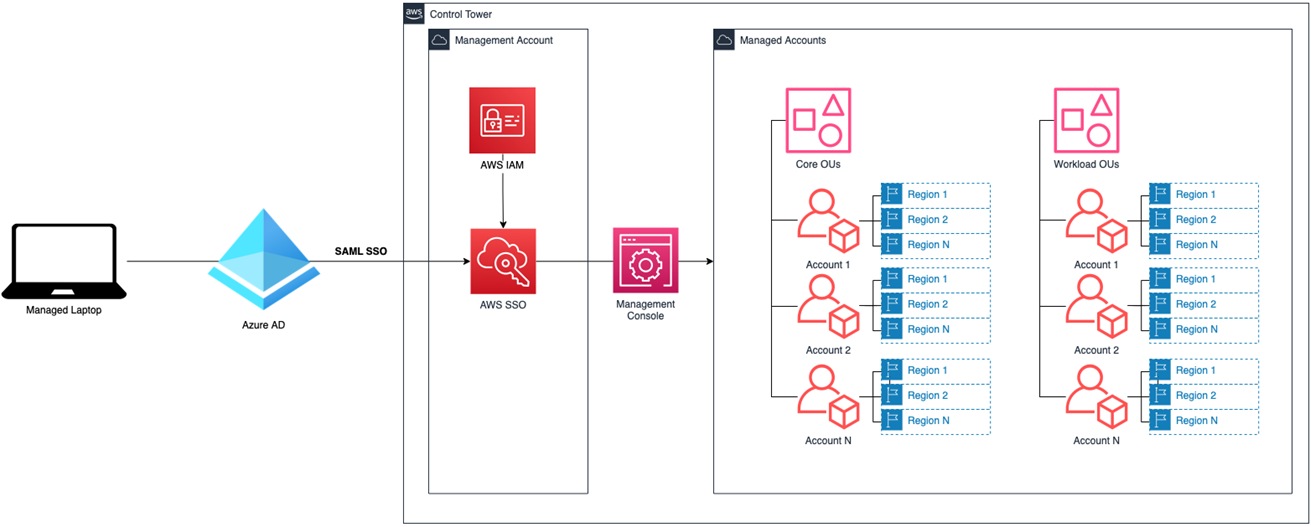
Leveraging AWS IAM Identity Center (previously AWS Single Sign-On), the service’s external identity provider capabilities enable automated user and group provisioning. Permission sets will provide the means to manage roles and permissions at the account level.
Figure 4 – Azure AD integration to AWS Organizations.
Your IdP is integrated to AWS IAM Identity Center to route users from laptops to the management console login screen. From here, users can select accounts and roles that are mapped to their user profile from the IdP.
Currently, AWS Control Tower supports Azure AD, Google Workspaces, Okta, OneLogin, and AD Connector.
Benefits of IAM Identity Center in conjunction with AWS Control Tower include:
- Federation with AWS IAM Identity Center for single-click access to the SSO user portal and its entitlements.
- Supports multi-account access for teams like DevOps, security, and operations.
- Locking down accounts (low human) with codified least privilege access through permission sets.
- CI/CD for automating deployment of permission sets to management account.
- Integration to IdP solution of choice.
- Multi-factor and adaptive authentication to secure access to Amazon WorkSpaces and AWS applications including AWS Control Tower.
- Seamless AWS Command Line Interface (CLI) access through federated authentication with IdP.
- Automated provisioning to keep single sign-on identities synchronized with IdP, providing synchronization between AWS and other user sources connected to IdP including HR systems, Active Directory(s), and LDAP(s).
- Entitlement management through group synchronization directly with IdP.
- Centralized reporting and auditing of user access across all apps and systems.
- Scalable approach to SSO for application onboarding.
AWS Security Suite Enablement and Finding Aggregation
A successful cloud migration requires a day zero security approach. This requires a wide variety of industry-leading AWS native and third-party solutions.
Security considerations include well-architected patterns, least privilege, defense in depth, access (IAM roles), DevSecOps deployment, security tooling, finding aggregation, network security, centralized firewall, cross-account access, root user management, and L0/L1/L2 alerting.
Properly implementing AWS security patterns in a multi-account environment at scale requires dozens of additional add-ons and SCP policies. AWS Security Hub is the single source of truth for both native and third-party security tools.
Additional third-party security tools can easily be integrated as well. This provides a single access point for integrating to an SIEM, helping your company quickly react to security findings and threats.
Baselining Best Practice Patterns at Scale
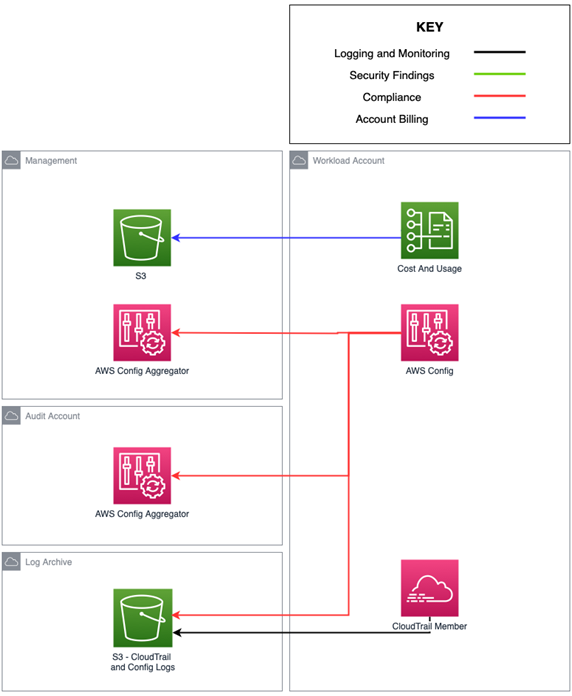
Account baselining is a major benefit of implementing CfCT. Through CloudFormation infrastructure as code and a manifest file, services and infrastructure can be deployed during account provisioning.
The use cases range from IAM, security, and compliance to observability, operations, and networking.
Figure 5 – AWS Control Tower default account baseline.
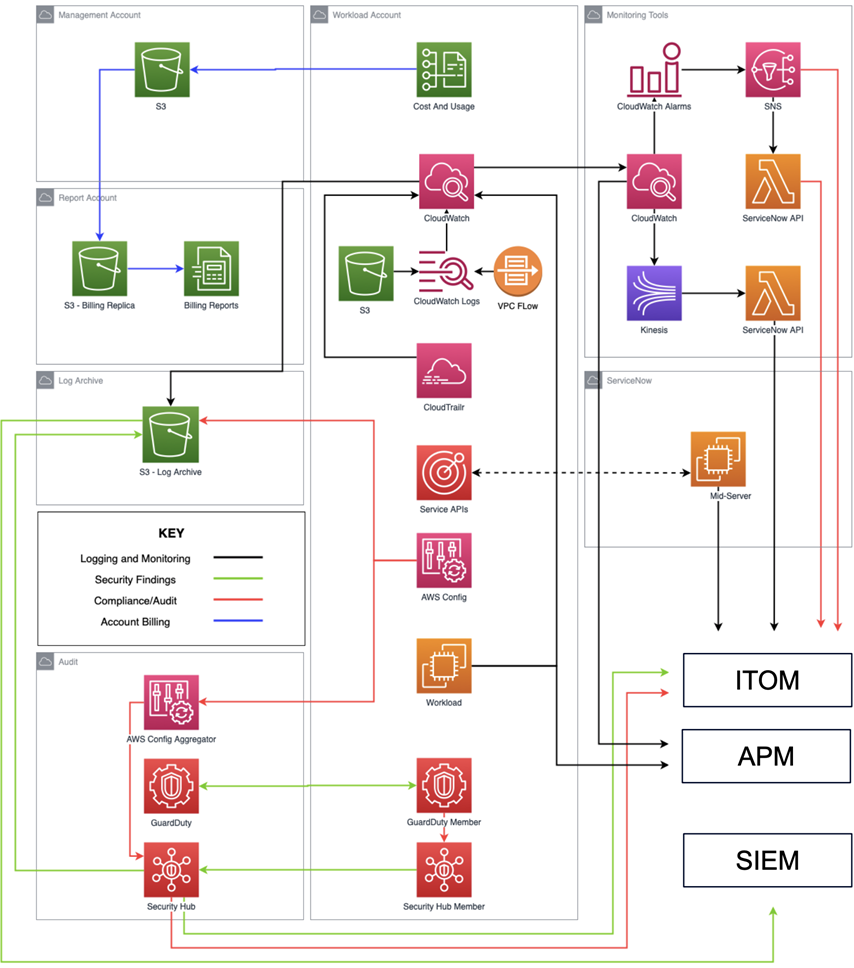
These two diagrams show AWS Control Tower default account baselines (Figure 5) and enterprise baselines (Figure 6) through customizations with CfCT.
Figure 6 – Enterprise account baseline.
Mphasis Stelligent has built out a suite of add-on templates based on multi-account best practices. These customizations configure workload accounts with integrations to security, audit, and monitoring accounts, aggregating data to core accounts with a member/main pattern.
Custom baselining provides a large number of benefits by automating core service deployment at the point of account provisionings. Native logs and metrics are captured through Amazon CloudWatch. Native security tools are enabled and the findings are aggregated into a centralized account. Additional detective guardrails are deployed into the workload accounts. Finally, you can implement patterns for integration to third-party tools such as ServiceNow, APMs, and SIEMs.
A list of commonly deployed templates can be found below:
- Native logging: Enabling and configuration aggregation of AWS native logs including AWS CloudTrail logs, VPC flow logs, Elastic Load Balancer logs, and Amazon Simple Storage Service (Amazon S3) access logs.
- Aggregators: AWS Config, AWS Security Hub, Amazon GuardDuty, AWS CloudTrail orgs, Amazon CloudWatch logs, native service logs, and AWS Security Hub findings.
- Permission sets: Integration to AWS IAM Identity Center.
- Roles and assume roles: Single sign-on groups, cross-account roles, and deployment roles.
- Compliance: Conformance pack, managed rules, and custom AWS Config rules.
- Alarms and notifications: L0 alerts for audit events and metric thresholds.
- Serverless Transit Network Orchestrator: STNO spoke templates for VPC onboarding.
Conclusion
In this post, we covered the critical components of AWS Control Tower and Customizations for Control Tower (CfCT). We examined guardrails, the underlying AWS services utilized by AWS Control Tower, and organizational unit (OU) structures for real-world enterprise implementations.
We also broke down CfCT including deployment of baselines, granting account access with AWS IAM Identity Center, and enabling AWS services for security and observability at scale. Finally, we dove into account baselining covering standard services and third-party tools requiring configuration and integration at the account level.
AWS Control Tower is the foundation for successful multi-account governance and management on AWS. Mphasis Stelligent provides solution modules for all enterprise Control Tower needs—access, observability, networking, compliance, and blast radius.
You can also learn more about Mphasis Stelligent on AWS Marketplace.
Mphasis – AWS Partner Spotlight
Mphasis is an AWS Premier Tier Services Partner that applies next-generation technology to help enterprises transform businesses by leveraging DevOps on AWS with Mphasis Stelligent.
Contact Mphasis | Partner Overview | AWS Marketplace | Case Studies