AWS Partner Network (APN) Blog
Securing the 5G Network on AWS with Palo Alto Networks
By Anurag Thantharate, Sr. Technical Manager – Palo Alto Networks
By Young Jung, Principal Solutions Architect – AWS
 |
| Palo Alto Networks |
 |
Security is job zero at Amazon Web Services (AWS) and is one of the most important design principles of a Well-Architected Framework.
As illustrated in this whitepaper, one of the essential concepts in the AWS Well-Architected Framework’s security pillar is the AWS Shared Security Responsibility Model. This means AWS is responsible for the security of the underlying cloud infrastructure, while the user of AWS is responsible for securing applications deployed on AWS.
To support this model, AWS ensures the security of infrastructure and provides building blocks of products and features to meet security objectives, such as data protection, identity and access management, network and application protection, threat detection and monitoring, and compliance and data privacy.
On top of the infrastructure layer security provided by AWS, Zero Trust security design principles must be applied throughout the architecture when building 5G networks on AWS. The core principle of this is “never trust, always verify, and verify continuously” for building complete solutions for 5G networks.
In this post, we will discuss the way to implement a 5G end-to-end security model based on Zero Trust using Palo Alto Networks’ 5G-native security solution for highly distributed and cloud-native 5G networks—with containerized 5G security and real-time threat correlation among 5G users, device identifiers, and a 5G network slice.
Palo Alto Networks is an AWS Security Competency Partner that helps customers accelerate cloud migration initiatives with inline and API-based security offerings that complement native AWS security features.
Zero Trust Security Model for 5G
Traditional corporate networks have been built around the concept of implicit trust, where network boundaries define this trust domain. If two or more resources are on a network without network security controls, those entities will implicitly trust each other.
The model becomes problematic when this environment encounters an advanced attacker who can establish a foothold on one of those trusted resources and move laterally within the corporate network, thus compromising all devices and applications where the implicit trust can be exploited. Further, this model fails if the trust of a resource is established at a point in time and not continually verified.
Zero Trust provides a model for the security of the network, users, data, and applications through continuous monitoring of transaction flow—from users to applications and data. To do this, an identity-centric approach is often employed, with this identity being viewed as being the “new perimeter.”
Zero Trust is based on the principle that no user, device, or transaction from inside or outside the network can be implicitly trusted. In the Zero Trust model, you define a protected surface which comprises your organization’s most critical and sensitive data, assets, applications, devices, and services. The protected surface is much smaller than the attack surface and should therefore be knowable.
5G Networks on AWS and End-to-End Security
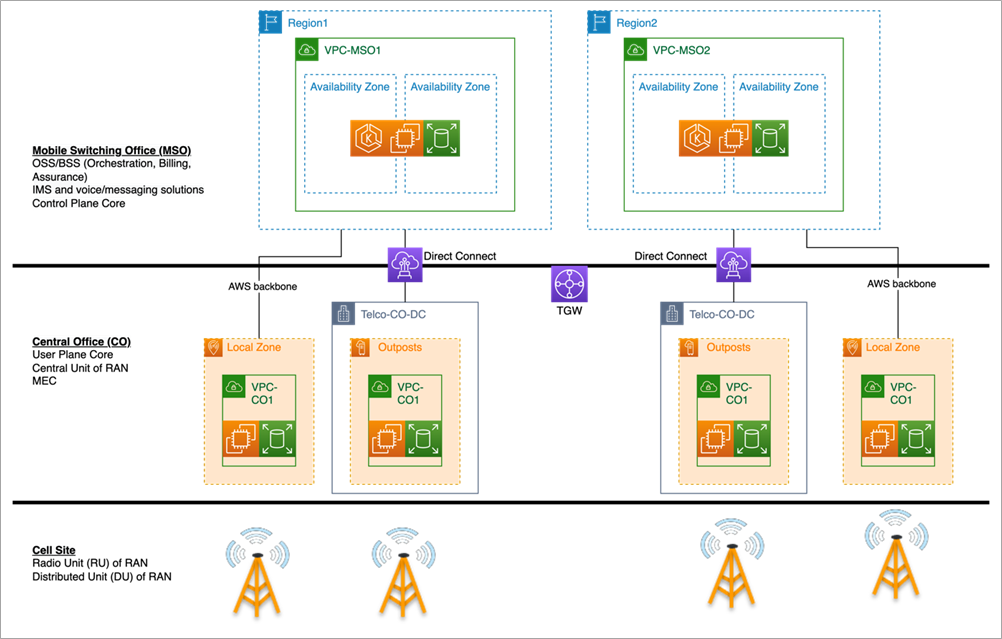
As introduced in the 5G network on AWS whitepaper, a traditional data center architecture for a telco network can be implemented with a hierarchy of logical virtual data centers using the concept of an Amazon Virtual Private Cloud (VPC) on various AWS infrastructure environments.
AWS regions can be the best place to host majority of 5G core control plane network functions because of hyper-scalability and elasticity of compute, storage, and networking resources for network functions. When using a region to host applications, AWS provides general security via AWS Identity and Access Management (IAM), in-transit and at-rest encryption of data by AWS compute and storage services, and overall monitoring and auditing. For details, please refer to the AWS security whitepaper.
Meanwhile, the user plane function (UPF), radio network central unit (CU), and edge applications can be hosted at Mobile Network Operator (MNO) data centers using AWS Outposts and Local Zones that AWS offers, for distributed and low-latency data processing.
Same as with a region environment, AWS provides infrastructure layer security for both Outposts and Local Zone services, which implies MNO can leverage a single pane of glass for orchestration as well as the security framework and architecture.
Figure 1 – General architecture for building a 5G network on AWS.
While AWS security addresses infrastructure layer security and provides baseline tools for end-to-end security design, MNO is still responsible for making 5G network architecture robust and comprehensive so that it protects all layers.
This security design must secure all locations, network interfaces, and attack vectors from external and internal sources through distributed security mechanisms by leveraging Zero Trust principles. To implement 5G security with Zero Trust principles, you have to keep in mind the following action items:
- Least privileged access: Use micro-segmentation to more precisely protect 5G network services and functions.
- Unified security policies: Customers need effective security policies for simplified control over data and application access.
- Protect workloads of cloud-native network functions (CNF): Protect CNF throughout their CI/CD lifespan.
- Detect and prevent threats: Monitor any interactions between network layer functions.
For building 5G end-to-end security architecture, Palo Alto Networks Next Generation Firewall (NGFW) plays a key role in securing the network function application and mobile subscriber of MNO, while Palo Alto Networks Prisma provides security for cloud application image, code, and templates used.
NGFW on AWS provides best-in-class security features for a 5G network function application while providing the full benefits of an AWS-native environment, such as automation of deployment and built-in scalability and resiliency. This means NGFW can be deployed with an automation tool such as AWS CloudFormation, which reduces the operational complexity, human errors, and time to deployment when deploying new NGFW instances.
In addition, as in this Git repo template, VM-Series (an Amazon EC2 instance-based solution) can be deployed in the auto scaling group to ensure scalability and high availability. If you’re using a container-based solution (such as CN-Series), it can leverage a horizontal pod autoscaler and cluster autoscaler of Amazon Elastic Kubernetes Service (Amazon EKS) along with an Amazon CloudWatch trigger.
In following sections, we’ll outline how to secure 1/ access to network functions, 2/ 3GPP interface, and 3/ network function applications running on cloud using Palo Alto NGFW and Prisma solutions in AWS.
Security for Network Function Access and 3GPP Interfaces
Securing Access to Network Function
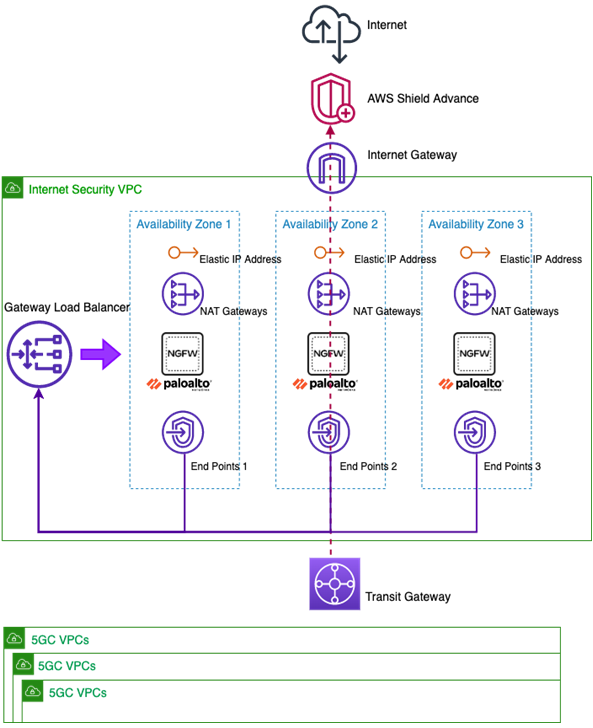
When you create a 5G network on AWS, access to the internet for 5G network function (such as for patching update) can be done directly from each 5G VPC, or via a centralized and secured internet security VPC, even though AWS Shield provides DDoS protection through the internet gateway (IGW).
In addition, if you use centralized security VPC for internet access, you can have more efficient governance and control for the internet access from the network function (or each host EC2 instance).
The diagram below shows the architecture with a centralized security VPC using Palo Alto Networks NGFWs. Through this architecture, VPC (security group, ACL), IGW, NAT-GW, AWS Shield, and NGFW altogether provide a maximum layer of protection to network functions when they are created on AWS.
Figure 2 – VPC infrastructure security.
Securing Network Function’s 3GPP Interfaces
Palo Alto Networks NGFW enables 5G-native security for MNO by allowing the implementation of fine-grained security policies and visibility into the 5G user traffic. That is, NGFW provides the ability to correlate the user or subscriber (using Subscriber Permanent Identifier – SUPI), equipment or device (using Permanent Equipment Identifier – PEI), and network slices (using a slice/service type identifier – SST) back to the potentially malicious traffic.
The ability to leverage visibility in both the GPRS tunneling protocol user plane (GTP-U or the data layer) and control plane protocol to correlate malware to the real subscriber and equipment identity is critical to detect and enable real-time threat response. This also allows NGFW to provide mobile identifier-based policy control and threat protection, which can correlate attacks, threats, and vulnerabilities to the actual 5G subscriber and equipment identities (such as SUPI and IMEI, for example).
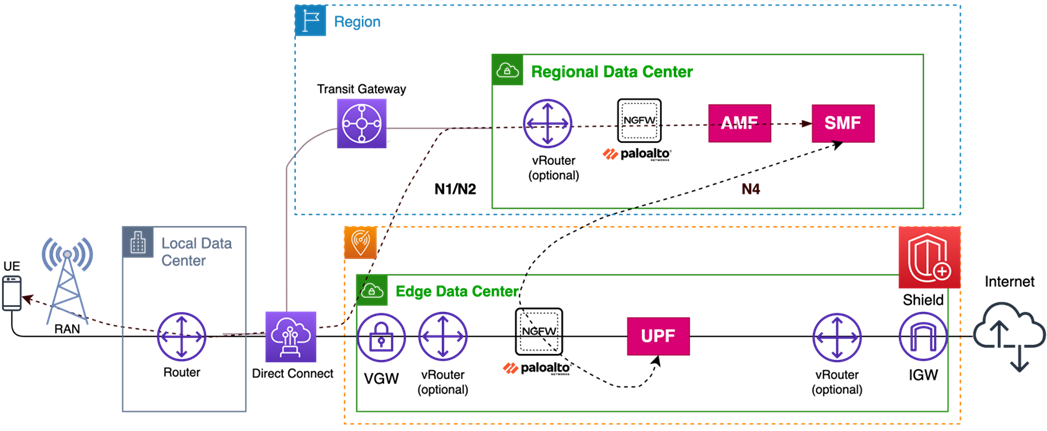
Furthermore, advanced application layer security enables MNO to fend off threats including exploits, malware, malicious URLs, malicious DNS, spyware, command and control, and data exfiltration in real time. For this end-to-end security, NGFWs can be deployed on AWS to have visibility into all 3GPP network interfaces (N1, N2, N3, N4, N6 and N9).
Figure 3 – Palo Alto Networks 5G security on AWS infrastructure.
Three specific postures are worth discussing in a bit more detail: RAN (signaling) security, user plane security, and internet security:
- RAN security: The interface from the RAN to the Access and Mobility Management Function (AMF) is the 3GPP N2 interface and is sent over Stream Control Transmission Protocol (SCTP). The NGFW in the region VPC offers SCTP security via features like stateful inspection, payload protocol identifier (PPID) filtering, and INIT flood protection. The NGFW in the region VPC is able to detect UE attach and AMF paging floods based on its dynamic database of threat signatures.
. - User plane security: The NGFW can be used to secure both the user plane traffic and user plane function (UPF). When deployed next to the UPF, the NGFW is able to provide user plane security, as well as perform stateful Packet Forwarding Control Protocol (PFCP) inspection of the N4 interface to secure communication between the UPF and session management function (SMF), as shown in Figure 3.
.
Palo Alto Networks NGFWs safely enable applications (App-ID) and their content (Content-ID) while using inline machine learning (ML) and continuous threat signature updates to identify and stop threats as quickly as possible. On top of App-ID and Content-ID, subscriber, equipment and slice identifiers are present in traffic, URL, and threat-related logs, making remediation from the security operation center (SOC) much easier. Furthermore, policies can be created leveraging these important identifiers for a granular security posture.
. - Internet security: Internet access over the N6 interface of the UPF can be made available in the region VPC, Local Zone, or AWS Outpost sites. In the case of region and Local Zone, N6 traffic can be secured via a combination of AWS Shield, AWS security groups, network access control lists (NACLs), and Palo Alto Networks NGFW solution. When securing internet traffic, the NGFW is able to provide application and threat visibility, along with additional features such as network address translation (NAT).
Security for Cloud Applications
In the framework of a shared responsibility security model, a customer’s responsibilities are based on the consumed service offering and any platform or software usage. Organizations are always responsible for securing their data, accounts, and identities within the cloud.
Through a machine learning-driven approach, Palo Alto Networks Prisma Cloud helps organizations fulfill their obligations in that shared responsibility model, in which Prisma Cloud is a security solution to provide real-time visibility and full-stack protection for applications running on the cloud.
MNOs can leverage Prisma Cloud for Cloud Workload Protection (CWP), Cloud Security Posture Management (CSPM) and Code Security. Together, these capabilities and others offer rich insight into potential vulnerabilities, runtime risks, and mistakes within infrastructure as code (IaC). This comprehensive solution, with tightly integrated components for ensuring complete visibility, reducing risk, preventing threats, provides detailed reporting and automating responses. Gaining new intelligence with each incident is required for effective 5G security.
Cloud Workload Protection (CWP)
Prisma Cloud’s CWP feature delivers flexible protection to secure cloud virtual machines (such as Amazon EC2 instances), containers and applications on Amazon EKS, serverless functions, and containerized offerings like AWS Fargate tasks.
Three critical features within CWP are runtime security for containers, hosts, and serverless functions that are actively running, vulnerability management, which offers visibility and protection before new images are deployed, and API security.
Prisma Cloud leverages defenders deployed in EKS clusters to help secure the cloud-native 5G workloads. Cloud security is multi-faceted and involves both runtime and pre-runtime controls, such as:
- Runtime security: Runtime security refers to end-to-end monitoring and validation of all activity within containers, hosts, and serverless functions. Runtime security works by leveraging application control and establishing a baseline of normal behavior for each container running in the 5G core.
.
Through real-time observation of file systems, processes, and network activity, runtime security detects suspicious or anomalous activity and alerts teams as needed or blocks anomalies in real time. When the defenders detect anomalies, alerts can be sent to extended security orchestration, automation, and response (XSOAR), where playbooks are run to correlate data from other sources and perform an automated response.
. - Vulnerability management: Prisma Cloud brings users one step closer by allowing organizations to scan images in various stages of the CI/CD pipeline and catch potential issues as early as possible (this is often referred to as “shift-left” security). Below are some of the ways this is accomplished:
- Security for the CI process: The easiest way to secure cloud-native applications is by preventing vulnerable images from making their way through the software development lifecycle (SDLC) in the first place. Prisma Cloud helps by integrating with AWS CodeBuild, AWS CodeDeploy, and AWS CodePipeline when creating, storing, and deploying container images.
- Registry scanning: MNOs can leverage Amazon Elastic Container Registry (Amazon ECR) for numerous container images deployed in its various network environments. Prisma Cloud complements ECR’s scanning capabilities by allowing scans from within the SDLC before images are placed in ECR.
Prisma Cloud also allows for visibility into vulnerabilities in running containers. Real-time threat intelligence feeds combine multiple commercial and proprietary sources to provide robust and timely data on potential malware in images.
- API security: Prisma Cloud offers web application and API security (WAAS) functionality to reduce the attack surface of the 5G service-based architecture (SBA). With features like denial of service (DoS) protection, API discovery, and the ability to ingest 3GPP OpenAPI files defining 3GPP service-based interfaces, the WAAS is a critical tool for protecting the network functions deployed as part of the SBA.
Cloud Security Posture Management (CSPM)
MNOs can use the Prisma Cloud CSPM to aggregate AWS resource configuration, IAM policies, user activity, and network traffic to provide concise and actionable insights. By leveraging hundreds of built-in compliance policies and custom policies unique to the 5G environment, MNOs can raise alerts and route them to XSOAR for an automated response.
- Code security: IaC tools like AWS CloudFormation make deployment of 5G on AWS rapid and convenient, but it’s also easy to make mistakes in IaC templates and rapidly spread misconfigurations across the mobile packet core without even realizing it. Prisma Cloud Code Security allows MNOs to catch misconfigurations before they happen.
.
Security for IaC can be embedded into workflows in DevOps tooling such as Terraform and CloudFormation templates. Code security also provides supply chain graphs showing an inventory and easy-to-consume visualization of your supply chain components to understand and protect your attack surface.
. - XSOR: XSOAR is a comprehensive security orchestration, automation, and response (SOAR) platform that unifies case management, automation, real-time collaboration, and threat intelligence management to serve security teams across the incident lifecycle. This level of automation, offered via playbooks and other tools, allows SOC analysts to focus on the things that matter.
Conclusion
Palo Alto Networks solutions, on top of AWS infrastructure security, can help protect mission-critical workloads in 5G networks of telco cloud environments with a complete set of security tools that are available to Mobile Network Operators (MNOs).
More specifically, the end-to-end 5G-native security solution can help you to implement cloud security at scale across cloud-native architectures, integrate security into each phase of the DevOps workflow, secure critical infrastructure as code, and provide visibility into network traffic. All of this while giving you the ability to orchestrate and automate your response to the incidents you encounter.
Palo Alto Networks – AWS Partner Spotlight
Palo Alto Networks is an AWS Security Competency Partner that helps customers accelerate cloud migration initiatives with inline and API-based security offerings that complement native AWS security features.
Contact Palo Alto Networks | Partner Overview | AWS Marketplace