Category: AWS Directory Service
AWS Directory Service Update – Support for Managed Microsoft Active Directory
 The AWS Directory Service allows you to use your existing corporate identities to access AWS services and to simplify cloud-based deployment of Microsoft Windows and Linux applications that are dependent on the availability of a directory. We launched the service last year with support for two types of directories (AD Connector and Simple AD); see my post, New AWS Directory Service, to learn more.
The AWS Directory Service allows you to use your existing corporate identities to access AWS services and to simplify cloud-based deployment of Microsoft Windows and Linux applications that are dependent on the availability of a directory. We launched the service last year with support for two types of directories (AD Connector and Simple AD); see my post, New AWS Directory Service, to learn more.
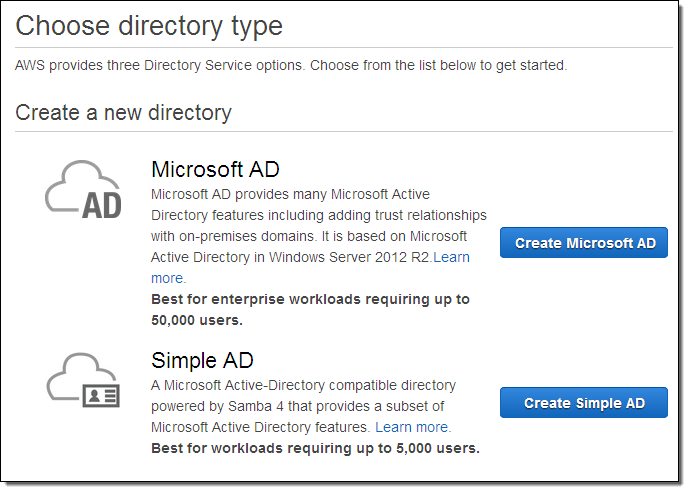
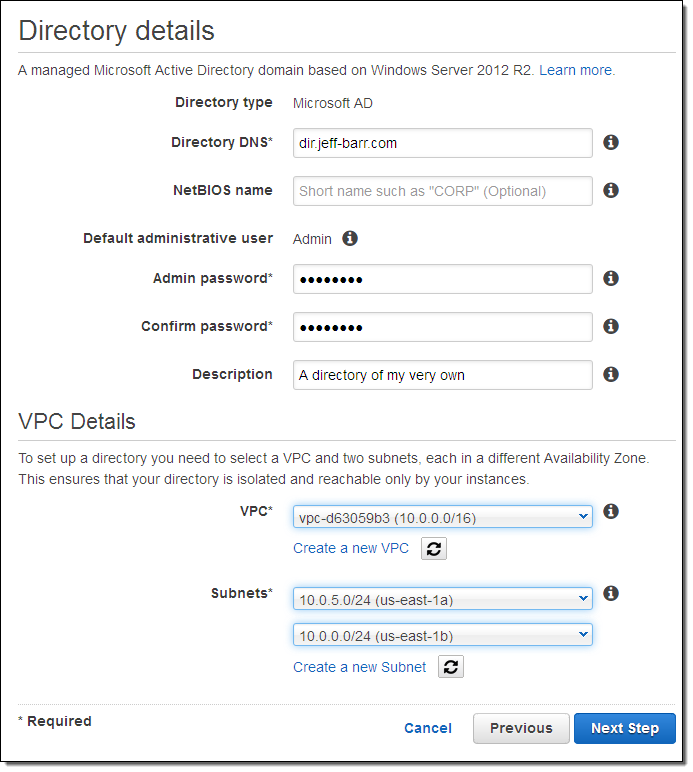
Late last week we launched a third option, support for a managed Microsoft Active Directory, powered by Windows Server 2012 R2. When you choose this option, you get a Microsoft Active Directory that is designed to support up to 50,000 users (approximately 200,000 directory objects, including users, groups, and computers). The directory runs in two separate Availability Zones within a Virtual Private Cloud.
Provisioning is easy, quick (25-30 minutes), and straightforward. Because this is a managed service, common administrative tasks are handled for you. This includes host monitoring with automatic replacement, data replication, snapshot backups, and automatic software updates. As is often the case with AWS, you will spend less time administering and more time working on your applications and your business.
Use Cases
With this launch, running workloads that are aware of a directory is easier than ever. This includes Microsoft SharePoint as well as custom applications that make use of .NET and/or SQL Server.
System administrators can manage user and group memberships, join Linux and Windows computers to a domain, set up Kerberos single sign-on (SSO), apply group policies, and create trust relationships between domains. They can also use their existing corporate credentials to log in to the AWS Management Console in order to manage AWS resources.
Provisioning a Directory
You can provision a managed Microsoft Active Directory from the AWS Directory Service Console. Visit the Console, click on Get Started Now, and then choose Create Microsoft AD:
Enter a name (I used dir.jeff-barr.com), set up an administrative password, choose a VPC, and pick two subnets of the VPC:
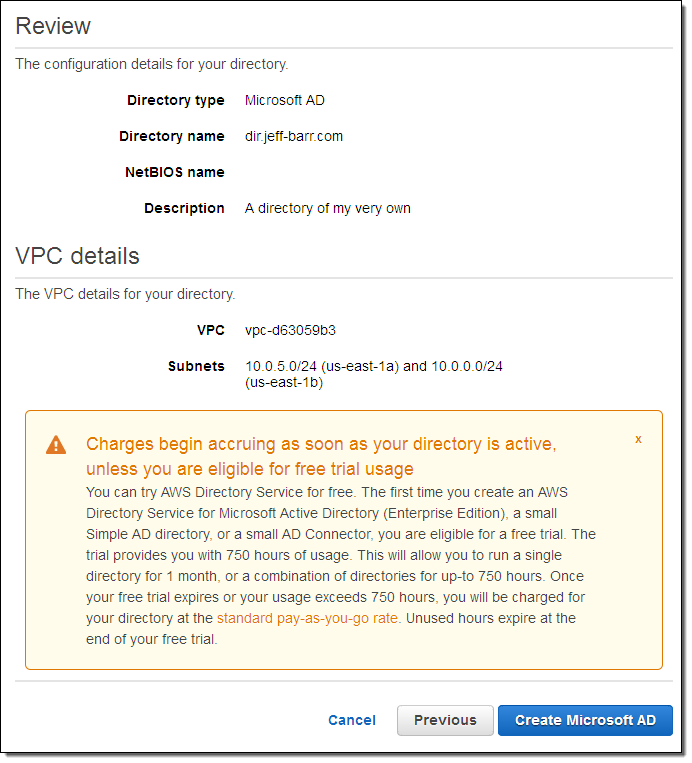
Then click on Next Step to review the settings and to make sure that you understand the terms of the free trial of AWS Directory Service, then click on Create Microsoft AD:
Visit the list of directories, check your email, walk your dog, and then wait for the status to change to Active (click on the refresh icon every so often):
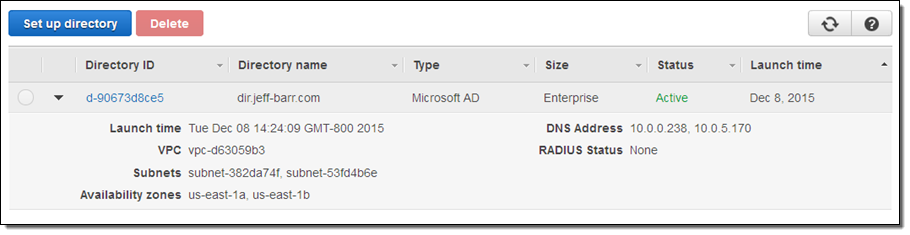
You can then connect to the directory in the usual way, create your groups and users, and enjoy the benefits that I listed above.
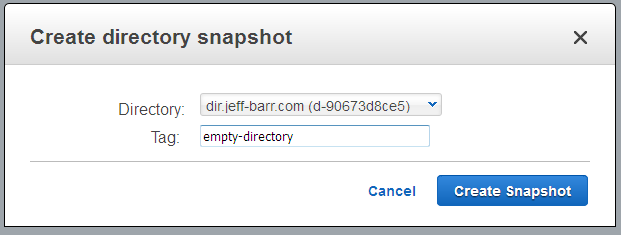
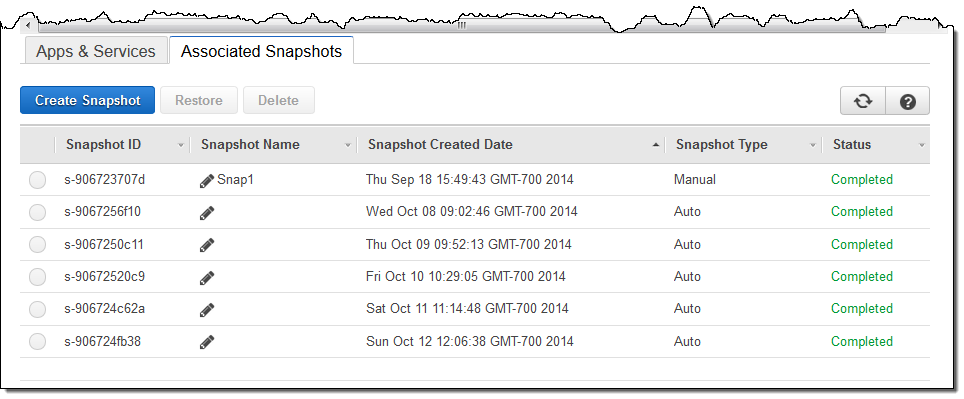
You can create snapshots (and restore them later) from the console; simply select Snapshots in the navigation bar and click on Create Snapshot:
Pricing and Availability
The Managed Microsoft Active Directory Service is available now in the US East (Northern Virginia), US West (Oregon), EU (Ireland), Asia Pacific (Sydney), and Asia Pacific (Tokyo) regions. You can try it out for one month (750 hours of usage) at no charge. After that, you’ll pay $0.40 per hour per in the US East (Northern Virginia) region; see the AWS Directory Service Pricing page for pricing in other regions.
— Jeff;
Joining a Linux Instance to a Simple AD (AWS Directory Service)
If you are tasked with providing and managing user logins to a fleet of Amazon Elastic Compute Cloud (EC2) instances running Linux, I have some good news for you!
You can now join these instances to an AWS Directory Service Simple AD directory and manage credentials for your user logins using standard Active Directory tools and techniques. Your users will be able to log in to all of the instances in the domain using the same set of credentials. You can exercise additional control by creating directory groups.
We have published complete, step-by-step instructions to help you get started. You’ll need to be running a recent version of the Amazon Linux AMI, Red Hat Enterprise Linux, Ubuntu Server, or CentOS on EC2 instances that reside within a Amazon Virtual Private Cloud, and you’ll need to have an AWS Directory Service Simple AD therein.
You simply create a DHCP Options Set for the VPC and point it at the directory, install and configure a Kerberos client, join the instance to the domain, and reboot it. After you have done this you can SSH to it and log in using an identity from the directory. The documentation also shows you how to log in using domain credentials, add domain administrators to the sudo’ers list, and limit access to members of specific groups.
— Jeff;
Now Available – AWS Directory Service API & CLI (Bonus: CloudTrail Integration)
 AWS Directory Service allows you to connect your AWS resources to an existing on-premises Active Directory or to set up a new, standalone directory in the AWS Cloud (see my post, New AWS Directory Service, to learn more).
AWS Directory Service allows you to connect your AWS resources to an existing on-premises Active Directory or to set up a new, standalone directory in the AWS Cloud (see my post, New AWS Directory Service, to learn more).
Until today, all operations on a Directory were initiated through the AWS Management Console. This was convenient, but was not ideal for integration with existing workflows.
API & CLI
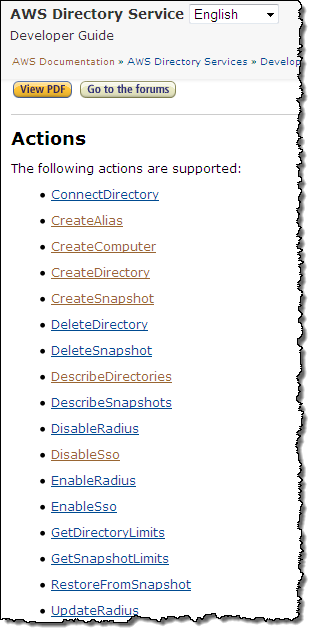
Today we are making Directory Service even more useful by adding API and CLI (Command-Line Interface) support. You can now create and delete directories, computer accounts, and aliases (alternate names for the directory). You can create snapshot backups for standalone directories, and you can manage sign-on modes (Radius and SSO).
You can use an IAM policy to grant permission to perform the API actions.
 Let’s take a look at some sample requests and responses, starting with a call to
Let’s take a look at some sample requests and responses, starting with a call to CreateDirectory. Here is the request:
{"Name": "corp.snackers.org",
"ShortName": "corp",
"Password": "Westbay@123",
"Description": "corp",
"Size": "Large",
"VpcSettings":
{"VpcId": "vpc-c3dd04a2",
"SubnetIds":
["subnet-9add04fb", "subnet-66dc0507"]
}
}
And here is the response:
{"DirectoryId": "d-90673058d7"}
Here’s a call to DescribeDirectories, with three Directory Ids as arguments:
{"DirectoryIds":
["d-9067315087", "d-9067312ba4", "d-906731a3f3"]
}
The response is fairly long; it starts like this:
{"DirectoryDescriptions":
[
{"AccessUrl": "d-9067312ba4.dev.awsapps.com",
"Alias": "d-9067312ba4",
"DirectoryId": "d-9067312ba4",
"DnsIpAddrs":
["172.16.1.130", "172.16.0.87"],
"LaunchTime": 1430175177.892,
"Name": "Eastbay.snackers.org",
"ShortName": "Eastbay",
"Size": "Large",
"SsoEnabled": false,
"Stage": "Active",
"StageLastUpdatedDateTime": 1430175333.603,
"Type": "SimpleAD",
"VpcSettings":
{"AvailabilityZones":
["us-east-1a", "us-east-1e"],
"SubnetIds":
["subnet-9add04fb", "subnet-13773d29"],
"VpcId": "vpc-c3dd04a2"}
},
...
CloudTrail Integration
Directory Service API actions (via an SDK, the Console, or the CLI) can now be recorded via AWS CloudTrail.
Learn More
To learn more, read the new AWS Directory Service API Developer Guide. You can download the AWS SDKs and the AWS Command Line Interface (CLI) to get started.
— Jeff;
AWS Expansion – WorkSpaces, Directory Service, ElastiCache, GovCloud, Kinesis, Traditional Chinese, More
We’ve  increased the geographic footprint and international relevance of several AWS services this past month. Here’s a summary:
increased the geographic footprint and international relevance of several AWS services this past month. Here’s a summary:
- Amazon WorkSpaces and AWS Directory Service are now available in the Asia Pacific (Singapore) region.
- Amazon ElastiCache is now available in the EU (Frankfurt) region.
- AWS Trusted Advisor, Amazon ElastiCache, and RDS integration with AWS CloudTrail are now available in AWS GovCloud (US).
- We added a second location in Korea for Amazon CloudFront and Amazon Route 53.
- Amazon Kinesis is now available in the US West (Northern California) region.
- The AWS website is now available in Traditional Chinese.
For more information on service availability, please take a look at our Products and Services by Region page.
— Jeff;
Amazon WorkMail – Managed Email and Calendaring in the AWS Cloud
Have you ever had to set up, run, and scale an email server? While it has been a long time since I have done this on my own, I do know that it is a lot of work! Users expect to be able to access their email from the application, device, or browser of their choice. They want to be able to send and receive large files (multi-megabyte video attachments and presentations often find their way in to my inbox). Email administrators and CSO’s are looking for robust security measures.
Paradoxically, email is both mission-critical and pedestrian. Everyone needs it to work, but hardly anyone truly understands what it takes to make this happen!
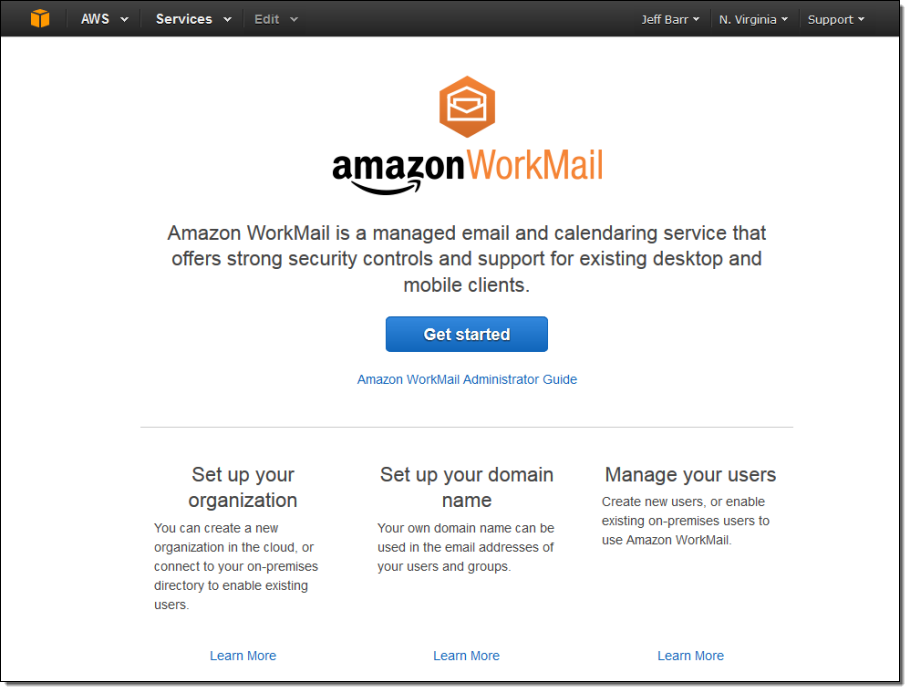
Introducing Amazon WorkMail
Today  I would like to introduce Amazon WorkMail. This managed email and calendaring solution runs in the Cloud. It offers a unique set of security controls and works with your existing desktop and mobile clients (there’s also a browser-based interface). If your organization already has a directory of its own, Amazon WorkMail can make use of it via the recently introduced AWS Directory Service. If not, Amazon WorkMail will use Directory Service to create a directory for you as part of the setup process.
I would like to introduce Amazon WorkMail. This managed email and calendaring solution runs in the Cloud. It offers a unique set of security controls and works with your existing desktop and mobile clients (there’s also a browser-based interface). If your organization already has a directory of its own, Amazon WorkMail can make use of it via the recently introduced AWS Directory Service. If not, Amazon WorkMail will use Directory Service to create a directory for you as part of the setup process.
Amazon WorkMail was designed to work with your existing PC and Mac-based Outlook clients including the prepackaged Click-to-Run versions. It also works with mobile clients that speak the Exchange ActiveSync protocol.
Our 30-day free trial will give you the time and the resources to evaluate Amazon WorkMail in your own environment. As part of the trial, you can serve up to 25 users, with 50 gigabytes of email storage per employee. In order to help you to move your organization to Amazon WorkMail, we also provide you with a mailbox migration tool.
Amazon WorkMail makes use of a number of AWS services including Amazon WorkDocs (formerly known as Amazon Zocalo), the Directory Service, AWS Identity and Access Management (IAM), AWS Key Management Service (KMS), and Amazon Simple Email Service (SES).
Amazon WorkMail Features
You can set up Amazon WorkMail for a new organization in a matter of minutes. As I mentioned earlier, you can use your existing directory or you can have Amazon WorkMail set one up for you. You can send and receive email through your existing domain name by adding a TXT record (for verification of ownership) and an MX record (to route the mail to Amazon WorkMail to your existing DNS configuration).
As a Amazon WorkMail user, you have access to all of the usual email features including calendaring, calendar sharing, tasks, contact lists, distribution lists, resource booking, public folders, and out-of-office (OOF) messages.
The browser-based interface has a full array of features. It works with a wide variety of browsers including Firefox, Chrome, Safari, and newer (IE 9 and higher) versions of Internet Explorer. The interface gives you access to email, calendars, contacts, and tasks. You can access shared calendars and public folders, book resources, and manage your OOF.
Amazon WorkMail was designed to work in today’s data-rich, email-intensive environments. Each inbox has room for up to 50 gigabytes of messages and attachments. Messages can range in size all the way up to 25 megabytes.
As part of this launch we are renaming Amazon Zocalo to Amazon WorkDocs! Amazon WorkMail can be used in conjunction with WorkDocs for simple, controlled distribution of documents that contain sensitive information.
Amazon WorkMail Security Controls
Let’s talk about security for a bit. Amazon WorkMail includes a number of security features and controls that will allow it to meet the needs of many types of organizations. Here’s an overview of some of the most important features and controls:
- Location Control – The Amazon WorkMail administrator can choose to create mailboxes in any supported AWS region. All mail and other data will be stored within the region and will not be transferred to any other region. During the Preview, Amazon WorkMail will be supported in the US East (Northern Virginia) and EU (Ireland) regions, with more to follow over time.
- S/MIME – Data in transit to and from Outlook clients and certain iPhone and iPad apps is encrypted using S/MIME. Data in transit to other clients is encrypted using SSL.
- Stored Data Encryption – Data at rest (messages, contacts, attachments, and metadata) is encrypted using keys supplied and managed by KMS.
- Message Scanning – Incoming and outgoing email messages and attachments are scanned for malware, viruses, and spam.
- Mobile Device Policies & Actions – The Amazon WorkMail administrator can selectively require encryption, password protection, and automatic screen locking for mobile devices. The administrator can also remotely wipe a lost or mislaid mobile device if necessary.
Getting Started with Amazon WorkMail
Let’s walk through Amazon WorkMail while wearing our email administrator hats! I need to create a Amazon WorkMail organization. In most cases, I would use a single organization for an entire company.
I start by opening up the AWS Management Console and choosing Amazon WorkMail:
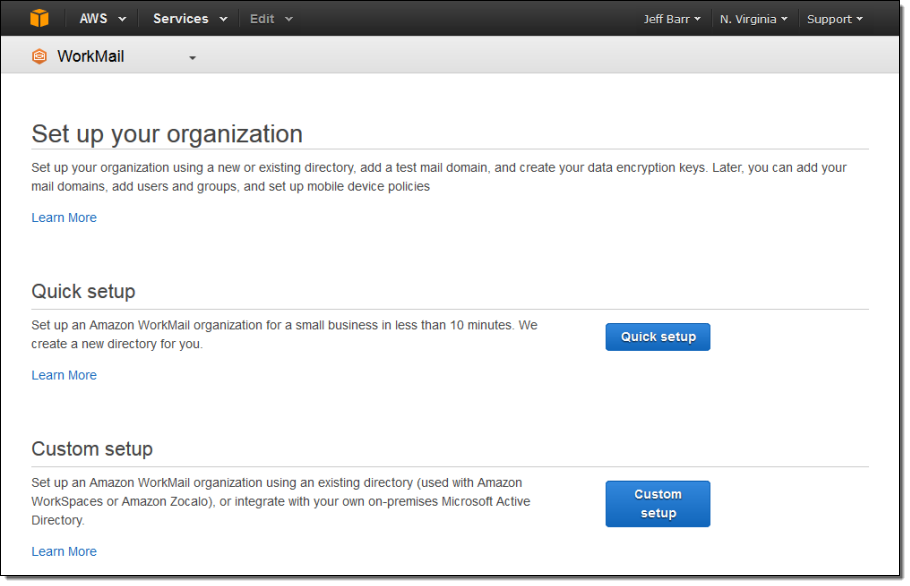
I click the Get started button. At this point I can choose between a Quick setup (Amazon WorkMail will create a new directory for me) or a Custom setup (Amazon WorkMail will use an existing directory that I configure):
I’ll go for the quick setup today. I need to pick a unique name for my organization:
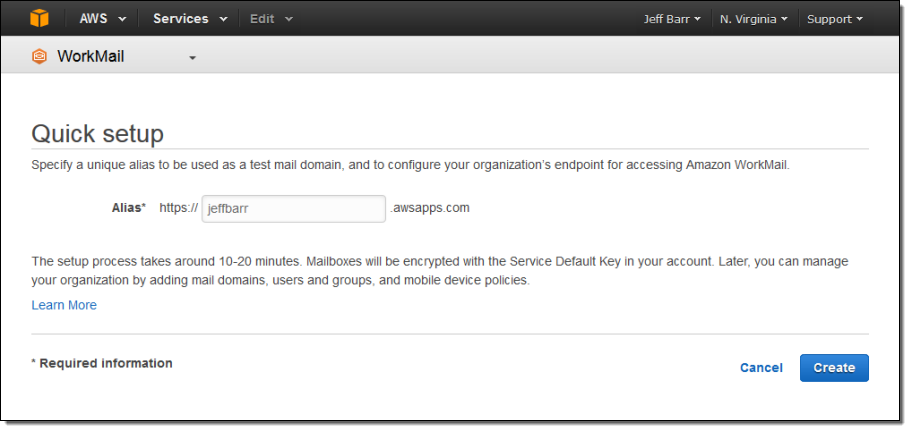
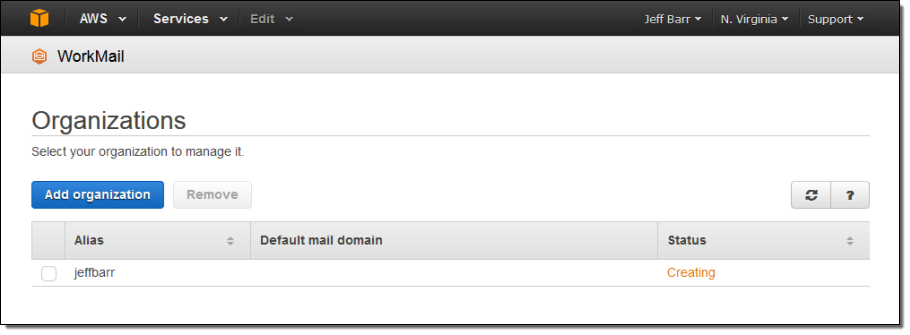
This will automatically create a directory and then create and initialize my organization. It will also initiate the Amazon SES domain verification process (for jeffbarr.awsapps.com in this case) and create a set of DKIM keys so that I can send DKIM-signed mail. The entire process takes 10 to 20 minutes and requires no additional work on my part. The organization’s status will start out as creating and will transition to active before too long:
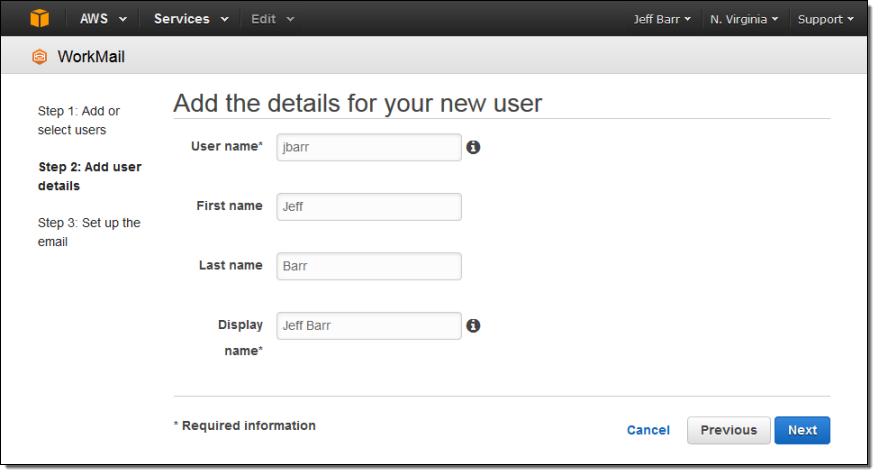
After the creation process completes I can begin to add Amazon WorkMail users to my organization (if I had used an existing directory in the previous step I could simply select them from a list at this point). I’ll begin by adding myself:
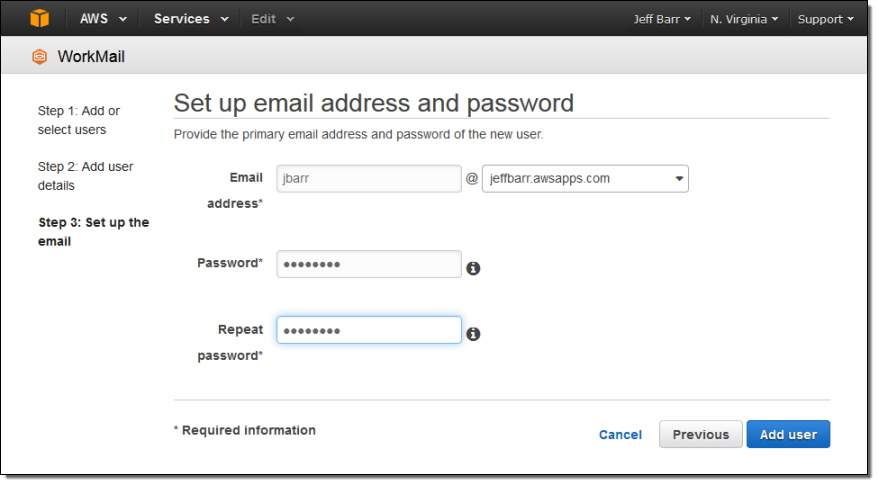
Then I specify the email address and password. If I have associated one or more domain names with the organization, I can use the name as the basis for the email address:
I can browse all of the organization’s users:
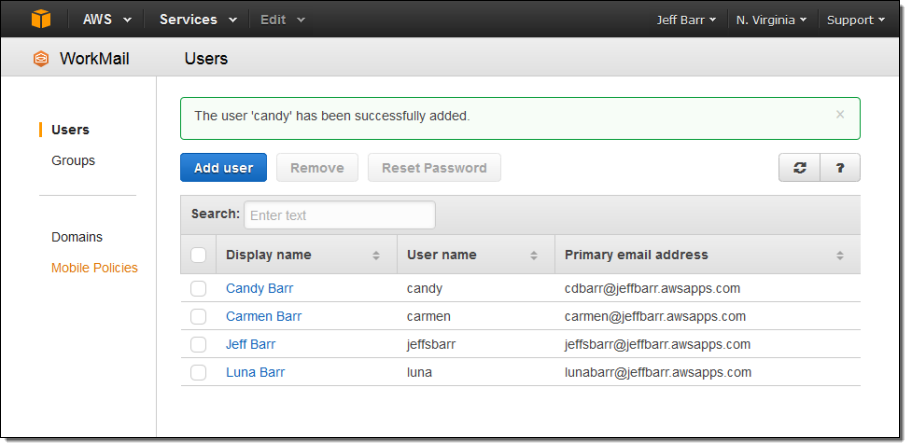
I can also create groups, attach domains, and manage mobile device policies, all from the Console.
The Amazon WorkMail Browser-Based Interface
Let’s take a look at the browser-based interface to Amazon WorkMail. Here’s my inbox:
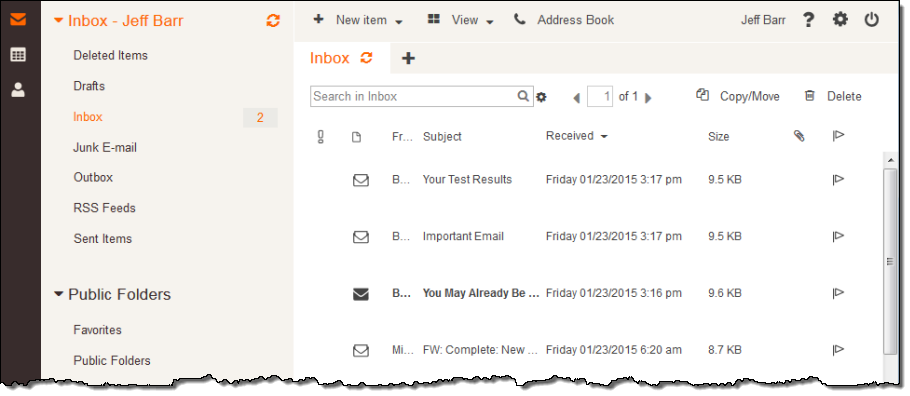
And my calendar:
This is just a sampling of the features that are available in the Amazon WorkMail.
Pricing and Availability
We are launching a Preview of Amazon WorkMail in the US East (Northern Virginia) and EU (Ireland) regions today and you can sign up for the Preview if you are interested in joining.
After the 30-day free trial (25 users and 50 gigabytes of storage per user), pricing is on a per-user, pay-as-you-go basis. You will be charged $4 per month for a 50 gigabyte Amazon WorkMail mailbox, or $6 per month for a bundle that includes Amazon WorkMail and WorkDocs. There is no separate charge for the use of SES to send messages.
— Jeff;
New AWS Directory Service
Virtually every organization uses a directory service such as Active Directory to allow computers to join domains, list and authenticate users, and to locate and connect to printers, and other network services including SQL Server databases. A centralized directory reduces the amount of administrative work that must be done when an employee joins the organization, changes roles, or leaves.
With the advent of cloud-based services, an interesting challenge has arisen. By design, the directory is intended to be a central source of truth with regard to user identity. Administrators should not have to maintain one directory service for on-premises users and services, and a separate, parallel one for the cloud. Ideally, on-premises and cloud-based services could share and make use of a single, unified directory service.
Perhaps you want to run Microsoft Windows on EC2 or centrally control access to AWS applications such as Amazon WorkSpaces or Amazon Zocalo. Setting up and then running a directory can be a fairly ambitious undertaking once you take in to account the need to procure and run hardware, install, configure and patch the operating system, and the directory, and so forth. This might be overkill if you have a user base of modest size and just want to use the AWS applications and exercise centralized control over users and permissions.
The New AWS Directory Service
Today we are introducing the AWS Directory Service to address these challenges! This managed service provides two types of directories. You can connect to an existing on-premises directory or you can set up and run a new, Samba-based directory in the Cloud.
If your organization already has a directory, you can now make use of it from within the cloud using the AD Connector directory type. This is a gateway technology that serves as a cloud proxy to your existing directory, without the need for complex synchronization technology or federated sign-on. All communication between the AWS Cloud and your on-premises directory takes place over AWS Direct Connect or a secure VPN connection within a Amazon Virtual Private Cloud. The AD Connector is easy to set up (just a few parameters) and needs very little in the way of operational care and feeding. Once configured, your users can use their existing credentials (user name and password, with optional RADIUS authentication) to log in to WorkSpaces, Zocalo, EC2 instances running Microsoft Windows, and the AWS Management Console. The AD Connector is available in Small (up to 10,000 users, computers, groups, and other directory objects) and Large (up to 100,000 users, computers, groups, and other directory objects).
If you don’t currently have a directory and don’t want to be bothered with all of the care and feeding that’s traditionally been required, you can quickly and easily provision and run a Samba-based directory in the cloud using the Simple AD directory type. This directory supports most of the common Active Directory features including joins to Windows domains, management of Group Policies, and single sign-on to directory- powered apps. EC2 instances that run Windows can join domains and can be administered en masse using Group Policies for consistency. Amazon WorkSpaces and Amazon Zocalo can make use of the directory. Developers and system administrators can use their directory credentials to sign in to the AWS Management Console in order to manage AWS resources such as EC2 instances or S3 buckets.
Getting Started
Regardless of the directory type that you choose, getting started is quick and easy. Keep in mind, of course, that you are setting up an important piece of infrastructure and choose your names and passwords accordingly. Let’s walk through the process of setting up each type of directory.
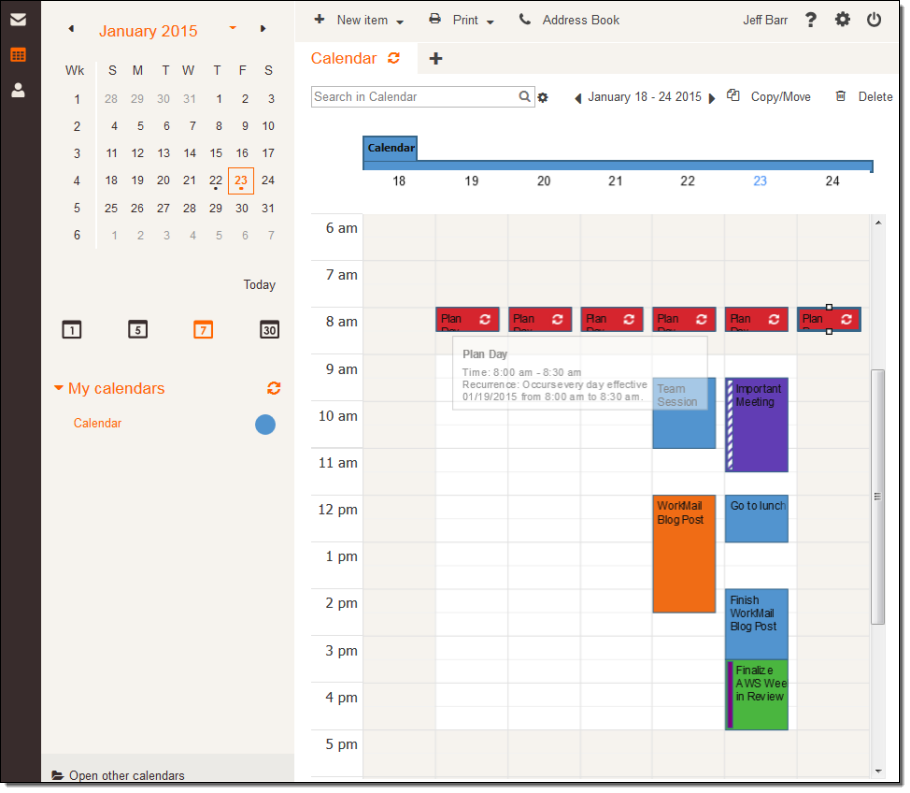
I can create an AD Connector as a cloud-based proxy to an existing Active Directory running within my organization. I’ll have to create a VPN connection from my Virtual Private Cloud to my on-premises network, making use of AWS Direct Connect if necessary. Then I will need to create an account with sufficient privileges to allow it handle lookup, authentication, and domain join requests. I’ll also need the DNS name of the existing directory. With that information in hand, creating the AD Connector is a simple matter of filling in a form:
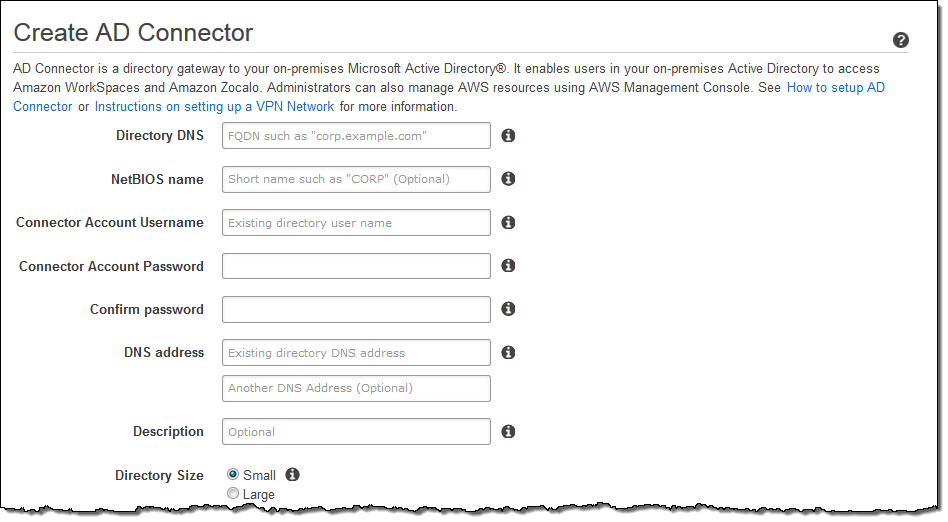
I also have to provide it within information about my VPC, including the subnets where I’d like the directory servers to be hosted:
The AD Connector will be up & running and ready to use within minutes!
Creating a Simple AD in the cloud is also very simple and straightforward. Again, I need to choose one of my VPCs and then pick a pair of subnets within it for my directory servers:
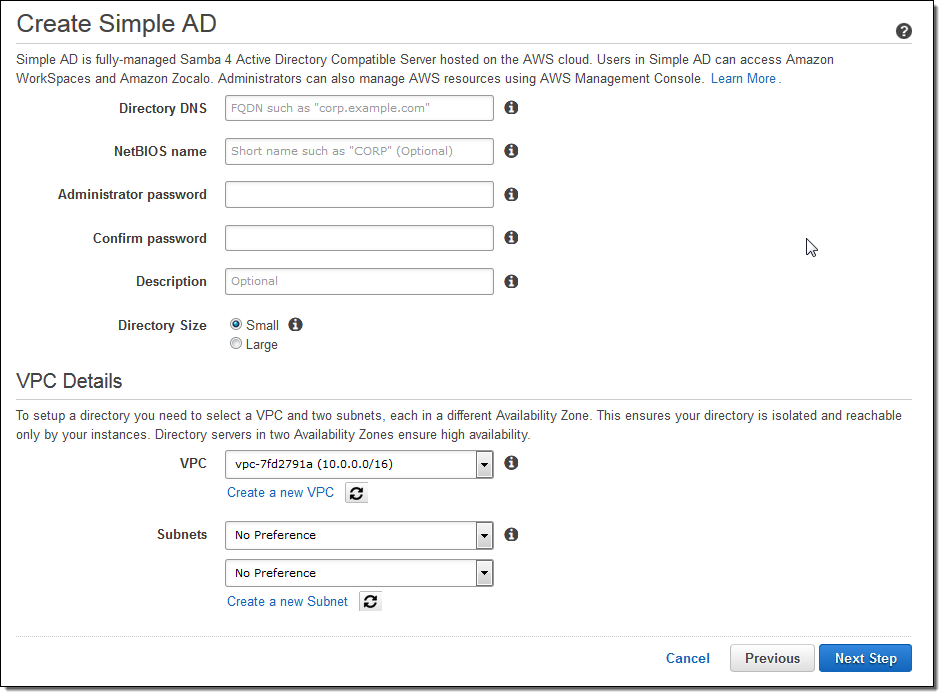
Again, the Simple AD will be up, running, and ready for use within minutes.
Managing Directories
Let’s take a look at the management features that are available for the AD Connector and Simple AD. The Console shows me a list of all of my directories:
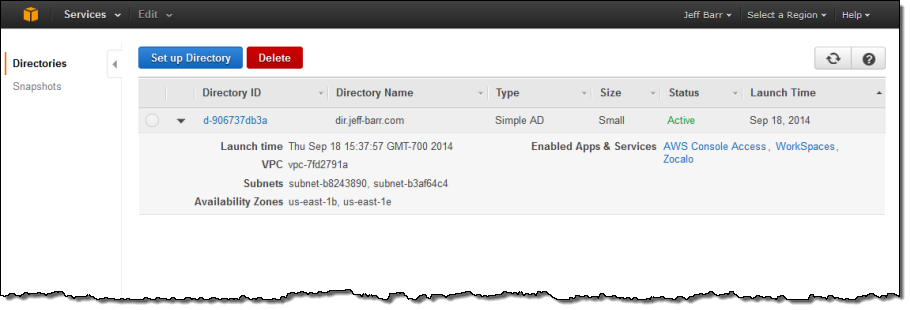
I can dive in to the details with a click. As you can see at the bottom of this screen, I can also create a public endpoint for my directory. This will allow it to be used for sign-in to AWS applications such as Zocalo and WorkSpaces, and to the AWS Management Console:
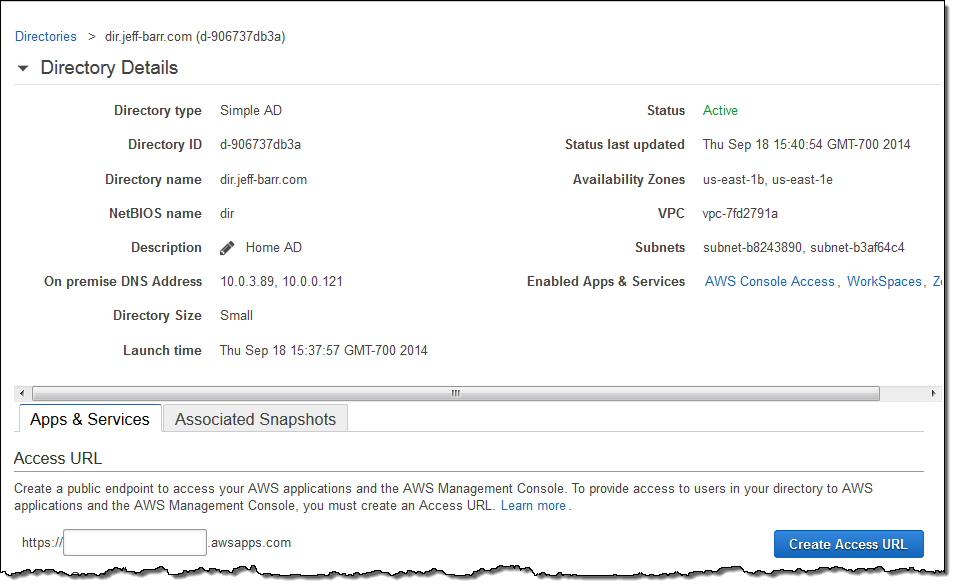
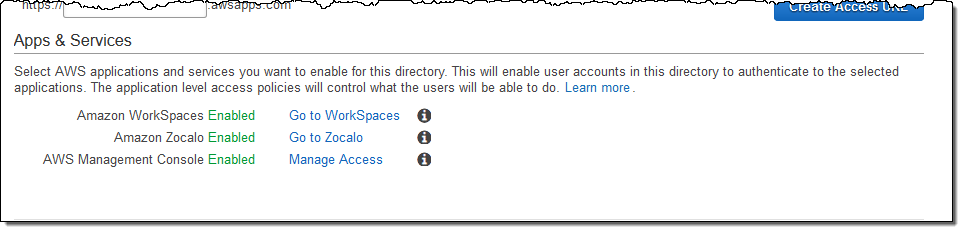
I can also configure the AWS applications and the Console to use the directory:
I can also create, restore, and manage snapshot backups of my Simple AD (backups are done automatically every 24 hours; I can also initiate a manual backup at any desired time):
Get Started Today
Both types of directory are available now and you can start creating and using them today in the US East (Northern Virginia), US West (Oregon), Asia Pacific (Sydney), Asia Pacific (Tokyo), and EU (Ireland) Regions. Prices start at $0.05 per hour for Small directories of either type and $0.15 per hour for Large directories of either type in the US East (Northern Virginia) Region. See the AWS Directory Service page for pricing information in the other AWS Regions.
— Jeff;